Chapter 1: Introduction to Azure Security
Security is a core component of any well-architected environment, and this is no different for Azure. Every workload that your organization implements in Azure needs to be implemented with security in mind. The risk associated with not doing this could range from an attacker being able to use your Azure resources to mine cryptocurrency at your expense to an attacker being able to gain access to sensitive customer data that could result in massive fines or sanctions against your company. It could also lead to reputation damage that may lead to customers moving to a competitor.
But how does cloud security work? Is it different from traditional security? Do you have to unlearn everything that you know about managing on-premises security and start from the beginning? You'll be glad that the answer to that latter question is "No." The principles of digital security are the same whether your workload sits in a traditional on-premises data center or in a cloud environment such as Microsoft Azure. The way you apply those principles, however, is quite different. Some of those differences are due to the dynamic and elastic nature of cloud environments. The ability to rapidly provision and release resources introduces new challenges that traditional security models struggle to address effectively, but we'll be covering how to solve this in this book – that is, we'll focus on how we apply security principles to secure dynamic Azure environments.
In any discussion on Azure security, it is critical to understand the "shared responsibility model," that is, which security tasks are handled by the cloud provider (Microsoft in this case) and which tasks are handled by the cloud consumers (us). In this chapter, I will introduce this concept and show how cloud security responsibilities vary depending on the type of service that you are using in Azure – Software as a Service (SaaS), Platform as a Service (PaaS), or Infrastructure as a Service (IaaS). I will also walk you through how to set up an Azure subscription that you can use to follow along with the hands-on sections of this book.
In this chapter, we're going to cover the following topics; however, feel free to skip to the next chapter if the information covered is already familiar to you:
- Shared responsibility model
- Setting up a practice environment
Technical requirements
To follow along with the instructions in this chapter, you'll need the following:
- An outlook.com account that you will use to sign up for your Azure subscription. Make sure that this is an account that you have not previously used to sign up for a free trial Azure subscription. This is because every Microsoft account is entitled to only one free trial signup. You can sign up for a new outlook.com account by going to https://outlook.live.com/owa/ and clicking Create free account.
- A PC with a web browser: The PC can run Windows, macOS, or GUI-based Linux, as long as it has a web browser installed and it has internet connectivity.
- A credit card: This will be needed during the sign-up process to validate your identity. The credit card will not be charged during the trial. You have to explicitly convert a free trial subscription to a pay-as-you-go subscription for it to be charged.
- A valid phone number: This will also be needed to validate your identity.
Shared responsibility model
As organizations transition their workloads from their on-premises data centers to the Azure cloud platform, the responsibility of security also shifts. One of these shifts is that you are no longer solely responsible (as an organization) for all aspects of security as you may be used to in a traditional environment. Security is now a concern that both the cloud provider (Microsoft) and the cloud customers (us) share. This is called the shared responsibility model and all cloud providers, including Microsoft's competitors such as AWS and GCP, follow this model as well.
The diagram in Figure 1.1 clearly highlights this. It is from a whitepaper on the shared security model that was published by Microsoft. You can download the whitepaper from this URL: https://azure.microsoft.com/en-gb/resources/shared-responsibility-for-cloud-computing/. In the diagram, the gray represents the security responsibilities that are transferred to Microsoft when we adopt Azure, while the blue represents security responsibilities that we still have to take care of as Azure customers:

Figure 1.1 – Shared responsibilities for different cloud service models
One of the things that I would like to highlight in the diagram is that regardless of the cloud service model that we are using in Azure – IaaS, PaaS, or SaaS – we are never without security responsibility. Here are some other lessons that I want you to take from this section:
- Your security responsibility varies depending on the model of service that you are using in Azure.
If you are using an IaaS service such as a virtual machine, you have more security responsibilities to take care of. For example, you are responsible for patching the operating system of your Azure-hosted virtual machines.
If you are using a PaaS service such as Azure App Service, you have fewer security responsibilities to take care of. For example, you are not responsible for patching the operating system used by the service, but you are still responsible for how you configure the service and also for controlling access to it.
If you are using a SaaS service such as Azure Search, you have even fewer security responsibilities, but you are still responsible for controlling access to your data.
- Not fulfilling your security responsibilities leaves you exposed to threats and attacks in those areas.
Have a good look at the diagram again. Wherever you see blue in the diagram, if you do not have a strategy to address those responsibilities, you are leaving yourself exposed to threats! Don't worry too much about this right now – by the end of this book, you'll be equipped with the knowledge and skills that you need to effectively take care of these security responsibilities.
In this section, we established the foundational concept of shared security responsibilities in Azure. This clarified for us what we are responsible for depending on the service model that we are using. In the next section, we will set up a test environment that we can use to practice the implementation of security controls in Azure.
Setting up a practice environment
One of the best ways to learn a new concept is through hands-on practice. This book includes walk-throughs that allow you to gain a practical experience of the concepts being discussed:
Figure 1.2 – Practice environment
To follow along with these walk-throughs, you will need access to an Azure subscription, and I will be walking you through how to sign up for one if you do not have an existing subscription now. If you have an existing subscription that you can use, feel free to skip the next section.
Create a free trial Azure subscription
To set up a free trial subscription, follow these steps:
- Open a browser window and browse to https://signup.azure.com/.
- In the Sign in window, enter your Outlook.com account and click Next:

Figure 1.3 – Enter your email address
- In the Your profile window that opens, the Country/Region, First name, Last name, and Email address fields should already be completed using information from your email profile. Enter the right values if the auto-completed values are not correct.
- Enter your phone number (without the country code).
- Skip Company VatID. Leave it empty and click Next. Depending on your Country/Region setting, this field may not be displayed, or you may be presented with a different option:

Figure 1.4 – Enter your profile information
- In the Identity verification by phone section, ensure your country code and phone number are correct, then click on Text me:

Figure 1.5 – Enter your phone number for identity verification
- A verification code will be sent to your phone number. Enter the verification code and click Verify code.
- In the Identity verification by card section, fill in Cardholder Name (as it appears on your credit card), Card number, Expires, and CVV:

Figure 1.6 – Enter your credit card information
- Enter your address information and click Next.
- In the Agreement section, select only I agree to the subscription agreement, offer details, and privacy statement and click on Sign up:

Figure 1.7 – Conclude the sign-up process
Important note
Clicking on subscription agreement, offer details, and privacy statement will take you to the respective documentation, where you can read the details to stay informed of what you are agreeing to when signing up.
The signup process will begin. It should only take a few minutes, after which you will be redirected to the Azure portal.
- To verify your subscription, in the Azure portal, click on Microsoft Azure in the top-left corner and click on Subscriptions under Navigate:

Figure 1.8 – Verify your new subscription
- In the Subscriptions window, you should see a subscription named Free Trial:
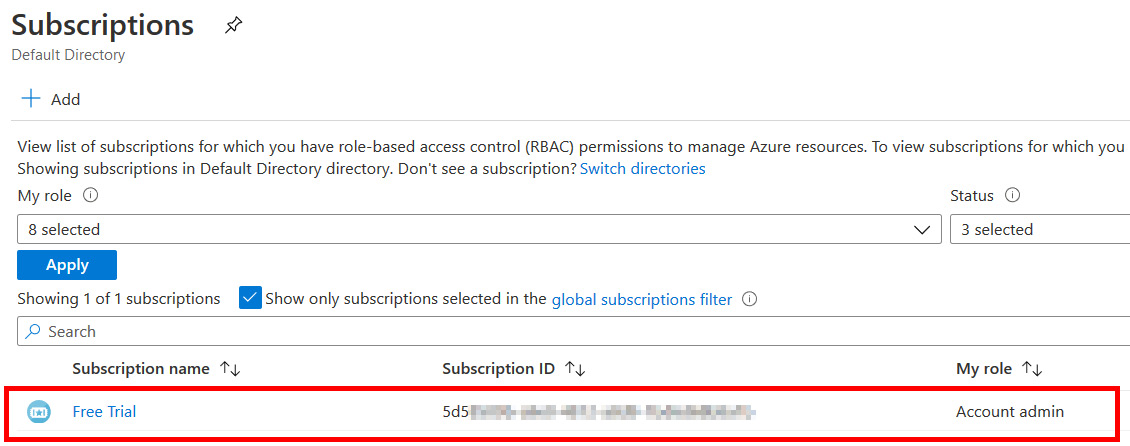
Figure 1.9 – Your new trial subscription
Congratulations! You now have an Azure subscription that you can use to follow along with the rest of the book.
Summary
In this chapter, we saw how cloud security is similar to yet different from traditional security. We also discussed the shared security model concept and highlighted how we have fewer security responsibilities when we adopt a cloud platform such as Microsoft Azure, but we are never without security responsibilities! And finally, I walked you through the process of setting up an Azure subscription, which puts you in a great place to follow along with the hands-on sections in the rest of this book.
Azure security is a deep and complex topic and we're only just getting started. In the next chapter, we'll start discussing one of the most important aspects of implementing security for your Azure environments – securing identity and access using Azure Active Directory.
Questions
As we conclude, here is a list of questions for you to test your knowledge regarding this chapter's material. You will find the answers in the Assessments section of the Appendix:
- True or false: When a workload is migrated from on-premises to Azure, you offload all security responsibilities to Microsoft.
a. True
b. False
- Which cloud service model requires the greatest security effort on the part of the customer?
a. Infrastructure as a Service (IaaS)
b. Platform as a Service (PaaS)
c. Software as a Service (SaaS)
- True or false: The principles of digital security are the same whether your workload sits in a traditional on-premises data center or in a cloud environment such as Microsoft Azure.
a. True
b. False
- Which security responsibility is solely that of the cloud provider when we move to Azure?
a. Network controls
b. Client and endpoint protection
c. Physical security
d. Identity and access management
Further reading
To learn more on the topics covered in this chapter, you can refer to the following links:
- Azure shared security responsibility documentation: https://docs.microsoft.com/en-us/azure/security/fundamentals/shared-responsibility




















 Download code from GitHub
Download code from GitHub