Note
"640 K is more memory than anyone will ever need."
Bill Gates, Founder, Microsoft
Even with the best of intentions, the future is always unpredictable. The WLAN committee designed WEP and then WPA to be fool proof encryption mechanisms but over time, both these mechanism had flaws, which have been widely publicized and exploited in the real world.
WLAN encryption mechanisms have had a long history of being vulnerable to cryptographic attacks. It started with WEP in early 2000, which eventually was broken entirely. In recent times, attacks are slowly targeting WPA. Even though there is no public attack available currently to break WPA in all general conditions, there are attacks which are feasible under special circumstances.
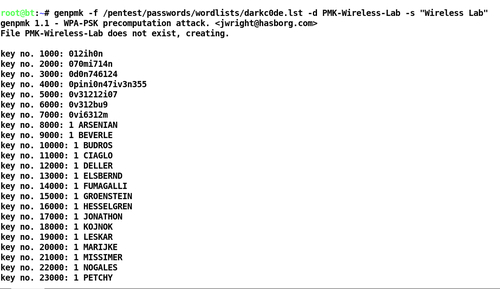
In this chapter, we shall look at the following:
Different encryption schemas in WLANs
Cracking WEP encryption
Cracking WPA encryption