Getting Started with Ripple
Money has undergone evolution since its existence: from a barter system to physical objects to gold coins. Paper currency replaced gold coins, which was again replaced, to an extent, by digital money. Even before digital money replaces paper currencies, we can start seeing money taking a new form through cryptocurrencies. Bitcoin was the first decentralized cryptocurrency. Later, many cryptocurrencies such as LiteCoin, Ethereum, and Ripple were introduced to the market.
In this chapter, we will be exploring the following topics to understand the basics of Ripple and why it is necessary:
- Introduction to the blockchain, the underlying technology behind cryptocurrencies
- Introduction to Bitcoin, the first decentralized cryptocurrency
- Inefficiencies with traditional payment systems
- Introduction to Ripple, the currency agnostic cryptocurrency
- The functionality of the Ripple Protocol
- Key features of Ripple
- Potential risks of Ripple
The need for decentralization
Few diamond firms found it unusual when Punjab National Bank demanded 100% cash margins for issuing LOUs (letters of undertaking), which is a form of bank guarantee under which its customers can raise money from any other Indian bank's foreign branch in the form of short-term credit.
However, the firms argued that this requirement was not enforced for the LOUs they received since 2010. This raised alarms and PNB called for an investigation. They found out a few employees had been issuing fake LOUs through the SWIFT system (a messaging system between banks). Unfortunately, the software that PNB used to facilitate SWIFT didn't record its transactions. This allowed the fraud to go undetected. A month later, PNB found out that the scam cost them $1.8 billion.
We have been using centralized systems to build internet applications for a long time. Here, business logic and data lies in one or more central servers. Client applications communicate with these servers to process information. Bank employees use software, which interfaces with the bank's central system, to facilitate transactions. Another example is your bank's application: when you tap to send money, the request is sent to the bank's centralized system for processing.
What happens if that central system is compromised? What happens when someone makes a transaction and deletes its traces? How do we prevent such fraudulent activities?
To solve these problems, we need to satisfy the following requirements:
- A system shouldn't have a central point of attack
- Transactions or data in the system must be tamper-proof
These are the key concepts behind distributed ledger systems or blockchain-based systems. Technically, these concepts are known as decentralization and immutability.
Introduction to blockchain
The word blockchain itself is descriptive. Here, blocks of digital information are linked back to one another like a chain of blocks. In the following image, we can see blocks that contain a series of transactions:

If someone tampers with the first transaction of the second block by altering $300 to $3,000, Ashin's balance would have an additional $2,700. Such tampering would lead to disastrous consequences. Hence, blockchain uses cryptography to make itself tamper-proof.
In the following blocks, we have added an additional attribute, the hash:

A hash is a set of characters that represents the contents of the block. It's calculated using a cryptographic hash function. For the sake of simplicity, we have made a simple hash by taking the first letters from the names of senders and beneficiaries. We also added the amount transferred in the middle of those first letters, and hence the hash for the first block is J500JJ450A. (Technically, this is not how a hash function works, but you get the idea.)
Since the first block has no preceding block, its previous hash field is not applicable. However, from the second block, all successive blocks have stored the hash of its previous block.
If someone tries to tamper with the first block and change John's transfer from $500 to $5,000, the hash of that block changes from J500JJ450A to J5000JJ450A. However, the successive block has already stored the hash as J500JJ450A. This mismatch would break the chain. Hence, the purpose of the hash is to ensure that blocks are not tampered with.
What if someone tries to change a block and the hash of all the succeeding blocks?
Different blockchains have different mechanisms to protect themselves from such situations. In the Bitcoin system, before a block is added to the chain, certain computationally intense tasks must be carried out.
Blocks are only confirmed once proof of running such intensive tasks or proof-of-work is shown. Hence, if a hacker wants to modify the hashes of n blocks, they need to run such computationally intense tasks n times to show the proof-of-work. Considering the present limits in computation, this scenario are highly unlikely.
Secondly, blockchain systems are decentralized. This means that a blockchain program isn't executed by a single computer, but all the computers in its network work collectively in executing its instructions. The data in the blockchain is also replicated in all the computers present in the network. Hence, the system would consider only what the majority say is correct.
Introduction to Bitcoin
Blockchain's application lies beyond building tamper-proof records. It can be used to make autonomous and automated systems that can work without human intervention. Bitcoin is an automated system that allows for the transfer of cryptoassets (bitcoin), directly between users without any intermediaries.
There are no signup forms to create a wallet. Instead, user keys are generated using cryptography. Here, there are two keys: the public key and the private key. The public key is like a username and the private key is similar to a password. These keys look like a long string with a combination of letters and numbers (for example, 18XgQU8FJbi8Vje6658hUKjeKjbbDS6eDa).
Privacy is one of the key features of Bitcoin. Since no user information is provided to the Bitcoin system, the system doesn't know any details about its users. Unless users expose their public key, they remain anonymous.
If a user wants to send money to another user, the sender needs to create a message, sign it and broadcast it. The broadcast message is later verified and committed to the ledger.
The following image depicts how a transaction makes its way to Bitcoin's tamper-proof ledger:

If Sosha wants to send 5 Bitcoin to Sneha, the message would look like the following:
Message: I am sending 5 Bitcoin to Sneha
Signature: Sosha's signature
Public Key: Sosha's public key
The signature is generated using a cryptographic function that takes Sosha's public key, private key, and message as input. Then, it generates the signature as output.
Now, anyone on the bitcoin network can verify it with another crypto function, which takes the public key, signature, and message as input. If the message is modified, the cryptographic function will throw an error.
Every 10 minutes, the bitcoin network groups new transactions as a block. This new block is only added to the blockchain once it is mined. To mine the block, the system creates a computational puzzle that should be solved by the miners. Here, humans don't solve the puzzles; instead, mining devices do.
Miners compete to solve this puzzle, and the first miner who solves this puzzle is rewarded with x number of Bitcoins. Presently, the reward is around 12.5 Bitcoin. These coins are minted out of thin air, and this is how new coins are added to the system.
Once a block is mined, it is permanently added to the blockchain. These blocks of transactions are visible to anyone. This results in transparency that, in turn, results in trust. Anyone can look up any blocks on the blockchain and also the transaction that occurred in the block. Here's the summary of block #544473:

Censorship resistance is a key feature of this innovation. Since there are no central servers, governments cannot enforce a ban on the system. To prevent bitcoin systems from functioning, all of its users' computers must be shut down. Since there are millions of such nodes in the network, it is almost impossible to achieve this.
Inefficiencies in payment systems
Speed and cost is an important factor in any payment system. In traditional banking, system money needs to move through several intermediaries before it reaches its destination. Each of these intermediaries adds to the transaction fees. Settlement happens slowly, since manual work is involved.
Consider John, who's a US account holder and wants to send money to his friend, Peter, in Germany. Here's how the money would flow from John's bank account to Peter's account:

Here is how the transfer happens:
- John places a request to transfer money.
- John's bank is a small bank and doesn't have an EU banking license. Hence, it needs the help of a large US bank to make the transfer. It sends money to the bank, which possesses an EU banking license.
- However, the small bank cannot transfer funds directly to the large bank; it has to route funds through a federal reserve.
- Once the money reaches the large bank, it transfers money from its nostro account to Peter's bank.
- However, the transfer doesn't happen directly, since the funds need to be routed through the European Central Bank.
Each of these intermediates adds to the transaction fee. If $5,000 needs to be transferred, around $250 is charged as transaction fees.
International money transfer through Bitcoin
Let's understand how international transfer can be simplified using Bitcoin.
Here's how the money would flow from John's bank account to Peter's account:

Here's how international money transfer happens through Bitcoin:
- John exchanges his USD for Bitcoin
- He directly transfers Bitcoin to Peter's account without any intermediaries
- Peter exchanges his Bitcoin for Euros
Disadvantages of Bitcoin
Though this process reduces intermediaries and reduces the transfer time to almost 60 minutes, it brings in new issues. Let's take a look at the disadvantages of Bitcoin:
- Bitcoin's system doesn't plug in to existing banking systems or currencies
- Users need to create bitcoin wallets and exchange it with their native currency
- Its market prices are highly volatile
- Bitcoin is not widely accepted as a currency; in certain countries, it's illegal
- It could handle only a limited number of transactions per second
- Its transaction fees are high
- Its proof-of-work mechanism demands an immense amount of energy
The key disadvantage of Bitcoin is that it doesn't work with existing currencies and forces the user to make transactions in Bitcoin. Since the currency is not widely accepted and some countries have banned transacting in Bitcoin, it brings in new risks to its users.
Ripple
Ripple addressed these issues and came up with a solution to incorporate blockchain with existing currencies. Ripple is a blockchain-based payment system that makes the global transfer of money cheaper, faster, and more efficient. Here, money doesn't need to be fiat currencies, but any item of value (for example, gold, digital assets, etc). It also issues its own native currency called XRP.
International money transfer through Ripple
Here's how money moves across borders through the Ripple protocol:
- John's bank would use Ripple's system to initiate the USD to EUR exchange. Market makers will compete by posting bids.
- Ripple's system is optimized to select the cheapest offer. The market maker will buy USD from John's bank and Ripple will transfer Euros from the market maker to Peter's account. These transactions are atomic, which means that both of these transactions happen simultaneously or they don't happen at all.
The following image depicts the flow of money from John's bank account to Peter's bank account through The Ripple Protocol:

Ripple reduces transfer time from days to a few seconds. This is because the transfer happens without intermediaries and the settlement process requires no human intervention. The average transaction fee in Ripple is around $0.0006; that's a significant reduction of cost.
The important point to note here is that users need not exchange Ripples. Ripple can be seamlessly plugged into a banks' systems. Hence, end users such as John and Peter don't have to interact with Ripple's blockchain. Now, let's go deep into the Ripple protocol and study how it works.
The Ripple Protocol
We will start by studying the details of how accounts are created, funded, and managed. Please note that in this chapter, we will only understand the underlying process of account creation, sending money, and so on. In the next chapter, we will learn to do it practically using tools that do these process by the click of a button.
Account creation
Similar to the Bitcoin system, Ripple has no signup process. Instead, we need to generate key pairs using cryptography. Since the process is mathematical, it can be done offline.
We start by generating a seed. A seed is a set of random characters. For the sake of simplicity, let's consider the seed as A34939449DJMABESEHLODAER. Once the seed is generated, a cryptographic function is used to derive a public key from it. We will use a simple function for the sake of understanding. Our function derives the public key from the seed by taking the first sixteen characters of the seed, A34939449DJMABES.
This is a one-way process: a public key cannot be used to derive the seed. Later, we can derive our Ripple identification by using the cryptographic hash function. This is the address we mention when we want to receive payments. This is done by creating the hash of the hash of the public key.
We will again use a simple function for the sake of understanding. We will strip the first eight characters to generate the first hash, A3493944. Then, we will strip the first four characters of the first hash to create the second hash,A349.
Now, A349 is our identity on the Ripple network. The key point to note here is that if you lose your seed, your account is compromised, since every other key can be derived from it. The following image demonstrates how the seed phrase is used to derive the public key and the Ripple identity:

This is a how a seed, public key, and account ID actually looks:
{
"seed": "sstV9YX8k7yTRzdkRFAHmX7EVqMfX",
"public_key": "aBQXEw1vZD3geCX3rHL8qy8ooDomdFuxZcWrbRZKZjdDkUoUjGVS",
"account_id": "rDGnaDqJczDAjwKHKdhGRJh2G7zJfZhj5q"
}
Reserve
Generating key pairs doesn't create an account in the XRP ledger. To prevent Ripple's ledger from growing excessively large, new accounts must be funded with a reserve amount of XRP from an existing amount to make them functional. The present reserve amount required is 20 XRP.
You can buy Ripple from a private exchange and send it to your Ripple's account ID. This transaction will create your account in the Ripple ledger. Now, your account will become functional and you can make transactions on Ripple. However, the reserve amount will remain locked.
The important point to note here is that funding an account doesn't give you access to an account. Only the person holding the secret key has access to its funds. It's possible to fund an address that doesn't have a secret key. However, this would result in a permanent loss of the sent XRP.
A Ripple account also has additional attributes such as a sequence number and history of transactions. The sequence number starts at 1, and every time a transaction is made it increases. It also holds the transaction history on how they affected the account's balances. The following image shows the front end of a simple ripple wallet:

Transactions
In order to send money, we need to create, sign, and submit the transaction to Ripple servers.
The following image depicts how a transaction makes its way to Ripple's tamper-proof ledger:
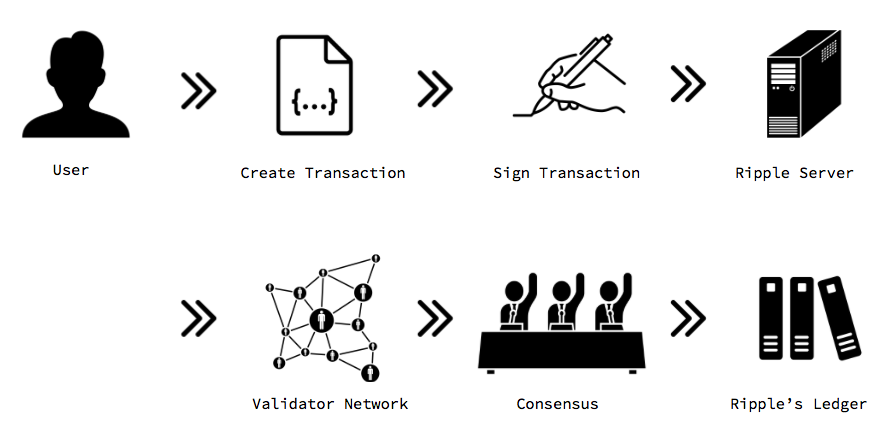
We would start by creating a transaction JSON. Here's an example of a transaction in JSON format. It includes sender address, destination address, currency type, amount to be transferred, and so on:
{
"TransactionType" : "Payment",
"Account" : "rf1BiGeXwwQoi4Z2ueFYTEXSwuJYfV2Jpn",
"Destination" : "ra5nK24KXfn9AHvsdFTKHSANinZseWnPcX",
"Amount" :
{
"currency" : "USD",
"value" : "2",
"issuer" : "rf1BiseXwwQoi8Z2ueFYTEXSwuJYfV2Jpn"
},
"Fee": "10",
"Flags": 2147482648,
"Sequence": 3,
}
We authorize the transaction using our secret key. Later, we submit it to the Ripple server for validation. Once it validates the transaction, it conveys the transaction to fellow members of the network. They apply these transactions to their version of the ledger in canonical order and submit the results. If enough validators reach consensus by sharing the same ledger, the transaction is confirmed and permanently added to the blockchain. If the transaction fails, it's also included in the ledgers. This is because failed transactions burn XRP and modify the account balances. XRP is burnt to prevent spammers from attacking the network with failed transactions.
Multisigning
We can add additional security to our account by authorizing transactions with a combination of multiple secret keys. We can put a requirement that multiple people need to sign the transaction for it to be valid. If we add Bob, Alice, and Ruth in the signer list and if Bob's account is compromised, the account is still safe, since transactions signed only by Bob are now invalid.
Consensus
Bitcoin uses the proof-of-work mechanism to prevent malicious users from spending Bitcoins they don't have. However, its mechanism is costly and slow since it uses an immense amount of energy. Ripple came up with a consensus mechanism that is cheaper and faster.
In order to validate a transaction, Ripple doesn't rely on central authority. Instead, it has made a set of rules that the nodes in the network must follow to agree and reach on a consensus on what must go on the permanent ledger. This set of rules are called the consensus protocol.
Important properties of the consensus protocol
The following are the properties of Ripple's consensus protocol:
- Every participant who uses the XRP ledger should agree on which transaction occurred in what order and what the resulting state is (an account balance is an example for the resulting state).
- A central authority is not required to confirm and validate transactions.
- The system will continue to validate transaction even if its people in the network decided to join, leave, or act maliciously.
- If a lot of people in the network misbehave, the network will stop making progress. This is to ensure correctness in the ledger.
- Unlike other blockchain-based currencies, confirming transactions in the ledger does not require people to waste energy.
Ledger versions
Similar to Bitcoin, XRP also processes transactions in blocks. These blocks are called ledger versions. They contain three components:
- State data: This contains values such as current account balance and other objects stored in the ledger. For example, Bob's Account Balance: 5 XRP, Alice's Account Balance: 10 XRP.
- Newly applied transactions: These are the set of transactions that were applied to the previous ledger and hence resulted in the current state (Bob sent $5 USD to Alice, Alice sent 30 XRP to Bob).
- Metadata: This contains information about the ledger and the preceding parent ledger. It includes values such as the ledger index and the cryptographic hash.
Validation
In the Ripple network, the participant can choose its list of validators. This list is called the Unique Node List. When a transaction reaches these validators, they take the previously confirmed or the validated ledger version as the starting point. Then they apply new transactions in the canonical order and share their results.
Here's an example of a confirmed block. Validators would use this as a starting point:
|
Confirmed Block No |
5 |
| Transaction 1 |
Alice Sent Bob $5 |
| Transaction 2 |
Bob sent Peter $20 |
| State |
Alice has $20, Bob has $30 |
Here comes a new set of transactions to be validated:
|
Alice Sent Bob $5 |
24 Sep 2018 09:12:17 |
|
Bob sent Peter $20 |
24 Sep 2018 10:12:17 |
If these transactions are applied according to in the order of their timestamp, the resulting state would be as follows:
| State |
Alice has $15, Bob has $15 |
The validators should arrive at the preceding conclusion. If they don't agree, then they would modify their proposal to match the validators they trust. This would continue in multiple rounds until they reach consensus. If 80% of the validators reach an agreement, then the transactions are confirmed and permanently added to the ledger. Otherwise, the ledger would stop making progress.
Advantages of Ripple
Now, let's have a look at key advantages of the Ripple cryptocurrency. These are the features that make it stand out among the other competitive currencies in the market.
Currency agnostic
Though the Ripple protocol has a native currency, XRP, it's not mandatory for users to transact only in XRP. It can transfer any item of value (fiat currencies, digital assets, and so on).
Simplified consensus
Unlike Bitcoin, Ripple has a simplified consensus or settlement mechanism. Once a transaction is signed and broadcasted, a selected number of Ripple servers reach a consensus on whether the transaction is valid or not. This process happens in 6 to 10 seconds. It can process around 1500 transactions per second; this is drastically higher than Bitcoin.
Low fee
Due to the simplified consensus mechanism and automated settlement, Ripple drastically reduces the transaction fee.
Reduced foreign exchange cost
The Ripple system is designed to select the cheapest bidder. This forces the market maker to make bids at competitive prices.
Pathfinding algorithm
Due to market limits, certain currencies cannot be exchanged directly. EUR/KRW is an example of such a currency that doesn't have a tight market. Hence, EUR needs to be exchanged for USD and USD needs to be exchanged for JPY and, finally, JPY can be exchanged for KRW. Ripple's system has a built-in pathfinding algorithm that would make the exchange by searching for the cheapest possible path.
Adaptable cryptography
Though the Ripple systems rely on time-tested encryptions such as ECDSA, it is also extendible to modern algorithms such as Ed25519. The system has the capability to add or disable algorithms. This is a great security feature, since if an encryption mechanism becomes obsolete, it can be replaced with a new one.
Anti-spam mechanism
In order to prevent spam requests on Ripple's ledger, while sending transactions a small amount of XRP must be destroyed. This fee is negligible for legitimate users, but can be costly for spammers who are trying to attack the network with bulk transactions.
Potential risks of Ripple
Now, let's look at the potential risks of Ripple. These are the few challenges Ripple would face to kick off as a currency.
- Regulatory issues
- Trust issues
- Security vulnerabilities
- Problems of being an open protocol
Regulatory issues
Certain countries such as India have banned cryptocurrencies and in certain countries laws on digital currencies are unclear. On the Ripple network, users are allowed to be anonymous. However, most governments are likely to have a problem with it.
Though governments cannot disable the XRP ledger, they can restrict people from buying XRP using fiat currencies such as USD and INR. In India, RBI has banned people from using credit cards to buy Bitcoins.
There are a lot of cryptocurrencies in the market with Ripple. Some of them are legitimate, some are scams. However, it would take time for the governments to understand the potential of cryptocurrencies. They would have a much harder time to distinguish the legitimate ones. Hence, it is hard to predict how the future of cryptocurrency will shape out.
Trust Issues
Ripple allows its users to transfer anything of value. This is accomplished with the help of issuers who link their assets to the XRP ledger. When users transact on the Ripple network, they have the option to trust these issuers.
However, if issuers misbehave and claim to have assets they don't have on the XRP ledger, it would lead to big problems. The issued currencies owned by users would lose their value overnight. This can affect people's trust in the Ripple network.
Security vulnerabilities
Security bugs are common in most online systems. However, a loophole in a distributed ledger can be fatal, since it can cause irreversible damage as data once confirmed is final and no one can alter it.
In Ethereum, bad coding has led to a loss of millions of dollars. Since Ripple limits the functionality on which a user can build on top of, there would be less room for vulnerabilities.
The question is, can Ripple continue to evolve without having any major security bugs?
Problems of being an open protocol
Ripple's code is totally free and open source. The problem with open protocols is that they can be forked easily. Bitcoin protocol was forked multiple times to create other currencies such as Bitcoin Cash and LiteCoin.
People can easily fork Ripple's code and build an advanced protocol that can compete with Ripple. Hence, partnerships are the key to Ripple's future. They need more financial institutions using the XRP ledger.
Summary
In this chapter, we learned the answers to the following questions.
- Why was decentralization necessary?
- What is blockchain?
- What is Bitcoin?
- What are the disadvantages of Bitcoin?
- What is Ripple?
- How does Ripple make international money transfers efficient?
- How does Ripple work?
- What are the key features of Ripple?
- What are the potential risks of Ripple?
Now that we understand how ripple works in theory, we will learn how to do some real transactions on Ripple's ledger in the next chapter.



















 Download code from GitHub
Download code from GitHub