A packet analyzer is also known as a packet sniffer or a network protocol analyzer. Packet analyzer has the ability to grab the raw packet from the wire, wireless, Bluetooth, VLAN, PPP, and other network types, without getting processed by the application. By doing so it brings the whole science and innovation to this field. In this chapter we will see a few use cases of the packet analyzer by covering the following topics:
Uses for packet analyzers
Introducing Wireshark
Other packet analyzer tools
Mobile packet capturing
More practically, packet analyzers are employed in network security and to analyze raw traffic so as to detect scans and attacks, and for sniffing, network troubleshooting, and many more uses, as shown in the following image:

Packet analyzers can be used as follows:
Network administrators can diagnose problems on a network
Security architects can perform a security audit on a packet
Protocol developers can diagnose/learn protocol-related issues
White-hat hackers can find vulnerabilities in the application and fix them before black-hat hacker find them
The use is not limited to these bullet point, there are lots of new tools and innovations happening in this area. Find a use case and build your own packet analyzer; the best example is Wireshark.
Wireshark is perhaps one of the best open source packet analyzers available today. Wireshark is a powerful packet analyzer tool, with an easy-to-use, rich GUI and a command-line utility with very active community support: http://ask.wireshark.org.
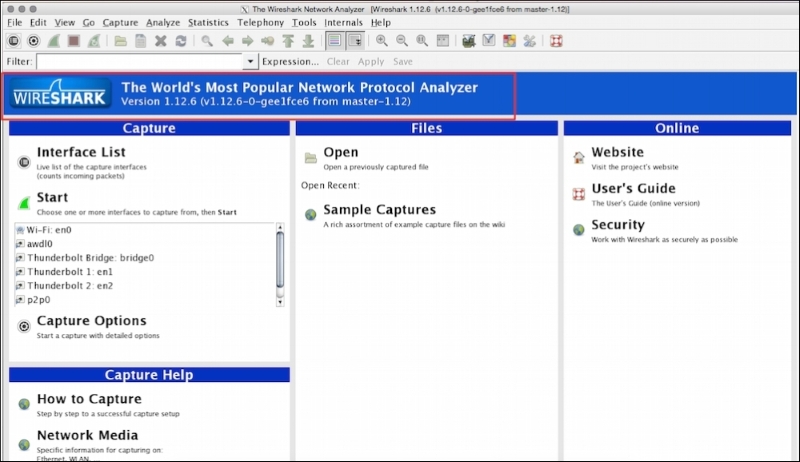
Wireshark uses pcap (libpcap) to capture packets, which means it can capture packets in offline mode—to view the captured packets—and online mode (live traffic) to capture and display the traffic in the Wireshark GUI. Once open, the Wireshark GUI looks like this:
We will see some of the important features that are available in Wireshark in the following figure:
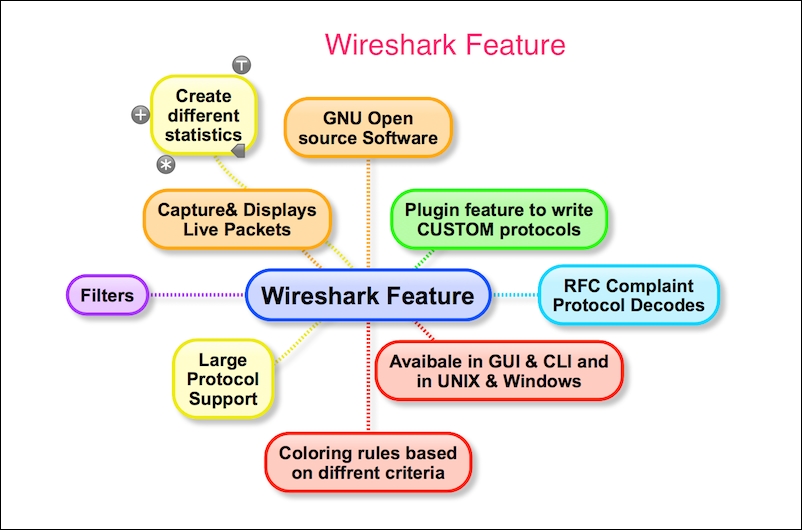
Wireshark has the following cool built-in features, few of them are listed as follows:
Ability to capture live packets from various types of interface
Filters packets with many criteria
Ability to decode larger sets of protocols
Can save and merge captured packets
Can create various statistics
User-friendly GUI and command-line interface
Active community support (http://ask.wireshark.org)
The Wireshark installation provides some command-line tools such as
dumpcap and tshark. Wireshark and tshark rely on dumpcap to capture traffic; more advanced functionality is performed by tshark. Also note that dumpcap can be run as its own standalone utility. tshark is a command-line version of Wireshark and can be used in the remote terminal.
The user must be aware of where Wireshark is installed and it should be obliged with your organization policy before start capturing on the TAP (Test Access Point) or Switch Port Analyzer (SPAN) port.
Usually developers install Wireshark on their personal laptop/desktop and capture packets, which goes in-out from the box.
Certain guidelines should be followed to perform this:
Make sure you're allowed to do what you're going to do; check your corporate policies before capturing a packet.
The operating system must support packet capturing:
Linux packet socket support is enabled in the kernel by default
Windows requires
WinPCapto be installed
Choose the interface and enable the promiscuous mode on it. Promiscuous mode accepts all packets whether they are addressed to the interface or not.
If using a Wi-Fi interface, enable the monitor mode for WLAN capturing.
Start capturing and use Wireshark's different features like (filters/statistics/IO/save) for further analysis

Wireshark is a packet analysis tool to use features such as packet editing/replaying, performing MITM, ARPspoof, IDS, and HTTP proxy, and there are other packet analyzer tools available and can be used as well.
The following is a list (not limited) of notable packet analyzer tools on the market; many others are commercially available. The table lists tools and their features:
|
Tools |
Packet editing |
Packet replay |
ARPspoof/MITM |
Password sniffing |
Intrusion detection |
HTTP debugger |
|---|---|---|---|---|---|---|
|
WireEdit (https://wireedit.com/) |
Y |
N |
N |
N |
N | |
|
Scapy (http://www.secdev.org/) |
Y |
Y |
Y |
N |
Y | |
|
Ettercap (https://ettercap.github.io/ettercap/) |
Y |
N |
Y |
Y |
N |
N |
|
Tcpreplay (http://tcpreplay.synfin.net/) |
N |
Y |
N |
N |
N |
N |
|
Bit-Twist (http://bittwist.sourceforge.net/) |
Y |
N |
N |
N |
N |
N |
|
Cain (http://www.oxid.it/cain.html) |
N |
N |
Y |
Y |
N |
N |
|
Snort (https://www.snort.org/) |
N |
N |
N |
N |
Y |
N |
Wireshark is not available on mobile platforms such as Android, iOS, or Windows. In order to capture mobile traffic the following tools are suggested based on the platform:
|
Platform |
Packet capture tool used |
URL |
|---|---|---|
|
Windows |
Microsoft Network Analyzers |
http://www.microsoft.com/en-in/download/details.aspx?id=19484 |
|
iOS |
Paros | |
|
Android |
Shark for Root | |
|
Kismet Android PCAP |
Various other techniques are used to capture mobile traffic using Wireshark. One such technique is creating a Wi-Fi hotspot on the laptop, allowing the mobile phone to use this Wi-Fi, and sniffing traffic on your Wi-Fi interface using Wireshark.
In this chapter we learned what packet analyzers are and what their use cases are. After a quick introduction to Wireshark, we covered what goes on behind-the-scenes when Wireshark captures packets; Wireshark benefits and important features; the necessary prerequisites before capturing packets; and other packet analyzer tools for packet editing/sniffing/replaying and so on. We also provided a brief overview of mobile packet capturing.
The next chapter will be more specific to Wireshark and its tips and tricks. After that we will explore TCP troubleshooting, then plunge into SSL, and other application protocols such as DHCPv6, DHCP, DNS, and HTTP. We will also analyze Wi-Fi capturing and carry out some security analyses with the help of Wireshark and tcpdump.