Deploying a New vSphere 6.7 Infrastructure
vSphere is a suite of core infrastructure solutions that form the foundation of any modern data center that is virtualized using VMware. Planning the deployment of these components and their implementation is important as it forms the basis for any other solution.
vSphere essentially includes the hypervisor (ESXi), vCenter Server and its plugins, supporting databases and host management agents. These hypervisors create a platform to run virtual machines (VMs), and vCenter forms the management layer. vCenter enables the creation of virtual data centers. Every other solution interfaces and interacts with vCenter to manage or utilize the virtual data center. For example, vRealize Automation, NSX, and vRealize Operations interact with vCenter.
Having said that, VMware does offer APIs that allow third-party software developers to build tools that help to manage platforms or leverage the management layer formed by the vCenter servers in an environment. For example, your backup software interacts with vCenter to manage virtual machine backups.
The following software components form the foundation of a vSphere environment:
- Hypervisor: VMware ESXi 6.7
- Core management software: VMware vCenter 6.7 server and its components
- Patch management software: VMware Update Manager 6.7
ESXi Hypervisor is the abstraction layer that allows you to run multiple instances of traditional operating systems as VMs sharing the same physical resources. With every major release, 6.7 enhances the ability of the hypervisor to scale up, as well as other new features. One of the notable new features is Quick Boot. Unlike the previous versions, a reboot does not power cycle the host; instead, it restarts just the hypervisor, reducing a considerable amount of the time that is otherwise required during server initialization.
Although the book was based on vSphere 6.7 U1, VMware did release two additional updates post that. Read the release notes of vSphere 6.7 U2 and U3 for details.
vSphere 6.7 U2: https://docs.vmware.com/en/VMware-vSphere/6.7/rn/vsphere-esxi-67u2-release-notes.html and https://docs.vmware.com/en/VMware-vSphere/6.7/rn/vsphere-vcenter-server-67u2-release-notes.html
vSphere 6.7U3: https://docs.vmware.com/en/VMware-vSphere/6.7/rn/vsphere-esxi-67u3-release-notes.html and https://docs.vmware.com/en/VMware-vSphere/6.7/rn/vsphere-vcenter-server-67u3-release-notes.html
Core management software – VMware vCenter Server 6.7 and its components:
The vCenter Appliance with vSphere 6.5 was a significant improvement and saw a substantial shift in the adoption of vCenter Server Appliance (VCSA). VCSA 6.5/6.7 is equally scalable, as the Windows version of the vCenter, needless to say, is more stable and easier to troubleshoot as all the software components are packaged to run on a lightweight Linux operating system called PHOTON OS (https://vmware.github.io/photon/). Also, VMware is gradually shifting away from its dependence on Microsoft SQL and Oracle Database systems by using a PostgreSQL-based (https://www.postgresql.org/) database called vPostgres.
VMware began bundling essential services, such as SSO, Inventory Service, and certificate management, into a single manageable component called the Platform Services Controller (PSC), starting with vSphere 6.0. With versions prior to vCenter 6.0 for Windows, all of these components had individual installers, making it possible for them to be either installed on the same machine as the vCenter or installed onto separate machines. Therefore, it became necessary to protect and manage more than one virtual or physical machine running Windows. It also made upgrading and troubleshooting cumbersome. Bundling them together onto the same Windows machine or deploying as an appliance made management and the upgrade of these components a breeze.
PSC can be deployed as a separate virtual machine (Windows/VCSA) or remain as an embedded component of the VCSA. Starting with vSphere 6.7, the need for an external PSC has been deprecated.
SSO is an authentication server component that's embedded into the PSC. It acts as an authentication gateway and accepts authentication requests from registered components and validates the credential pair against identity sources that are added to the SSO server. Once successfully authenticated, they are provided with security tokens for authentication exchanges going forward.
vCenter Update Manager (VUM) is used to upgrade or patch a vSphere environment. It is predominantly used to install patches or perform ESXi upgrades. It can perform additional tasks, such as upgrading VMware tools and upgrading virtual machine hardware. The solution is fully integrated into the vCenter Appliance and is enabled by default.
vSphere Certificate Manager is a built-in certificate manager that uses VMware Certificate Authority (VMCA) as the issuing authority by default.
VMware Licensing Service is a repository for the licensing information of all VMware products that work with the PSC/vCenter. License information is replicated between PSCs that are in the same SSO domain.
The vCenter database is the source of truth for vCenter. vCenter will not function without an active connection to the database.
In this chapter, we will cover the following recipes:
- Installing ESXi – the interactive method
- Configuring the ESXi Management Network
- Scripted deployment of ESXi
- Deploying the vCenter Server Appliance (VCSA)
- Deploying vCenters in a Linked Mode configuration
- Configuring Single Sign-On (SSO) identity sources
- Configuring vCenter Roles and Permissions
- Joining ESXi to an Active Directory domain
Installing ESXi – the interactive method
VMware ESXi can be installed in more than one way. The traditional approach is to use the ESXi CD/DVD-ROM image to perform an interactive installation. In this recipe, we will learn how to install ESXi using the bootable installer image.
Getting ready
Before you begin, it is recommended that you refer to the VMware Compatibility Guide to verify whether the server hardware is compatible with VMware ESXi 6.7.
Hardware requirements
Once you have made sure that the server hardware is compatible, the next step is to make sure that the server meets the hardware capacity requirements, which are as follows:
- The physical server should have at least two 64-bit x86 CPU cores.
- AMD No Execute (NX) and Intel Execute Disable (XD) processor functions should be enabled in the server BIOS.
- To be able to run 64-bit operating systems on VMs, you will need to allow the use of hardware virtualization (Intel VT-x or AMD RVI) in the server BIOS.
- A minimum of 4 GB of physical memory for the hypervisor alone, and an additional 4 GB to start hosting VMs.
Software required for the installation
The VMware ESXi 6.7 hypervisor ISO image can be downloaded from VMware's downloads page, at https://my.vmware.com/web/vmware/downloads.
Using the ESXi image
You need a way to present the ISO to the physical machine so that it can boot from it.
Of course, you could burn the ISO to a physical DVD and then insert it into the DVD drive of the physical machine. However, most modern servers will have a method to present the ISO image to the server as a virtual drive via its IPMI interface. If you are an administrator, you may already be aware of terms such as ILO (HP), DRAC (Dell), and KVM manager (Cisco). These are web-based tools that will connect to a Remote Access Card (RAC) on the server and enable remote access to the server's console through the web interface.
How to do it...
The following procedure will guide you through the steps involved in deploying ESXi 6.7 using the interactive installer:
- Mount the ISO to the server via its IPMI interface.
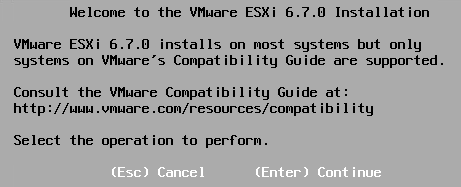
- Boot the server of the ISO. Unlike the older version of the installers, it no longer presents you with the installer boot menu. Instead, it starts loading the installer into the memory and subsequently shows the following Welcome to the VMware ESXi 6.7.0 Installation screen:
- Once you hit Enter to continue, on the next screen, hit F11 to accept the license agreement and continue.
- On the next screen, you will be prompted to choose a storage device to install ESXi on, which could be a local SSD, a local hard disk, or a LUN from remote storage (in a boot from a SAN scenario). Use the keyboard to make a selection and hit Enter to confirm. Alternatively, to make a cautious effort to ensure that you have selected the correct disk, and before you confirm the selection by hitting Enter, hit F1 to fetch more details regarding the storage device that you've selected. Step 5 covers this process:
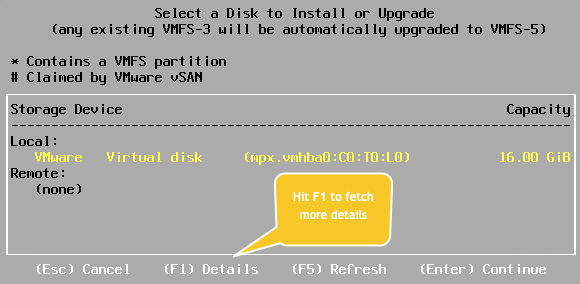
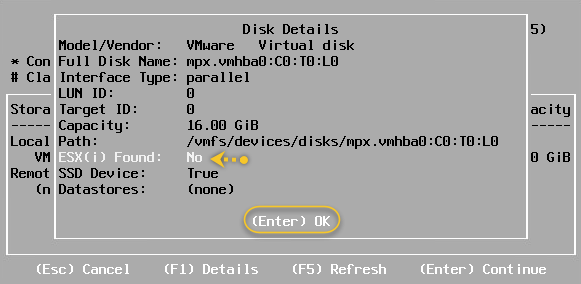
- An optional step: select the storage device and hit F1. You will now be presented with unique details, such as the CTL path to the device, LUN ID, Target ID (if using iSCSI), and the capacity of the disk, along with other general information. It will also tell you if an existing installation of ESXi is present on the storage device:
- Once you are done with the verification process, hit Enter. You will be taken back to the Select a Disk to Install or Upgrade screen. Hit Enter to confirm the device selection.
- On the next screen, select a keyboard layout. The US default is preselected. Make a different selection if necessary and hit Enter to continue.
- You will be prompted to set a password for the ESXi root account. Once you type in the password, hit Enter to continue.
- At the Confirm Install screen, review the storage device name that's displayed. If that is the correct device, hit F11 to start the installation. If you are unsure, use F9 to go back and make the necessary changes:

- The Install ESXi 6.7.0 screen will show the progress of the installation. It could take a few minutes to complete.
- When the installation completes, you will be advised to remove the installation media (unmount the ISO) before you restart the server. Once done, hit Enter to reboot:
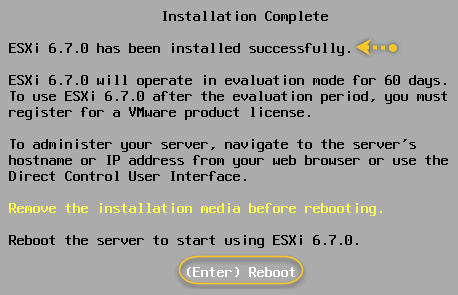
- After a reboot, you will be at the main screen for ESXi 6.7.0.
This completes the process of installing ESXi on a bare-metal server using the ESXi installer ISO.
How it works...
The ESXi installer loads all the necessary modules into the memory, detects hardware resources, and then lets you perform the installation on a storage device that's been specified. Once installed, ESXi runs in a 60-day evaluation mode and needs to be licensed for production use. The first post-installation step is to make the ESXi host available on the network by configuring its management TCP/IP stack. Read the following Configuring the ESXi management network recipe to learn more.
Configuring the ESXi Management Network
After installing ESXi, it is essential to configure its management network. The management network configuration is associated with a VMkernel interface. Think of it as a virtual network interface for VMkernel. We will learn more about these in the Chapter 3, Configuring Network Access Using vSphere Standard Switches. ESXi hypervisor runs a DHCP client, so it procures a DHCP address if there is a DHCP server on its network; however, in most cases, this is not enough. For instance, if your management network is on a VLAN, then you will need to configure a VLAN ID. Also, it is recommended to assign a static IP address for ESXi's management network.
In this recipe, we will use the Direct Console User Interface (DCUI) to achieve this.
Getting ready
You will need the following information to proceed with the steps:
- You will need access to the server's remote console via its IPMI interface (Dell DRAC, HPE ILO, Cisco KVM).
- The password for the root account.
- TCP/IP configuration - IP address, subnet mask, IP gateway address, VLAN ID, DNS server addresses, and hostname.
How to do it...
The following procedure will guide you through the steps that are required to set up the TCP/IP configuration for ESXi's management network:
- At the main screen of ESXi, hit F2 to log in to the DCUI by supplying the root password.
- Navigate to Configure Management Network and hit Enter:

- The Configure Management Network screen will present you with options to select the Network Adapters, assign a VLAN ID if necessary, and configure the IPv4/IPv6 settings and DNS configuration. Each of these sections can be selected by hitting Enter and then using the onscreen instructions to select/modify/confirm the settings:

- The Network Adapters section can be used to assign/unassign adapters to the Management Network Port Group. Use the onscreen instructions to make selections and confirm them:

- The VLAN (optional) section is used to supply a VLAN ID for the interface. The IPv4 Configuration section is used supply an IP Address/Subnet Mask/Default Gateway:

- The IPv6 Configuration section is used to supply IPv6 addresses. IPv6 is enabled by default. If IPv6 is not required for your environment, select the Disable IPv6 (restart required) option and hit Enter.
- The DNS Configuration section can be used to supply primary/alternate DNS server addresses and hostnames:

- Custom DNS Suffixes are optional if you used an FQDN as a hostname in the previous step:

- Once you are done with all the network configuration, while on the Configure Management Network: Confirm screen, hit Esc. You will be prompted to apply the changes by restarting the management network. Hit Y to apply the settings and reboot the hosts:

- Once the reboot is complete, you should be able to reach the ESXi host over the network. From here, the ESXi host can be managed directly using the host client or can be added to vCenter Server.
How it works...
Much like the VMs that would run on the ESXi hosts, the VMkernel would also need to interface with the network for a variety of purposes. These interfaces act as network node points for the VMkernel. The very first VMkernel interface - vmk0 is created during the installation of ESXi. This interface is the management interface for the ESXi host. VMware allows you to create a maximum of 256 (vmk0 – vmk255) VMkernel interfaces on an ESXi host.
The use cases include interfaces for Management traffic, VMotion traffic, FT traffic, Virtual SAN traffic, iSCSI, and NAS interfaces. Since each interface is a network node point, it will need an IP configuration and a MAC address.
OUI MAC addresses
Every physical network interface will have a burned-in 48-bit MAC address whose numbering is organizationally unique. This is because every vendor that makes the card will have a set of organizationally unique identifiers (OUI) assigned to them by the Institute of Electrical and Electronics Engineers (IEEE).
VMware also has a set of OUIs assigned to it, that is, 00:50:56 and 00:0C:29. Although both OUIs are used differently, they can be assigned to virtual machine NICs and the VMkernel interface.
Scripted deployment of ESXi
When you have a large number of ESXi hosts to deploy, any method to automate and reduce the amount of manual work is considered gold. The main benefit of automating installation is that it helps standardize multiple installations without having to carefully audit each installation. VMware has always supported the scripted installation of ESXi hosts, and that has not changed with vSphere 6.7.
Like with any automated task, the scripted installation of an ESXi host requires the use of a configuration file that contains the intended host configuration that's stored at a location that's accessible to the ESXi host. The configuration file is referred to as a kickstart file (.cfg).
A kickstart file can be stored at any of the following supported locations:
- A webserver (access over HTTP or HTTPS)
- A network file server (FTP/NFS)
- A local storage medium that's accessible to the host (CD-ROM/USB)
In this recipe, we will learn how to perform an unattended installation of ESXi using the installer medium, a local USB device, and a network location.
Getting ready
Before you begin, prepare a script for the installation. A default script is available on every ESXi host at /etc/vmware/weasel/ks.cfg. Although the extension is .cfg, the filename doesn't need to be the same. It should be a plain text file with the .cfg extension.
Here is a sample script:
# Sample scripted installation file for vdescribed.lab
# Accept the VMware End User License Agreement
vmaccepteula
# Clear/format existing partitions
clearpart --firstdisk --overwritevmfs
# Set the root password for the DCUI and Tech Support Mode
rootpw password@123
# The install media is in the CD-ROM drive
install --firstdisk --overwritevmfs
# Set a static IP Configuration
network --bootproto=static --device=vmnic0 --ip=192.168.78.91 --netmask=255.255.255.0 --gateway=192.168.78.1 --nameserver=192.168.78.130 --hostname=bkesx02
reboot
# Post Installation Tasks
%firstboot --interpreter=busybox
#Create vSwitch
esxcli network vswitch standard add --vswitch-name=vSwitch2
# Disable ipv6
esxcli network ip set --ipv6-enabled=false
sleep 30
reboot
Once the script has been prepared, store it in one of the support locations. For this recipe, I have stored it on an NFS server.
How to do it...
The following procedure will guide you through the steps that are required to perform a scripted installation of the ESXi host:
- Boot the server using the ESXi ISO. The ISO can be mounted to the server via its IPMI interface (DRAC, ILO, and so on).
- At the Loading ESXi Installer screen, before it automatically boots, hit Shift + O to edit the boot options. This is indicated in the bottom right-hand corner of the screen:

- On the next screen, enter the location of the kickstart file and hit Enter to begin the installation:

- Once the installation is complete, if the kickstart script includes a reboot command, like it does in our script, the server will be rebooted; otherwise, you will be prompted for confirmation.
How it works...
When using a kickstart file, the ESXi installation requires no user intervention. The kickstart file can be configured to run a variety of tasks. It can also be configured to run Python scripts after the installation.
Let's examine the sample script that was used in this recipe. This script is available in the Getting ready section:
|
Script command |
Purpose |
|
vmaccepteula |
Accepts the ESXi End User License Agreement. |
|
clearpart --firstdisk --overwritevmfs |
Used to format the selected disk and overwrite any VMFS volume. This is a destructive process and cannot be reversed. |
|
install --firstdisk --overwritevmfs |
Used to indicate that this is a fresh installation, and the installation will be informed on the first disk in the list by overwriting any VMFS volume. |
|
rootpw password@123 |
Sets the root password as password@123. |
|
network --bootproto=static --device=vmnic0 --ip=192.168.78.91 --netmask=255.255.255.0 --gateway=192.168.78.1 --nameserver=192.168.78.130 --hostname=bkesx02 |
Configures a static IP address, a DNS server address, and a hostname for ESXi. |
|
reboot |
Reboots the ESXi host. |
|
%firstboot --interpreter=busybox |
This is used to indicate that the commands following this line will be executed on first boot. Setting the interpreter to busybox will let you execute the CLI command. Setting it to Python will let you run Python scripts. |
|
esxcli network vswitch standard add -v=vSwitch2 |
Creates a second standard switch with the name vSwitch2. |
|
esxcli network ip set --ipv6-enabled=false |
Disables IPv6. |
|
sleep 30 |
Will not execute any commands for 30 seconds. |
There's more...
Although scripted installation automates the process to some extent, it still requires you to log in to each ESXi host and supply a location for the script file. An unattended deployment should not require any user intervention other than just booting up the server. This is achieved by PXE booting the hosts and using the kickstart script from a network location to run the installation. However, if unattended deployment has been considered, then the recommendation is to use vSphere Auto Deploy, which offers more control and manageability. vSphere Auto Deploy will be covered in a later chapter.
Deploying the vCenter Server Appliance (VCSA)
Deployment of the VCSA is done with an installer, which deploys the VCSA VM onto a chosen ESXi host. The installer GUI collects all the information that's required to configure the vCenter server.
There are two types of deployment:
- Embedded Appliance
- Separate vCenter and PSC Appliance (deprecated)
An external PSC was a requirement in the past if you chose to configure Enhanced Linked Mode for your vCenters. This is no longer the case in vSphere 6.7. With vCenter 6.7, the concept of an external PSC is deprecated, and Enhanced Linked Mode between vCenters with embedded PSCs is now fully supported. We will learn more about Enhanced Linked Mode in the Deploying vCenter Servers in a Linked Mode configuration recipe.
Getting ready
Here is what you will need before you install vCenter Server:
- Download the VMware VCSA 6.7 ISO from https://my.vmware.com/web/vmware/downloads
- Access to a machine (Windows/Linux/macOS) to run the vCenter installer from
- IP address/FQDN of the ESXi host or the vCeter the VCSA will be deployed on
- IP configuration (static IP address, subnet mask, gateway address, and DNS server addresses)
- A DNS host record for the VCSA
How to do it...
The following procedure will walk you through the steps involved in deploying VCSA 6.7 with an embedded PSC:
- Mount the VCSA ISO to a machine to run the installer from.
- Navigate to the CDROM:\\VMware VCSA\vcsa-ui-installer\win32 directory and run installer.exe to bring up the VCSA installer wizard.
Stage 1 of the deployment starts here:
- On the Stage 1: Deploy appliance screen, click Install.
- On the Introduction screen, click Next to continue.
- Accept the End user license agreement and click Next.
- On the Select deployment type screen, choose Embedded Platform Services Controller:

- On the Appliance deployment target screen, supply the IP address of the ESXi host or vCenter the VCSA will be deployed on and provide its credentials. Click Next to continue.
- Accept the vCenter/ESXi certificate by clicking Yes.
- On the Set up appliance VM screen, specify a VM name for the VCSA and set its root password. The VM name doesn't need to be the same as the hostname or FQDN for the appliance:

- On the Select deployment size screen, specify a Deployment size and Storage size for the appliance. There is a default storage size for each deployment size. However, this can be overridden by selecting a larger storage size (Large or X-Large) if you want a larger disk (vmdk) for the /storage/seat partition that stores the stats, tasks, events, and alarms:

- On the Select datastore screen, choose a datastore for the VCSA and click Next to continue. Enable Thin Disk Mode is selected by default.
- On the Configure network settings screen, choose a VM port group for the VCSA VM, the IP version, and set the IP address type to static. Specify the FQDN, IP address/netmask, gateway, and DNS server addresses. Don't change the Common Ports (HTTP/HTTPS) from 80/443 unless absolutely necessary:

- On the Ready to complete stage 1 screen, review the settings and click Finish to start deploying the VM.
- Once the deployment completes, you will be presented with a screen confirming this. Click Continue:

Stage 2 of the deployment starts here:
- On the Install - Stage 2: Set up vCenter Server Appliance with an Embedded PSC screen, click Next.
- On the Appliance Configuration screen, specify a Time synchronization mode and enable SSH access (disabled by default).
- On the SSO configuration screen, choose to Create a new SSO domain. Specify a domain name (the default is vsphere.local) and set the password for the SSO administrator:

- On the Configure CEIP screen, choose to uncheck the Join VMware Customer Experience Improvement Program (CIEP).
- On the Ready to complete screen, review the settings and click FINISH to initiate the configuration:

- You will be prompted with a warning indicating that once you choose to continue, the operation cannot be stopped. Click OK to continue.
- Once the setup/configuration is complete, you will be presented with a confirmation screen and the URL (https://FQDN of vCSA:443) to vCenter's Getting Started page. Click Close to exit the installer.
This finishes the installation, and you will now be able to get to vCenter's Getting Started page:

How it works...
The process of deploying a VCSA is split into two phases. In phase 1, the installer deploys a vCenter appliance virtual machine based on the sizing requirements specified, while in phase 2, you need to specify the SSO configuration. It is a general practice to take a snapshot of the newly deployed VCSA after phase 1 so that it can be reused if phase 2 of the installation were to fail for any reason.
Deploying vCenters in a Linked Mode configuration
When you have more than one vCenter to manage in your environment, being able to manage them under a single view is always beneficial. This is achieved by configuring the PSCs to become part of the same SSO domain, thereby putting them in an Enhanced Linked Mode configuration. vCenters in a Linked Mode will replicate roles and permissions, licenses, and other details, letting the administrator perform a single login into the vSphere Web Client to view and manage the inventory objects of all the linked vCenter Servers.
Getting ready
You will need the following information at hand before you proceed:
- The VMware VCSA 6.7 ISO from https://my.vmware.com/web/vmware/downloads
- Access to a machine (Windows/Linux/macOS) to run the vCenter installer from
- The IP address/FQDN of the ESXi host or the vCenter the VCSA will be deployed on
- The IP configuration (including the static IP address, subnet mask, gateway address, and DNS server addresses)
- A DNS host record created for the new VCSA
- The IP address/FQDN of the peer PSC
- The SSO domain name of the peer PSC
- SSO administrator credentials for the chosen domain
How to do it...
The following procedure will guide you through the steps that are required to configure vCenters in a Linked Mode configuration:
- Go through with Stage 1 of the installation by deploying a new VCSA.
- On the Install - Stage 2: Set up vCenter Server Appliance with an Embedded PSC screen, click Next.
- On the Appliance Configuration screen, specify a Time synchronization mode and enable SSH access (disabled by default).
- On the SSO configuration screen, choose to Join an existing SSO domain. Specify the FQDN/IP of the peer PSC, its SSO domain, and the administrator credentials:

- On the Configure CEIP screen, choose to uncheck the Join VMware Customer Experience Improvement Program (CIEP).
- On the Ready to complete screen, review the settings and click FINISH to initiate the configuration:

- Once the setup/configuration is complete, you will be presented with a confirmation screen, as well as the URL (https://FQDN of VCSA:443) to vCenter's Getting Started page. Click Close to exit the installer.
This finishes the Linked Mode configuration:

Now, when you log in to the web client, it should list all the vCenter servers in the same PSC domain.
How it works...
Once the vCenters are in ELM, they replicate the VMDir contents, license keys, global permissions, tags, and categories.
The replication status can be checked from each node by running the following commands:

The same commands, when executed on the peer vCenter/PSC, should report similar data:

There's more...
You can still deploy external PSCs in vSphere 6.7, although there is no strong use case for doing so. If your 6.5.x or older environment had externalized PSC or SSO servers, they will be migrated/upgraded to become external PSCs by default. These can, however, be converted into embedded VCSAs during the upgrade. We will learn more about this in the next chapter.
Configuring Single Sign-On (SSO) identity sources
An SSO identity source is a repository of users or groups. It can be a repository of local OS users, Active Directory or OpenLDAP and VMDir. Adding an identity source allows you to assign vCenter permissions to users from such a repository.
The VCSA Photon OS (local OS) and SSO domain (vsphere.local) are pre-recognized identity sources. However, when you try to add identity sources, you are allowed to add three different types:
- Active Directory (Windows Integrated Authentication)
- Active Directory over LDAP
- Open LDAP
In this recipe, we will learn how to add an Active Directory identity source.
How to do it...
The following two-part procedure will allow you to join the PSC to Active Directory and add an Active Directory identity source.
Part 1 – Joining the PSC to Active Directory
- Log in to the vCenter Server/PSC as the SSO administrator (administrator@vsphere.local).
- Use the Menu to navigate to Administration:

- On the Administration page, navigate to Single Sign On | Configuration | Active Directory Domain and click on JOIN AD:

- On the Join Active Directory Domain window, specify the name of the domain, OU (optional), and the credentials of a domain user that has permission to join the machine to the domain. Click Join.
- Once done, the host has to be rebooted for the changes to take effect.
- Once the reboot is complete, it should show the vCenter/PSC as joined to the domain:

Part 2 – Adding the identity source
Use the following process to add an identity source:
- Go to the Administration page, navigate to Single Sign On | Configuration | Identity Sources, and click on ADD IDENTITY SOURCE:

- On the Add Identity Source window, set the Identity Source Type to Active Directory (Windows Integrated Authentication). The Domain name will be prepopulated with the FQDN of the domain the PSC is joined to. Use the machine account to authenticate:

- Once done, the Active Directory domain will be listed among the other identity sources:

This completes the process of configuring SSO identity sources on a vCenter Server.
How it works...
VMware SSO is an authentication server that was made available starting with vSphere 5.1. With version 5.5, it has been rearchitected so that it is simple to plan and deploy, as well as easier to manage. With vSphere 6.0 and 6.5, it is now embedded into the PSC.
SSO acts as an authentication gateway, which takes the authentication requests from various registered components and validates the credential pair against the identity sources that are added to the SSO server. The components are registered to the SSO server during their installation.
Once authenticated, the SSO clients are provided with a token for further exchanges. The advantage here is that the user or administrator of the client service is not prompted for a credential pair (username and password) every time it needs to authenticate.
SSO supports authenticating against the following identity sources:
- Active Directory
- Active Directory as an LDAP server
- Open LDAP
- Local OS
Here are some of the components that can be registered with the VMware SSO and leverage its functionality. These components, in SSO terms, are referred to as SSO clients:
- VMware vCenter Server
- VMware vCenter Orchestrator
- VMware NSX
- VMware vCloud Director
- VMware vRealize Automation
- VMware vSphere Web Client
- VMware vSphere Data Protection
- VMware log browser
Configuring vCenter Roles and Permissions
By default, the SSO-Domain\Administrators (vsphere.local\Administrators) group is assigned an Administrator role on the vCenter and is defined as a Global Permission. This means that if there were to be more than one vCenter in an Enhanced Linked Mode configuration, then the vsphere\Administrators group will have Administrator role permissions on all the connected vCenters.
The only member of the vsphere.local\Administators group is the SSO administrator (administator@vsphere.local). Users from other identity sources can be added as members of this group if you so desire.
However, in most environments, although multiple vCenters will be managed under a single ELM umbrella, you will sometimes need to provide vCenter-specific permissions. For instance, if you manage multiple vCenters belonging to different customers, then assigning global permissions is not considered ideal. In such cases, you will need to provide user access to specific vCenters only.
In this recipe, we will learn how to assign vCenter permissions to an Active Directory user/group.
Getting ready
Before you set off and assign vCenter permissions, ensure that the domain hosting the intended user/group is added as an identity source. To learn how to add identity sources, read the Configuring SSO identity sources recipe in this chapter.
How to do it...
The following procedure will guide you through the steps required to configure vCenter permissions to a domain user or group:
- Log in to the vSphere Client (HTML 5) interface as the SSO administrator.
- Select the vCenter object from the inventory, navigate to its Permissions tab, and click + to bring up the Add Permission window:

- On the Add Permission window, select a domain user or group using the search box, and then specify a role. You can also choose to propagate the permissions to waterfall down to other inventory objects. Click OK to confirm:

- Once done, the user/group should be listed under Permissions.
How it works...
Any user account that is used to log in to the vSphere Web Client needs permission on the vCenter to be able to view and manage its inventory. When configuring global permissions, it is important to ensure that it is propagated to the child objects so that the permissions are set on the vCenter Server(s) as well. Permissions can be configured for both local and Active Directory users, provided that the required identity sources are added to SSO.
Joining ESXi to an Active Directory domain
As an administrator managing a vSphere environment, the last thing that you would want to do is share the root password. Remember, a forgotten root password cannot be recovered/reset and will require a reinstallation of ESXi.
Joining an ESXi host to an Active Directory domain will allows users from a particular domain user group to log in to the ESXi host without needing to know the root password. This not only eliminates the need to periodically change the root password, but also enables better auditing.
Getting ready
Here is what you will need before you join the ESXi host to the domain and configure access to it:
- The name of the domain
- The username and password of a domain user that has permissions to join the machine to the domain
- The name of the domain user group that selected users will be a part of
How to do it...
The following procedure will guide you through the steps that are required to join the ESXi host to the domain and allow a domain user group access to it:
- Connect to the vCenter Server's HTML 5 interface, that is, https://FQDN of vCenter/ui.
- Select the ESXi host from the Inventory and navigate to Configure | System | Authentication Services. From here, click on Join Domain.
- On the Join Domain screen, specify a domain name and domain credentials and click OK:

- You should see a Join Windows Domain task complete successfully message in the Recent Tasks pane.
Now that the host is joined to the domain, we can configure it to allow access for a domain user group.
- With the host selected, navigate to Configure | System | Advanced System Settings and click Edit.
- On the Edit Advanced System Settings screen, type esxadmin into the search box to filter the settings.
- Click on the Value field corresponding to the Config.HostAgent.plugins.hostsvc.esxAdminsGroup setting and enter the name of the domain user group:

You should now be able to log in as a domain user to the console (direct/SSH) and DCUI using the following formats:
- user@domain: For example, abhilashgb@vdescribed
- domain\user: For example, vdescribed\abhilashgb
How it works...
Once the ESXi host has been joined to the Active Directory domain, a domain user group can be allowed to log in to the ESXi host. This access is enabled by specifying the name of the user group using the advanced system setting, that is, Config.HostAgent.plugins.hostsvc.esxAdminsGroup.
By default, this user group is granted administrator privileges. This behavior can, however, be changed by using the advanced system setting, that is, Config.HostAgent.plugins.hostsvc.esxAdminsGroupAutoAdd.