Addressing Cybersecurity in the Age of Industry 4.0
We are seeing fast-paced digital transformation in all industries, including the operational technology (OT) and Internet of Things (IoT) industries.
The different eras of industry, as seen in Figure 1.1, have brought significant changes in the ways businesses work. Revolutionary changes within the way that industries operate have been brought about by manufacturing companies becoming more secure, efficient, productive, and profitable:

Figure 1.1 – The different eras of industrial revolution
The computing technology of Industry 4.0 is powered by a connected network and has a digital twin on the internet too. This enables communication and information sharing. This networking is sometimes referred to as a cyber-physical production system. This makes organizations and industries more autonomous. First, let us look at how Industry 4.0 came to be:
- Industry 1.0: innovations of steam power and mechanical engines in Industry 1.0 led to the faster conveyance of goods and people, resulting in enormous time savings.
- Industry 2.0: Electrical power and electronic assembly brought down the cost of production and business became more profitable and agile to demands.
- Industry 3.0: With computers and programming logic, businesses started automating complete assembly lines; so, parts were built faster as the assembly line system became more efficient at performing tasks. However, during this revolution, things remained human-driven and machine-executed. The fast pace amazed consumers and businesses.
- Industry 4.0: This revolution was built on top of Industry 3.0, in which isolated devices were connected through computer networks. Meanwhile, manually driven operations were converted into fully automated and integrated systems with digital twins on the internet to simulate different tasks on devices. The entire field was positively impacted by all the insights incorporated from demand to supply. Connected devices brought more intel.
The entire journey from Industry 1.0 to 4.0 has made business more profitable, agile, and cost-effective. Automation and intelligence have also introduced visibility into the demand and supply of raw materials and enhanced the quality of finished products. Businesses are now more empowered by all the intelligence derived from the system to make the right decisions.
Microsoft presently invests over $5 billion in IoT research and is a pacesetter regarding this new technology, thus contributing to the overall Industry 4.0 revolution. Microsoft Defender for IoT (MDIoT) is accelerating this digital transformation for organizations, with comprehensive security across IoT or OT infrastructure. MDIoT provides agentless network detection and response (NDR). The technology is rapidly deployed and works with various IoT, OT, and industrial control systems (ICS). For IoT device producers, MDIoT provides a lightweight agent to enhance device-level security. It is a solution that interacts with Microsoft 365 Defender, Microsoft Sentinel, Microsoft Defender for Endpoint, devices, and external security operations center (SOC) tools. It can be deployed on-premises, in a hybrid setup, or via the cloud. MDIOT covers the IoT, OT, and the Enterprise Internet of Things (EIoT). This book focuses on securing OT.
Before we get to that, though, in this chapter, we will cover the following topics:
- How is Industry 4.0 being leveraged?
- Understanding cybersecurity challenges in the age of Industry 4.0
- Enumerating the factors influencing IoT/OT security
- How to overcome security challenges
How is Industry 4.0 being leveraged?
The power of artificial intelligence (AI) tools has led to the evolution of Industry 4.0. Various sectors—such as manufacturing, healthcare, finance, the public sector, consumer goods, retail, and smart city planning and building—use intelligent machines to help subject matter experts (SMEs) streamline processes, thus helping to meet highly competitive industry demands. How is this leveraged by different industry verticals?
The following figure describes how Industry 4.0 is leveraged by different industry verticals:
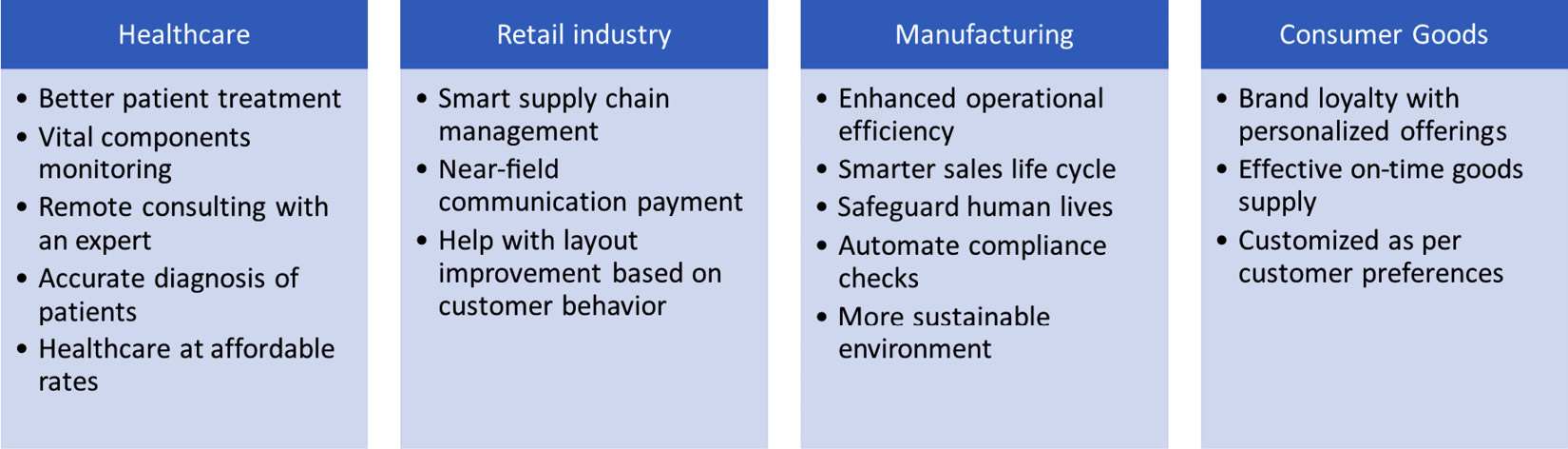
Figure 1.2 – Industries leveraging industry 4.0
The factors that are common across all verticals are the reduced cost of operations and enhanced customer experience, ultimately making companies more secure, efficient, productive, and profitable.
Now that we have seen some of the verticals leveraging and benefiting from Industry 4.0, we can go into detail regarding how these industries operate in the real world. In the real world, the convergence of information technology (IT) and OT brings about new challenges to conquer – that is, cybersecurity – and this convergence is bound to happen in pursuit of better business results, profits, data analytics, and much more.
Let us quickly learn a few basic terms:
- OT is hardware and software that detects or causes a change through directly monitoring and/or controlling industrial equipment, assets, processes, and events.
- The IoT is the concept of interconnected computer devices, mechanical and digital machines, objects, animals, or people, armed with unique identifiers (UIDs) and the ability to transmit data over a network, without intervention or computer interaction.
- The EIoT refers to how digital transformation and enterprise strategies being connected enables seamless collaboration between people and technology. It also provides more insight and improves the productivity of an enterprise by reducing the amount of manual work and optimizing business outcomes.
- The Industrial Internet of Things (IIoT) refers to the expansion and use of the IoT in industrial applications. It focuses strongly on machine-to-machine (M2M) communication, big data, and machine learning (ML). The IIoT enables industries and businesses to make their operations more efficient and reliable. It encompasses industrial applications, including robotics, medical devices, and software-defined manufacturing processes.
- Supervisory control and data acquisition (SCADA) is a control system architecture that includes computers, networked data communications, and graphical user interfaces to monitor machinery and processes at a high level. This includes sensors and other devices, such as programmable logic controllers (PLCs), that are connected to process systems or machines.
- A distributed control system (DCS) is an automated control system for a process or plant, usually with many control loops, in which self-contained controls are distributed throughout the system, but there is no centralized operator supervision. This is in contrast to systems with centralized controllers, discrete controllers in a central control room, or a central computer. The DCS concept increases reliability and reduces installation costs by placing control functions close to the process installation with remote monitoring.
The following figure provides more insight into the convergence of IT and OT, along with the IoT:
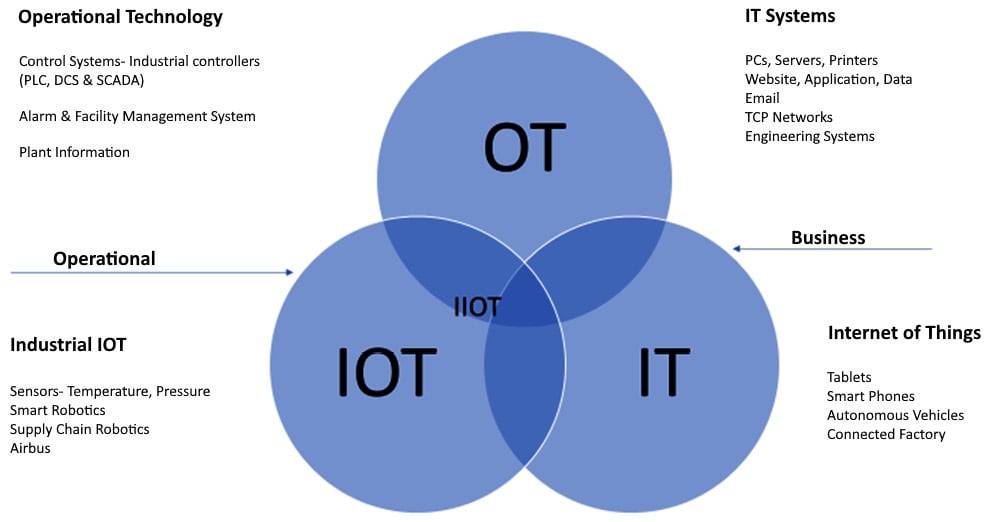
Figure 1.3 – Convergence of IT, OT, and the IoT
While OT covers control systems such as PLCs and DCS, IT covers PCs, servers, websites, and applications hosted within the organization or leveraged by an organization. The IT industry focuses on data while OT is focused on operations and the IoT focuses on M2M communication over the internet.
The IIoT industry, on the other hand, is about the use of smart sensors and actuators to enhance the outcome of industrial processes. This represents the intersection between OT and the IoT.
The legacy model of operation for organizations required IT and OT to be isolated. However, the convergence of IT and OT has brought about a successful transformation for the OT and IoT industries.
The IoT has already crossed the nascent stage and it has become mainstream. In fact, the number of IoT devices has already surpassed the number of IT devices. This proliferation of IoT devices has brought about increased attention, and adversaries and threat actors have already started targeting them for quick monetary gain by exploiting their vulnerabilities.
Industry 4.0 has three important stages:
- Digitization: Digitized outputs that are connected to industrial assets lead to the convergence of the digital and physical worlds. Connecting digitized outputs to security information and event management (SIEM) solutions can provide visibility to all incidents and actions in real time.
- Sensorization: Adding sensors to industry processes helps bring about better interconnection. This enables the autodetection of issues or changes in temperature, pressure, humidity, and so on, as it helps ascertain that the continuous monitoring of inputs and any sudden changes to them is in place. This prevents mishaps, too.
- Optimization: With the AI and ML world we live in, data analytics is leveraged to improve business and process outcomes. Leveraging data analytics and simulations leads to optimized results, which bring about profits for the organization through the management of time and effort.
So far, we have understood the impact of and the blazing changes brought in by Industry 4.0, and how a connected world and its disruptive technology (the use of AI and ML) have changed our future trajectory in general.
Understanding cybersecurity challenges in the age of Industry 4.0
It is a known fact that cybersecurity breaches in any industry negatively affect business outcomes, and this is still a concern in the age of Industry 4.0. Cyberattacks on critical industrial equipment hamper businesses. Digitization is driven by four kinds of disruption:
- The astronomical rise in data volumes: As everything moves toward digitization, we can imagine the wealth of data generated as a result, thus making it easy for an attacker to intercept data and steal intellectual property (IP) as the amount of data that needs to be protected against threats and malware increases.
- Forever-increasing computational power: The job of attackers gets easier every time we see an increase in computational power. Quantum computing has increased our computational power manifold. This has empowered attackers to break or crack open more boundaries and types of authentication faster.
- A super-connected world (connected vehicles, airbuses, heart defibrillators, etc.): The attack surface has increased to an extent that it can now affect human life as well. Thinning down network segmentation, collecting data from sensors, and sending it for further processing have contributed to an increased attack surface.
- A data (AI and ML) world (deep insights, business intelligence, and analytics): Analytics are key for any organization to thrive today. While data brings about more business intelligence and provides opportunities for businesses to take calculated steps toward success, if infiltrated, these insights and intelligence fall directly into the hands of an attacker.
As a lot of industries adapt to Industry 4.0, they have become an appealing target for attackers. Attackers jump across IT and OT laterally on the lookout for vulnerabilities to exploit them, paving the way for industrial espionage, IP leakage, or IP theft.
The improved connectivity between and the convergence of OT and IT have increased the attack surface. This also requires that the compliance requirements of every industry be retouched to meet the ever-growing security requirements.
We are here to address this challenge and aid organizations in line with Industry 4.0 to protect their infrastructure from attacks continuously. We can do this with MDIoT. We will see more about MDIoT in upcoming chapters.
Cybersecurity challenges are ever-increasing, and the few that affect the IoT/OT world that we have mentioned are just examples to get us started on this journey to understand the challenges and how to address them better with MDIoT.
Enumerating the factors influencing IoT/OT security
Attacks on internet devices have increased manifold in recent years and are commonplace now. The reasons for this are the following:
- Weak credentials: How often have we ignored notifications to change our default passwords? We cannot forget the Mirai botnet attack, which made use of default usernames and passwords of this kind.
- Legacy software and hardware: We don’t always see IoT devices being updated. With the pace at which technology is growing, it becomes very easy for attackers to find weaknesses. Hence, it is of paramount importance to always update devices.
- Proprietary protocols and the complex structure of OT devices: With so many types of devices in use, we can only imagine the many proprietary protocols and the complex structures they would bring in. Siemens, Schneider, ABB, Rockwell Automation, and so on all use closed protocols.
- Anomalous operational events: Operations such as start, stop, and restart are all priority commands for Retentive Timers (RTOs), PLCs, actuators, and so on. Hence, it becomes a priority to clearly distinguish legitimate events from anomalous events.
These are some of the obvious factors that affect IoT/OT security. As we proceed further through the book, we will see more of these factors and how MDIoT addresses the challenges involved.
How to overcome security challenges
IoT/OT security should focus on providing visibility into the landscape of connected devices within an organization while going by the principle, “If you do not need the device at all, do not have it!” Reduce your attack surface.
However, if you do need a device, ensure that you have an accurate asset inventory. If you do not know the assets owned by your organization, you do not know what to protect—especially in a decentralized environment with multiple IoT/OT devices:

Figure 1.4 – Approach to securing an IoT/OT infrastructure
A trusted computing base (TCB) or a security baseline approach is a basic requirement and a necessity in today’s world to harden the infrastructure. We close many exploits that could be open if we plan our baseline security well.
Vulnerabilities on devices such as ICS and SCADA need to be addressed and may require working closely with vendors to always be on top of patching. Zero-day vulnerabilities can pose a huge risk and need to be identified and mitigated immediately by looking out for indicators of compromise. Since we are talking about vulnerabilities, we can already imagine having focused patching for all enterprise-wide devices. The IoT, OT, and IT are all crucial, and taking a piecemeal approach to patching is a recipe for disaster.
Continuous monitoring is key for any security-focused organization. An organization focused on monitoring its IoT/OT assets one day that then lapses the next day will not really be effective at thwarting any attacks coming its way. With so many focused and agile attackers capable of even engaging in nation-state attacks, you need to ensure that your monitoring is always turned on and that alerts are sent to the SOC team in near real time as well.
This section provided more perspective on a holistic approach that you can take to securely manage IoT/OT devices.
Summary
In conclusion, there are multiple ways you can secure your organization holistically (IT, OT, the IoT, and the IIoT). In this chapter, you have seen the evolution and adoption of Industry 4.0 and how it has affected the cybersecurity landscape of IoT/OT devices. There are multiple approaches to adopting secure practices for the IoT or OT that organizations can take, and we have discussed some of the best approaches. To top it off, you can always look at defense in depth to ensure you have a backup security mechanism and are covered in the case of any failures.
In the next chapter, we will look at the network architecture of IoT/OT devices and how this affects cybersecurity when it is not managed well.



















 Download code from GitHub
Download code from GitHub