Demoting a domain controller forcefully
It's also an option to forcefully remove a domain controller from Active Directory. While graciously demoting should be the preferred option, you might have to resort to this option.
The process of demoting a domain controller forcefully consists of these steps:
- Performing a metadata cleanup
- Deleting the domain controller from DNS
- Deleting the computer object for the domain controller
- Deleting the SYSVOL replication membership
- Deleting the domain controller from Active Directory Sites and Services
- Seizing any FSMO roles that were hosted by the domain controller (you can do this first to ensure there are no impacts on domain members)
- Taking care of the existence of global catalog servers
If the domain controller was the last domain controller for a domain in an existing forest, the domain will need to be removed, as it is now an orphaned domain.
Getting ready
Although you would demote a domain controller forcefully when it no longer replicates, you should ensure that the remaining domain controllers are replicating properly.
How to do it...
This recipe describes two ways to do it:
- Using the Active Directory Domain Services Configuration Wizard
- Using manual steps
Using the Active Directory Domain Services Configuration Wizard
The Active Directory Domain Services Configuration Wizard can be used to forcefully demote a domain controller when the Windows Server installation is still bootable and you are able to sign in to it with administrative credentials.
Perform these steps:
- Press Start.
- Search for Server Manager and click its corresponding search result, or run
servermanager.exe. The Server Manager window appears. - In the gray top bar of Server Manager, click Manage.
- Select Remove Server Roles and Features from the menu.
- On the Before you begin screen, click Next >.
- On the Select destination server screen, select the local Windows Server installation from the server pool list.
- Click Next >.
- On the Select server roles screen, deselect the Active Directory Domain Services role from the list of installed roles.
- In the pop-up window, click the Remove Features button to remove features that are required for Active Directory Domain Services.
- On the Validation Results screen, follow the Demote this domain controller link to acknowledge that the domain controller needs to be demoted before the Active Directory Domain Services role can be removed.
- On the Credentials screen, select the Force the removal of this domain controller option:
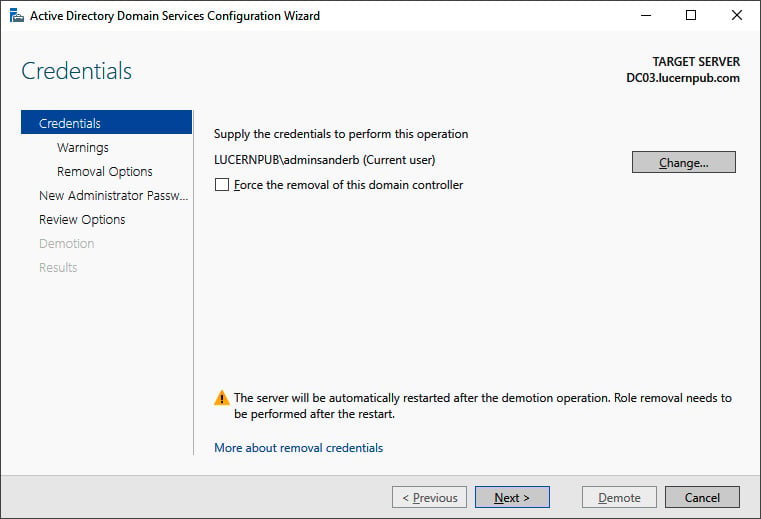
Figure 2.17 – The Credentials screen of the Active Directory Domain Services Configuration Wizard
- Click Next >.
- On the Removal options screen, select the Proceed with removal option and click Next >.
- On the New administrator password screen, enter the new password for the built-in administrator account.
- Click Next > to proceed to the next screen.
- On the Review Options screen, click Demote.
- When configuration of the Active Directory Domain Services server role is done, click Close to close the Remove Roles and Features Wizard.
Using manual steps
Sometimes, the Active Directory Domain Services Configuration Wizard cannot be used, such as in the following situations:
- You can no longer sign in interactively or remotely to the domain controller.
- The physical hardware of the domain controller has been damaged beyond repair.
- The domain controller is no longer reachable for other domain controllers.
- The domain controller, for some reason, can no longer be trusted to provide Active Directory Domain Services in a meaningful way.
In these scenarios, the following manual steps can be performed to remove the domain controller from Active Directory.
Performing metadata cleanup
Perform these steps to perform metadata cleanup:
- Sign in interactively to the domain controller that is known to be good. The domain controller holding the Domain Naming Master is preferred.
- Press Start.
- Search for Command Prompt, right-click its search result, and choose Run as administrator from the context menu. Alternatively, run
cmd.exe, but instead of running it by pressing Enter, press Ctrl, Shift, and Enter. - Run the following command to start the NTDS utility in interactive mode:
ntdsutil.exe
- Type the following command in interactive mode to start the metadata cleanup:
metadata cleanup
- Type the following command to remove the
DC04.lucernpub.comserver:remove selected server "CN=DC04,CN=Servers,CN=RemoteLocation,CN=Sites,CN=Configuration,DC=LucernPub,DC=com"
- Type the following command in interactive mode to exit the metadata cleanup context:
quit
- Type the following command in interactive mode to exit the NTDS utility itself:
quit
- Close the Command Prompt window.
Deleting the domain controller from DNS
After the metadata cleanup, the DNS records for the domain controller may still be present. Use the DNS MMC Snap-in to remove the DNS A, AAAA, PTR, and SRV records for the domain controller.
Deleting the computer object for the domain controller
To delete the computer object for the domain controller, use the Active Directory Administrative Center:
- Press Start.
- Search for Active Directory Administrative Center and click its corresponding search result, or run
dsac.exe. The Active Directory Administrative Center window appears. - In the main Welcome to Active Directory Administrative Center pane, in the GLOBAL SEARCH field, enter the search criteria of the desired object and then click the Search button:
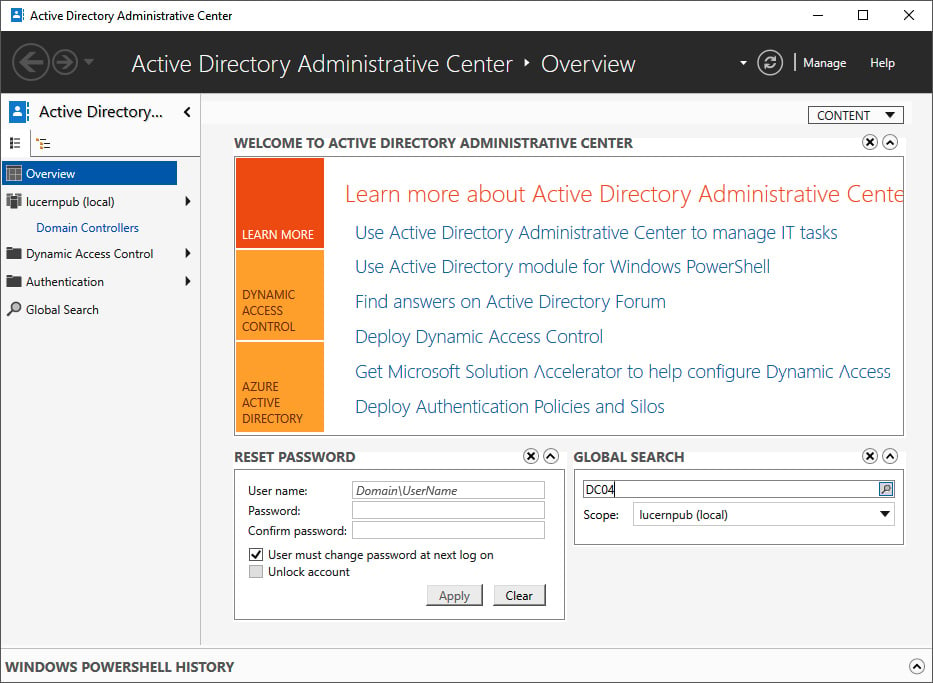
Figure 2.18 – Searching for an object using Global Search in the Active Directory Administrative Center
- From the search results, locate the domain controller object.
- Right-click it and then click Delete.
- Confirm you want to delete the domain controller.
- Close the Active Directory Administrative Center window.
To delete the computer object for the domain controller, alternatively, run the following line of Windows PowerShell:
Remove-ADComputer -Identity DC04
Replace DC04 with the name of the domain controller you want to remove.
Deleting the SYSVOL replication membership
The domain controller was also a member of the replication group for the Active Directory SYSVOL.
Perform these steps to remove the domain controller:
- Press Start.
- Search for Active Directory Administrative Center and click its corresponding search result, or run
dsac.exe. The Active Directory Administrative Center window appears. - At the top of the left navigation pane, switch to Tree view from List view.
- Expand the Active Directory domain.
- Expand the System container.
- Expand the DFSR-GlobalSettings container.
- Expand the Domain System Volume container.
- Expand the Topology container.
- In the main window, right-click the object for the domain controller you want to delete from the Topology container:
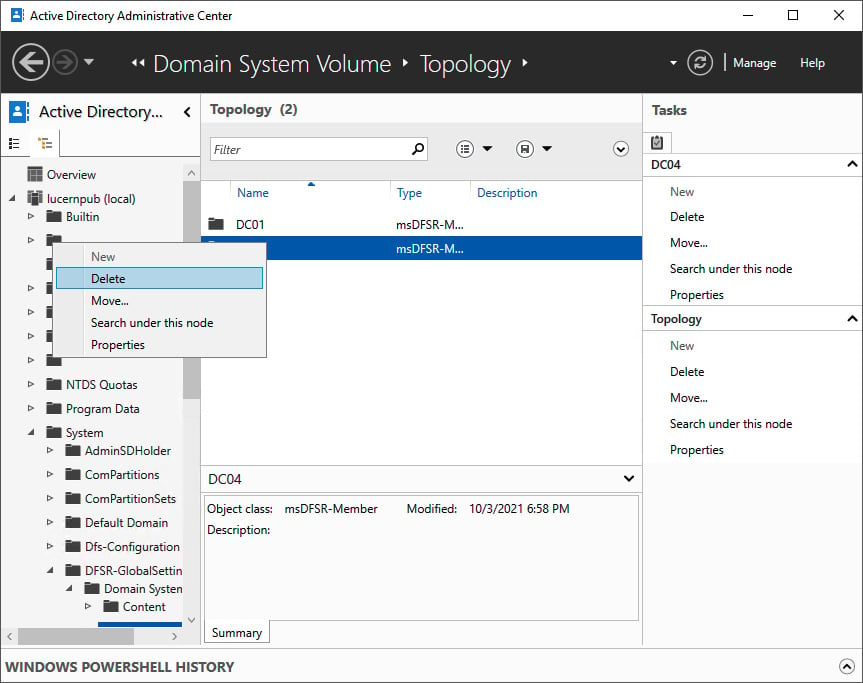
Figure 2.19 – Deleting the SYSVOL replication membership in the Active Directory Administrative Center
- Select Delete.
- In the Delete Confirmation pop-up window, click Yes to acknowledge that you are sure you want to delete msDFSR-Member.
- Close the Active Directory Administrative Center window.
Deleting the domain controller from Active Directory Sites and Services
To delete the domain controller from Active Directory Sites and Services, perform these steps:
- Press Start.
- Search for Active Directory Sites and Services and click its corresponding search result, or run
dssite.msc. The Active Directory Sites and Services window appears:
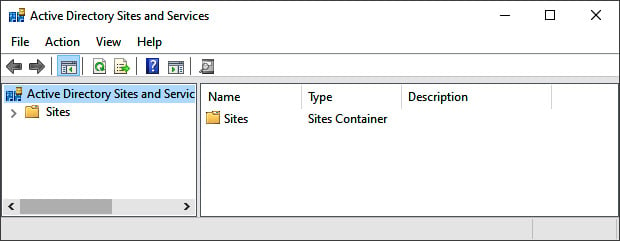
Figure 2.20 – The Active Directory Sites and Services window
- In the left navigation pane, expand Sites.
- Expand the Active Directory site where the domain controller resides.
- Expand the Servers node.
- Right-click the object for the domain controller you want to delete from the Servers node and select Delete.
- In the Active Directory Domain Services pop-up window, click Yes to acknowledge that you are sure you want to delete the server.
- Close Active Directory Sites and Services.
Deleting an orphaned domain
When you've removed the last domain controller for a domain, it becomes an orphaned domain. Perform these steps to perform a metadata cleanup for the orphaned domain:
- Sign in interactively to the domain controller that is known to be good with an account that is a member of the Enterprise Admins group. A domain controller that hasn't experienced any replication challenges throughout its lifetime might be your best choice. Also, note that performing the following actions on the domain controller holding the Domain Naming Master FSMO role is preferred.
- Press Start.
- Search for Command Prompt, right-click its search result, and choose Run as administrator from the context menu. Alternatively, run
cmd.exe, but instead of running it by pressing Enter, press Ctrl, Shift, and Enter. - Run the following command to start the NTDS utility in interactive mode:
ntdsutil.exe
- Type the following command in interactive mode to start the metadata cleanup:
metadata cleanup
- Type the following commands to specify the current domain controller as the server on which to make the changes, as it is the Domain Naming Master:
Connections connect to server localhost quit
- Type the following commands to list the Active Directory domains in the Active Directory forest so that you can select the domain you wish to remove:
select operation target list domains
- This outputs a list of domains in the forest, denoted by an identifier. Note down the identifier for the orphaned domain you want to remove.
- Type the following command in interactive mode to select the domain to remove:
select domain <ID>
- Type the following command to exit the operation target selection context:
quit
- Type the following command to remove the domain:
remove selected domain
- Type the following command in interactive mode to exit the metadata cleanup context and then the NTDS utility itself:
quit quit
- Close the Command Prompt window.
See also
To seize the FSMO roles, see the Managing FSMO roles recipe in Chapter 3, Managing Active Directory Roles and Features.
To configure domain controllers as global catalog servers, see the Managing global catalogs recipe in Chapter 3, Managing Active Directory Roles and Features.