Getting Started
Every few years there are technological innovations that change the entire landscape and ecosystem around them. If we go back in time, the 70's and 80's was a time of mainframes. They were huge in size, practically occupying large rooms and almost all computing work was carried out by them. It was difficult to procure one and it was also time-consuming. Enterprises used to order months before they could have an operational mainframe set up.
The first part of the 90's was the era of personal computing and the internet. Computers became much smaller in size and were comparatively easier to procure. Both personal computing and internet innovation changed the entire computer industry. People had a desktop through which they could run multiple programs and could connect to the internet. The rise of the internet also propagated the rise of client-server deployments. Now, there could be centralized servers hosting applications and services that could be reached out by anyone who had a connection to the internet globally. This was also when server technology got a lot of prominences. Windows NT, Windows 2000, and Windows 2003 were launched during this time.
The most remarkable innovation of the 2000's was the rise and adoption of devices, especially smartphones, and with them came a plethora of apps. Apps could connect to centralized servers on the internet and could carry out business as normal. Users were no longer dependent on browsers to make this work. All servers were typically either self hosted or hosted with a service provider, such as an Internet Service Provider (ISP).
Users did not have much control over their servers. Multiple customers and their deployments were part of the same server even without customers knowing about it.
However, there was something else happening towards the mid and later parts of the 2000's. This was the rise of cloud computing and it again rewrote the entire landscape of the IT industry. Although, initially the adoption was slow and people approached it with caution either because the cloud was in its infancy and yet had to mature or people were having multiple varied diverse notions about it.
Nevertheless, today cloud computing is one of the most promising and still upcoming technology and enterprise--no matter how big or small, every company/organization has adopted it as a part of their IT strategy. It is difficult these days to have any meaningful conversation without including cloud computing in the overall solution discussions.
Cloud computing, or simply cloud in layman terms, refers to the availability of resources on the internet. These resources are made available to users on the internet as services. For example, storage is available on-demand through the internet to users for them to store their files, documents, and so on. Here storage is a service provided by a cloud provider.
A cloud provider is an enterprise or consortium of companies that provide cloud services to other enterprises and consumers. They host and manage the services on behalf of the user. They are responsible for enabling and maintaining the health of services. Typically, there are large data centers across the globe opened by cloud providers to cater to IT demands from users.
Cloud resources could be a delivery of hosting services or providing on-demand infrastructures, such as a computer, network, and storage facilities to users for consumption. This flavor of the cloud is also typically known as Infrastructure as a Service.
There are three types of services provided by cloud based on their level of abstraction and degree of control on these services by users and cloud providers:
- Infrastructure as a Service (also popularly known as IaaS)
- Platform as a Service (also popularly known as PaaS)
- Software as a Service (also popularly known as SaaS)
IaaS, PaaS, and SaaS differ based on the level of control between a cloud consumer and a cloud provider. With SaaS, a cloud provider has almost complete control over the services with the consumer having control only over its data and application. Similarly, a cloud provider has higher control with IaaS as compared to cloud consumer.
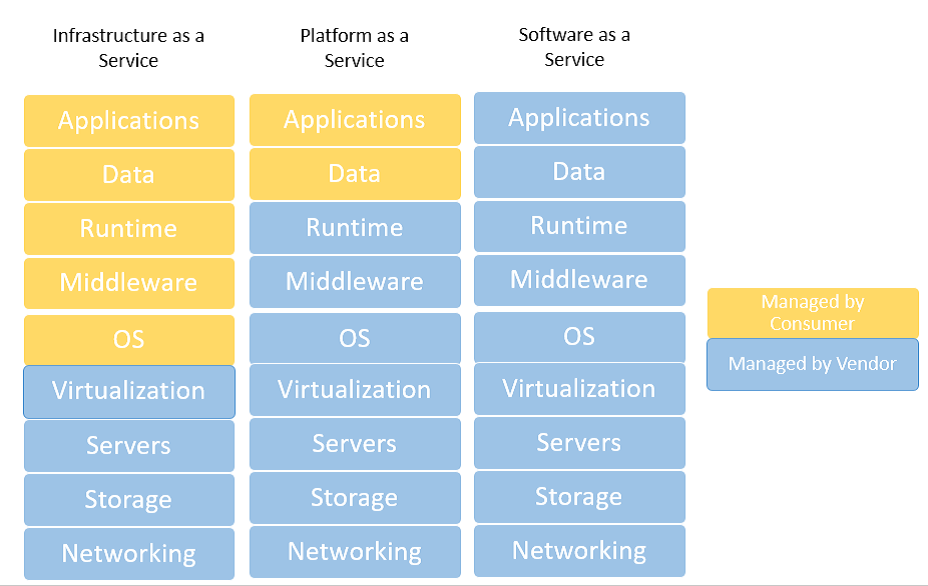
The preceding diagram shows the three categories of service available through cloud providers and the layers that are comprised of each service. These layers are stacked vertically on each other and each layer in the stack is colored differently depending on who manages it, the customer or the provider. From the figure, we see that for IaaS, a cloud provider is responsible for providing, controlling, and managing layers from the network layer up to the virtualization layer. Similarly, for PaaS, a cloud provider controls and manages from the hardware layer up to the runtime layer, while the consumer controls only the application and data layers.
Infrastructure as a Service
As the name suggests, IaaS are infrastructure services provided by a cloud provider. This service includes the physical hardware and its configuration, network hardware and its configuration, storage hardware and its configuration, load balancers, compute, and virtualization. Any layer above virtualization is the responsibility of the consumer. The consumer can decide to use the provided underlying infrastructure in whatever way best suits their requirements. For example, consumers can consume the storage, network, and virtualization to provision virtual machines on top of it. It is then the consumer's responsibility to manage and control the virtual machines and the software deployed within it.
Platform as a Service
PaaS enables consumers to deploy their applications and services on the provided platform, consuming the underlying runtime, middleware, and services. The cloud provider provides the services from infrastructure to runtime. The consumers cannot provision virtual machines as they cannot access and control them. Instead, they can only control and manage their applications. This is a comparatively faster method of development and deployment because now the consumer can focus on application development and deployment. Examples of Platform as a Service include Azure Automation, Azure SQL, and Azure App Services.
Software as a Service
Software as a Service provides complete control of the service to the cloud provider. The cloud provider provisions, configures, and manages everything from infrastructure to the application. It includes the provisioning of infrastructure, deployment, and configuration of applications, and provides application access to the consumer. The consumer does not control and manage the application and can use and configure only parts of the application. They control only their data and configuration. Generally, multi-tenant applications are used by multiple consumers, such as Office 365 and Visual Studio Team Services, which are examples of SaaS.
Last few years have witnessed exponential growth in cloud adoption. While most of the initial growth was from small and medium enterprises, the current adoption is coming from large enterprises. This is happening primarily because of the following drivers mentioned:
- Cost effective: Cloud helps in eliminating capital expenditure and instead just incurs an operational cost. Users can stop purchasing physical hardware, expensive software's licenses and set up large data centers. All these are available on the cloud without user spending anything to buy them.
- Unlimited scale and capacity: Cloud provides the notion of unlimited availability of resources. This encourages organizations to deploy their workloads on it because they are not constrained by hardware availability limitations.
- Elasticity: Cloud computing is elastic in nature. Customers can shrink or increase their Cloud presence based on their needs easily using simple to use user interface. There is no upfront cost, resource availability constraints, and time lag in doing so.
- Pay as you go: Using cloud eliminates capital expenditure and organizations pay only for what they use, thereby providing maximum return on investment. Organizations do not need to build additional infrastructure to host their application for times of peak demand.
- Faster and better: Cloud provides ready-to-use applications and faster provisioning and deployment of environments. Moreover, organizations get better-managed services from their cloud provider with higher service-level agreements.
What is Azure?
According to Wikipedia:
Azure obviously provides all the benefits of cloud, but it is also an open and flexible cloud. Azure cloud supports a variety of operating systems, languages, tools, platforms, utilities, and frameworks. It supports both Linux and Windows, SQL Server, MySQL, Postgres and more, C#, Python, Java, Node.js, Bash, and more languages, MongoDB and DocumentDB NoSQL databases, and Jenkins to VSTS as continuous integration tools. The whole idea behind this ecosystem is to enable users to have their choice and freedom of language, their choice of platform and operating system, their choice of databases, and their choice of storage, their choice of tools and utilities. Users should not be constrained from the technology perspective, instead, they should be able to build and focus on their business solution and Azure provides them with world-class technology stack. Azure is compatible with the user's choice of technology stack.
For example, Azure provides availability of all popular (open source or commercial) database environments. Azure provides Azure SQL, MySQL, and Postgres PaaS service. It provides a Hadoop ecosystem and offers HDInsight, a 100% Apache Hadoop-based PaaS services. It also provides Hadoop on Linux VM implementation for customers who prefer IaaS approach. Azure also provides a Redis cache service and supports other popular database environments, such as MongoDB, Couchbase, Oracle, and many others as an IaaS implementation.
The number of services is increasing by the day and the following figure just provides the rich set of services provided by Azure. Not all services are shown here and it keeps on growing.

Azure also provides a unique cloud computing paradigm--the Hybrid cloud. Hybrid cloud refers to a deployment strategy in which a subset of services are deployed on a public cloud, while other services are deployed in an on-premise private cloud or data center. There is a Virtual Private Network (VPN) connection between both the public and private cloud. Azure provides users the flexibility to divide and deploy their workload on both public cloud and on-premise data center.
Azure has data centers across the globe. Azure combines these data centers into regions. Each region has multiple data centers to ensure that recovery from disasters is quick and efficient. At the time of writing, there are 38 regions across the globe. This provides users the flexibility to deploy their services at their choice of location and regions. They can also combine these regions to deploy a solution that is disaster resistant and deployed near their customer base.

Azure as an intelligent cloud
Azure is not just a cloud; it is an intelligent cloud. Now, you might be wondering what an intelligent cloud is. People consume computing power primarily because of two reasons: Either they are searching for something and after finding what they were looking for, act on it. The entire computing powers are associated with these two purposes. Azure provides infrastructure and services to invest millions and billions of records with hyper-scale processing. It provides multi-petabytes of storages for data. It provides a host of inter-connected services that can pass data among each other. With such capabilities in place, data can be processed to generate meaningful knowledge and insights. There are multiple types of insights that can be generated through data analysis:
- Descriptive: This kind of analysis provides details about what is happening or happened in the past
- Predictive: This kind of analysis provides details about what is going to happen in the near-future or the future
- Prescriptive: This kind of analysis provides details about what should be done to either enhance or prevent the current or future happening
- Cognitive: This actually executes the actions determined by prescriptive analytics in an automated manner
While insights are good to them, it is also important to act on them reactively or proactively. Azure provides a rich platform to ingest big data, process and augment data through its rich services, store data in its large data storage systems, conduct analysis on them, generate insights and dashboards, and then execute actions based on it. These services are available to every user of Azure and provide a rich ecosystem to create solutions on top of them. Enterprises are creating applications and services that are completely disrupting industries because of easy availability of these intelligent services from Azure that are easily combined to create meaningful value to end customers. Azure had ensured that services that were commercially unviable to implement by small and medium companies can now readily consume and deploy them in a few minutes.
Azure Resource Manager
Azure Resource Manager is the technology platform and orchestration service from Microsoft that ties up all components discussed earlier. It brings Azure resource providers, resources, and resource groups together to form a cohesive cloud platform. It helps in the registration of resource providers to subscriptions and regions, it makes the resource types available to resource groups, makes the resource and resource APIs accessible to the portal and other clients, and authenticates access to resources. It also enables features, such as tagging, authentication, Role-Based Access Control (RBAC), resource locking, and policy enforcement for subscriptions and its resource groups. It provides the same deployment and management experience whether through a portal or client-based tools such as PowerShell or a command-line interface.
Azure Resource Manager architecture
The architecture of Azure Resource Manager and its components are as shown in the following figure. As we can see Azure Subscription comprises of multiple resource groups. Each resource group contains resource instances that are created from resource types available in the resource provider.

ARM and ASM
ASM has inherent constraints and some of the major ones are discussed here: ASM deployments are slow and blocking. Operations are blocked if an earlier operation is already in progress:
- Parallelism: Parallelism is a challenge in ASM. It is not possible to execute multiple transactions successfully in parallel. The operations in ASM are linear and executed one after another. Either there are parallel operation errors or they will get blocked.
- Resources: Resources in ASM are provisioned and managed in isolation from each other, there is no relation between ASM resources. Grouping of services and resources or configuring them together is not possible.
- Cloud services: Cloud services are the unit of deployment in ASM. They are reliant on affinity groups and not scalable due to its design and architecture.
Granular and discreet roles and permissions cannot be assigned to resources in ASM. Users are either service administrators or co-administrators in the subscription. They either get full control on resources or do not have access to them at all. ASM provides no deployment support. Deployments are either manual or you will need to resort to writing procedural scripts in PowerShell or .NET.
ASM APIs were not consistent between resources.
ARM advantages
The ARM provides distinct advantages and benefits over ASM.
- Grouping: ARM allows grouping of resources together in a logical container. These resources can be managed together and undergo a common life cycle as a group. This makes it easier to identify related and dependent resources.
- Common life cycle: Resources in a group have the same life cycle. These resources can evolve and be managed together as a unit.
- Role-Based Access Control: Granular roles and permissions can be assigned to resources providing discreet access to users. Users can have only those rights that are assigned to them.
- Deployment support: ARM provides deployment support in terms of templates enabling DevOps and Infrastructure as Code (IAC). The deployments are faster, consistent, and predictable.
- Superior technology: Cost and billing of resources can be managed as a unit. Each resource group can provide their usage and cost information.
- Manageability: ARM provides advanced features such as security, monitoring, auditing, and tagging features for better manageability of resources. Resources can be queried based on tags. Tags also provide cost and billing information for resources tagged similarly.
- Migration: Easier migration and update of resources within, as well as from across resource groups.
ARM concepts
With the ARM, everything in Azure is a resource. Examples of resources are a virtual machine, network interfaces, public IP address, storage accounts, virtual networks, and more. ARM is based on concepts related to resource providers and resource consumers. Azure provides resources and services through multiple resource providers that are consumed and deployed in groups.
Resource providers
These are services responsible for providing resource types through Azure Resource Manager. The top-level concept in the ARM is resource providers. These providers are containers for resource types. Resource types are grouped into resource providers. They are responsible for deploying and managing the resources. For example, a virtual machine resource type is provided by a resource provider called Microsoft.Compute Namespace. The REST API operations are versioned to distinguish between them. The version naming is based on the dates on which they are released by Microsoft. It is necessary that a related resource provider is available to a subscription to deploy a resource. Not all resource providers are available to a subscription out of the box. If a resource is not available in the subscription, one must check if the required resource provider is available in each region. If that is available, the user can explicitly register in the subscription.
Resource types
These are an actual resource specification defining it's public API interface and implementation. It implements the working and operations supported by the resource. Similar to resource providers, resource types also evolve over time with regard to their internal implementation and have multiple versions of its schema and public API interface. The version names are based on dates that they are released on by Microsoft as a preview or General Availability (GA). The resource types become available to a subscription after a resource provider is registered to it. Also, not every resource type is available in every Azure region. The availability of a resource is dependent on the availability and registration of a resource provider in an Azure region and must support the API version needed for provisioning it.
Resource groups
Resource groups are a unit of deployment in the ARM. They are containers grouping multiple resource instances in a security and management boundary. A resource group is uniquely named in a subscription. Resources can be provisioned on different Azure regions yet belong to the same resource group. It provides additional services to all resources within it. Resource groups provide metadata services, such as tagging, which enables categorization of resources, policy-based management of resources, RBAC, protection of resources from accidental deletion or updates, and more. As mentioned before, they have a security boundary and users that don't have access to a resource group cannot access resources contained within it. Every resource instance needs to be part of a resource group or else it cannot be deployed.
Resource and resource instances
Resources are created from resource types and should be unique within a resource group. The uniqueness is defined by the name of the resource and its type together. In OOP parlance, resource instances can be referred to as objects, while resource types can be referred to as a class. The services are consumed through the operations supported and implemented by resource instances. They define properties that should be configured before usage. Some are mandatory properties, while others are optional. They inherit the security and access configuration from its parent resource group. These inherited permissions and role assignments can be overridden for each resource. A resource can be locked in such a way that some of its operations can be blocked and not made available to roles, users, and groups even though they have access to it. They can be tagged for easy discoverability and manageability.
Azure Resource Manager features
The following are some of the major features provided by Azure Resource Manager:
- Role-Based Access Control: Azure Active Directory (AAD) authenticates users to provide access to subscriptions, resource groups, and resources. ARM implements OAuth and RBAC within the platform, enabling authorization and access control to resources, resource groups, and subscriptions based on roles assigned to a user or group. A permission defines access to operations on a resource. These permissions could allow or deny access to the resource. A role definition is a collection of these permissions. Roles map AAD users and groups to the permissions. Roles are subsequently assigned to a scope, which can be an individual, collection of resources, resource group, or subscription. The AAD identities (users, groups, and service principles) added to a role gain access to the resource according to permissions defined in the role. ARM provides multiple out-of-the-box roles. It provides system roles, such as owner, contributor, reader, and more. It also provides resource-based roles, such as SQL DB contributor, virtual machine contributor, and more. ARM allows the creation of custom roles.
- Tags: Tags are name-value pairs that add additional information and metadata to resources. Both resources and resource groups can be tagged with multiple tags. Tags help in the categorization of resources for better discoverability and manageability. Resources can be quickly searched and identified easily. Billing and cost information can be fetched for resources that have the same tags applied. While this feature is provided by the ARM, an IT administrator defines its usage and taxonomy with regard to resources and resource groups. Taxonomy and tags, for example, can be defined based on departments, resource usage, location, projects, or any other criteria deemed fit from a cost, usage, billing, and search perspective. These tags can then be applied to resources. Tags defined at the resource group level are not inherited by its resources.
- Policies: Another security feature provided by ARM are policies. Custom policies can be created to control access to the resources. Policies are defined conventions and rules and must be adhered to while interacting with resources and resource groups. The policy definition contains an explicit denial of actions on resources or access to resources. By default, every access is allowed if it is not mentioned in the policy definition. These policy definitions are assigned to resource, resource group, and subscriptions scope. It is important to note that these policies are not replacements or substitutes for RBAC. In fact, they complement and work together with RBAC. Policies are evaluated after a user is authenticated by AAD and authorized by the RBAC service. ARM provides JSON-based policy definition language for defining policies. Some of the examples of policy definition are that it must tag every provisioned resource or resources can only be provisioned to specific Azure regions.
- Locks: Subscriptions, resource groups, and resources can be locked to prevent accidental deletion and updates by an authenticated user. Locks applied at higher levels flow downstream to child resources. Locks applied at subscription level lock every resource group and resources within it.
- Multi-region: Azure provides multiple regions for the provisioning and hosting of resources. ARM allows resources to be provisioned at different locations and yet reside within the same resource group. A resource group can contain resources from different regions.
- Idempotent: This feature ensures predictability, standardization, and consistency in resource deployment by ensuring that every deployment will result in the same state of resources and their configuration no matter the number of times it is executed.
- Extensible: ARM architecture provides an extensible architecture to allow creation and plugging of newer resource providers and resource types into the platform.
Virtualization
Virtualization was a breakthrough innovation that completely changed the way physical servers were looked at. It refers to the abstraction of a physical object into a logical object.
Virtualization of physical servers enabled the creation of multiple virtual servers, better known as virtual machines. These virtual machines consume and share the same physical CPU, memory, storage, and other hardware with the physical server on which they were hosted. This enabled faster and easier provisioning of application environments on demand, providing high availability and scalability with reduced cost. One physical server was enough to host multiple virtual machines, each virtual machine containing its own operating system and hosting services on it.
There was no longer any need to buy additional physical servers for deploying new applications and services. The existing physical servers were sufficient to host more virtual machines. Furthermore, as part of rationalization, many physical servers were consolidated into a few with the help of virtualization.
Each virtual machine contains the entire operating system and each virtual machine is completely isolated from other virtual machines, including the physical hosts. Although a virtual machine uses the hardware provided by the host physical server, it has full control over its assigned resources and its environment. These virtual machines can be hosted on a network such as a physical server with its own identity.
Azure helps in creating Linux and Windows virtual machines in a few minutes. Microsoft provides its own images along with images from partners and the community. Users can bring in their own images. Virtual machines are created using these images.
Containers
Containers are also a virtualization technology; however, they do not virtualize a physical server. Instead, a container is an operating-system-level virtualization. What this means is that containers share the operating system kernel provided by the host among themselves along with the host. Multiple containers running on a host (physical or virtual) share the host operating system kernel. Containers ensure that they reuse the host kernel instead of each having a dedicated kernel to themselves.
Containers are also completely isolated from the host and other containers, such as a virtual machine. Containers use Windows storage filter drivers and session isolation for providing isolation of operating system services such as the filesystem, registry, processes, and networks. Each container gets its own copy of operating system resources.
The container has the perception that it has a completely new and untouched operating system and resources. This arrangement provides lots of benefits, they are as follows:
- Containers are faster to provision. They do not need to provide the operating system and its kernel services. They are available from the host operating system.
- Containers are lightweight and require fewer computing resources compared to virtual machines. The operating system resource overhead is no longer required in containers.
- Containers are much smaller in size compared to virtual machines.
- Containers help in solving the problems related to managing multiple application dependencies in an intuitive, automated, and simple manner.
- Containers provide infrastructure to define all application dependencies in a single place.
Containers are an inherent part and feature of Windows Server 2016 and Windows 10; however, they are managed and accessed using a Docker client and Docker daemon. Containers can be created on Azure with Windows Server 2016 SKU as an image.
Each container has a single main process that must be running for the container to exist. A container will stop when this process ends. Also, a container can either run in interactive mode or in a detached mode like a service.

The figure shows all the technical layers that enable containers. The bottommost layer provides the core infrastructure in terms of network, storage, load balancers, and network cards. At the top of the infrastructure is the compute layer, consisting of either a physical server or both physical as well as virtual servers on top of a physical server. This layer contains the operating system with the ability to host containers. The operating system provides the execution driver that the layers above use to call kernel code and objects to execute containers. Microsoft has created Host Container System Shim (HCSShim) for managing and creating containers and uses Windows storage filter drivers for image and file management.
The container environment isolation ability is provided to the Windows session. Windows Server 2016 and Nano Server provide the operating system and enable the container features and execute the user-level Docker client and Docker engine. The Docker engine uses the services of HCSShim, storage filter drivers, and sessions to spawn multiple containers on the server, each containing a service, application, or database.
Docker
Docker provides management features to Windows containers. It comprises of two executables:
- Docker daemon
- Docker client
The Docker daemon is the workhorse for managing containers. It is a Windows service responsible for managing all activities on the host related to containers. The Docker client interacts with the Docker daemon and is responsible for capturing inputs and sending them across to the Docker daemon. The Docker daemon provides the runtime, libraries, graph drivers, and engine to create, manage, and monitor containers and images on the host server. It also provides capabilities to create custom images that are used for building and shipping applications to multiple environments.
Interacting with intelligent cloud
Azure provides multiple ways to connect, automate, and interact with it. All method require users and codes to be authenticated with valid credentials before they can be used.
- Azure portal
- PowerShell
- Azure Command Line Interface (CLI)
- Azure REST API
Azure portal
Azure portal is a great place to get started. With the Azure portal, users can log in and start creating and managing Azure resources manually. The portal provides an intuitive and user-friendly user interface through the browser. The Azure portal provides an easy way to navigate to resources using blades. The blades display all properties of a resource, logs, cost, its relationship with other resources, tags, security options, and more. The entire cloud deployment can be managed through the portal.
PowerShell
PowerShell is an object-based command-line shell and scripting language used for administration, configuration, and management of infrastructure and environments. It is built on top of the .NET framework and provides automation capabilities. PowerShell has truly become a first-class citizen among IT administrators and automation developers for managing and controlling the Windows environment. Today, almost every Windows and many Linux environments can be managed by PowerShell. In fact, almost every aspect of Azure can also be managed by PowerShell. Azure provides rich support for PowerShell. It provides a PowerShell module for each resource provider containing hundreds of cmdlets. Users can use these cmdlets in their scripts to automate interacting with Azure. Azure PowerShell module is available through the web platform installer as well as through the PowerShell Gallery. Windows Server 2016 and Windows 10 provides package management and PowerShellGet modules for quick and easy downloads and installation of PowerShell modules from the PowerShell gallery. The PowerShellGet module provides the Install-Module cmdlet for downloading and installing modules on the system. Installing a module is a simple act of copying the module files at well-defined module locations:
Import-module PowerShellGet Install-Module -Name AzureRM -verbose
Azure Command-Line Interface (CLI)
Azure also provides Azure CLI 2.0 that can be deployed on Linux, Windows, as well as Mac operating systems. The Azure CLI 2.0 is Azure's new command-line utility for managing Azure resources. Azure CLI 2.0 is optimized for managing and administering Azure resources from the command line, and for building automation scripts that work against the Azure Resource Manager. The command-line interface can be used to execute commands using Bash Shell or Windows command line. Azure CLI is a very famous non-Windows user as it allows us to talk to Azure on Linux and Mac. Steps for installing Azure CLI 2 are available at https://docs.microsoft.com/en-us/cli/azure/install-azure-cli?view=azure-cli-latest.
Azure REST API
All Azure resources are exposed to users through REST endpoints. Representational State Transfer (REST) APIs are service endpoints that implement HTTP operations (methods), providing create, retrieve, update, or delete (CRUD) access to the service's resources. Users can consume these API's to create and manage resources. In fact, the CLI and PowerShell mechanism uses these REST API's internally to interact with resources on Azure.
Azure Resource Manager templates
In an earlier section, we witnessed deployment features such as multi-service, multi-region, extensible, and idempotent provided by the ARM. ARM templates are primary means of provisioning resources in the ARM. ARM templates provide implementation support for ARM deployment features.
ARM templates provide a declarative model through which resources, their configuration, scripts, and extensions are specified. ARM templates are based on JavaScript Object Notation (JSON) format. They use the JSON syntax and conventions to declare and configure resources. JSON files are text-based, human-friendly, and easily readable files.
They can be stored in a source code repository and have version control. They are also a means to represent IAC that can be used to provision resources in an Azure resource group again and again, predictably, consistently, and uniformly. A template needs a resource group for deployment. It can only be deployed to a resource group and the resource group should exist before executing a template deployment. A template is not capable of creating a resource group.
Templates provide the flexibility to be generic and modular in their design and implementation. Templates provide the ability to accept parameters from users, declare internal variables, help in defining dependencies between resources, link resources within same or different resource groups, and execute other templates. They also provide scripting language type expressions and functions that make them dynamic and customizable at runtime.
Deployments
PowerShell allows two modes of deployment of templates:
- Incremental
- Complete
Incremental deployment adds resources declared in the template that doesn't exist in a resource group, leaves resources unchanged in a resource group that is not part of a template definition, and leaves resources unchanged in a resource group that exists in both the template and resource group with the same configuration state.
Complete deployment, on the other hand, adds resources declared in a template to the resource group, deletes resources that do not exist in the template from the resource group, and leaves resources unchanged that exist in both the resource group and template with the same configuration state.
Summary
The cloud is not more than 10 years old. It is a new paradigm and still in its nascent stage. There will be a lot of innovation and capabilities added over time. Azure is one of the top cloud providers today and it provides rich capabilities through IaaS, PaaS, SaaS, and hybrid deployments. In fact, Azure stack, which is an implementation of private cloud from Microsoft, will release soon. This will have the same features available on private cloud as that on a public cloud. They both will, in fact, connect and work seamlessly and transparently together. It is very easy to get started with Azure, but also developers and architects can fall into a trap if they do not design and architect their solutions appropriately. This book is an attempt to provide guidance and directions towards architecting solutions the right way using appropriate services and resources. Every service on Azure is a resource. It is important to understand how these resources are organized and managed in Azure. This chapter provided context around Azure Resource Manager and groups--the core framework that provides building blocks for resources. It provides a set of services to resources that help provide uniformity, standardization, and consistency in managing them. The services, such as RBAC, tags, policies, locks, and more are available to every resource provider and resource. Azure also provides rich automation features to automate and interact with resources. Tools such as PowerShell, ARM templates, and Azure CLI can be incorporated as part of release pipelines and continuous deployment and delivery. Users can connect to Azure from heterogeneous environments using these automation tools.
Next chapter will discuss some of the important patterns that help in solving common cloud-based deployment problems and ensure the application is secure, available, scalable, and maintainable in long run.



















 Download code from GitHub
Download code from GitHub