In this chapter, we will cover the following:
Understanding each component for a real-world implementation
Planning for High Availability
Designing the VMM server, database, and console implementation
Specifying the correct system requirements for a real-world scenario
Licensing the System Center
Troubleshooting VMM and supporting technologies
This chapter has been designed to provide an understanding of the underlying Virtual Machine Manager (VMM) modular architecture, which is useful for improving implementation and troubleshooting VMM.
As a reference, this book is based on the System Center 2012 R2 Virtual Machine Manager version.
The first version of VMM was launched in 2007 and was designed to manage virtual machines. The VMM 2012 version is a huge product change that will now give you the power to manage your own private cloud.
The focus of VMM 2012 is the ability to create and manage private clouds, retain the characteristics of public clouds by allowing tenants and delegated VMM administrators to perform functions, and abstract the underlying fabric to let them deploy the VM's applications and services. Although they have no visibility into the underlying hardware, there is a uniform resource pooling that allows you to add or remove the capacity as your environment grows. VMM also supports private clouds across supported hypervisors, such as Hyper-V, Citrix, and VMware.
The main strategies of VMM 2012 are as follows:
Application focus: VMM abstracts fabric (host servers, storage, and networking) into a unified pool of resources. It also gives you the ability to use Server App-V to deploy applications and SQL Server profiles to deploy customized database servers.
Service consumer: One of the powerful features of VMM 2012 is its capability to deploy a service to a private cloud. These services are dependent on multiple VMs that are tied together (for example, web frontend servers, application servers, and backend database servers). These services can be provisioned as simply as provisioning a VM, but they all should be provisioned together.
Dynamic Optimization: This strategy will balance the workload in a cluster, while a feature called Power Optimization can turn off physical virtualization host servers when they are not needed. It can then turn them back on when the load increases. This process will automatically move VMs between hosts to balance the load.
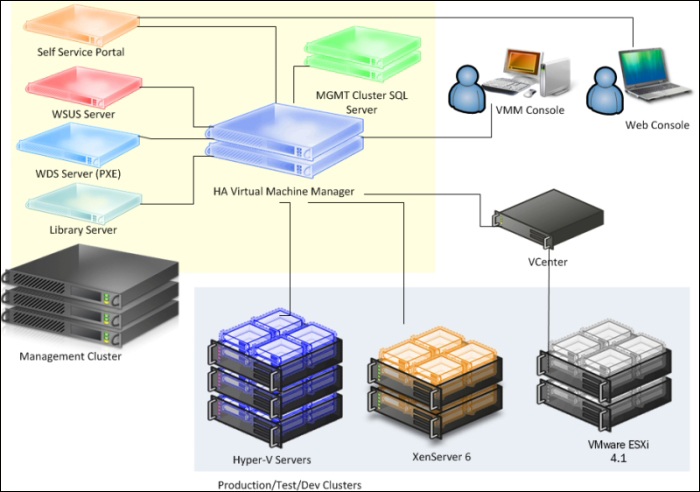
Multivendor hypervisor support: The list of managed hypervisors has been extended. VMM 2012 now manages Hyper-V, VMware, and Citrix XenServer, covering all of the major hypervisors on the market.
The following figure highlights VMM Multivendor hypervisor support:

This is the first step. You need to do an assessment of your current environment to find out how and where the caveats are. You can use the Microsoft Assessment and Planning (MAP) toolkit (download it from http://www.microsoft.com/en-us/download/details.aspx?id=7826) or any other assessment tool to help you carry out a report assessment by querying the hardware, OS, application, and services. It is important to define what you can and need to address and, sometimes, what you cannot virtualize.
Tip
The MAP toolkit will assess your environment using agentless technology to collect data (inventory and performance) to provide reports. Server Consolidation, VMware Discovery , Microsoft Workload Discovery, and Microsoft Private Cloud Fast Track Onboarding Assessment are some of the useful reports that will enable your IT infrastructure planning. For more information, refer to http://social.technet.microsoft.com/wiki/contents/articles/1640.microsoft-assessment-and-planning-toolkit.aspx.
Currently, Microsoft supports the virtualization of all MS infrastructure technologies (for example, SQL, Exchange, AD, Lync, IIS, and file server).
With the assessment report in hand, it is recommended that you spend a reasonable amount of time on the solution design and architecture, and you will have a solid and consistent implementation. The following figure highlights the new VMM 2012 features for you to take into consideration when working on your private cloud design:

In VMM, before deploying VMs and services to a private cloud, you need to set up the private cloud fabric. There are three resources that are included in the fabric in VMM 2012, which are as follows:
Servers: These contain virtualization hosts (Hyper-V, VMware, and Citrix servers) and groups, Preboot eXecution Environment (PXE), update servers (that is, Windows Server Update Services), and other servers.
Networking: This contains the network fabric and devices' configuration (for example, gateways, virtual switches, and network virtualization); it presents the wiring between resource repositories, running instances, VMs, and services.
Storage: This contains the configuration for storage connectivity and management, simplifying storage complexities, and the way storage is virtualized. It is here that you configure the SMI-S and SMP providers or a Windows 2012 SMB 3.0 file server.
If you are really serious about setting up a private cloud, you should carry out a virtualization assessment using MAP, as discussed earlier, and work on a detailed design document that covers the hardware, hypervisor, fabric, and management. With this in mind, the implementation will be pretty straightforward.
System Center 2012 will help you install, configure, manage, and monitor your private cloud from the fabric to the hypervisor and up to the service deployment. It will also allow you to manage the public cloud (Azure).
System Center 2012 Virtual Machine Manager has six components. It is important to understand the role of each component in order to have a better design and implementation.
For small deployments, test environments, or a proof of concept, you can install all of the components in one server, but as is the best practice in the production environments, you should consider separating the components.
Let's start by reviewing each component of VMM 2012 and understanding the role it plays:
VMM console: This application connects to the VMM management server to allow you to manage VMM, centrally view and manage physical and virtual resources (for example, hosts, VMs, services, fabric, and library resources), and carry out tasks on a daily basis, such as VM and services deployment, monitoring, and reporting.
By using the VMM console from your desktop, you will be able to manage your private cloud without needing to remotely connect it to the VMM management server.
The management server: The management server is the core of VMM. It is the server on which the Virtual Machine Manager service runs to process commands and control communications with the VMM console, the database, the library server, and the hosts.
Think of the VMM management server as the heart, which means that you need to design your computer resources accordingly to accommodate such an important service.
Note
For High Availability (HA), VMM Management Server must be deployed as an HA service on Windows Server Failover Cluster. Note, though, that SQL Server, where the VMM database will be installed and the file share for the library share must also be highly available. For more information, check the Planning for High Availability recipe and Chapter 4, Installing a High Available VMM Server.
The following figure shows the Windows Failover Cluster Manager console. For HA, you will need to have at minimum two VMM servers on a cluster.

As is the best practice for medium and enterprise production environments, keep the VMM management server on a separate cluster from the production cluster, due to its crucial importance for your private cloud.
Database: The database server runs SQL Server and contains all of the VMM data. It plays an important role when you have a clustered VMM deployment by keeping the shared data. The best practice is to also have the SQL database in a cluster.
VMM library: The VMM library servers are file shares, a catalog that stores resources, such as VM templates, virtual hard drive files, ISOs, scripts, and custom resources with a
.crextension, which will all be visible and indexed by VMM and then shared among application packages, tenants, and self-service users in private clouds.The library has been enhanced to support services and the sharing of resources. It is a store for drivers for Bare Metal deployments, SQL data-tier applications (SQL DAC), and Web Deploy packages.
In a distributed environment, you can group equivalent sets of resources and make them available in different locations by using resource groups. You can also store a resource in a storage group that will allow you to reference that group in profiles and templates rather than in a specific Virtual Hard Disk (VHD). This is especially important when you have multiple sites, and VMM will automatically select the right resource from a single reference object. This essentially enables one template that can reference an object that can be obtained from multiple locations.
You can also have application profiles and SQL profiles (answer files for the configuration of the application or SQL) to support the deployment of applications and databases to VM after the base image is deployed. Application profiles can be Server App-V packages, web applications, or a SQL data-tier.
Self Service Portal: The web-based Self Service Portal was removed from SC 2012 VMM.
VMM command shell: VMM is based on PowerShell. Everything you can do on the GUI, you can do by using PowerShell. VMM PowerShell extensions make available the cmdlets that perform all of the functions in VMM 2012.
As you may have noticed, although the VMM management is the core, each component is required in order to provide a better VMM experience. In addition to this, for a real-world deployment, you also need to consider implementing other System Center family components to complement your design. Every System Center component is designed to provide part of the private cloud solution. The Microsoft private cloud solution includes the implementation of VMM 2012 plus the following utilities:
System Center 2012 App Controller: This provides a common self-service experience across private and public clouds that can help application owners easily build, configure, deploy, and manage services
System Center 2012 Configuration Manager: This provides comprehensive configuration management for the Microsoft platform that can help users with the devices and applications they need in order to be productive while maintaining corporate compliance and control
System Center 2012 Data Protection Manager: This provides unified data protection for the Windows environment, delivering protection and restore scenarios from the disk, tape, off premise, and cloud
System Center 2012 Endpoint Protection: This is built on the System Center Configuration Manager and provides threat detection of malware and exploits as part of a unified infrastructure to manage client security and compliance to simplify and improve the endpoint protection
System Center 2012 Operations Manager: This provides deep application diagnostics and infrastructure monitoring to ensure the predictable performance and availability of vital applications, and it offers a comprehensive view of the data center, private cloud, and public clouds
System Center 2012 Orchestrator: This provides the orchestration, integration, and automation of IT processes through the creation of runbooks to define and standardize best practices and improve operational efficiency
System Center 2012 Service Manager: This provides flexible self-service experiences and standardized data center processes to integrate people, workflows, and knowledge across enterprise infrastructure and applications
When deploying System Center, there are some other systems and configurations you need to consider.
Windows Azure Pack (WAP) is an administrator portal to manage resources that integrate with System Center and Windows Server to provide a customizable self-service portal to manage services such as websites, Virtual Machines, and Service Bus; it also includes capabilities for automating and integrating additional custom services. For more information, refer to http://www.microsoft.com/en-us/server-cloud/products/windows-azure-pack/.
Service Reporting, an optional component of System Center 2012 R2, enables IT (particularly hosting providers) to create detailed views of the virtual machines' consumption of the resources (CPU, memory, storage, and networking) for each customer (tenant). For more information, refer to http://technet.microsoft.com/en-us/library/dn251058.aspx.
Although the domain controller is not part of the System Center family and is not a VMM component, it plays an important role in the deployment of a private cloud as VMM requires it to be installed on a domain environment.
Windows Server Update Service (WSUS) plays an important role with reference to the private cloud as it is used to update the Hyper-V hosts, library servers, or any other role for compliance and remediation.
The App Controller provides a self-service experience through a web portal that can help you easily configure, deploy, and manage VMs and services across private, third-party hosters (that support Microsoft Hyper-V) and public clouds (Azure). For example, moving a VM from a private cloud to Azure, creating checkpoints, granting access, scaling out deployed services, and so on.
The App Controller is a replacement for the VMM Self-Service Portal since SC 2012 SP1 and it is the key for Cloud mobility.
The following table will guide you through choosing the System Center component that is necessary as per your deployment:
Note
Although Configuration Manager (SCCM) is not mentioned in the following table, it plays an important role when it comes to patching Virtual Machine and now you can use SCCM Task Sequence (TS), which is a new feature in SC 2012 R2, on a single process to deploy an OS to a Virtual Hard Disk. For more information, refer to http://technet.microsoft.com/en-us/library/dn448591.aspx.
You should also check Service Management Automation, which will enable Orchestrated offline VM Patching. For more information, refer to http://blogs.technet.com/b/privatecloud/archive/2013/12/07/orchestrated-vm-patching.aspx.
|
Scenarios |
Enabling technologies | ||||
|---|---|---|---|---|---|
|
AppCtrl |
Operations Manager |
Orchestrator |
Service Manager |
VMM | |
|
The fabric provider | |||||
|
Bare Metal deploy |
√ | ||||
|
Integration with network and storage |
√ |
√ | |||
|
Host patching |
√ | ||||
|
Host Optimization/Power Optimization |
√ | ||||
|
Monitoring of the fabric |
√ |
√ | |||
|
Capacity reporting |
√ |
√ | |||
|
The service provider | |||||
|
Service templates (offerings) |
√ | ||||
|
Service and VM catalog |
√ |
√ |
√ | ||
|
Life cycle (create, upgrade, and retire) |
√ |
√ |
√ |
√ | |
|
Application and SLA monitoring |
√ | ||||
|
SLA and capacity reporting |
√ |
√ | |||
|
The service consumer | |||||
|
Request quote or capacity (cloud) |
√ |
√ |
√ | ||
|
Request/deploy VM |
√ |
√ |
√ |
√ |
√ |
|
Request/deploy service |
√ |
√ |
√ |
√ |
√ |
|
Quota enforcement |
√ |
√ | |||
|
Request approvals |
√ |
√ | |||
The Planning for High Availability recipe
Chapter 9, Integration with System Center Operations Manager 2012 R2
Chapter 10, Scripting in Virtual Machine Manager
High Availability is important when your business requires minimum or no downtime, and planning for it in advance is very important.
Based on what we learned about each component, we now need to plan the HA for each VMM component.
Start by planning the HA for the core component, followed by every VMM component of your design. It is important to consider the hardware and other System Center components as well the OS and software licenses.
When planning for highly available VMM management servers, you should first consider where you can place the VMM cluster. As per best practices, the recommendation is to install the VMM cluster on a management cluster, preferably on physical servers, if using a converged network for your virtual network. However, if you plan to install highly available VMM management servers on the managed cluster, you need to take into consideration the following points:
Only one highly available VMM management server is allowed per failover cluster.
Despite the possibility of having a VMM management server installed on all cluster nodes, only one node can be active at a time.
To perform a planned failover, use Failover Cluster Manager. The use of the VMM console is not supported.
In a planned failover situation, ensure that there are no running tasks on the VMM management server, as it will fail during a failover operation and will not automatically restart after the failover operation.
Any connection to a highly available VMM management server from the VMM console will be disconnected during a failover operation, and it will be reconnected right after.
The failover cluster must run Windows Server v2012 or higher in order to be supported.
The highly available VMM management server must meet the system requirements. For information about system requirements for VMM, see the Specifying the correct system requirements for a real-world scenario recipe in this chapter.
In a highly available VMM management deployment, you will need a domain account to install and run the VMM management service. You are required to use Distributed Key Management (DKM) to store the encryption keys in Active Directory.
A dedicated and supported version of Microsoft SQL Server should be installed. For supported versions of SQL Server for the VMM database, refer to the Specifying the correct system requirements for a real-world scenario recipe.
The following sections are the considerations for SQL Server and the VMM library in an HA environment.
In an enterprise deployment of VMM, it is recommended that you have a SQL Server cluster to support the HA VMM, preferably on a cluster separated from the VMM cluster. VMM 2012 R2 supports SQL Server AlwaysOn Availability Groups. The following link will show you a good example of how you can set it up:
As the best practice in an enterprise deployment, it is highly recommended that you use a highly available file server to host the VMM library shares, as VMM does not provide a method to replicate files in the VMM library, and they need to be replicated outside of VMM.
As a suggestion, you can use the Microsoft Robocopy tool to replicate the VMM library files, if necessary.
When planning a VMM 2012 design for deployment, consider the different VMM roles, keeping in mind that VMM is part of the Microsoft private cloud solution. If you are considering a private cloud, you will need to integrate VMM with the other System Center family components.
Tip
By integrating VMM 2012 with Microsoft Server App-V, you can create application profiles that will provide instructions for installing Microsoft App-V applications, Microsoft Web Deploy applications, and Microsoft SQL Server data-tier applications. The profiles will also provide instructions for running scripts when deploying a virtual machine as part of a service. It is important to note that if you use Server App-V, you should confirm with the application owner whether the app will be supported if it's sequenced. Web Deploy and SQL DAC would not have the same issue.
In VMM, you can create the hardware, guest operating system, SQL Server, and application profiles that will be used in a template to deploy virtual machines. These profiles are essentially answer files to configure the application or SQL during the setup.
You can create a private cloud by combining hosts, even from different hypervisors (for example, Hyper-V, VMware, and Citrix) with networking, storage, and library resources.
To start deploying VMs and services, you first need to configure the fabric.
Create a spreadsheet with the server names and the IP settings of every System Center component you plan to deploy, as shown in the following table. This will help you manage and integrate the solution.
|
Server name |
Role |
IP settings |
|---|---|---|
|
Vmm-mgmt01 |
VMM Management Server 01 |
IP: 10.16.254.20/24 GW: 10.16.254.1 DNS: 10.16.254.2 |
|
Vmm-mgmt02 |
VMM Management Server 02 |
IP: 10.16.254.22/24 GW: 10.16.254.1 DNS: 10.16.254.1 |
|
Vmm-consol01 |
VMM console |
IP: 10.16.254.50/24 GW: 10.16.254.1 DNS: 10.16.254.2 |
|
Vmm-lib01 |
VMM library |
IP: 10.16.254.25/24 GW: 10.16.254.1 DNS: 10.16.254.2 |
|
w2012-sql |
SQL Server 2012 |
IP: 10.16.254.40/24 GW: 10.16.254.1 DNS: 10.16.254.2 |
The following rules need to be considered when planning a VMM 2012 deployment:
The computer name cannot contain the character string "SCVMM" (for example, srv-scvmm-01) and cannot exceed 15 characters.
Your VMM database must use a supported version of SQL Server to perform a VMM 2012 deployment. Express editions of Microsoft SQL Server are no longer supported for the VMM 2012 database. For more information, check the system requirements specified in the Specifying the correct system requirements for a real- world scenario recipe in this chapter.
VMM 2012 R2 does not support a library server on a computer that runs Windows Server 2003/2008; it now requires Windows Server 2012 as a minimum, but for consistence and standardization, I do recommend that you install it on Windows Server 2012 R2.
VMM 2012 no longer supports Microsoft Virtual Server 2005 R2 Hosts. If you are upgrading from a previous version of VMM that has Virtual Server hosts, they will be removed from the VMM 2012 database. If you do not want these hosts to be removed automatically, remove the hosts manually before you start the upgrade process.
Hosts that run the following versions of VMware ESX and VMware vCenter Server are supported:
ESX 3.x
ESX 4.1
ESX 5.0, ESX 5.1
Upgrading a previous version of VMM to a highly available VMM 2012 requires additional preparation. Refer to Chapter 2, Upgrading from Previous Versions, for this purpose.
If you're planning for High Availability of VMM 2012, be sure to install SQL Server on a Cluster and on separate servers as it cannot physically be located on the same servers as your VMM 2012 management server.
The VMM management server must be a member of a domain. (This rule does not apply to the managed hosts, which can be on a workgroup.)
The startup RAM for the VMM management server (if running on VM with dynamic memory enabled) must be at least 2048 MB.
The VMM library does not support DFS Namespaces (DFSN) or DFS Replication (DFSR).
VMM does not support file servers configured with the case-insensitive option for Windows Services for Unix as the network filesystem case control is set to
ignore. Refer to the Windows Services for UNIX 2.0 NFS Case Control article available at http://go.microsoft.com/fwlink/p/?LinkId=102944 to learn more.The VMM console machine must be a member of a domain.
For a complete design solution, there are more items you need to consider.
VMM provides support for both block-level storage (fibre channel, iSCSI, and Serial Attached SCSI (SAS) connections) and file storage (on SMB 3.0 network shares, residing on a Windows file server or on a NAS device).
By using storage providers, VMM enables discovery, provision, classification, allocation, and decommissioning.
Storage classifications enable you to assign user-defined storage classifications to discovered storage pools for Quality of Service (QoS) or chargeback purposes.
Tip
You can, for example, assign a classification of GOLD to storage pools that have the highest performance and availability, SILVER for high performance, and BRONZE for low performance.
In order to use this feature, you will need the SMI-S provider.
VMM 2012 R2 can discover and communicate with Storage Area Network (SAN) arrays through the Storage Management Initiative (SMI-S) provider and SMP provider.
If your storage is SMI-S compatible, you must install the storage provider on a separately available server (do not install the VMM management server) and then add the provider to the VMM management. If your storage is compatible with SMP, it does not require a provider installation.
Tip
Each vendor has its own SMI-S setup process. My recommendation is that you contact the storage vendor to ask for a storage provider compatible with VMM 2012 R2.
CIM-XML is used by VMM to communicate with the underlying SMI-S providers since VMM never communicates with the SAN arrays itself.
By using the storage provider to integrate with the storage, VMM can create LUNs (both GPT and MBR) and assign storage to hosts or clusters.
Note
Do not install a storage provider other than the WMI SMP providers from Dell EqualLogic and Nexsan in the VMM Management Server as they are not supported.
VMM 2012 also supports the SAN snapshot and clone feature, allowing you to duplicate a Logical Unit Number (LUN) through a SAN copy-capable template to provide for new VMs, if you are hosting them in a Hyper-V platform. You will need to provision the outside of VMM for any other VMs hosted with VMware or Citrix hosts.
This capability enables VMM 2012 to identify the hardware, install the Operating System (OS), enable the Hyper-V role, and add the machine to a target-host group with streamlined operations in an automated process.
The PXE capability is required and is an integral component of the server pool. The target server will need to have a Baseboard Management Controller (BMC) that supports one of the following management protocols:
Data Center Management Interface (DCMI) 1.0
Systems Management Architecture for Server Hardware (SMASH) 1.0
Intelligent Platform Management Interface (IPMI) 1.5 or 2.0
HP Integrated Lights-Out (iLO) 2.0
Enterprise and hosting companies will benefit from the ability to provide new Hyper-V servers without having to install the Operating System manually on each machine. By using BMC and integrating with Windows Deployment Services (WDS), VMM deploys the OS to designated hosts through the boot from the VHD(X) feature.
To ensure that users can perform only assigned actions on selected resources, create tenants, self-service users, delegated administrators, and read-only administrators in VMM using the VMM console. You will need to create Run As accounts to provide necessary credentials for performing operations in VMM (for example, adding hosts).
Run As accounts are a very useful addition to enterprise environments. These accounts are used to store credentials that allow you to delegate tasks to other administrators and self-service users without exposing sensitive credentials.
Note
By using Windows Data Protection API (DPAPI), VMM provides OS-level data protection when storing and retrieving the Run As account.
There are several different categories of Run As accounts, which are listed as follows:
Host computer: This is used to provide access to Hyper-V, VMware ESX, and Citrix XenServer hosts
BMC: This is used to communicate with BMC on the host computer for out-of-band management
Network device: This is used to connect to network load balancers
Profile: This is to be used for service creation in the OS and application profiles as well as SQL and host profiles
External: This is to be used for external systems such as System Center Operations Manager
Only administrators or delegated administrators can create and manage Run As accounts.
When designing the VMM implementation, you need to plan which ports you are going to use for communication and file transfers between VMM components. Based on the chosen ports, you will also need to configure your host and external firewalls. Refer to the Configuring ports and protocols on the host firewall for each VMM component recipe in Chapter 3, Installing VMM 2012 R2.
My recommendation is to create a big CSV volume spread across multiple disk spindles, as it will give great storage performance for VMs, as opposed to creating volumes based on the VHD purpose (for example, OS, data, and logs).
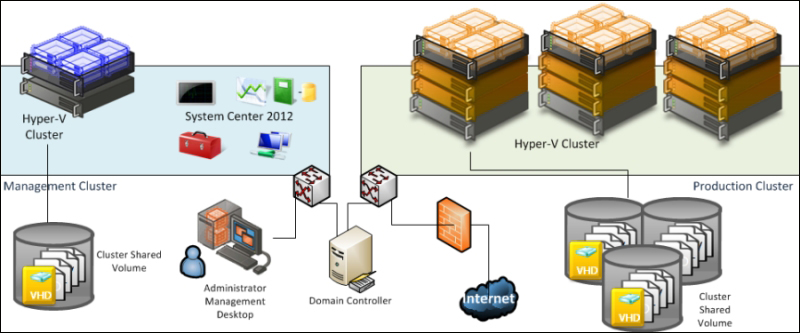
The best practice is to have a separate management cluster to manage the production, test, and development clusters.
In addition to this, although you can virtualize the domain controllers with Windows 2012, it is not the best practice to have all the domain controllers running on the management clusters, as the cluster and System Center components highly depend on the domain controllers.
The following figure shows you a two-node management cluster with System Center 2012 and SQL Server cluster installed in separate VMs to manage the production cluster:
In a small environment, you can have all the VMM components located on the same server. A small business may or may not have High Availability in place as VMM 2012 is now a critical component for your private cloud deployment.
Start by selecting the VMM server's location, which could be a physical server or a virtual machine.
You can install SQL Server on the VMM server as well, but as VMM 2012 does not support SQL Express editions, you will need to install SQL Server first and then proceed with the VMM installation.
If you are managing more than 10 hosts in the production environment, my recommendation would be that you have SQL Server running on a separate machine.
It is important to understand that when deploying VMM in production environments (real-world scenarios), the business will require a reliable system that it can trust.
The following figure illustrates a real-world deployment where all VMM 2012 components are installed on the same VM and SQL is running on a separate VM:
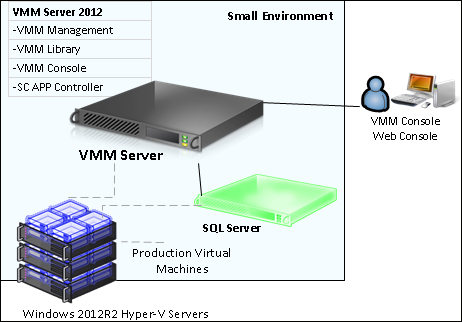
I would recommend up to 50 hosts in a lab environment with SQL Server and all VMM components installed on a single VM. This will work well, but I would not recommend this installation in a production environment.
In a medium- or large-scale environment, the best practice is to split the roles across multiple servers or virtual machines. By splitting the components, you can scale out and introduce High Availability to the System Center environment.
In the following design, you can see each component and what role it performs in the System Center Virtual Machine Manager environment:
When designing an enterprise private cloud infrastructure, you should take into consideration some key factors such as business requirements, company policies, applications, services, workloads, current hardware, network infrastructure, storage, security, and users.
The following is a sample of a real-world infrastructure that can support up to 3000 VMs and 64 server nodes that run Windows 2012 R2 Hyper-V.
The number of VMs you can run on an implementation such as this will depend on some key factors. Do not take the following configuration as a mirror for your deployment but as a starting point. My recommendation is that you start understanding the environment, and then run a capacity planner such as a MAP toolkit. It will help you gather information that you can use to design your private cloud.
I am assuming a ratio of 50 VMs per node cluster with 3 GB of RAM, which has been configured to use Dynamic Memory (DM).
Servers
64 servers (4 clusters x 16 nodes)
A dual processor of 6 cores, which makes it 12 cores in total
192 GB RAM
2 x 146 GB local HDD (ideally SDD) in Raid 1
Storage
Switch and host redundancy
A fibre channel or iSCSI
An array with the capacity to support customer workloads
A switch with connectivity for all hosts
Network
A switch that provides switch redundancy and sufficient port density and connectivity to all hosts. It provides support for VLAN tagging and trunking. NIC Team and VLAN are recommended for better network availability, security, and performance achievement.
Storage connectivity
If it uses a fibre channel: 2 x 4 GB HBAs
If it uses ISCSI: 2 x dedicated NICs (recommended 10 GbE)
Network connectivity
If it maintains a 1 GbE connectivity: 6 dedicated 1 GbE (live migration, CSV, management, virtual machines' traffic)
If it maintains a 10 GbE connectivity: 3 dedicated NICs 10 GbE (live migration, CSV, management, and virtual machines' traffic)
System Center 2012 SP1 VMM introduced multi-tenancy. This is one of the most important features for hosting companies as they only need to install a single copy of System Center VMM and then centralize their customer management, each running in a controlled environment in their own domain. Hosting companies want to maximize their compute capacity and a VLAN segmented on hardware won't allow for that. Network virtualization moves the isolation up to the software stack, enabling the hoster to maximize all the capacity and isolate customers via software-defined networking.
VMM 2012 R2 brings a new networking feature: network virtualization. Taking advantage of Windows Server 2012 R2's new features, VMM now delivers site-to-site NVGRE gateway for Hyper-V network virtualization. This new capability will now enable you to use network virtualization to support multiple site-to-site tunnels and direct access through a NAT firewall. Networking Virtualization (NV) now uses the NVGRE protocol, allowing network load balancers to act as NV gateways. Plus, switch extensions can make use of NV policies to interpret the IP information in packets being sent, and the communication between Cisco switches and VMM is now expanded to support Hyper-V NV.
The Planning for High Availability recipe
The Configuring ports and protocols on the host firewall for each VMM component recipe in Chapter 3, Installing VMM 2012 R2
The Rapid Provisioning of Virtual Machines Using SAN Copy Overview article at http://technet.microsoft.com/en-us/library/gg610594.aspx
The Understanding Generation 1 and Generation 2 Virtual Machines in VMM article at http://technet.microsoft.com/en-us/library/dn440675.aspx
For more information on SMI-S, refer to the link at http://www.snia.org/ctp/conformingproviders/index.html
For more information on DPAPI architecture and security, visit the link at http://go.microsoft.com/fwlink/p/?LinkID=213089
In a real-world production environment, you need to specify a system according to the design and business requirements.
When specifying the hardware for your private cloud deployment, take into consideration future growth needs. It is also important to apply the latest OS and software updates.
Use the following tables to carry out an extensive documentation of the hardware and software requirements for your deployment.
Create a document that outlines every solution component, describing the system requirements, before starting to implement it.
The following table shows you the supported OS and servers for SC 2012 R2:
|
Component |
OS/Server supported |
Version |
|---|---|---|
|
VMM server |
Windows Server 2012 Windows Server 2012 R2 |
64 bit (Standard and Datacenter) |
|
VMM database |
SQL Server 2008 R2 SP1 or higher |
Standard, Enterprise, and Datacenter |
|
SQL Server 2012 and SQL Server 2012 SP1 | ||
|
VMM console |
Windows Server 2008 R2 SP1 |
64 bit (Standard, Enterprise, and Datacenter) |
|
Windows Server 2012 and Windows 2012 R2 |
64 bit (Standard and Datacenter) | |
|
Windows 7 SP1 |
x86 and x64 Enterprise and Ultimate | |
|
Windows 8 and Windows 8.1 |
x86 and x64 | |
|
VMM library |
Windows Server 2008 R2 SP1 |
Standard, Enterprise, and Datacenter (full installation or Server Core installation) |
|
Windows Server 2012 and Windows 2012 R2 | ||
|
SC App Controller |
Windows Server 2008 R2 SP1 |
Standard, Enterprise, and Datacenter |
|
Windows Server 2012 and Windows 2012 R2 |
64 bit (Standard and Datacenter) | |
|
WSUS |
Windows Server 2012 and Windows 2012 R2 - WSUS 3.0 SP2 |
64 bit (Standard and Datacenter) |
|
PXE |
Windows Server 2008 R2, Windows Server 2012, or Windows Server 2012 R2 |
64 bit (Standard and Datacenter) |
For any procedure that uses .vhdx, the library server must be running on Windows Server 2012.
The following are the hardware requirements to consider when specifying your VMM environment. The minimum values are the Microsoft-recommended values.
The first scenarios would be for up to 50 hosts, SMB environments, POC, and demos (all components installed on a single server). Although, for this type of scenario, you can have SQL installed on the VMM management server, the recommendation is to have SQL Server installed on another server:
|
Hardware component |
Minimum |
Recommended |
|---|---|---|
|
Processor |
One Processor, 2 GHz (x64) |
Dual processor, dual core, 2.8 GHz (x64) or higher |
|
RAM |
4 GB |
6 GB *2 |
|
Hard disk space (recommended OS partition) *4 |
20 GB |
40 GB or higher |
|
Hard disk space (VMM components )*1 *4 |
80 GB *2 |
150 GB *2 |
|
Hard disk space (VMM library) *1 *4 |
As a minimum, I recommend 80 GB, taking into consideration some samples from real-world implementation. However, this will vary depending on business requirements, the number and size of the files stored, and especially when working with templates. | |
|
Roles |
VMM management VMM library VMM console VMM database (SQL Server full version—Standard or Enterprise) *3 | |
|
*1 Excluding OS partition *2 With a full version of Microsoft SQL Server installed on the same server *3 The recommendation is to have SQL Server installed on another server *4 The recommended minimum total hard disk space for this deployment with full SQL is 270 GB | ||
The second scenario would be for up to 150 hosts. In this scenario, the recommendation is to have each component installed on a separate server, especially the VMM library server. Although (and this is not recommended) you can install SQL Server on the VMM management server as well.
The following table will give you hardware requirements for the VMM management server:
|
Hardware component |
Minimum |
Recommended |
|---|---|---|
|
Processor |
Pentium 4, 2 GHz (x64) |
Dual processor, dual core, 2.8 GHz (x64) or greater |
|
RAM |
2 GB |
4 GB *2 / 6 GB *3 |
|
Hard disk space *1 |
2 GB *2/ 80 GB *3 |
40 GB *2 / 150 GB *3 |
|
*1 Excluding OS partition *2 Without a local VMM database (SQL Server installed) *3 With a local VMM database (Microsoft SQL Server installed on the same server) | ||
The following table will give you hardware requirements for the VMM database server:
|
Hardware component |
Minimum |
Recommended |
|---|---|---|
|
Processor |
Pentium 4, 2.8 GHz |
Dual core 64 bit, 2 GHz |
|
RAM |
2 GB |
4 GB |
|
Hard disk space* |
80 GB |
150 GB |
|
* Excluding OS partition | ||
The following table will give you hardware requirements for the VMM console:
|
Hardware component |
Minimum |
Recommended |
|---|---|---|
|
Processor |
Pentium 4, 550 MHz |
Pentium 4, 1 GHz or higher |
|
RAM |
512 MB |
1 GB |
|
Hard disk space * |
512 MB |
2 GB |
|
* Excluding OS partition | ||
The following table will give you hardware requirements for the VMM library server.
The minimum and recommended requirements for a VMM library server will be determined by the quantity and size of the files that will be stored.
|
Hardware component |
Minimum |
Recommended |
|---|---|---|
|
Processor |
Pentium 4, 2.8 GHz |
Dual core 64 bit, 3.2 GHz or higher |
|
RAM |
2 GB |
2 GB |
|
Hard disk space |
As a minimum, I recommend 80 GB, taking into consideration the following table that contains some samples of real image sizes. However, the recommended size will vary depending on business requirements and on the number and size of files stored, especially when working with templates. | |
The following table will give you sizes of different ISO images:
|
Image |
ISO size |
Application |
|---|---|---|
|
en_windows_server_2008_r2_with_sp1_vl_build_x64_dvd_617403 |
2.94 GB |
Windows 2008 R2 |
|
en_install_disc_windows_small_business_server_2011_standard_x64_dvd_611535 |
6.35 GB |
SBS 2001 |
|
en_office_professional_plus_2010_x86_515486 |
650 MB |
Office 2010 |
The following table will give you hardware requirements for the VMM management server:
|
Hardware component |
Minimum |
Recommended |
|---|---|---|
|
Processor |
Pentium 4, 2.8 GHz (x64) |
Dual processor, dual core, 3.6 GHz or higher (x64) |
|
RAM |
4 GB |
8 GB |
|
Hard disk space* |
10 GB |
50 GB |
|
* Excluding OS partition | ||
The following table will give you hardware requirements for the VMM database server:
|
Hardware component |
Minimum |
Recommended |
|---|---|---|
|
Processor |
Dual-Core 64-bit, 2 GHz |
Dual core 64 bit, 2.8 GHz |
|
RAM |
4 GB |
8 GB |
|
Hard disk space * |
150 GB |
200 GB |
|
* Excluding OS partition | ||
The following table will give you hardware requirements for the VMM console:
|
Hardware component |
Minimum |
Recommended |
|---|---|---|
|
Processor |
Pentium 4, 1 GHz |
Pentium 4, 2 GHz or higher |
|
RAM |
1 GB |
2 GB |
|
Hard disk space * |
512 MB |
4 GB |
|
* Excluding OS partition | ||
The following table will give you hardware requirements for the VMM library server.
The minimum and recommended requirements for a VMM library server will be determined by the quantity and size of the files that will be stored.
|
Hardware component |
Minimum |
Recommended |
|---|---|---|
|
Processor |
Pentium 4, 2.8 GHz |
Dual core 64 bit, 3.2 GHz or higher |
|
RAM |
2 GB |
2 GB |
|
Hard disk space |
As a minimum, I recommend 80 GB*, taking into consideration the following table that contains some samples of real image sizes. However, the recommended size will vary depending on business requirements and the number and size of files stored, especially when working with templates. | |
|
* Excluding OS partition | ||
The following table shows you the software requirements for the VMM management for SC 2012 R2:
|
Software requirement |
Notes |
|---|---|
|
Windows Remote Management (WinRM) 2.0 |
The WinRM service is set to start automatically (delayed start). If it is not configured in this way (manually modified or by GPO), you must configure and start it before installing VMM. |
|
Microsoft .NET Framework 4.0, or Microsoft .NET Framework 4.5 |
This is included in Windows Server 2012/ R2. Microsoft .NET Framework 4.5 is available at http://go.microsoft.com/fwlink/p/?LinkId=267119. |
|
Windows Automated Installation Kit (AIK) |
To install the Windows AIK, you need to download the ISO from http://go.microsoft.com/fwlink/p/?LinkID=194654, burn the ISO file to a DVD or map the ISO if VMM is a VM, and then install the Windows AIK. Important Windows ADK replaced Windows Automated Installation (Windows AIK) as a VMM prerequisite in VMM 2012 R2. |
|
A supported version of SQL Server (if you're installing SQL on the VMM management server) |
Refer to the first table in this section for the supported OS's and servers for SC 2012 R2. |
|
SQL Server 2012 Command Line Utilities |
The SQLCMD utility allows users to connect to, send Transact-SQL batches from, and output row set information from SQL Server 2005, SQL Server 2008, SQL Server 2008 R2, and SQL Server 2012 instances (http://go.microsoft.com/fwlink/?LinkID=239650&clcid=0x409). |
|
Microsoft SQL Server Native Client |
This contains runtime support for applications using native code APIs (ODBC, OLE DB, and ADO) to connect to Microsoft SQL Server 2005, 2008, 2008 R2, and SQL Server 2012. SQL Server Native Client is used to enhance applications that need to take advantage of new SQL Server 2012 features (http://go.microsoft.com/fwlink/?LinkID=239648&clcid=0x409). |
The following table shows the requirement for the VMM console:
|
Software requirement |
Notes |
|---|---|
|
Windows PowerShell 2.0 |
This is included in Windows Server 2008 R2 and Windows 7 |
|
At least Microsoft .NET Framework 3.5 Service Pack 1 (SP1) |
On a computer that runs Windows 7, .NET Framework 3.5.1 will be installed by default. On a computer that runs Windows Server 2008 R2, if the .NET Framework 3.5.1 feature is not installed (not installed by default), the VMM setup wizard will install it. |
The following table shows the requirement for the VMM library:
|
Software requirement |
Notes |
|---|---|
|
Windows Remote Management (WinRM) 1.1 or 2.0 |
Version 1.1 is included in Windows Server 2008 Version 2.0 is included in Windows Server 2008 R2 By default, the WinRM (WS-Management) service is set to start automatically (delayed start). If it is not configured in this way (manually modified or by GPO), it must be configured and started before the setup can continue. |
Download the Windows Assessment and Deployment Kit (ADK) for Windows 8.1 at http://www.microsoft.com/en-us/download/details.aspx?id=39982
System Center 2012 is licensed with two versions, Standard and Datacenter. The same capabilities across editions are differentiated only by virtualization rights. All System Center components are included in these two editions.
The license is now required only to manage endpoints. No additional licenses are required for management consoles and they are available exclusively with Software Assurance.
As part of the private cloud design solution, you need to define the license that you will need, based on your solution design and business requirements.
Note
For updated information about licensing, go to https://www.microsoft.com/licensing/about-licensing/SystemCenter2012-R2.aspx.
The following is the license summary for System Center 2012 R2:
For endpoints being managed: No additional licenses are needed for management servers or SQL Server technology
Consistent licensing model across editions: Processor-based license that covers server management (up to two processors). User-based or OS environment (OSE)-based license for client management
|
System Center 2012 editions |
Datacenter |
Standard |
|---|---|---|
|
Recommendation |
For highly virtualized environments |
For lightly or non-virtualized environments |
|
Virtualization rights |
Unlimited |
Two Operating Systems |
|
Capabilities |
All SC components and all workload types |
All SC components and all workload types |
|
License type |
This recipe will take you through the process of troubleshooting VMM and its supporting technologies for a successful VMM deployment.
Having an understanding of the core technologies that VMM depends on in order to work correctly is the initial step to troubleshooting VMM:
WS Management (WinRM)
WMI
BITS
DCOM
WCF
Troubleshooting is never an easy task, but VMM 2012 provides tools and ways to help you find and remediate an issue.
The following are some techniques you can use to troubleshoot:
Event logs: A good starting point is to look at the event logs. Look for OS- and VMM-related errors or failures. A problem with the Operating System or one of its core services could result or lead to a problem in VMM.
For example, if you are running SQL Server on the same server and it did not start, the VMM management service will not start either and VMM operations will fail as a direct result of this. You can easily find this by looking for errors in the system or application logs or errors that would indicate, in this example, that the service is not running (for this example, you can also check
Services.msc).VM manager log: When looking for VMM errors, it is recommended that you look at the VM Manager log as well. To do so, perform the following steps on the VMM server that runs Windows 2012:
In the Server Manager window, click on Tools.
Select Event Viewer, expand Applications and Services logs, and then select the VM Manager log.
VMM installation-related troubleshooting logs: VMM records information about the VMM agent installation. However, if the installation logging is not sufficient to determine the cause of failure, you can enable tracing by using the VMM MPS Reports tool and then restart the installation.
VMM server setup logging: Installation logs are written, by default, to the
C:\ProgramData\VMMLogshidden folder.VMM agent installation logging: When installing an MSI package, such as installing the VMM agent manually, you can enable logging using the following syntax:
msiexec /I <MSIPackageName.msi> /L*V <path\logfilename>.log
For example, using the syntax, we can come up with something like the following command:
msiexec /I "C:\setup\vmmAgent.msi" /L*V vmmagent.logThe local agent installation information is logged in the
C:\ProgramData\VMMLogshidden folders.Look for the log file,
vmmAgent.msi_<m-d-yyy_hh-mm-dss>.log.Troubleshooting WinRM: To check whether WinRM has remote access, check the following:
The Security Identifier (SID) in RootSDDL maps to the Virtual Machine Manager Servers local group on each Hyper-V host
The local group contains the account that VMM management service runs as a service
A good understanding of what a successful installation log contains from a POC or a pilot environment is important to identify possible issues, especially if it appears when deploying VMM on a production environment, as you can then compare both logs.
Run the following command on the Hyper-V host:
winrm id
This should produce an output similar to the following one:
IdentifyResponse ProtocolVersion = http://schemas.dmtf.org/wbem/wsman/1/wsman.xsd ProductVendor = Microsoft Corporation ProductVersion = OS: 6.1.7201 SP: 0.0 Stack: 2.0
If the result shows an error, run the following command for a quick configuration of WinRM:
winrm qc
If prompted, answer Yes. You will receive a response similar to the following one:
WinRM already is set up to receive requests on this machine. WinRM is not set up to allow remote access to this machine for management. The following changes must be made: Enable the WinRM firewall exception Make these changes [y/n]? WinRM has been updated for remote management. WinRM firewall exception enabled. WinRM can now be tested again by typing 'winrm id' as before
Now, check the listener with the following command:
winrm enum winrm/config/listener
Run the following command on the VMM management server:
winrm id –r:http://HyperVHost.yourdomain.local:5985 –u:YOURDOMAIN\AdminUser
The result will be similar to the following one:
IdentifyResponse ProtocolVersion = http://schemas.dmtf.org/wbem/wsman/1/wsman.xsd ProductVendor = Microsoft Corporation ProductVersion = OS: 6.1.7201 SP: 0.0 Stack: 2.0
Otherwise, you will receive the following error:
Error number: -2144108526 0x80338012 The Client cannot connect to the destination specified in the request
This could indicate communication issues, so check your network, host firewall, and connectivity.
Most WinRM-related events appear in the system or application event logs. The Service Control Manager often contains the error, as the WinRM service has terminated or restarted for some reason.
During the VMM installation, you will get the following error:

To avoid this scenario, conduct the following checks:
Make sure that you have installed all of the prerequisites
Check the firewall rules and make sure the ports are configured correctly
Open the command prompt (Run as Administrator) and type the following commands:
winrm qc -q winrm set winrm/config/service/auth @{CredSSP="True"} winrm set winrm/config/winrs @{AllowRemoteShellAccess="True"} winrm set winrm/config/winrs @{MaxMemoryPerShellMB="2048"}
You can check whether the WinRM can communicate with OS WMI providers by running the following command:
winrm enum wmi/root/cimv2/Win32_ComputerSystem -r:http://servername:5985 [–u:YOURDOMAIN\AdminUser]
By running the following command, you can check whether the WinRM can communicate with Hyper-V WMI providers:
winrm enum wmi/root/virtualization/msvm_computersystem -r:http://servername:5985 [–u:YOURDOMAIN\AdminUser]
Also, to check whether WinRM can communicate with the VMM agent WMI provider, run the following command:
winrm invoke GetVersion wmi/root/scvmm/AgentManagement -r:servername [–u:YOURDOMAIN\AdminUser] @{}
The following are the troubleshooting tools available for use:
Windows Management Instrumentation Tester (
wbemtest.exe): Thewbemtest.exetool gives you the ability to query WMI namespaces on local or remote servers.Connecting to a namespace locally indicates that it is properly registered and is accessible via the WMI service. By connecting to a remote server additionally, it also indicates that the WMI connectivity between the two machines is working.
For more information about wbemtest, refer to the link at http://technet.microsoft.com/en-us/library/cc785775.aspx.
WMI Service Control Utility: This tool configures and controls the WMI service, allowing namespace permissions to be modified.
To open this tool, type in the following command in the command prompt:
winmgmt.mscThen, perform the following steps:
Right-click on WMI Control (Local).
Select Properties.
Click on the Security tab, and then select Root.
Click on the Security button to check the permissions.
Background Intelligent Transfer Service (BITS) transfers files between machines, providing information about the operation's progress. The transfer can be asynchronous.
In VMM, BITS is used for encrypted data transfer between managed computers. Encryption is done by using a self-signed certificate that is generated when the Hyper-V host is added to VMM.
You can use BITSadmin to verify that BITS is working properly outside of VMM. BITSadmin can be downloaded at http://msdn.microsoft.com/en-us/library/aa362813(VS.85).aspx.
You can also find some examples of BITSadmin at http://msdn.microsoft.com/en-us/library/aa362812(VS.85).aspx.
The following tools are used to collect data surrounding VMM issues:
VMM tracing tools: VMM tracing tools provide the ability to manage, collect, and view various traces and diagnostic information in a VMM environment.
When you face an issue and need to report it to Microsoft, you can gather the trace by performing the following steps:
In the VMM server, open the command prompt with administrative rights and type in the following command:
logman create trace VMMDebug -v mmddhhmm -o %SystemDrive%\VMMlogs\DebugTrace_%computername%.ETL -cnf 01:00:00 -p Microsoft-VirtualMachineManager-Debug
Start the trace collection by executing the following command:
logman start VMMDebugNext, try to reproduce the issue, and at the end, stop the trace collection by executing the following command:
logman stop VMMDebugSend the ETL file located in
%SystemDrive%\VMMlogs\DebugTrace_%computerna;me%.ETLto Microsoft.Delete the debug information by executing the following command:
logman delete VMMDebug
The VMM TraceViewer utility: After gathering the trace, you can use TraceViewer on the traces. This tool converts the ETL binary trace logs into CAR files that can be viewed in both the TraceViewer and other trace parsing tools and provides basic trace parsing.
To convert the ETL file, perform the following steps:
In the TraceViewer, drag the trace file into the open pane.
Provide the location to where you want to save the CAR file. Once the file has been saved, TraceViewer will open the converted ETL file for analysis.
You can download the tool from http://blogs.technet.com/b/jonjor/archive/2011/01/07/vmmtrace-simplified-scvmm-tracing.aspx.
The Configuring ports and protocols on the host firewall for each VMM component recipe in Chapter 3, Installing VMM 2012 R2