Chapter 4. Understanding the Blockchain
| | "With e-currency based on cryptographic proof, without the need to trust a third party middleman, money can be secure and transactions effortless." | |
| | --Satoshi Nakamoto, Bitcoin developer |
Bitcoin's underlying transaction database is called the Blockchain. Its novel design, as a distributed ledger, allows it to function without any trusted central authority. Understanding how it works is essential for integrating information systems with Bitcoin. In this chapter, you will be given a simplified explanation of the blockchain's internal mechanisms. Building on the previous chapters, we'll cover the following subjects in more detail:
September 15th, 2008 marked a defining moment for the finance industry, as Lehman Brothers, at that time the fourth largest investment bank, filed for chapter 11 bankruptcy after massive losses in stock price and assets. The collapse marked the beginning of the Global Financial Crisis of 2008.
Shortly after, Bitcoin, a new type of virtual currency, was launched by an anonymous developer, or group of developers, under the name Satoshi Nakamoto. The software was built on a publicly-accessible transaction ledger, that is distributed and validated by a network of independent nodes. More importantly, its design was powerfully resilient to attacks.
The mysterious developer launched Bitcoin at the beginning of 2009. Encoded in the first block of transactions was a message highly relevant to the state of global financial affairs at that time:
"The Times 03/Jan/2009 Chancellor on brink of second bailout for banks."
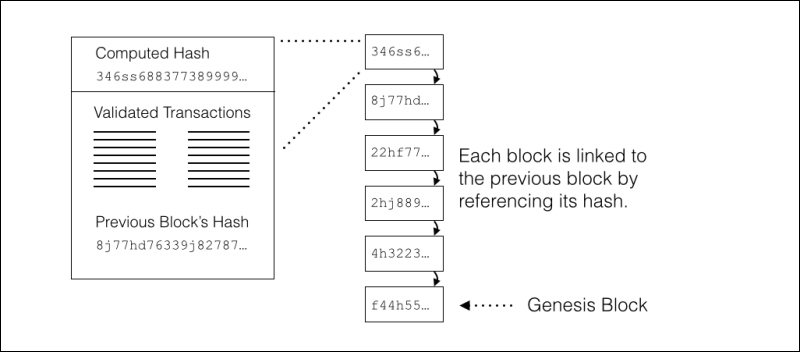
The first block of transactions, called the "genesis block", set forth...
Keys, transactions, and blocks
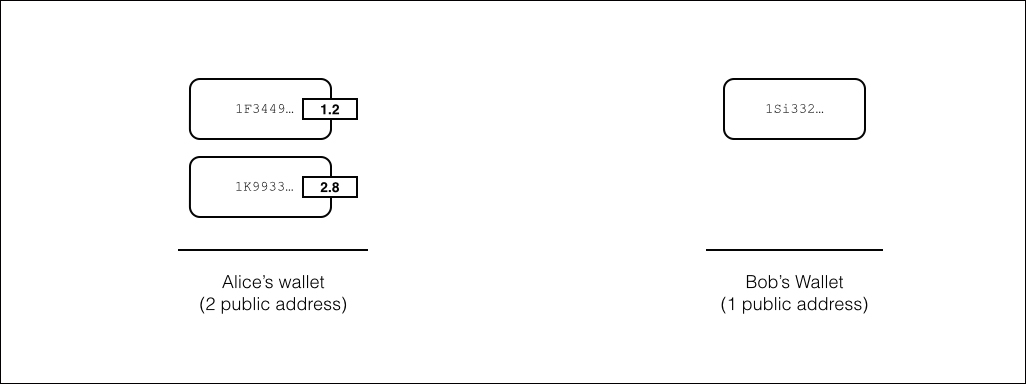
To help you understand how Bitcoin transactions work, we'll need to explain how some of its basic mechanisms work with various cryptographic algorithms. With the classic example of sending money between Alice and Bob, we will illustrate how the Bitcoin network confirms a transaction.
Let's start with an example where Alice wants to send 4.0BTC to Bob. Alice has a bitcoin wallet with two addresses along with the corresponding private keys that control the two amounts 1.2BTC and 2.8BTC. To receive the money, Bob will generate a private key with a Bitcoin address:
To transfer the bitcoin, we need to create a valid transaction and broadcast it to the Bitcoin network for confirmation. If confirmed by the network, the transferred amount will be available for spending by the receiver.
The transaction can record a transfer between...
Bitcoin uses a unique and novel way of storing and distributing its transaction ledger. To create a database of transactions that is both resilient and transparent, it distributes all its transactions across a global network of nodes. This database is called the blockchain. To understand how the blockchain works, we'll explore how the blocks are used to group and distribute the transactions.
The blockchain is a chain of blocks linked together, from the genesis block to the latest block, as shown in the following Figure 4.11. Every node connected to the network maintains a complete copy of the entire blockchain. This redundancy results in a very resilient system.
New blocks are mined by the nodes listening for transactions on the network. The nodes can share and relay the transactions amongst themselves. When a new transaction is received by a node, it is added to the new block. The new block is kept...
The Bitcoin network is protected by the consensus of the network. Valid transactions and changes to the software must be accepted by the majority of the miners on the network. Let's discuss the attacks that could occur:
It is theoretically possible for a large amount of computing power to overtake the network and accept double spending or prevent confirmations. This is called the 51 percent attack.
Although theoretically possible, the opposing argument to the attack notes the amount of computing power needed to perform the attack. Some argue that it is not financially feasible to execute the attack as the network could quickly reject the malicious blocks. It would be difficult for a large pool of nodes to produce a segment of the blockchain of more than six blocks in a row with a corrupt transaction.
A malicious spender could try to double spend by broadcasting two transactions to the network at the same time. Given that the merchant would accept...
The Bitcoin software is open source and available to the public. From the public repository, many "alternative coins" have been created by copying the source code and re-configuring specific parameters. Each alt-coin can implement a different ruleset independent of any other alt-coin.
Generally, alt-coins implement different quantities for the total money supply or different block rates. For example, Litecoin has a total supply of 84 million coins and a mining rate of approximately two minutes.
Other alt-coins may implement a built-in inflation. For example, Friecoin has a built-in demurrage that's 5 percent per year. Basically, if you hold 1 Friecoin, it will be worth 5 percent less if you spend it one year later. This was used as an incentive to promote spending.
As another interesting coin, Namecoin uses its blockchain to record information about the ownership of names. The most popular use for this mechanism is to record the ownership of domain names. Using the Namecoin...
The blockchain is quickly proving to be a very impressive technology for recording the transfer of money. Due to its decentralized design, it is extremely resilient and completely transparent. It will continue to be a powerful force in the financial world as it develops over time.
In the next chapter, we'll set up and install our own Bitcoin node.