Bruce Schneier - Race Condition Attacks against LLMs: "These aretwo attacks against the system components surrounding LLMs: "We propose that LLM Flowbreaking, following jailbreaking and prompt injection, joins as the third on the growing list of LLM attack types. Flowbreaking is less about whether prompt or response guardrails can be bypassed, and more about whether user inputs and generated model outputs can adversely affect these other components in the broader implemented system."
Bruce Schneier - NSO Group Spies on People on Behalf of Governments: "The Israeli company NSO Group sells Pegasus spyware to countries around the world (including countries like Saudi Arabia, UAE, India, Mexico, Morocco and Rwanda). We assumed that those countries use the spyware themselves. Now we’velearned that that’s not true: that NSO Group employees operate the spyware on behalf of their customers."
Bruce Schneier - What Graykey Can and Can’t Unlock: "The Graykey, a phone unlocking and forensics tool that is used by law enforcement around the world, is only able to retrieve partial data from all modern iPhones that run iOS 18 or iOS 18.0.1, which are two recently released versions of Apple’s mobile operating system, according to documents describing the tool’s capabilities in granular detail obtained by 404 Media. The documents do not appear to contain information about what Graykey can access from the public release of iOS 18.1, which was released on October 28."
Bruce Schneier - Security Analysis of the MERGE Voting Protocol: "The recently published “MERGE” protocol is designed to be used in the prototype CAC-vote system. The voting kiosk and protocol transmit votes over the internet and then transmit voter-verifiable paper ballots through the mail. In the MERGE protocol, the votes transmitted over the internet are used to tabulate the results and determine the winners, but audits and recounts use the paper ballots that arrive in time. The enunciated motivation for the protocol is to allow (electronic) votes from overseas military voters to be included in preliminary results before a (paper) ballot is received from the voter. MERGE contains interesting ideas that are not inherently unsound; but to make the system trustworthy—to apply the MERGE protocol—would require major changes to the laws, practices, and technical and logistical abilities of U.S. election jurisdictions."
CheckPoint - Gaming Engines: An Undetected Playground for Malware Loaders: "Cybercriminals constantly try to evolve their tactics and techniques, aiming to increase infections. Their need to stay undetected pushes them to innovate and discover new methods of delivering and executing malicious code, which can result in credentials theft and even ransomware encryption. Check Point Research discovered a new undetected technique that uses Godot Gaming Engine to execute malicious GDScript code."
Krebs on Security - Hacker in Snowflake Extortions May Be a U.S. Soldier: "Two men have been arrested for allegedly stealing data from and extorting dozens of companies that used the cloud data storage company Snowflake, but a third suspect — a prolific hacker known as Kiberphant0m — remains at large and continues to publicly extort victims. However, this person’s identity may not remain a secret for long: A careful review of Kiberphant0m’s daily chats across multiple cybercrime personas suggests they are a U.S. Army soldier who is or was recently stationed in South Korea."
Krebs on Security - Feds Charge Five Men in ‘Scattered Spider’ Roundup: "Federal prosecutors in Los Angeles this week unsealed criminal charges against five men alleged to be members of a hacking group responsible for dozens of cyber intrusions at major U.S. technology companies between 2021 and 2023, including LastPass, MailChimp, Okta, T-Mobile and Twilio."
Nozomi - Over-the-Air Vulnerabilities Discovered in Advantech EKI Access Points: "Nozomi Networks Labs has conducted an analysis of version 1.6.2 of the EKI-6333AC-2G industrial-grade wireless access point. Thanks to its resilience in challenging environments, this device is utilized across diverse sectors, ranging from automobile assembly lines up to warehousing and distribution operations within logistics. Our analysis identified 20 vulnerabilities, each assigned a unique CVE identifier. These vulnerabilities pose significant risks, allowing unauthenticated remote code execution with root privileges, thereby fully compromising the confidentiality, integrity, and availability of the affected devices."
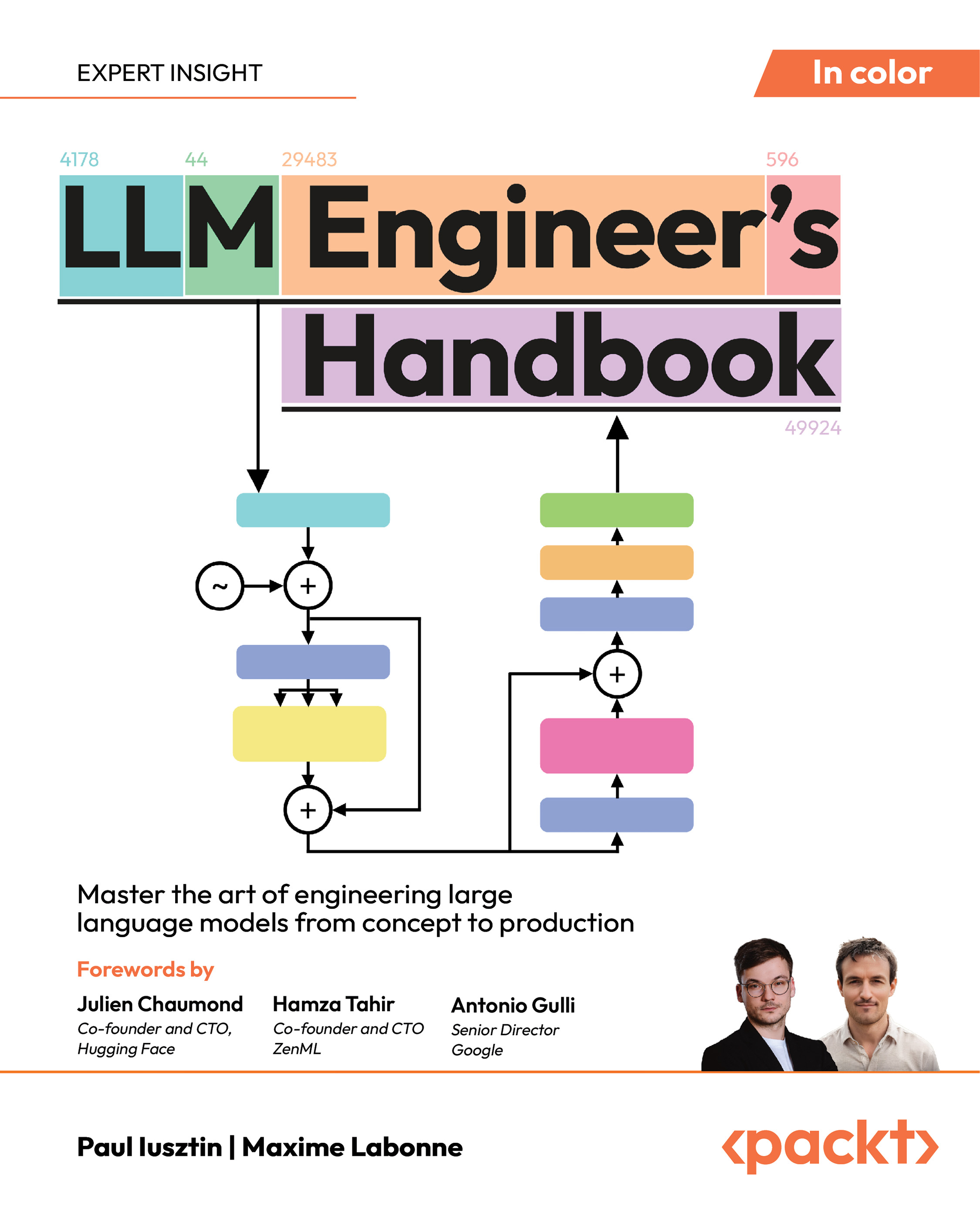
Unlock access to the largest independent learning library in Tech for FREE!
Get unlimited access to 7500+ expert-authored eBooks and video courses covering every tech area you can think of.
Renews at $19.99/month. Cancel anytime
Phylum - Python Crypto Library Updated to Steal Private Keys: "Phylum's automated risk detection platform discovered that the PyPI package aiocpa was updated to include malicious code that steals private keys by exfiltrating them through Telegram when users initialize the crypto library. While the attacker published this malicious update to PyPI, they deliberately kept the package's GitHub repository clean of the malicious code to evade detection."
TrendMicro - Game of Emperor: Unveiling Long Term Earth Estries Cyber Intrusions: Since 2023, Earth Estries (aka Salt Typhoon, FamousSparrow, GhostEmperor and UNC2286) has emerged as one of the most aggressive Chinese advanced persistent threat (APT) groups, primarily targeting critical industries such as telecommunications and government entities in the US, the Asia-Pacific region, the Middle East, and South Africa. In this blog entry, we will highlight their evolving attack techniques and analyze the motivation behind their operations, providing insights into their long-term targeted attacks.
Trustware - Rockstar 2FA: A Driving Force in Phishing-as-a-Service: We have been tracking a widespread phishing campaign delivered via email that showed a significant increase in activity in August 2024 and continues to be prevalent as of writing. This campaign employs an AiTM attack, allowing attackers to intercept user credentials and session cookies, which means that even users with multifactor authentication (MFA) enabled can still be vulnerable. Microsoft user accounts are the prime target of these campaigns, as target users will be redirected to landing pages designed to mimic Microsoft 365 (O365) login pages.
WeLiveSecurity- Bootkitty: Analyzing the first UEFI bootkit for Linux: "A common thread among these publicly known bootkits was their exclusive targeting of Windows systems. Today, we unveil our latest discovery: the first UEFI bootkit designed for Linux systems, named Bootkitty by its creators. We believe this bootkit is merely an initial proof of concept, and based on our telemetry, it has not been deployed in the wild. That said, its existence underscores an important message: UEFI bootkits are no longer confined to Windows systems alone."
 United States
United States
 Great Britain
Great Britain
 India
India
 Germany
Germany
 France
France
 Canada
Canada
 Russia
Russia
 Spain
Spain
 Brazil
Brazil
 Australia
Australia
 Singapore
Singapore
 Canary Islands
Canary Islands
 Hungary
Hungary
 Ukraine
Ukraine
 Luxembourg
Luxembourg
 Estonia
Estonia
 Lithuania
Lithuania
 South Korea
South Korea
 Turkey
Turkey
 Switzerland
Switzerland
 Colombia
Colombia
 Taiwan
Taiwan
 Chile
Chile
 Norway
Norway
 Ecuador
Ecuador
 Indonesia
Indonesia
 New Zealand
New Zealand
 Cyprus
Cyprus
 Denmark
Denmark
 Finland
Finland
 Poland
Poland
 Malta
Malta
 Czechia
Czechia
 Austria
Austria
 Sweden
Sweden
 Italy
Italy
 Egypt
Egypt
 Belgium
Belgium
 Portugal
Portugal
 Slovenia
Slovenia
 Ireland
Ireland
 Romania
Romania
 Greece
Greece
 Argentina
Argentina
 Netherlands
Netherlands
 Bulgaria
Bulgaria
 Latvia
Latvia
 South Africa
South Africa
 Malaysia
Malaysia
 Japan
Japan
 Slovakia
Slovakia
 Philippines
Philippines
 Mexico
Mexico
 Thailand
Thailand