Chapter 1: Approaching a Penetration Test Using Metasploit
Penetration testing is an intentional attack on a computer-based system where the intention is to find vulnerabilities, security weaknesses, and certify whether a system is secure. A penetration test allows an organization to understand their security posture in terms of whether it is vulnerable to an attack, whether the implemented security is enough to oppose any invasion, which security controls can be bypassed, and much more. Hence, a penetration test focuses on improving the security posture of an organization.
Achieving success in a penetration test largely depends on using the right set of tools and techniques. A penetration tester must choose the right set of tools and methodologies to complete a test. While talking about the best tools for penetration testing, the first one that comes to mind is Metasploit. It is considered one of the most effective auditing tools to carry out penetration testing today. Metasploit...
Technical requirements
In this chapter, we made use of the following software and operating systems (OSes):
- VMWare Workstation 12 Player for virtualization (any version can be used)/Oracle Virtual Box (throughout this book, we will use VMWare Workstation Player).
- Ubuntu 18.03 LTS Desktop as a pentester's workstation VM with an IP of
192.168.188.128. You can download Ubuntu from https://ubuntu.com/download/desktop. - Windows 7 Ultimate 64-bit, version: 6.1.7601 Service Pack 1 Build 7601 as a target with IPs of
192.168.188.129and192.168.248.153(any 64-bit Windows 7 release version prior to 2017). - Microsoft Windows Server 2008 R2 Enterprise 64-Bit, Version: 6.1.7601 Service Pack 1 Build 7601 as the domain controller with an IP of
192.168.248.10(any Windows Server 2008/2012). - Metasploit 5.0.43 (https://www.metasploit.com/download).
Organizing a penetration test
When we think about conducting a penetration test on an organization, we need to make sure that everything works according to the penetration test standards. Therefore, if you feel you are new to penetration testing standards or uncomfortable with the term Penetration Testing Execution Standard (PTES), please refer to http://www.pentest-standard.org/index.php/PTES_Technical_Guidelines to become more familiar with penetration testing and vulnerability assessments.
In line with to PTES, the following diagram explains the various phases of a penetration test:
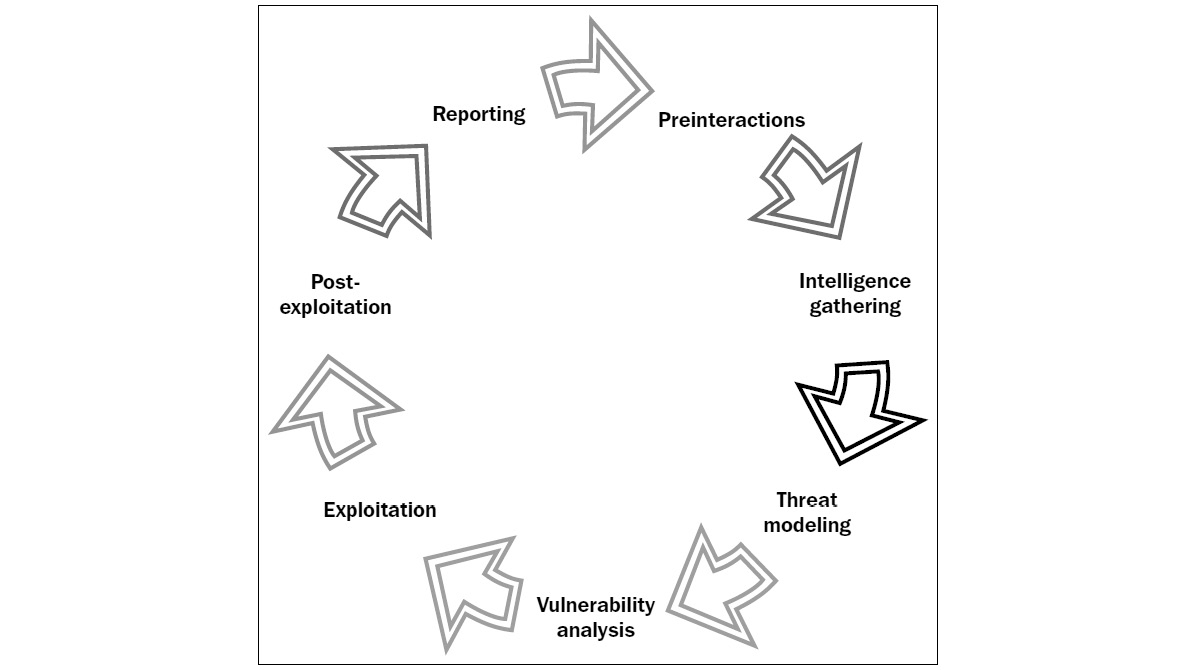
Figure 1.2 – Phases of a penetration test
Important Note
Refer to http://www.pentest-standard.org/index.php/Main to set up the hardware and systematic stages to be followed when setting up a work environment.
Before we start firing sophisticated and complex attacks with Metasploit, let's understand the various phases of a penetration test and learn...
Mounting the environment
A successful penetration test largely depends on how well your work environment and labs are configured. Moreover, a successful test answers the following set of questions:
- How well is your test lab configured?
- Are all the necessary tools for testing available? How good is your hardware to support such tools?
Before we start testing anything, we must make sure that all of the required sets of tools are available and updated.
Let's go ahead and set up Metasploit in a virtual environment.
Setting up Metasploit in a virtual environment
Before using Metasploit, we need to have a test lab. The best idea for setting up a test lab is to gather different machines and install different OSes on them. However, if we only have a single device, the best idea is to set up a virtual environment.
Virtualization plays an essential role in penetration testing today. Due to the high cost of hardware, virtualization plays a cost-effective role in...
The fundamentals of Metasploit
Now that we have recalled the essential phases of a penetration test and installed Metasploit, let's talk about the big picture; that is, Metasploit. Metasploit is a security project that provides exploits and tons of reconnaissance features to aid any penetration tester. Metasploit was created by H.D. Moore back in 2003, and since then, its rapid development has led it to be recognized as one of the most popular penetration testing tools available. Metasploit was a natively Ruby-driven project, but with its latest releases, it has started to support Python and Go modules as well. Metasploit offers various exploits, post exploits, and auxiliary, scanner, evasion, and exploit development tools.
With the release of Metasploit 5, a number of new capabilities have been added to Metasploit, some of which are as follows:
- A choice between a database and the new HTTP-based data service
- Evasion modules
- The Automation API
- Exploitation...
Conducting a penetration test with Metasploit
Now that we've set up Metasploit 5, we are ready to perform our first penetration test. However, before we start the test, let's recall some of the essential functions and terminologies used in Metasploit Framework.
Recalling the basics of Metasploit
After we run Metasploit, we can list all the useful commands available by typing help or ? in the Metasploit console. Let's recall the basic terms used in Metasploit, which are as follows:
- Exploits: This is a piece of code that, when executed, will exploit the vulnerability of the target.
- Payload: This is a piece of code that runs on the target after successful exploitation. It defines the actions we want to perform on the target system.
- Auxiliary: These are modules that provide additional functionalities such as scanning, fuzzing, sniffing, and much more.
- Encoders: Encoders are used to obfuscate modules to avoid detection by a protection mechanism such...
Benefits of penetration testing using Metasploit
Before we jump into an example penetration test, we must know why we should prefer Metasploit to manual exploitation techniques. Is this because of a hacker-like Terminal that gives us a pro look, or is there a different reason? Metasploit is the preferable choice compared to traditional manual techniques because of specific factors. We will discuss these in this section.
Open source
One of the top reasons why we should go with Metasploit Framework is because it is open source and actively developed. Various other expensive tools exist for carrying out penetration testing. However, Metasploit allows its users to access its source code and add their own custom modules. The Pro version of Metasploit is chargeable, but for the sake of learning, the Framework edition is mostly preferred.
Support for testing large networks and natural naming conventions
Using Metasploit is easy. However, here, ease of use refers to natural naming...
Case study – reaching the domain controller
Recalling the basics of Metasploit, we are all set to perform our first penetration test with Metasploit. Let's consider an on-site scenario where we are asked to test an IP address and check if it's vulnerable to an attack. The sole purpose of this test is to ensure all the proper checks are in place. This scenario is quite straightforward. We will presume that all the pre-interactions have been carried out with the client and that the actual testing phase is going to start.
Please refer to the Revisiting the case study section if you want to perform the hands-on exercise while reading the case study, as this will help you emulate the entire case study with exact configuration and network details.
Gathering intelligence
As we discussed earlier, the gathering intelligence phase revolves around collecting as much information as possible about the target. This includes performing active and passive scans, which include...
Revisiting the case study
We were given an IP address of 192.168.188.129 in order to test against known vulnerabilities. We followed a systematic approach, as follows:
- We created a new workspace using the
workspace –acommand for our test. - We switched to the workspace using the
workspace[workspace-name]command. - We initialized a no ping Nmap scan against the target and found numerous open ports.
- The Nmap scan suggested that, on port
445, an SMB service could be running on Windows 7-Windows 10. - We initiated another Nmap scan, but this time, it was meant for only port
445. We did this using thesmb-os-discoveryscript. - We found that the results suggested that the operating system that's running was Windows 7 SP1 Ultimate edition.
- We knew that Windows 7/Windows Server 2008 are highly vulnerable against CVE-2017-0143, that is, the EternalBlue exploit.
- We initiated another Nmap scan, this time to confirm the presence of the vulnerability...
Summary
Throughout this chapter, we introduced the phases involved in penetration testing. We saw how we could set up a virtual environment and install Metasploit. We recalled the basic Metasploit commands and looked at the benefits of using databases in Metasploit. We conducted a penetration test exercise against a target and compromised it. Using the compromised system, we launched an attack against the Domain Controller system and gained access to it.
Having completed this chapter, you now know about the phases of a penetration test; the benefits of using databases in Metasploit; the basics of Metasploit Framework; and using exploit, post-exploits, plugins, and auxiliary modules in Metasploit.
The primary goal of this chapter was to get you familiar with the phases of a penetration test and the basics of Metasploit. This chapter focused entirely on preparing ourselves for the following chapters.
In the next chapter, we will dive deep into the wild world of scripting and...



















 Download code from GitHub
Download code from GitHub






