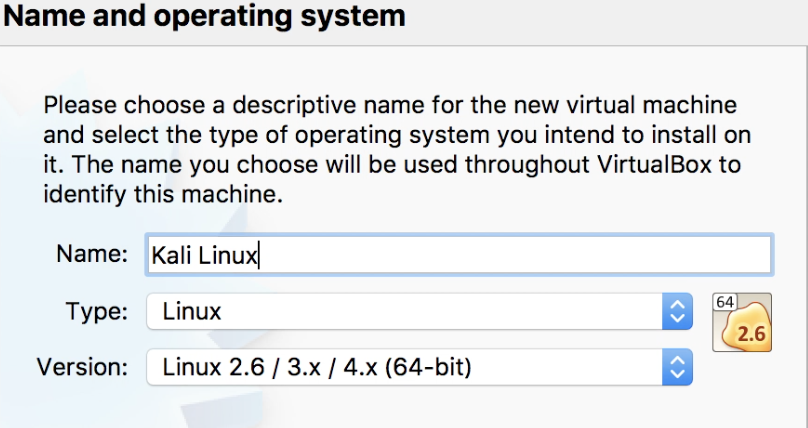
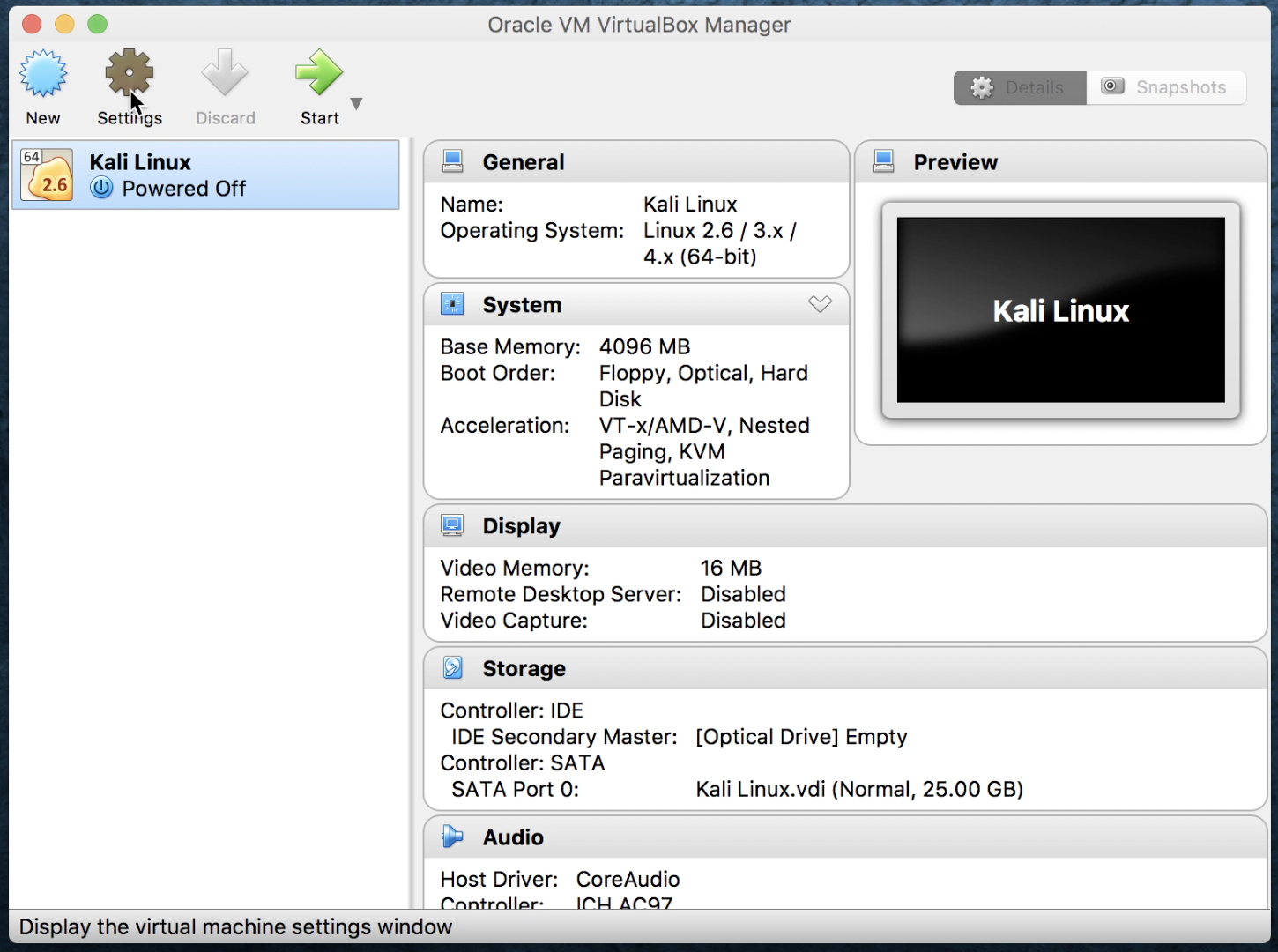
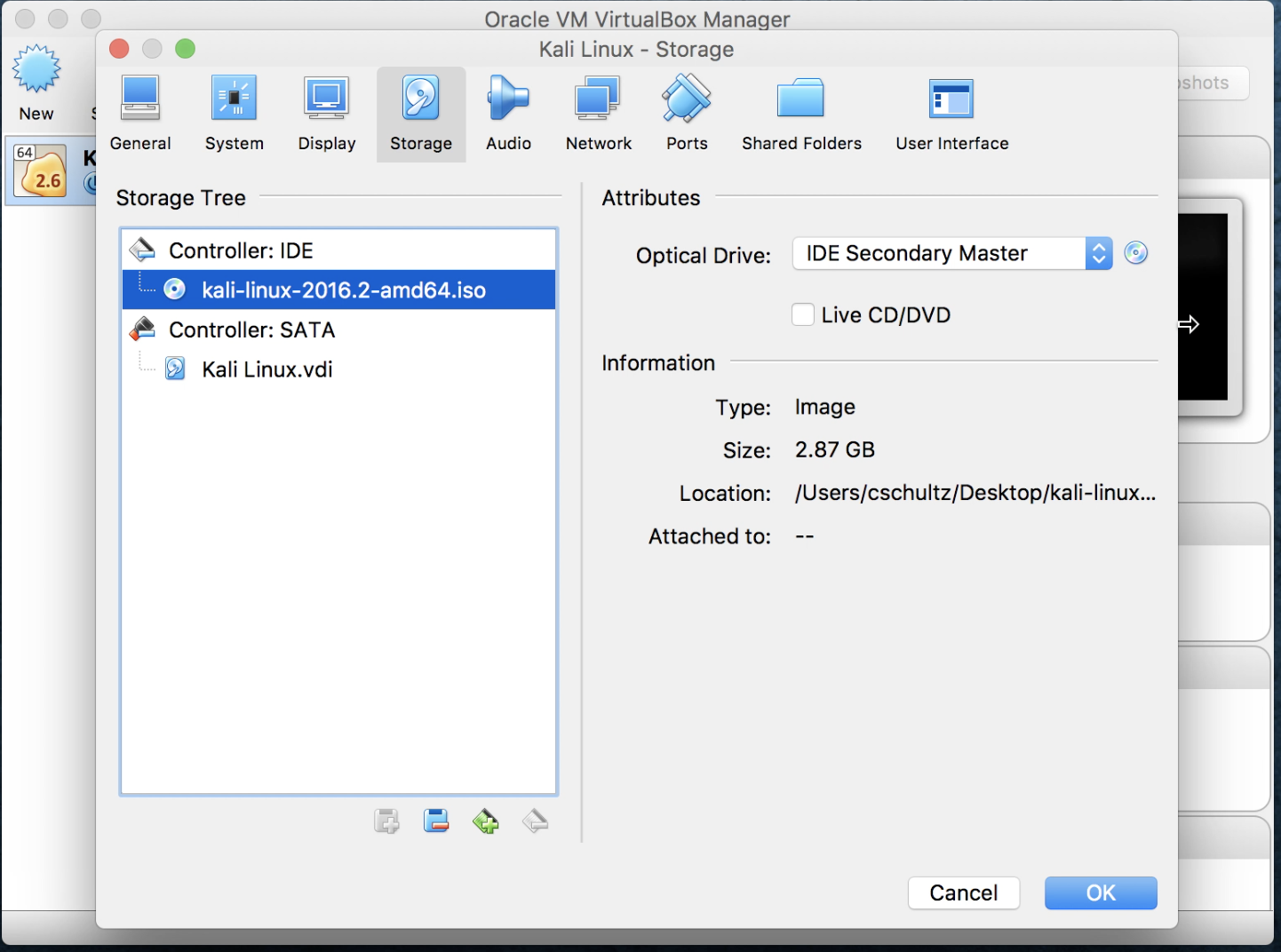
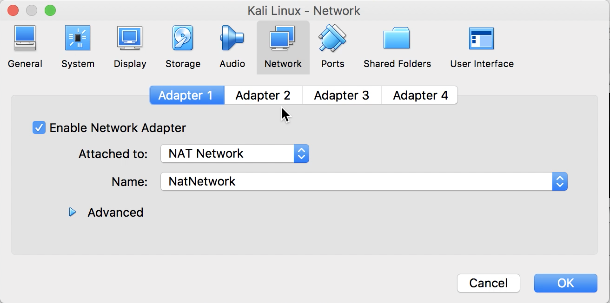
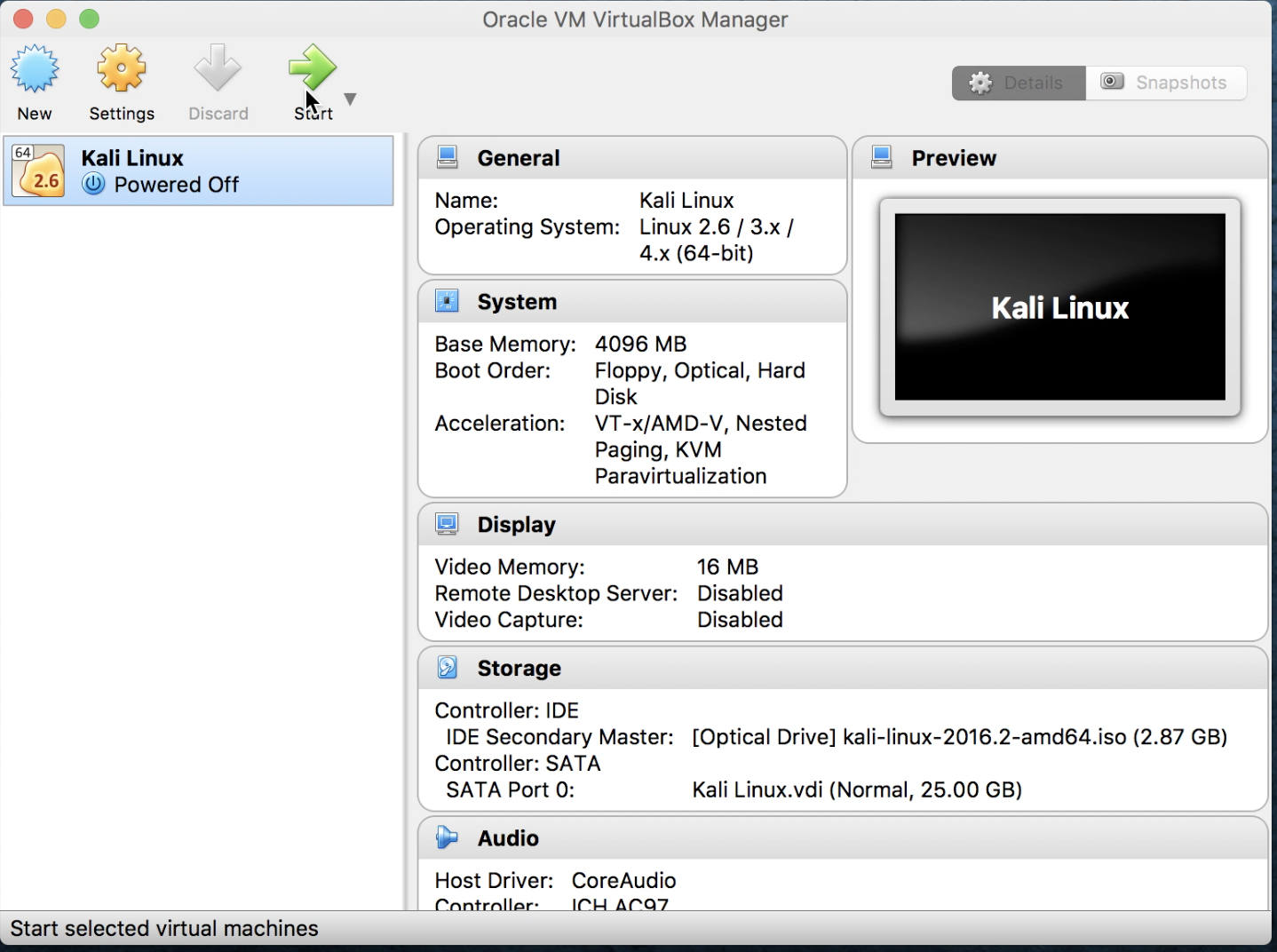
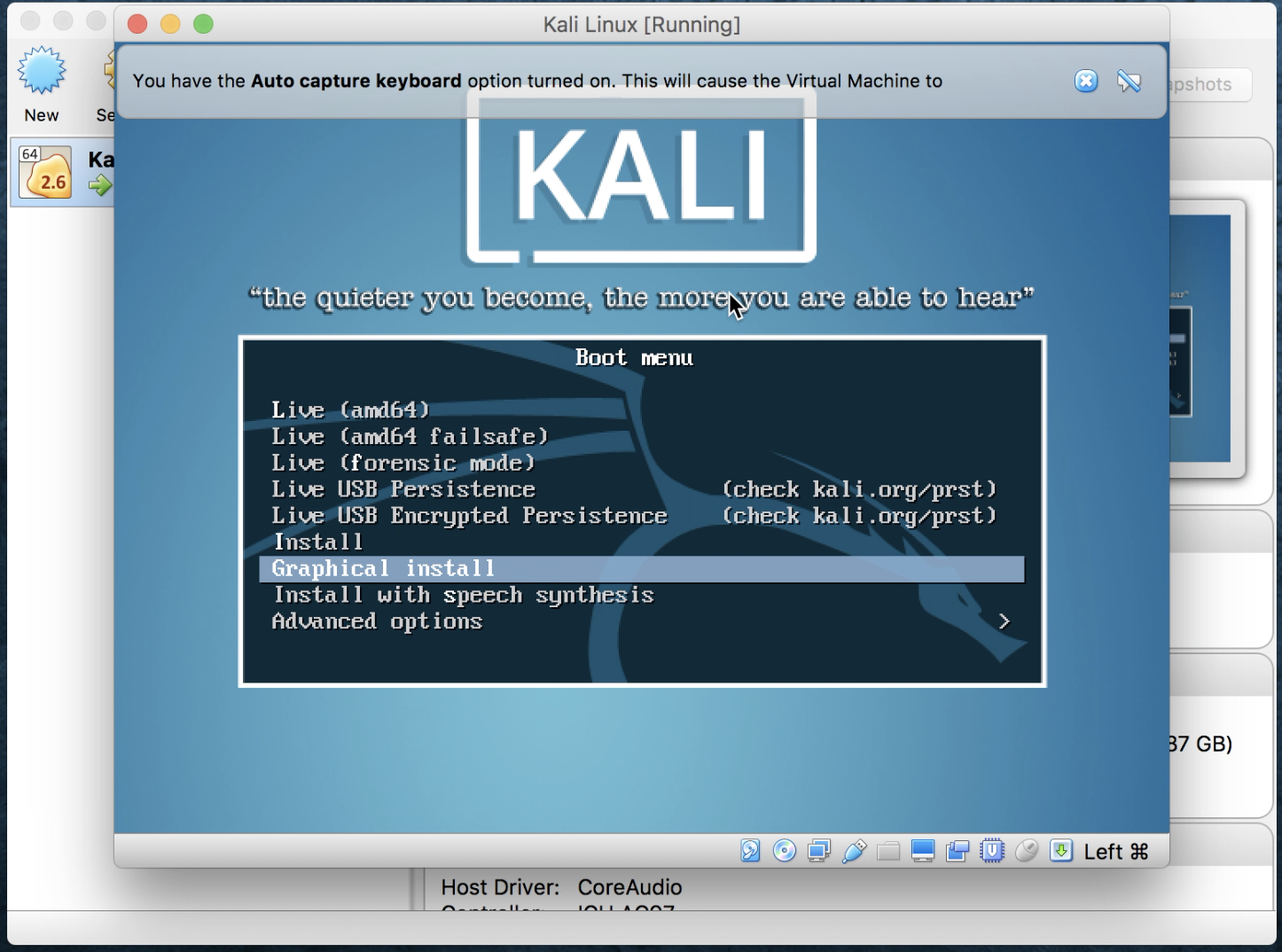
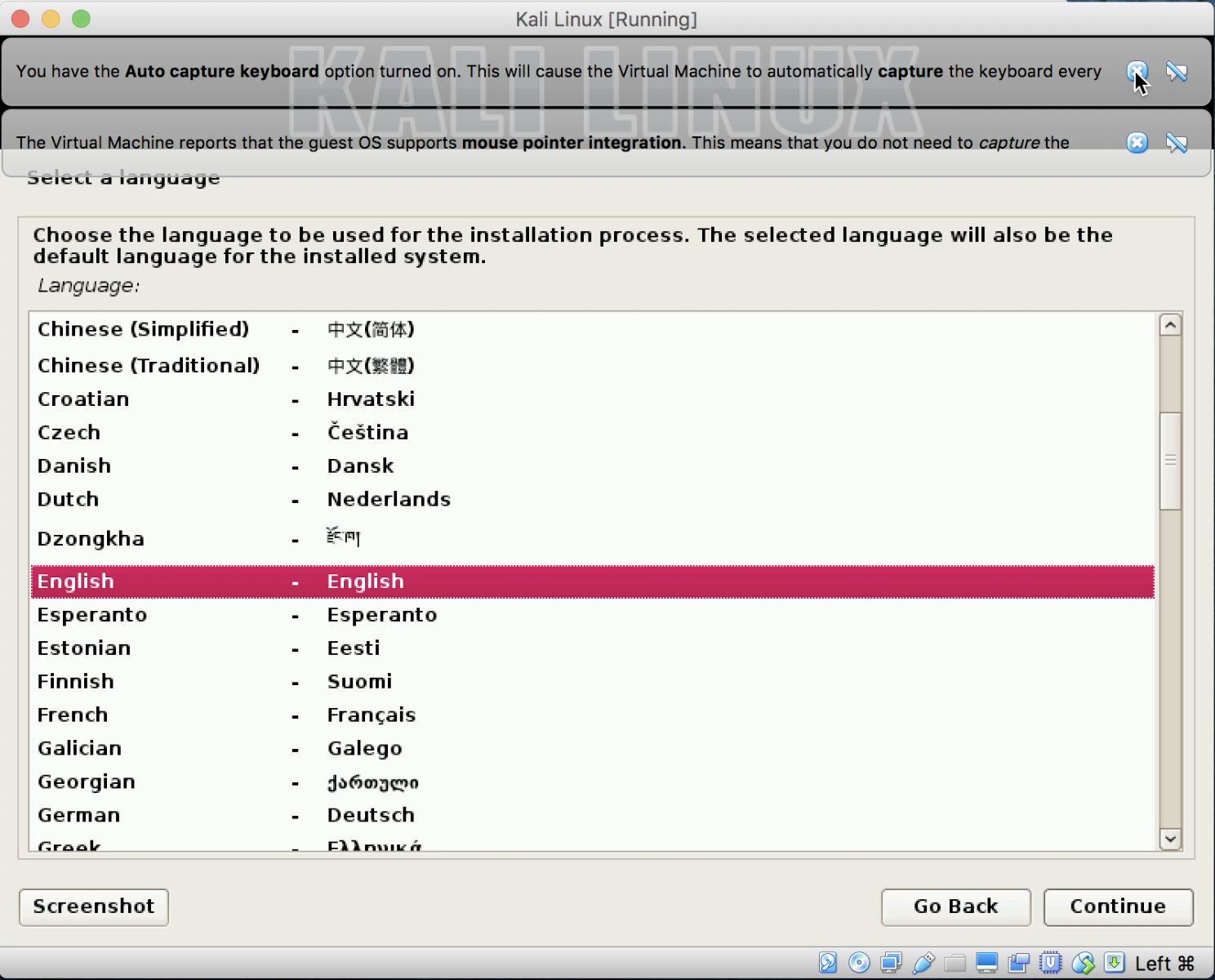
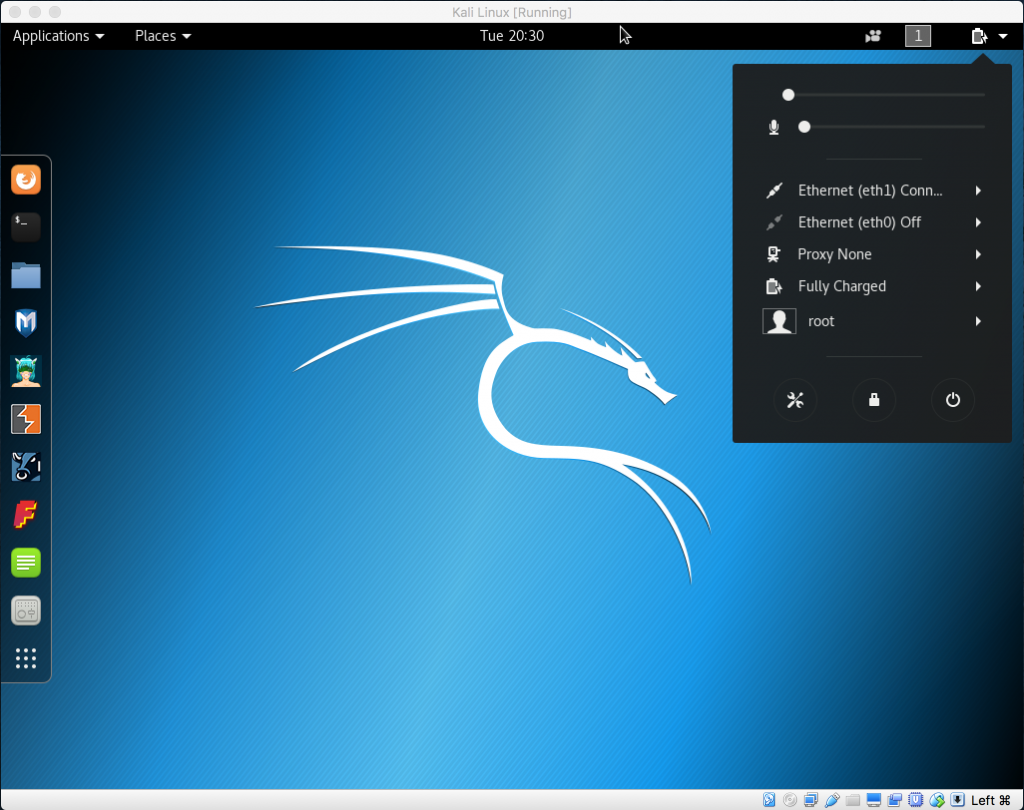
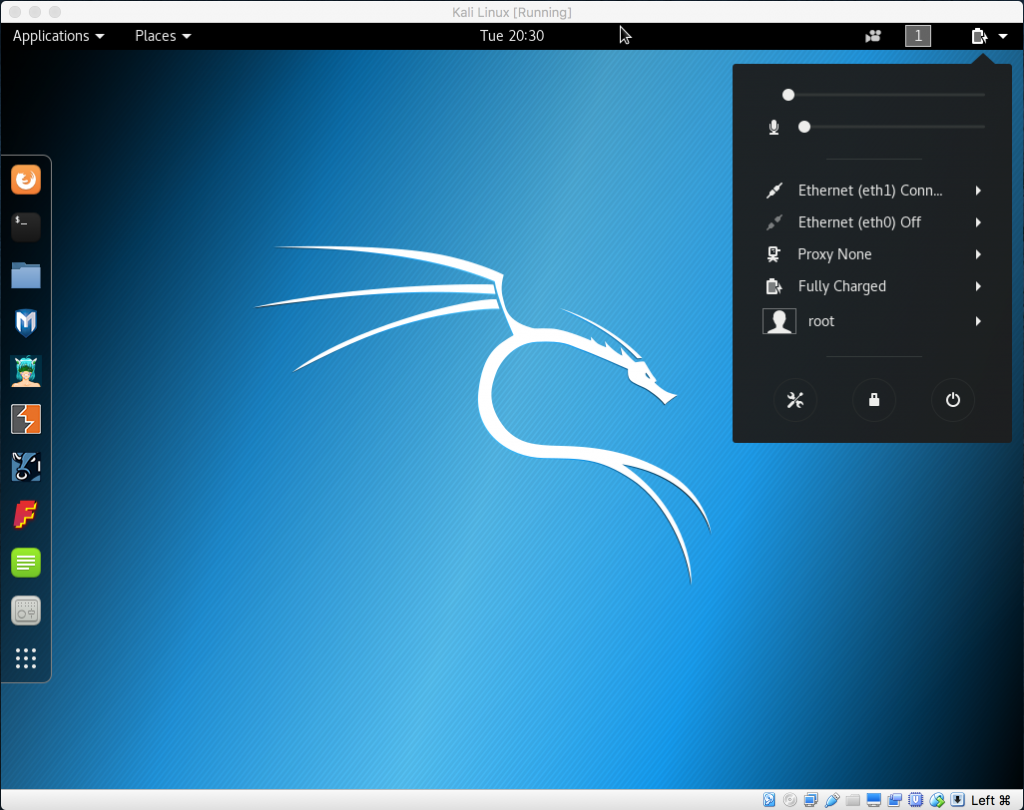
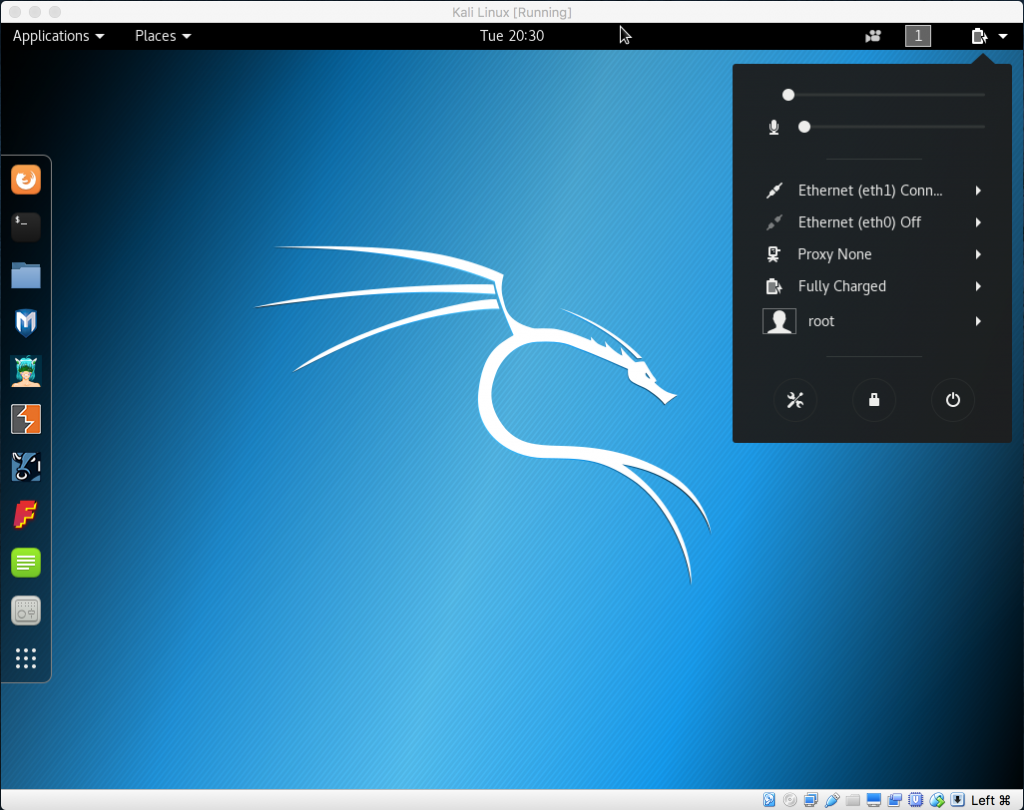
In this section, we will install Kali Linux into a virtual host in the VirtualBox environment, as we described in the previous section.
Kali Linux (Kali) is based on the Debian operating system; and it is a self-contained environment that includes hundreds of tools that can be used for security auditing and testing purposes. It provides a platform, which you can use to build your penetration testing skills. It is one of the most widely used platforms for this purpose.
Kali comes in a variety of different flavors – we will be using the full Kali install using the Gnome windows manager, inside an Oracle VirtualBox environment. However, Kali can be installed on any hypervisor; it can be non-destructively run from a USB or CD drive, on Raspberry Pi's, or other similar single board computers. It supports installation on both the Intel and Arm processors.
When you first go to the Kali website and look at the downloads section (www.kali.org/downloads), it may be a bit overwhelming with all the options at first, so let's run through some of them, so you understand the differences.
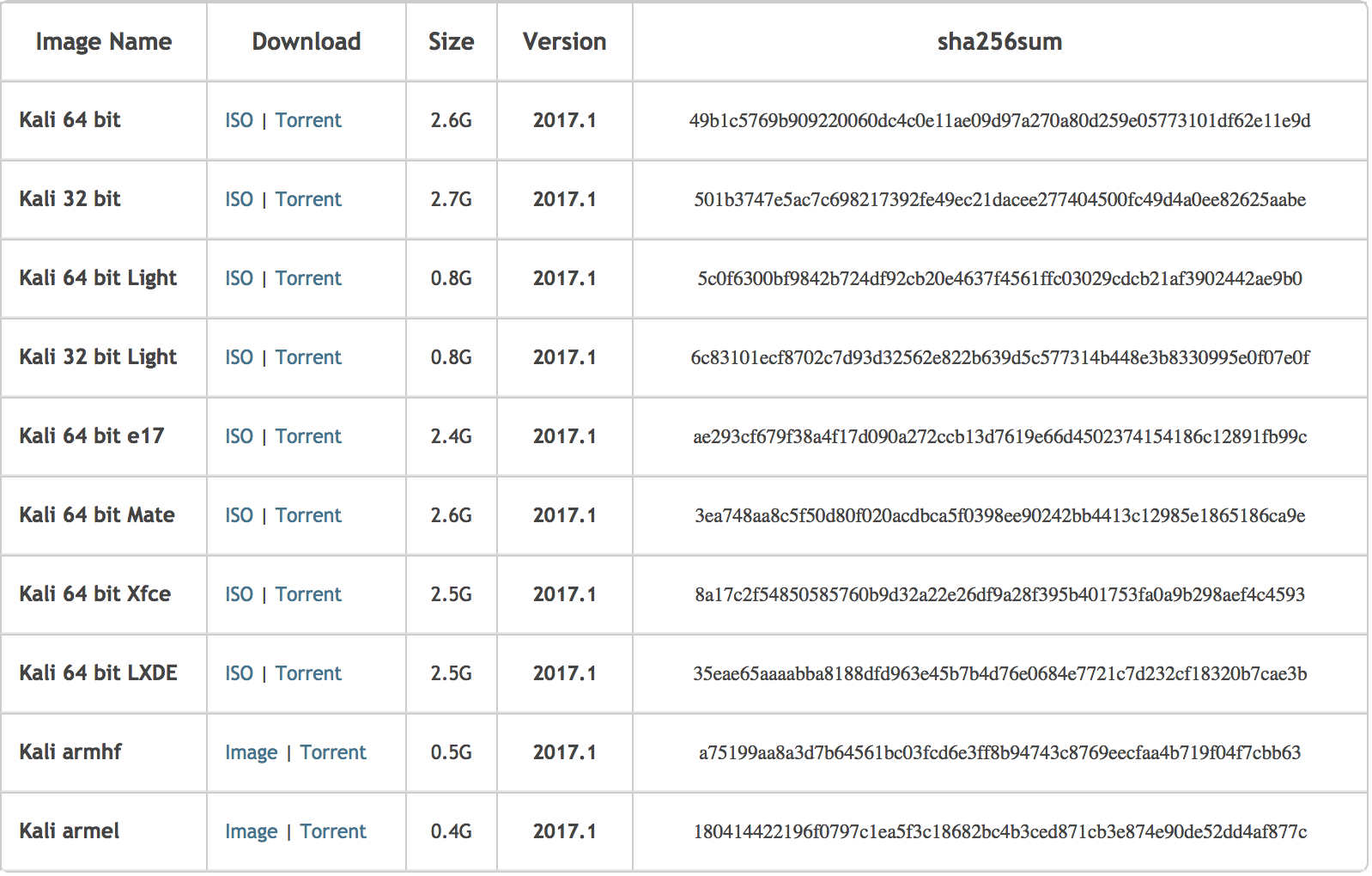
With reference to the following image, you will note that the top two entries, the Kali 64 bit and the Kali 32 bit, are the default full install of the operating system using the Gnome windows manager.
The next two entries denoted by lightare a minimal install of Kali with the Gnome Windows manager for some space constrained systems. You can use this along with manually installing only the needed tools for your specific purposes.
The next four entries denoted with e17, Mate, Xfce, and LXDE are full installs of the Kali operating system, each using a different graphical windows manager for its desktop interface. If you happen to have an older device, consider running Kali with the XFCE interface, as it requires less resources than Gnome. I would only suggest these if you are familiar with them, and opt not to use the default Gnome windows manager or have a specific purpose to do so such as resource constraints.
The last two entries, armhf and armel, are for those two flavors of the arm architecture with armhf supporting the older ARMv4 instruction set, and the armel supporting the new version 7 instruction set.
Please also note that the sha256 value is displayed. This allows you to validate that you have downloaded an unaltered version of the image:
Kali.org download page, image section, as of May 2017
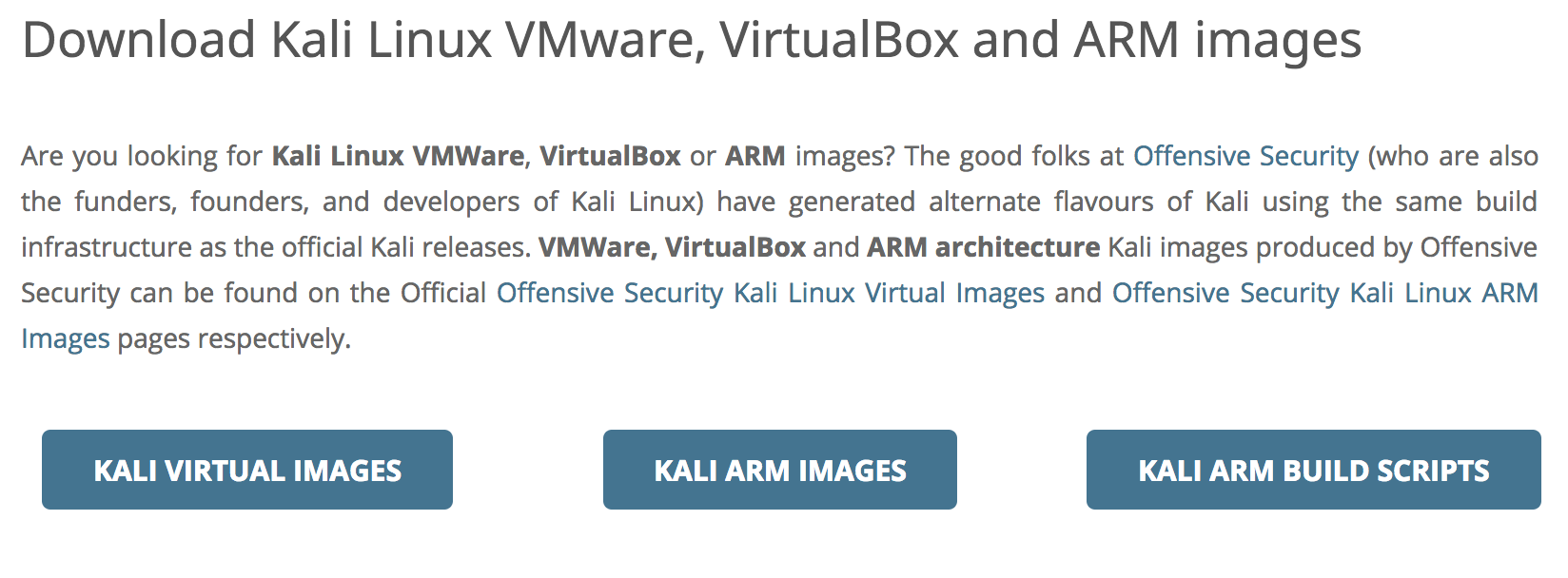
If you scroll down the page a bit more, you will see the section that allows you to download pre-prepared images that can automatically run without going through the setup process; in addition, it supports various hypervisors, or, in the case of ARM, has images and scripts for popular arm-based computers, such as Raspberry Pi's or other popular arm-based devices.
We will not be using these images as we want to walk you through a full installation and setup of Kali, so you have a better understanding of the process.
Kali.org download page, hypervisor and arm section, as of May 2017