Understanding the Network Architect’s Role
Today, the network infrastructure (or fabric as I like to call it) is vast compared to how it was just 23 years ago, and even more sophisticated than when networks were around in the early 1970s. The infrastructure has evolved, and so has the people required to take care of and maintain them. But even in doing so, the role and responsibility have also evolved to be more. Before, the responsibility could have seen one or two people doing everything, such as racking and stacking, cabling, router configurations (as there were no switches at the time), installing hubs, and storage consolidation. Now, there are many roles in an organization that specialize in these varied tasks.
So much emphasis is put on the various roles within an organization when it comes to the IT business unit versus the IT department. Let’s not confuse the two – the IT department is your desktop/laptop support team who can grant you access to various services, while your IT business unit is responsible for making sure that your various lines of business are functional and sustainable to generate revenue for your organization. The latter encompasses the network architect.
In this chapter, we’re going to cover the following main topics:
- What is a network architect?
- The function of a network architect
- Understanding network architecture
Let’s get started!
What is a network architect?
The network architect is vital to an organization’s sustainability within their industry’s vertical. A network architect is one of many architects that an organization has.
Here’s my twist on the definition of the network architect:
Before diving into what a network architect does in an organization, a brief articulation of other architects that you’ll find in an organization will help to discern the difference from that of a network architect. Each has unique technical skills to address business needs, goals, and complexity. Moreover, there will be some overlap in tasks, deliverables to an organization, responsibilities, and maybe even KPIs.
KPIs
Key Performance Indicators (KPIs) are used to evaluate the success of an organization/team or a particular activity they are engaged in.
Solutions architects
Solution architects evaluate the requirements from the line of business (LoB) and determine what solution(s), whether it be products or services, can be used to meet or fulfill those requirements.
They design, describe, and manage the solution. This includes the networking (fabric) aspects, the storage aspect, database systems, security, and the overall scheme that will be deployed. In some ways, the solutions architect (SA) bridges a business problem and the technology solution. Additionally, the SA outlines each of the desideratum and the phases to make that solution work, after which they must confer with the other architects in the organization to validate the design feasibility.
To some degree, SAs create the overall technical vision for a specific solution to a (specific) business problem. I say to some degree because an organization’s overall IT/technical vision comes from the Chief Technical Officer (CTO).
Storage architects
A storage architect builds central database systems; one such system is a Configuration Management Database (CMDB), which holds the most crucial business information for an organization. Some crucial information includes (but is not limited to) finance, compliance, accounting, and human resources.
They typically design based on the SA’s findings, install new data storage systems using different software and various hardware, liaise with IT experts, and identify storage requirements to meet the needs of business units.
Examples of storage architects’ designs include the following:
- FC zoning
- SAN and vSAN
- NAS, NFS, and SMB shares
Some routine operations can include analyzing data, potential issues, frequency of updates, maintenance, and hardware/software Service Level Agreements (SLAs). Storage architects also need to communicate critical information to clients (internal or external) or an organization’s management team.
The role of a storage architect can vary, depending on the organization itself and what they’re looking for in the architect, but the storage architect’s main task is to design a stable, reliable, and resilient storage architecture.
Database architects
A database architect’s (DBA’s) function is to understand an organization’s main needs for data and its current data infrastructure. DBAs in some respects work closely with storage architects.
After taking the needs of an organization and conversing with the SA (and other stakeholders), the DBA analyzes the organization’s priorities and goals, assesses whether the current data infrastructure is design-feasible, and then determines where changes should and must be made.
They must design the database’s infrastructure to ensure that it’s scalable, secure, reliable, and, like other designs, cost-effective.
Depending on a country’s boundaries and compliances, DBAs must also ensure that a database meets any regulations and standards, especially when dealing with sensitive data.
Enterprise architects
An enterprise architect (EA) is somewhat similar to an SA. While the SA is charged with defining the correct services/infrastructure to meet the BU’s needs, the EA is responsible for the upkeep and maintenance of those services/infrastructure.
They’re also responsible for improving and upgrading enterprise services (e.g., CRMs, HRMs, and PoS systems), software, and hardware.
Like the SA, EAs must have a wide view and scope (vision) of what’s happening within an organization, as well as being abreast of new trends and technologies, and any software services or hardware that might improve business processes.
Cloud architects
As you may have guessed, a cloud architect is involved with cloud computing. Their function is to oversee an organization’s cloud adoption strategy. Cloud architects oversee application architecture and deployment in cloud environments, including the public cloud, private cloud, and hybrid cloud. Additionally, they act as consultants to their organization and also need to stay abreast of the latest trends and issues (https://www.techtarget.com/searchcloudcomputing/definition/cloud-architect).
Cloud architects must understand application owners’ and application developers’ needs and requirements. Then, they must survey how to closely replicate it, if possible, in a cloud-centric environment based on what’s already allocated and consumed on-premises. The premises can be an organization’s leased space, owned property, or IT setup, solely owned by that organization, which would then be migrated.
In all cases, the cloud architect has to determine whether the application (workload) fits into one of Gartner’s five Rs of migrating applications into the cloud (Migrating Applications to the Cloud: Rehost, Refactor, Revise, Rebuild, or Replace?, available at https://www.gartner.com/en/documents/1485116)
The following diagram is a cloud migration strategy currently used by AWS, based on Gartner’s original five Rs:

Figure 1.1 – AWS’s version of Gartner’s five Rs of cloud migration strategies (source: https://aws.amazon.com/blogs/enterprise-strategy/new-possibilities-seven-strategies-to-accelerate-your-application-migration-to-aws/)
Technical architects
While other architects may be broad(er) in scope, technical architects (TAs) are more specific. They take the most hands-on approach during the execution of IT projects and focus mainly on a single implementation for a specific domain that they’re, technically, inclined for. An example would be a TA who is extremely familiar with SAP, MongoDB, Python, or even Cisco.
Because of this, TAs produce best practice strategies utilized by an organization, which, in most cases, are used by other IT architects during their development and strategy sessions for their own solutions.
Out of all the IT architects, TAs are the closest to an organization’s end user. Thus, they have to ensure that the technology is not only delivered on time but is fully functional for the end user (https://rb.gy/uw31fb).
Chief architects
Depending on the organization, the chief architect (CA) may oversee and coordinate the efforts of other technology-specific architects, including the chief security architect, the chief data architect, the chief mobile architect, and the chief cloud architect.
A CA is primarily a leader and communicator. They need to understand and influence the business strategy and lead the development of an architecture strategy that supports and enables that strategy (https://www.redhat.com/architect/what-is-chief-architect). A CA can also be referred to as an EA, as defined previously.
In addition, there are other architect roles, such as the following:
- Application
- Migration
- Security
- Automation
- Site Reliability Engineer (SRE)
- Software
The role of every architect in IT is directly related to the added complexities of information technology, and the need for a strategic top-down approach to the management of shared data and processes.
There can be varying degrees of overlap with some or all of these IT architects in an organization. Many are structured differently when it comes to who owns what, who’s in charge, or who has the last say and signs things off.
Relatively speaking from my experience, this is what I came across from a hierarchy perspective:

Figure 1.2 – The IT architect hierarchy in an organization
As I said before, there are not only overlaps in job function and responsibility but also overlaps when it comes to the roles within an organization, including business-centric, operations-centric, or even vendor and application-centric roles.
In general, the role of an IT architect is to ensure that an organization’s IT systems are aligned with its business objectives and able to support its operations effectively.
Network architects
A network architect is mainly responsible for designing, managing, and implementing an organization’s data communication networks, including the computer networks that support their IT systems, storage networks, and the internet edge. This means the network architect is responsible for the following:
- Designing local area networks (LANs), wide area networks (WANs), and intranets for organizations
- Designing the data and storage area networks (SANs)
- Both the hardware and software components of a network
- The policies and procedures that govern its use
While other IT architects may have a more general focus and be responsible for designing and implementing the overall IT infrastructure of an organization, a network architect must be fully embedded and have the required knowledge of many different network technologies (platforms) related to network routing and switching, networking protocols, network hardware and software, and the latest trends.
The network architect does overlap with the other architects mentioned. They also need to fully understand a business’s operations and its operating model, which is discussed in Chapter 4. It’s prudent to say network architects do not operate in siloes and should be a part of any meeting that requires a change, addition/removal, request, or ideation for an organization’s network (fabric) infrastructure.
Now that we have a general overview of the various architects in an IT organization, let’s talk more in depth about the topic this book is dedicated to, the network architect.
The function of a network architect
The function of a network architect is characterized by their responsibilities, which can vary, depending on the specific organization and the size and complexity of their network. However, some common functions/responsibilities of a network architect might include the following:
- Designing and planning the overall architecture of an organization’s network, including its physical and logical layout
- Selecting and configuring the hardware and software components that make up the network, such as switches, routers, protocols, and firewall appliances
- Implementing and maintaining network security measures to protect against external threats and unauthorized access
- Ensuring the network is scalable, agile, flexible, and able to handle growing demands from business units
- Monitoring the performance of the network and identifying and troubleshooting any issues that arise
- Developing and implementing policies and procedures for the use of the network
- Collaborating with other IT professionals, such as system administrators and application developers, to support the overall IT infrastructure of the organization, and other architects to express opinions about design concerns, constraints, and success
- Articulating business needs to the leadership
- Managing vendor relationships and working with external contractors or service providers as needed
- Staying up to date with the latest technologies and trends in networking and evaluating their potential impact on the organization’s network
A network architect may also be responsible for designing and implementing specific subsystems within a network, such as the data center, the campus network, the metro network, and other private network systems.
In most cases, these responsibilities are completed standalone, meaning without validation or approval from other IT architects. Generally speaking, activities, concerns, or anything similar are brought up during a stand-up or regularly scheduled IT meeting.
In summary, a network architect is responsible for the overall design, implementation, and maintenance of an organization’s computer networks. They play a key role in ensuring that a network is reliable, secure, and able to support the needs of an organization.
Understanding network architecture
Network architecture refers to the overall design of a computer network, along with other auxiliary networks. It includes the hardware, software, and protocols that make up the network, as well as the physical and logical layout of the network and the relationships between the various components.
Network architecture should be designed to support the needs and goals of an organization, taking into account factors such as the size of the network, the types of devices and applications that will be traversed across, the number of end users (consumers), the level of security required, and the availability and performance requirements.
The architecture must be able to support the current organizational needs (from the various lines of businesses, stakeholders, leadership, and end users), be flexible for future growth, meet multiple degrees of SLx (such as SLAs and SLOs), and be agile to support shifts in the market, all the while maintaining a cost balance between CapEx and OpEx.
There are many different approaches to designing network architecture, and the most appropriate one will depend on the specific needs and constraints of an organization. Some common types of network architectures include the following:
- Client-server architecture, in which one or more central servers provide services to multiple clients
- Peer-to-peer architecture, in which all devices on a network are able to communicate directly with each other
- Hierarchical architecture, in which a network is divided into multiple layers, each with a specific function
- Hybrid architecture, in which multiple different architectures are combined in order to meet the needs of an organization
- Spine-leaf architecture, to take advantage of high-speed throughput for east–west traffic and a higher level of redundancy
Let’s take a closer look at these architectures.
Client/server architecture
The client/server architecture is a computing model in which the server hosts, delivers, and manages most of the resources and services requested by the client.

Figure 1.3 – An example of a client/server architecture
It’s also known as a networking computing model or client/server network, as all requests and services are delivered over a network. Client/server architecture is a common way to design and implement computer systems. It is used in a wide variety of applications, including web applications, email systems, and database management systems.
These systems can be HR, CMDB, network (fabric) monitoring and logging, or storage systems.
Multiple clients’ requests are made to and from a central server. The server is responsible for handling requests, processing data, and providing a client with the requested information. The client, on the other hand, initiates the request and displays the received data to the user. This architecture is commonly used in distributed computing, where a centralized server manages and distributes data to multiple clients over a network.
The communication between the client and the server typically occurs over a network, such as the internet, and follows a request-response model. Clients make requests to the server for specific services or data, and the server processes those requests and returns the requested information to the clients.
Typically, in a client/server architecture, the client computer is responsible for the user interface. The client computer displays information to the user and accepts input from the user. The server computer is responsible for the data. The server computer stores data and processes data requests from the client computer.
A common example of a client-server architecture, used every day, is a web application. In this case, the client is a web browser (such as Chrome or Firefox) that runs on a user’s computer, and the server is a computer or group of computers that host the web application and store the files and databases that the application uses. The client sends requests to the server (such as to load a web page or submit a form), and the server responds by sending the requested data back to the client.
The following is a request made by a client to reach to load my blog site at www.ahaliblogger.tech.
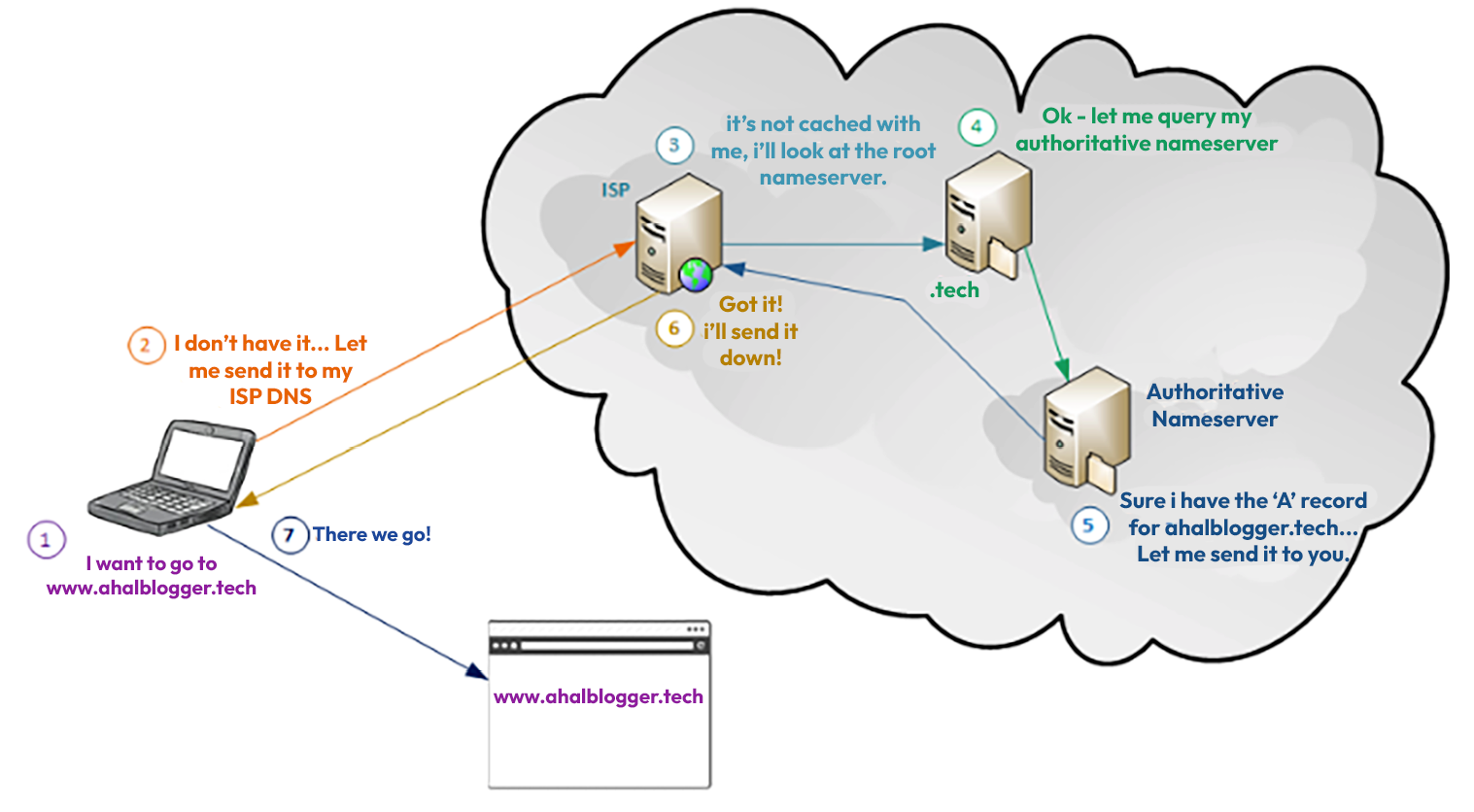
Figure 1.4 – A DNS request flow to ahaliblogger.tech
In the diagram, a client makes a request to reach ahaliblogger.tech. As the request flows through several DNS servers, an authoritative server responds to the client with the proper information.
Client/server architecture has several advantages over other computing models. One advantage is that it is scalable. The systems can be easily expanded to accommodate more users. Another advantage is that it is reliable. Client/server systems are less likely to fail than other networking computing models.
However, client/server architectures also have some disadvantages. One disadvantage is that it can be complex to design and implement. Another disadvantage is that it can be expensive to maintain.
Peer-to-peer architecture
A peer-to-peer (P2P) network architecture is a type of network in which each computer or device (known as a peer) is able to act as both the client and the server. This means that each peer is able to both request and provide a response to other peers on the network, without the need for a central server or authority to manage the network.
Peer-to-peer networks are often decentralized and self-organizing and can be used for a wide range of applications, including file sharing, online gaming, and distributed computing.
An example of a peer-to-peer network architecture is a BitTorrent file-sharing network.

Figure 1.5 – How BitTorrent works
In this network, clients (peers) share files with each another by breaking the files into small pieces and distributing them across the network. The (BitTorrent) client contacts a “tracker” specified in the .torrent file (https://www.howtogeek.com/141257/htg-explains-how-does-bittorrent-work/).
Each client is able to download pieces of the file from multiple other peers and can also upload pieces of the file to other peers. This allows the efficient distribution of large files, as the load is distributed among many users rather than relying on a central server.
Hierarchical architecture
Hierarchical network architecture is a type of network design that uses a multi-layered approach to organize and manage network resources. It separates a network into distinct layers, where each layer has a defined function that, in turn, defines its role in the network. These layers are the access layer, the distribution layer, and the core layer.

Figure 1.6 – The three-tier network architecture model
The preceding diagram illustrates each layer in the hierarchical architecture model.

Figure 1.7 – The access layer of the three-tier hierarchical architecture model
The access layer is the point of entry into a network, and it is where end user devices such as computers, servers, printers, VOIP phones, and other IP devices connect. The access layer is responsible for providing basic (and, at times, more complex) connectivity and controlling access to the network.

Figure 1.8 – The distribution layer of the three-tier hierarchical architecture model
The distribution layer is where a network is divided into different segments or VLANs, and it acts as a bridge between the access and core layers. This layer is responsible for routing and filtering traffic, and providing security and Quality of Service (QoS) features.

Figure 1.9 – The core layer of the three-tier hierarchical architecture model
The core layer is the backbone of a network, and it is responsible for the high-speed switching and routing of traffic between different segments of the network. This layer is designed to be highly available and redundant, providing a fast and efficient data transfer throughout the network.

Figure 1.10 – The collapsed core model
The preceding diagram shows a variation of the hierarchical architecture, where the distribution and core layers are combined into what is known as a collapsed layer. In this design, the core and distribution functions are performed within one device (or a pair of devices).
The hierarchical design allows for better scalability, security, and manageability. Separating the different functions into specific layers also allows for better troubleshooting, as the network administrators can easily identify the problem area by looking at the specific layer.
The most common hierarchical architecture used in today’s network is spine/leaf.
Hybrid network architecture
Hybrid network architecture is a type of network architecture that combines elements of two or more different types of network architectures. The most common types of network architectures that are combined in a hybrid network are peer-to-peer (P2P) and client-server (C/S) architectures.
In a hybrid P2P/C/S network, a network is made up of both clients and servers, but the clients also have the ability to act as servers. This allows for network resources to be used more efficiently and can provide a better user experience, as data can be shared and distributed more easily.
For example, a hybrid P2P/C/S network might be used in a file-sharing application, where users can upload and download files from a central server but also share files directly with one another.
Another example would be combining the use of both wired and wireless connections. This allows a more flexible and reliable network – for example, a wireless connection can be used for mobile devices, while a wired connection can be used for more demanding applications such as video conferencing.

Figure 1.11 – An example of hybrid architecture – wireless and wired
A more common approach to hybrid network architecture is distributed computing systems, where a combination of cloud computing and edge computing is used. This allows data processing to take place at the edge of the network, close to the source of the data, while still giving you the ability to offload to the cloud for more processing power and storage.
An example is Tesla’s self-driving car. The car’s sensor constantly monitors certain regions around it, detecting an obstacle or pedestrian in its way, and then the car must be stopped or move around without hitting anything (https://www.geeksforgeeks.org/difference-between-edge-computing-and-fog-computing/). The vehicle must process the data quickly to determine what needs to be done next and also send it to backend systems (cloud or on-premises), where it is put in a data store (i.e., Hadoop clusters or cloud buckets). At this point, the data can be processed for further analysis, such as ETL processing or AI/ML pipelines.
The following diagram illustrates the use of edge devices in hybrid network architecture.

Figure 1.12 – Hybrid architecture – edge computing to cloud computing
Hybrid network architectures can provide the best of both worlds, the flexibility of P2P and the central control of C/S, and it can also allow for more efficient use of resources, better security and scalability, and a better user experience.
Spine-leaf architecture
A spine-leaf network architecture is a type of data center network architecture in which all devices are connected to leaf switches, which, in turn, are connected to spine switches.
The leaf switches provide end devices with access to a network, while the spine switches provide high-speed interconnections between the leaf switches. This architecture creates a flat, non-blocking network that allows efficient communication between devices and provides high redundancy.

Figure 1.13 – Spine-leaf architecture
The architecture can also be easily scaled to support a large number of devices and high throughput. The purpose of this architecture is to provide a cost-effective, scalable, and high-performance solution for modern data centers.
Summary
A network architect falls under the umbrella of the many architects that an organization may have, and it is vital to any organization’s success. The role and function of the network architect are more specific than that of a CA or SA but just as important when understanding the needs and requirements of stakeholders, end users, and leadership within an organization.
The network architecture is just as vital, as it’s the backbone of the entire organization. The design determines its flexibility, capacity to change, ability to introduce newer technologies and decommission older systems, and whether it is agile enough to support market changes in an organization, while simultaneously supporting end user requests for resources and services.
In the next chapter, we’ll dive deeper into the network architect in an organization.
Further reading
- Why Networks Are Evolving Toward Leaf-Spine Architectures: https://www.networkcomputing.com/networking/why-networks-are-evolving-toward-leaf-spine-architectures/
- Multitier architecture: https://en.wikipedia.org/wiki/Multitier_architecture
- Cisco Networking Academy Connecting Networks Companion Guide: Hierarchical Network Design: https://www.ciscopress.com/articles/article.asp?p=2202410&seqNum=4



















 Download code from GitHub
Download code from GitHub
