Chapter 1: Fundamentals of Windows Security
Nowadays, the conversation of cybersecurity has become a hot topic throughout the world. And even more so with leadership teams and board members of many major organizations asking the question, are we secure? The short answer is no: no one is secure in today's digital world, and there has never been a more critical time to ensure that you are doing everything within your power to protect your organization and its users.
As we continue to receive daily news of breaches throughout the world, it is clear how severe the issue of cybercrime has become. To put it bluntly, we simply need to do a better job of protecting the data that we collect and manage within our organizations today. This isn't an easy task, especially with the advancement of organized cyber and state-sponsored groups with budgets, most likely, far exceeding that of most organizations. As security professionals, we need to do our due diligence and ensure we identify all risks within the organization. Once identified, they will need to be addressed or accepted as a risk by leadership.
As a consumer, it is most likely that your data has already been breached, and there's a chance your account information and passwords are sitting on the dark web somewhere. We need to work with the assumption that our personal data has already been breached and build better barriers around our data and account information. For example, in the U.S., purchasing identity protection as a service to monitor your identity can serve as an insurance policy if you incur any damages. In addition to this, the ability to place your credit reports on hold to prevent bad actors from opening accounts under your name is another example of a defensive approach that you can take to protect your personal identity.
As the cybersecurity workforce continues to evolve and strengthen with more and more talented individuals, we want to help contribute to the importance of securing our data, and we hope this book provides you with the necessary knowledge to do the right thing for your organization. As you read this book, you will not only learn the technical aspects of securing Windows, but you will also learn what else is necessary to ensure the protection of Windows and the users that use it. Protecting Windows has become a lot more than making a few simple configuration changes and installing an antivirus (AV) tool. There is an entire ecosystem of controls, tools, and technology to help protect your Windows systems and users.
As you read through this chapter, you will learn about the broader fundamentals of security and the principles behind the foundation that is needed to protect your Windows environment. Specifically, you will learn about the following:
- An overview of the security transformation within the industry
- A look at security trends as they relate to today's digital world
- A review of the current threat landscape and common vulnerabilities
- An overview of some recent publicly known breaches
- An overview of the current security challenges faced today
- What Zero Trust security is, and why we need to adopt this approach moving forward
Understanding the security transformation
Over the years, security has evolved from being just a shared role or a role that didn't even exist within a business. Today, well-defined teams and organizational structures do actually exist or are being created to focus solely on security. Not only are these teams maturing constantly, but the Chief Information Security Officer (CISO) has become a person of significant importance who may report directly to a Chief Executive Officer (CEO) within an organization and not the CIO.
Over the years, many roles that never existed before have begun to appear within the security world, and new skill sets are always in demand. As an overview, the following is a list of some of the more common security roles that you can expect to see within a security program:
- CISO/CSO (Chief Information Security Officer/Chief Security Officer)
- IT Security Director
- IT Security Manager
- Security Architect/Engineer
- Security Analyst
- Security/Compliance Officer
- Security Administrator
- Security Engineer
- Software/Application Security Developer
- Software/Application Security Engineer
- Cryptographer/Cryptologist
- Security Consultant/Specialist
- Network Security Engineer
- Cloud Security Architect
One thing to point out, in regard to these roles, is the major shortage of the cybersecurity workforce throughout the world. A cybersecurity workforce study by (ISC)² shows that a worldwide growth of 145% is needed to meet the demand for cyber experts. In the US, this number needs to grow by 62%. These numbers clearly show the demand for skilled cybersecurity experts along with opportunities for growth. The challenge with this growth is that new positions are continuously being created as new skills are needed, which makes it difficult to find well-seasoned talent (read more about the (ISC)² 2019 Cybersecurity Workforce Study here: https://www.isc2.org/Research/Workforce-Study).
One of the primary factors for the growing need of security experts correlates to the advancement of the PC (or personal computer) and its evolution throughout the years. The PC has changed the way we connect. And, with this evolution comes the supporting infrastructure, which has evolved into many data centers seen throughout the world.
As we are all aware, Windows has been the victim of numerous vulnerabilities over the years and continues to be a victim even today. The initial idea behind the Windows Operating System (OS) was a strong focus on usability and productivity. As a result of its success and adoption across the globe, it became a common target for exploits. This, in turn, created many gaps in the security of Windows that have traditionally been filled by many other companies. A good example is a need for third-party AV software. As the world has turned more toward digitization over the years, and the adoption of Windows usage has continued to grow, so has the need for improved security along with dedicated roles within this area. Protecting Windows has not been an easy task, and it continues to be an ongoing challenge.
Living in today's digital world
Today, we are more reliant on technology than ever and live in a world where businesses cannot survive without it. As our younger generations grow up, there is greater demand for the use of advanced technology. One scary thought is how fast the world has grown within the previous 100 years compared to the overall history of mankind. Technology continues to push the boundaries of innovation, and a significant portion of that change must include the securing of this technology. Especially since the world has become a more connected place with the advancement of the internet.
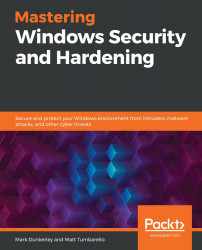
To give you a rough idea of technology usage today, let's take a look at the current desktop usage throughout the world. For these statistics, we will reference an online service, called Statcounter GlobalStats: https://gs.statcounter.com/. This dataset is not all-inclusive, but there is a very large sampling of data used to give us a good idea of worldwide usage. Statcounter GlobalStats collects its data through web analytics via tracking code on over 2 million websites globally. The aggregation of this data equates to more than 10 billion page views per month. The following screenshot shows the OS market share that is in use worldwide. More information from Statcounter can be viewed at https://gs.statcounter.com/os-market-share/desktop/worldwide:

Figure 1.1 – Statcounter Desktop Operating System Market Share Worldwide
As you can see, the Windows desktop market is more widely adopted than any other OS available today. Seemingly, Windows has always had negative connotations because of its ongoing vulnerabilities in comparison to other OSes. Part of this is due to how widely used Windows actually is. A hacker isn't going to waste their time on an OS that isn't widely adopted. We can assume there would be a direct correlation between OS adoption rates and available security vulnerabilities. Additionally, the Windows OS is supported across many types of hardware, which opens up opportunities for exploits to be developed. One reason as to why we see significantly fewer macOS vulnerabilities is due to the hardware control with which Apple allows its software to run. As the platform has grown, though, we have seen an increase of vulnerabilities within its OS too. The point we're making is that we tend to focus our efforts on areas where it makes sense, and Windows has continued to be a leader in the desktop space, making it a very attractive source to be attacked. This, in turn, has created an ecosystem of vendors and products over the years, all aimed at helping to protect and secure Windows' systems.
Let's take a look at the current adoption of the different Windows OSes in use. The following screenshot from Statcounter shows the current Windows desktop version usage around the world today. To view these statistics, visit https://gs.statcounter.com/os-version-market-share/windows/desktop/worldwide:

Figure 1.2 – Desktop Windows Version Market Share Worldwide
As you can see, Windows 10 has become the most adopted OS. Microsoft continues to push more users and organizations to Windows 10, and this is where they spend the majority of their development resources. There are also major changes to Windows 10 compared to older versions, which is why it is critical to migrate from older versions, especially for security-specific reasons. Microsoft ended its support (including security updates) for Windows XP in April 2014 and Windows 7 in January 2020.
NetMarketShare is another analytical site similar to Statcounter GlobalStats with its own set of statistics for reference: https://netmarketshare.com/.
A recent buzz term you have most likely heard in recent years is that of digital transformation. This refers to the shift from a legacy on-premises infrastructure to a modernized cloud-first strategy to support the evolving need of big data, machine learning, Artificial Intelligence (AI), and more. A significant part of this shift also falls within Windows systems and management. In Chapter 3, Server Infrastructure Management, we will look at the differences between a data center and a cloud model, including where the responsibilities fall for maintaining and securing underlying systems. Prior to digital transformation, we relied heavily on the four walls of the corporation and its network to protect a data center and its systems. This included a requirement for client devices to be physically on the corporate network in order to access data and services. With this model, our devices were a little easier to manage and lock down, as they never left the corporate office. Today, the dynamics have changed, and, referencing back to Statcounter in the following screenshot, you can see a significant shift from traditional desktop usage to a more mobile experience and requirement. To view the source of this diagram, visit https://gs.statcounter.com/platform-market-share/desktop-mobile-tablet/worldwide/#monthly-200901-202003:
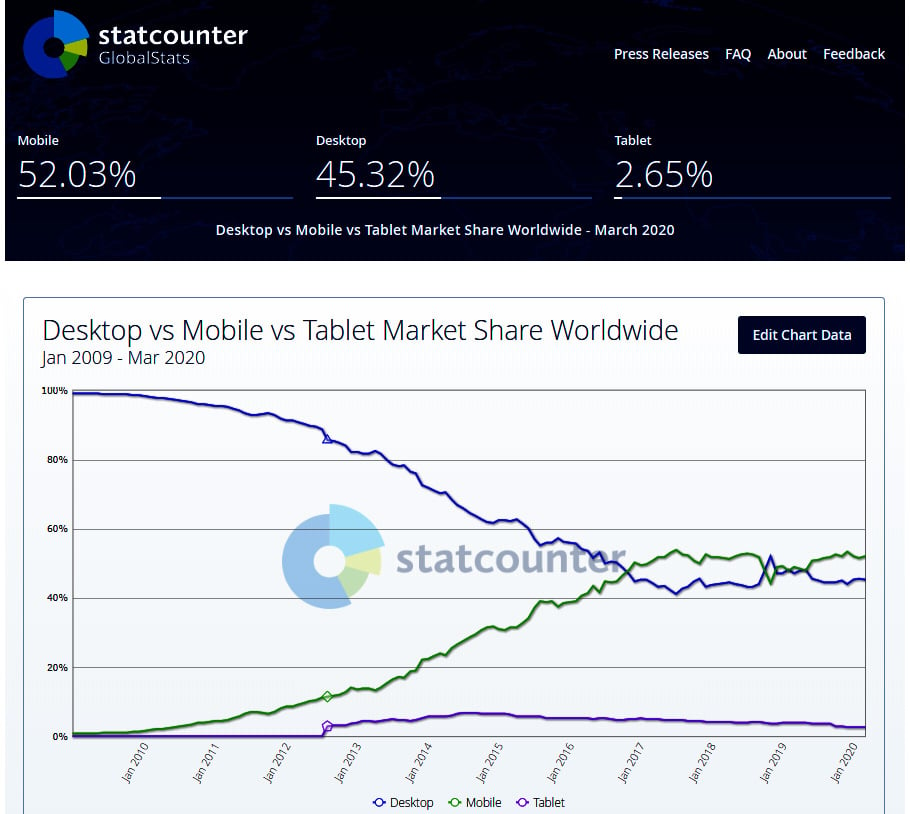
Figure 1.3 – Statcounter platform comparison Jan 2009 – Mar 2020
Focusing on Windows security, the traditional model of an organization would have typically included the following security tools as part of its baseline:
Depending on your organization or industry, there may have been additional tools. However, for the most part, I'd imagine the preceding list was the extent of most organizations' security tools on Windows client devices. The same would have most likely applied to the Windows servers in the traditional model. As this digital transformation has brought change, the traditional method of Windows management has become a legacy. There is an expectation that we can work and access data from anywhere at any time. We live in an internet-connected world, and, when we plug our device in, we expect to access our data with ease. With this shift, there is a major change in the security of the systems we manage and, specifically, the Windows server and client. As we shift our infrastructure to the cloud and enable our users to become less restricted, the focus of security revolves not only around the device itself but that of the user's identity and, more importantly, the data. Today, the items that we listed earlier will not suffice. The following tools are those that would be needed to better protect your Windows devices:
- Advanced Threat Protection (ATP): AV and threat protection, advanced analytics and behavioral monitoring, network protection, exploit protection, and more
- Advanced data loss prevention
- Information protection
- Identity protection: biometric technology, multi-factor authentication, and more
- Application control
- Machine learning and advanced AI security services
Today's threats
The threat landscape within the cyber world is extremely diverse and is continually becoming more complex. The task of protecting users, data, and systems is becoming more difficult and requires the advancement of even more intelligent tools to keep the bad actors out. Today, criminals are more sophisticated, and large groups have formed with significant financial backing to support the wrongdoings of these groups. The following is a list of cyber threats:
- National governments
- Nationstates
- Terrorists
- Spies
- Organized crime groups
- Hacktivists
- Hackers
- Business competitors
- Insiders/internal employees
Tip
To learn more about these cyber threat sources, the Department of Homeland Security has a great reference here: https://www.us-cert.gov/ics/content/cyber-threat-source-descriptions.
To shed some light on real-world examples of data breach sources today, Verizon has created a 2020 Data Breach Investigations Report (https://enterprise.verizon.com/resources/reports/dbir/). The report is built on a set of real-world data and contains some eye-opening data on attack sources:
- External actors: 70%
- Organized criminal groups: 55%
- Internal actors: 30%
- Partners: 1%
- Multiple parties involved: 1%
The full report can be found here:
https://enterprise.verizon.com/resources/reports/2020-data-breach-investigations-report.pdf
There are many types of cyberattacks in the world today, and this creates a diverse set of challenges for organizations. While not all threats are Windows-specific, there's a chance that Windows is the median or attack vector in which an attacker gains access by exploiting a vulnerability. An example of this could be an unpatched OS or an out-of-date application. The following list contains many common types of threats that could cause damage directly from a vulnerability within the Windows OS or by using the Windows OS as an attack vector.
Malware is software or code designed with malicious intent that exploits vulnerabilities found within the system. The following types of threats are considered malware:
- Adware
- Spyware
- Virus (polymorphic, multipartite, macro, or boot sector)
- Worm
- Trojan
- Rootkit
- Bots/botnets
- Ransomware
- Logic bomb
In addition to malware, the following are types of attack techniques that can be used to exploit vulnerabilities:
- Keylogger
- Phishing
- Spear phishing
- Whale phishing
- SQL injection attack
- Cross-Site Scripting (XSS)
- Denial of Service (DoS)
- Session hijacking
- Man-in-the-Middle Attacks (MITM)
- Password attacks (brute-force, dictionary, or birthday attacks)
- Credential reuse
- Identity theft
- Advanced persistent threats
- Distributed Denial of Service (DDoS)
- Intellectual property theft
- Shoulder surfing
- Golden Ticket: Kerberos attacks
Tip
To learn more about the threats listed earlier, the National Institute of Standards and Technology (NIST) contains a glossary that provides more information on most, if not all, of the preceding list: https://csrc.nist.gov/glossary.
Identifying vulnerabilities
Now that we know more about the threats, it's even more important for you to know where to access information about these vulnerabilities. You also need to be aware of any resources that are available so that you can educate yourself on what's required to remediate any vulnerabilities. As you are already aware, Windows is renowned for its ongoing vulnerabilities, and patching/updating these systems has morphed into a full-time and very specialized role over the years. The following website is the authoritative source with regard to Microsoft security updates: https://portal.msrc.microsoft.com/en-us/security-guidance.
Useful information
Here is the link to the Microsoft Security Response Center (MSRC): https://www.microsoft.com/en-us/msrc?rtc=1.
As shown in the following screenshot, you will be provided with a list of all identified vulnerabilities from Microsoft within a selected time range with additional filtering options. To give you an idea of the risk profile for Windows, the following filter is scoped to Windows 10 for x64-based systems over the last month, which returned 47 uniquely addressed vulnerabilities:

Figure 1.4 – Microsoft Security Update Guide
One term you may have heard as part of vulnerability management with Microsoft is the famous Patch Tuesday (also referred to as Update Tuesday). Patch Tuesday occurs on the second Tuesday of every month and is the day that Microsoft releases its monthly patches for Windows and other Microsoft products. There are many references on the internet for Patch Tuesday in addition to the MSRC. One example of a common resource used to track Patch Tuesday releases is the Patch Tuesday Dashboard: https://patchtuesdaydashboard.com/. Another example to better manage your notifications when vulnerabilities are released is PatchManagement.org: http://patchmanagement.org/.
As you review the updates needed for your Windows systems, you will notice that each of them has a unique identifier to reference the update beginning with CVE®. CVE stands for Common Vulnerabilities and Exposures and is the standard for vulnerability management, allowing one source to catalog and uniquely identify vulnerabilities. CVE is not a database of vulnerabilities but a dictionary providing definitions for vulnerabilities and exposures that have been publicly disclosed. The U.S. Department of Homeland Security (DHS) and the Cybersecurity and Infrastructure Security Agency (CISA) sponsor the CVE.
Tip
Visit this website to learn more about CVE: https://cve.mitre.org/about/index.html.
The following screenshot shows an overview of what the CVE provides and can be found at https://cve.mitre.org/cgi-bin/cvekey.cgi?keyword=Windows:
Figure 1.5 – CVE® Windows Search Results
In addition to the CVE there's the NVD. The NVD is the National Vulnerability Database, which is an additional resource for vulnerability management provided by NIST. The NVD is synced with the CVE to ensure the latest updates appear within its repository. The NVD provides additional analysis of the vulnerabilities listed in the CVE dictionary by using the following:
- Common Vulnerability Scoring System (CVSS) for impact analysis
- Common Weakness Enumeration (CWE) for vulnerability types
- Common Platform Enumeration (CPE) for a structured naming standard
The following screenshot shows an overview of what the NVD provides and can be found via https://nvd.nist.gov/vuln/search/results?form_type=Basic&results_type=overview&query=Windows&search_type=all:
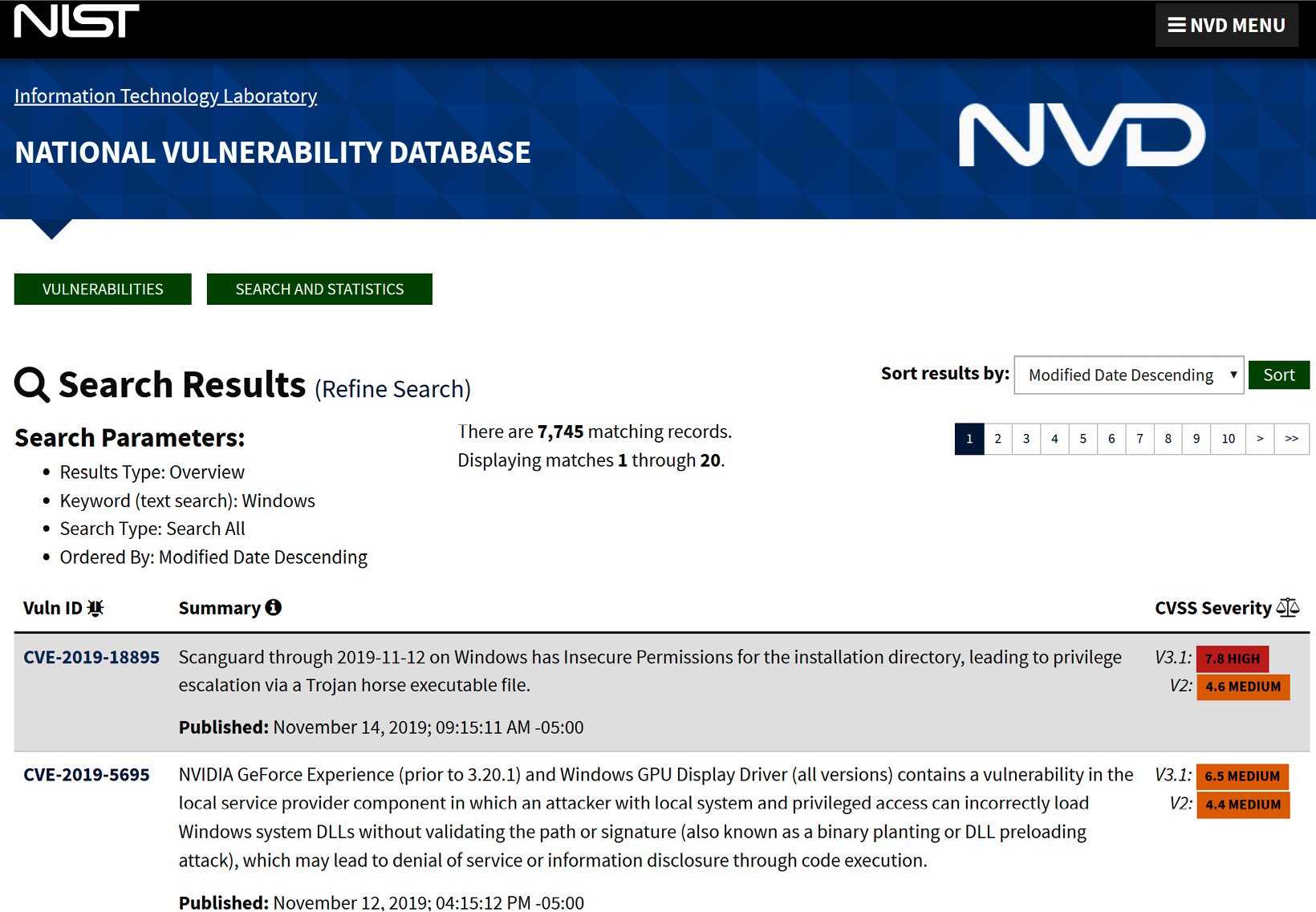
Figure 1.6 – NVD Windows Search Results
One additional resource that we should mention is the Open Web Application Security Project (OWASP). OWASP is a nonprofit organization to help improve the security of software for individuals and enterprises. They provide a tremendous amount of resources such as tools, documentation, and a community of professionals all looking to continually enhance software security. Although application and web-specific, there is a high possibility that the application or web app will be running on both your Windows server and Windows client. Because of this, it is critical, as a security professional, for you to be able to intelligently discuss these concerns and challenges with the business, developer(s), and application/web app owners.
Tip
You can find more information about OWASP at https://www.owasp.org/index.php/Main_Page.
One of the more common projects that OWASP provides is the OWASP Top 10, which provides the most critical web application security risks. The latest version available was published in 2017 and is presented here:
- Injection
- Broken authentication
- Sensitive data exposure
- XML External Entities (XXE)
- Broken access control
- Security misconfiguration
- Cross-Site Scripting (XSS)
- Insecure deserialization
- Using components with known vulnerabilities
- Insufficient logging and monitoring
Tip
View OWASP Top 10 2017 – The Ten Most Critical Web Application Security Risks here: https://owasp.org/www-project-top-ten/OWASP_Top_Ten_2017/.
Recognizing breaches
If you follow the news, you are probably aware that there is no shortage of breaches today. They are happening so frequently that it is not uncommon for several breaches to occur weekly or even daily. What is an even scarier thought is these are just the ones that we hear about. To give you an idea of how serious the issue has become, the following list has some of the more notable breaches that are documented on Wikipedia's List of data breaches page. There are many sources on the internet of top breaches, but Wikipedia has the most comprehensive I have found with references to each of the listings:

Figure 1.7 – Wikipedia List of data breaches
You can find the source for the preceding screenshot here: https://en.wikipedia.org/wiki/List_of_data_breaches.
As you review the breaches and understand how they occurred, you will see a common trend where, for the most part, the breach occurred from hacking or poor security practices. You might also notice that other common methods of breaches include lost or stolen equipment. These statistics are alarming, and they indicate how critical it is to secure and harden our systems as best as possible.
To give you an idea of the importance of securing and hardening your environment, the article referenced next shows that the cost of a user record from a data breach is $242 per record. A quick calculation of this multiplied by 100,000 customers calculates a potential loss estimated at $24.2 million. When you look at the number of breached records shown in the table, you will understand how this could be extremely damaging to a business's value and reputation.
View the table at What's the Real Cost of a Data Breach? here: https://www.pkware.com/blog/what-s-the-real-cost-of-a-data-breach.
Tip
An interesting site for reference is Have I Been Pwned. This site will show you whether your email has ever been breached and, if so, where it was breached: https://haveibeenpwned.com/. You can also sign up for notifications for any breaches related to a specific domain.
There are many sources available where you can view security news and follow the latest trends and best practices. The following are some of the resources used to keep up to date with what is happening in the security world today:
- DarkReading: https://www.darkreading.com/
- Cyware: https://cyware.com/cyber-security-news-articles (recommended phone app)
- Business Insider: https://www.businessinsider.com/sai
- ZDNet: https://www.zdnet.com/topic/security/
- Newsfusion Cyber Security News: https://www.newsfusion.com/cyber-security (recommended phone app)
- BBC: https://www.bbc.com/news/technology
- The Hacker News: https://thehackernews.com/
Current security challenges
By the time you finish reading through the chapter, you will have hopefully been provided with a sense of how important security has become today and the challenges that come with it. We are continually becoming more reliant on technology than ever before with no signs of slowing down. We have an expectancy of everything being digitized, and, as IoT begins to take off, everything around us will be connected to the internet, thus creating even more challenges to ensure security is efficient.
As we briefly covered earlier, attacks are becoming more and more sophisticated every day. There is an ever-growing army of bad actors working around the clock trying to breach any data they can get their hands on because the cost of private data is very expensive. With the advancement of cloud technology, supercomputers, and the reality of quantum computing coming to light, hackers and organized groups are easily able to crack passwords and their hashes much more easily, making them obsolete as the only factor of authentication. No one should be using only passwords anymore; however, the reality is, most still are. The same applies to encryption. The advancement of computers is making algorithms insecure with the ongoing need for stronger encryption. These are just some of the ongoing challenges we are faced with when protecting our assets.
Keeping up with vulnerabilities today is a full-time role. It's critical that we keep on top of what they are, and which Windows systems need to be updated. We will discuss the management of Windows updates later in the book, but having a program in place to manage the overwhelming amount of Windows updates is critical. Additionally, third-party applications will need to be carefully monitored and updated accordingly. An example of a commonly used application is Adobe Acrobat Reader DC to view PDFs. The following screenshot is a vulnerability report from Microsoft Defender Security Center. It provides a software inventory of all machines with the application installed and lists the number of vulnerabilities detected across all machines in your organization:

Figure 1.8 – Acrobat Reader DC identified vulnerabilities
As you can see, out-of-date applications have critical known vulnerabilities that are used by attackers.
Most organizations are reluctant to release the latest Windows updates to their servers straight away because of the risk that a patch could break a production system. The downside to this is that your system will have a known vulnerability, which opens an opportunity for it to be exploited between the time of the patch release and the system being patched. Another challenge we are faced with is zero-day vulnerabilities. A zero-day vulnerability is one that has been identified but, currently, has no remediation or mitigation available from the vendor. Because of these challenges, it is critical we build in a layered defense strategy with our Windows clients and servers. For example, never make your database server accessible via the internet, encrypt the traffic to your web servers, and only open the ports needed to communicate, such as only allowing port 443 for secure (HTTPS) traffic only.
As we focus on securing Windows devices within our environments, we can't turn a blind eye to the fundamentals, including the overarching ecosystem that also needs to be considered when protecting your Windows devices. This book will cover a lot of detail on the specifics of securing and hardening your Windows systems and devices, but we also want to ensure the bigger picture is covered; for example, simple concepts of identity and access management. A user whose account has been compromised to allow an intruder on your Windows system has just made all the securing and hardening of that system irrelevant. The concept of weak physical access controls and policies could allow someone to simply walk into a server room and gain physical access to your systems. Other examples are allowing a developer to install an insecure web app with vulnerabilities on it, or a business that develops a process without security best practices in mind. All the controls you put in place with Windows become irrelevant as an educated hacker could use the web app or exploit a process as an attack vector to gain access to your system. These examples show the criticality of not only being familiar with how to secure and harden the Windows OS, but all the other factors that fall within a mature security platform to ensure your environment is as secure as possible. This, of course, doesn't come easily, and it is critical you stay current and continue to learn and learn and learn!
Managing and securing your Windows systems is not a simple task, especially if you are working toward securing them correctly. There is a lot involved, and in order to efficiently and effectively secure your Windows systems, you need well-defined policies, procedures, and standards in place along with a rigorous change control process to ensure anything that falls outside of the standards receives the appropriate approval to minimize risk. Full-time roles exist today to manage and secure your Windows systems along with specialized roles that are necessary to manage your Windows environments. Examples include Windows desktop engineers, Windows server engineers, Windows update administrators, Windows security administrators, Windows Intune/MDM engineers, and others. As part of these roles, it is critical that the staff are continuously educated and trained to provide the best security for Windows. The landscape is changing daily, and if your staff isn't dynamic or doesn't stay educated, mistakes and gaps will occur with your security posture.
Other tasks to think about that must be addressed with your Windows devices are inventory management, that is, ensuring you know where all your devices are and who has access to them. Even more important is ensuring that devices are collected upon any terminations, especially those pertaining to disgruntled employees. Enforcing policies on your Windows devices is also another challenge; for instance, how do you ensure all your devices have the latest policies and how can you ensure accurate reporting on non-compliant devices? Remote management can also be a challenge, that is, to make sure that not just anyone can remotely access your devices, including the auditing of support staff for anything that they shouldn't be doing. Running legacy applications on your Windows devices creates an instant security concern and making sure they are patched to the latest supported version is critical. This list goes on, and we will be diving in much greater detail in the following chapters to help provide the information you need to protect your Windows environment.
Before we move on to the last topic, one additional challenge that needs mentioning is Shadow IT. In short, Shadow IT is the setup and use of servers and infrastructure without IT or the security team's approval or knowledge, for example, a business function. This instantly creates a significant security concern as Windows systems will most likely be used with no standards or hardening in place. This can be a challenge to manage, but it is something that needs to be understood and prevented within any business.
Implementing a Zero Trust approach
To close out the chapter, we wanted to touch on a concept known as Zero Trust. The Zero Trust architecture model was created by John Kindervag while he was at Forrester Research Inc. back in 2010. You may be wondering what exactly Zero Trust is. Essentially, it is a model where we trust no one until we can validate who they are, who they are meant to be, and whether they are authorized to have access to the system or information. Effectively implementing a Zero Trust model is going to require a multilayered approach to the security strategy along with the use of the most current and modern technology available. The method of allowing a user to access the environment with only a username and password is outdated and insecure. With Microsoft's version of a Zero Trust model, they are recommending the use of a strong identity, ensuring devices are enrolled within a management tool, enforcing the concept of least privilege, and verifying the health of both devices and services. To support this model, some of the technologies include Azure Active Directory, multi-factor authentication, biometrics, Conditional Access, Microsoft Intune, and Microsoft Defender ATP. As you read through this book, you will find the guidance and instructions that are provided will ultimately lead to a Zero Trust model.
Tip
You can read more about the Zero Trust Microsoft model here: https://www.microsoft.com/en-us/itshowcase/implementing-a-zero-trust-security-model-at-microsoft.
Summary
In this chapter, we covered, at a high level, what you can expect to read throughout this book. We provided an overview of the security in an enterprise and briefly covered the different roles that you can expect to see within security departments. Next, we looked at how security relates to the digital world and how relevant it's become as the world becomes more digital. We also looked at the usage of the Windows OS throughout the world to better understand the adoption by users.
We then reviewed the current threat landscape and the types of cyber threat sources. We moved on to provide an overview of the threats we typically see in an enterprise today. We then provided details on where you can go to learn and view all of the recent Microsoft vulnerabilities with correlating patches and instructions on how to keep your devices up to date. In addition to Microsoft's vulnerability resources, we provided additional insight into where the patches get their naming standards via CVE along with NVD, which is provided by NIST. Next, we looked at some of the biggest breaches that have occurred to date and provided some popular sources to keep you up to date with the latest cyber news. We finished the chapter with an insight into some of today's general security challenges and, more specifically, those with Windows systems, before closing with an overview of Zero Trust security and what it entails.
In the next chapter, we will review building a baseline. The chapter will review what a baseline is, and then go into detail as to why a baseline must be formed. As part of the baseline, you need to ensure your policies, standards, and procedures are in place, that they are well-defined, and that they are signed off by the leadership and all the stakeholders who are liable for protecting the data. Having these documented is important for security reasons as well as for compliance and auditing purposes. Following this, we will briefly cover change management and its importance as it relates to baselining. We will then review frameworks and what they entail before moving on to some common frameworks that should be referenced to build your baseline. We will finish the chapter with a review of baseline controls and how to implement them before providing the best practices around baselining.