Goal-Based Penetration Testing
Everything starts with a goal to achieve. Remember, there are only two types of people, those who get hacked and those who hack. Therefore, in this chapter, we will discuss the importance of goal-based penetration testing and also how vulnerability scans (Vscans), penetration tests (pentests), and Red Team Exercises (RTEs) typically fail in the absence of a goal. This chapter also provides an overview of security testing and setting up a verification lab, and focuses on customizing Kali to support some advanced aspects of penetration testing. By the end of this chapter, you will have learned about the following:
- Security testing
- Classical failures of vulnerability scanning, penetration testing, and red teaming exercises
- Updating and organizing Kali
- Using Bash scripts to customize Kali
- Setting up defined targets
- Building a verification lab
Conceptual overview of security testing
Every household, individual, and public or private business in the world has several things to worry about when it comes to cyberspace, such as data loss, malware, and cyber terrorism. Everything starts with the concept of protection. If you ask, "What is security testing?" to 100 different security consultants, it is very likely that you will receive varying responses. In the simplest form, security testing is a process for verifying whether an information asset or system is protected and whether its functionality is maintained as intended.
Classical failures of vulnerability scanning, penetration testing, and red team exercises
In this section, we will focus on the limitations of classical Vscanning, pentesting, and red teaming exercises. Let's now discuss the actual meaning of these three methodologies in simple terms and look at their limitations:
- Vscanning: This is the process of identifying vulnerabilities or security loopholes in a system or network. The limitations with Vscanning are the potential vulnerabilities, including false positives, which can be confusing to the business owner.
- Pentesting: This is the process of safely exploiting vulnerabilities without much impact to the existing network or business. There are a fewer number of false positives, since the testers will try and simulate the exploit faithfully. A key limitation of pentesting is that the exploits it can detect are only those that are currently known and publicly available exploits. Also, most pentests are project-focused tests. In pentesting, we often hear "Yay, got root!", but we never then hear "What's next?" This could be due to various reasons, such as the project limiting the pentester to reporting only the high-risk issues immediately to the client, or the client being interested only in one segment of the network and wanting the pentester to compromise.
- RTEs: This is the process of evaluating the effectiveness of an organization's defenses against cyber threats and improving them; during RTEs, we notice multiple ways of achieving project goals, such as the complete coverage of all activities under a defined project goal. The key limitations with RTEs are that they are limited in terms of time and can only simulate specific predefined scenarios, and they have an assumed rather than a real environment.
Often, all three of these testing methodologies refer to the terms hack or compromise. "We will hack your network and show you where its weaknesses are –," but wait: does the client or business owner understand the terms hack or compromise? How do we measure hack or compromise? What are the criteria? When do we know that a hack or compromise is complete? All these questions point to only one thing: needing to know the primary goal.
The primary goal of pentesting and RTEs is determining the risk, differentiating the risk rating from the scanner, and performing a business risk value assessment of each asset, as well as the brand/image of the organization. It's not about how many threats there are, but how much risk the organization is exposed to. A risk does not really constitute a threat and doesn't necessarily need to be demonstrated. For example, a Cross-Site Scripting (XSS) attack on a brochure website may not have significant impact on the business; however, a client might put in a mitigation plan for the risk using a Web Application Firewall (WAF) to prevent the XSS attacks.
The testing methodology
Methodologies rarely consider why a penetration test is being undertaken or what data is critical to the business and needs to be protected. In the absence of this vital first step, penetration tests lose focus.
Many penetration testers are reluctant to follow a defined methodology, fearing that it will hinder their creativity in exploiting a network. Pentesting fails to reflect the actual activities of a malicious attacker. Frequently, the client wants to see whether you can gain administrative access to a particular system (perhaps they want to see whether you can root the box, for instance). However, the attacker may be focused on copying critical data in a manner that does not require root access or cause a denial of service.
To address the limitations inherent in formal testing methodologies, they must be integrated in a framework that views the network from the perspective of an attacker, the kill chain.
In 2009, Mike Cloppert of Lockheed Martin CERT introduced the concept that is now known as the attacker kill chain. This concept includes the steps taken by an adversary when they attack a network. These attacks do not always proceed in a linear way; some steps may occur in parallel. Multiple attacks may be launched over time against the same target, and stages may overlap.
In this book, we have modified Cloppert's kill chain concept to more accurately reflect how attackers apply these steps when exploiting networks, applications, and data services.
The following diagram shows the typical kill chain of an attacker:
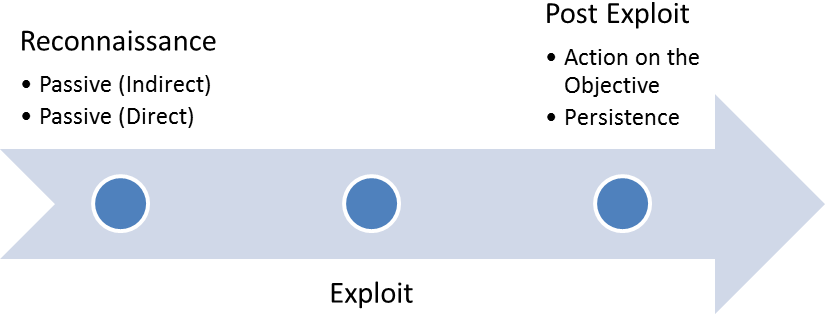
A typical kill chain of an attacker can be described as follows:
- The reconnaissance phase: The adage "reconnaissance time is never wasted time," adopted by most military organizations, acknowledges that it is better to learn as much as possible about an enemy before engaging them. For the same reason, attackers will conduct extensive reconnaissance of a target before attacking. In fact, it is estimated that at least 70 percent of the work of a penetration test or attack is spent conducting reconnaissance! Generally, a penetration tester or attacker will employ two types of reconnaissance:
- Passive reconnaissance: In this, the attacker does not directly interact with the target in a hostile manner. For example, the attacker will review the publicly available website(s), assess online media (especially social media sites), and attempt to determine the attack surface of the target. One particular task will be generating a list of names of past and current employees. These names will form the basis of attempts to brute-force or guess passwords. They will also be used in social engineering attacks. This type of reconnaissance is difficult, if not impossible, to distinguish from the behavior of regular users.
- Active reconnaissance: This can be detected by the target, but not without some difficulty. Activities occurring during active reconnaissance include physical visits to target premises, port scanning, and remote vulnerability scanning.
- The delivery phase: Delivery entails the selection and development of the weapon that will be used to complete the exploit during the attack. The exact weapon chosen will depend on the attacker's intent as well as the route of delivery (for example, across the network, via wireless, or through a web-based service). The impact of the delivery phase will be examined in the second half of this book.
- The exploit or compromise phase: This is the point where a particular exploit is successfully applied, allowing attackers to reach their objective. The compromise may have occurred in a single phase (for example, when a known operating system vulnerability was exploited using a buffer overflow), or it may have been a multiphase compromise. (For example, say an attacker physically accesses premises to steal a corporate phone book. The names could be used to create lists for brute-force attacks against a login portal. In addition, emails could be sent to all employees asking them to click on an embedded link to download a crafted PDF file that compromises their computers.) Multiphase attacks are the norm when a malicious attacker targets a specific enterprise.
- Post-exploit (action on the objective): This is frequently and incorrectly referred to as the exfiltration phase, because there is a focus on perceiving attacks solely as a means to steal sensitive data (such as login information, personal information, and financial information); it is common for an attacker to have a different objective. For example, a business may wish to cause a denial of service in their competitor's network to drive customers to their own website. Therefore, this phase must focus on the many possible actions of an attacker. One of the most common exploit activities is when the attackers attempt to improve their access privileges to the highest possible level (vertical escalation) and to compromise as many accounts as possible (horizontal escalation).
- Post-exploit (persistence): If there is any value in compromising a network or system, then that value can likely be increased if there is persistent access. This allows attackers to maintain communications with a compromised system. From a defender's point of view, this is the part of the kill chain that is usually the easiest to detect.
Kill chains are metamodels of an attacker's behavior when they attempt to compromise a network or a particular data system. As a metamodel, kill chains can incorporate any proprietary or commercial pentesting methodology. Unlike the aforementioned methodologies, however, it ensures a strategic focus on how an attacker approaches the network. This focus on the attacker's activities will guide the layout and content of this book.
Introduction to Kali Linux – history and purpose
Kali Linux (Kali) is the successor to the BackTrack pentesting platform, which is generally regarded as the de facto standard package of tools used to facilitate pentesting to secure data and voice networks. It was developed by Mati Aharoni and Devon Kearns of Offensive Security. The following details on the history of Kali are from BackTrack:
- In March 2013, BackTrack was superseded by Kali, which uses a new platform architecture based on the Debian GNU/Linux operating system.
- Kali 1.1.0 (February 9, 2015): This was the first dot release in two years, in which the kernel was changed to 3.18, had a patch for wireless injection attacks, and had support for wireless drivers – around 58 bugs were fixed. Other releases, such as Kali 1.1.0a, fixed the inconsistencies in the installers.
- Kali 2.0 (August 11, 2015): This was a major release – now a rolling distribution – with major UI changes. Kali 2.0 can be updated from the older version to the new version.
- Kali 2016.1 (January 21, 2016): The first rolling release of Kali. Kernel 4.3 and the latest Gnome 3.18 were updated.
- Kali 2016.2 (August 31, 2016): The second Kali rolling release. Kernel 4.6 and Gnome 3.20.2 were updated, and there were also some bug fixes.
The other features of Kali 2.0 include the following:
- Over 300 pentesting data forensics and defensive tools are included in it. The majority of the tools have now been replaced by similar tools that provide extensive wireless support, with multiple hardware and kernel patches to permit the packet injection required by some wireless attacks.
- Support for multiple desktop environments, such as KDE, GNOME3, Xfce, MATE, e17, lxde, and i3wm, is available.
- Debian-compliant tools are synchronized with Debian repositories at least four times a day, making it easier to update packages and apply security fixes.
- There are Secure Development Environment- and GPG-signed packages and repositories.
- Support for ISO customizations, allowing users to build their own versions of customized Kali, is available. The bootstrap function also performs enterprise-wide network installs that can be automated using preseed files.
- Since increases in ARM-based systems have become more prevalent and less expensive, support for ARMEL and ARMHF in Kali to be installed on devices such as rk3306 mk/ss808, Raspberry Pi, ODROID U2/X2, Samsung Chromebook, EfikaMX, Beaglebone Black, CuBox, and Galaxy Note 10.1 was introduced.
- Kali continues to be an open source project that is free. Most importantly, it is well supported by an active online community.
The purpose of Kali is to secure things and bundle all the tools to provide a single platform for penetration testers.
Installing and updating Kali
In the previous edition of this book, we focused on the installation of Kali to VMware only. We will now take a deep dive into the different technologies involved in installing and updating Kali.
Using Kali from a portable device
Installing Kali to a portable device is fairly simple. In some situations, clients do not permit the use of external laptops inside a secure facility; in such cases, typically, a testing laptop is provided by the client to the pentester to perform scans. Running Kali from a portable device has more advantages during a pentest or RTE:
- Most portable devices can be kept in the pocket, as in the case of a USB drive or a mobile phone
- It can be run live without making any changes to the host operating system
- You can customize the build of Kali and even make the storage persistent
There is a simple three-step process to making a USB into a portable Kali from a Windows PC:
- Download the official Kali Linux image from the following URL:
http://docs.kali.org/introduction/download-official-kali-linux-images. - Download Win32 Disk Imager from https://sourceforge.net/projects/win32diskimager/.
- Open Win32 Disk Imager as an administrator. Plug the USB drive into the PC's available USB port. You will see something similar to the following screenshot; select the correct drive name and then click on Write:
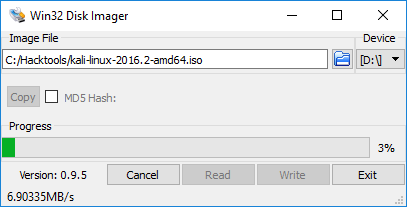
Once complete, exit Win32 Disk Imager and safely remove the USB. Kali is now ready on the portable device and can be plugged into any laptop to be booted up live. If your host operating system is Linux, this can be achieved by two standard commands: sudo fdisk -l , which will display all the disks mounted on the drive, and dd if=kali linux.iso of=/dev/nameofthedrive bs=512k. That's it. The dd command-line utility does the convert and copy if it is used for the input file, where of is for the output file and bs is for the block size.
Installing Kali into a virtual machine
In this section, we will take a deep dive into how to install Kali onto VMware Workstation Player and Oracle VirtualBox.
VMware Workstation Player
Formerly known as VMware Player, VMware Workstation Player is free for personal use, and it is available as a commercial product for business use from VMware as a desktop application that allows us to run a virtual machine inside our host operating system. This application can be downloaded from the following URL:
http://www.vmware.com/products/player/playerpro-evaluation.html
Next, we will see the step-by-step installation of Kali onto VMware Workstation Player.
Once the file is downloaded to your host operating system, you just click on Open the executable and you should be able to see the following:
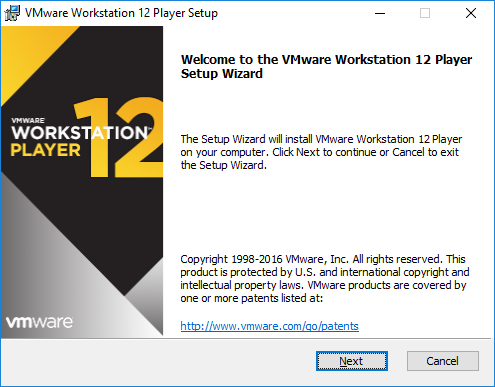
The next step is to Accept the end user license agreement and click on Next until you get the following screen, which depicts the successful installation of VMware on your host operating system:
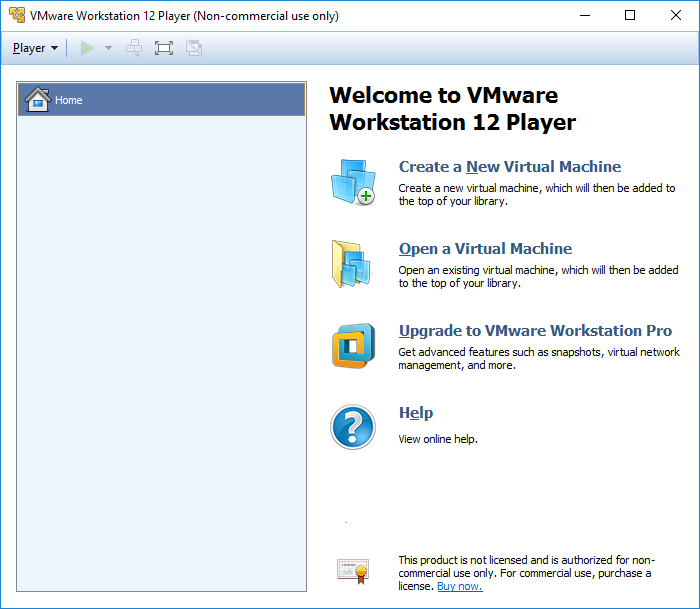
The next step to install Kali to VMware, now that we have downloaded the file from the official Kali downloads, is to click on Create a New Virtual machine and select Installer disc image file (iso). Browse to the ISO file that was downloaded and then click on Next; you can now enter the name of your choice (for example, HackBox) and select the custom location where you would like to store your VMware image. Click on Next and then specify the disk capacity at the minimum for running Kali (recommended is 10 GB) and click on Next until you finish. You should be able to see the following screen once all the settings are complete:
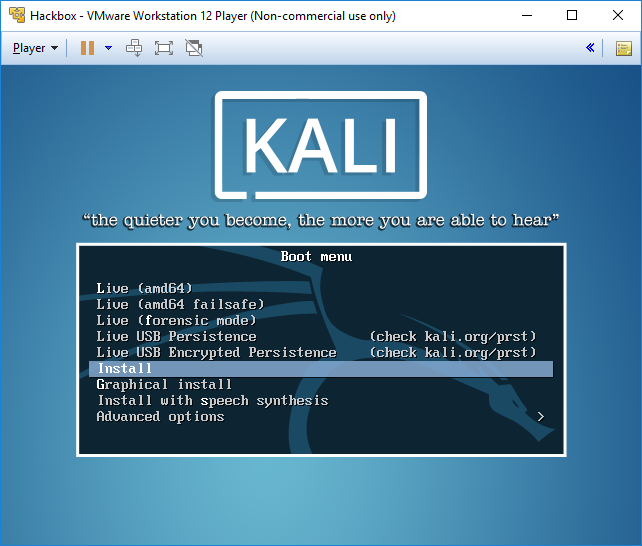
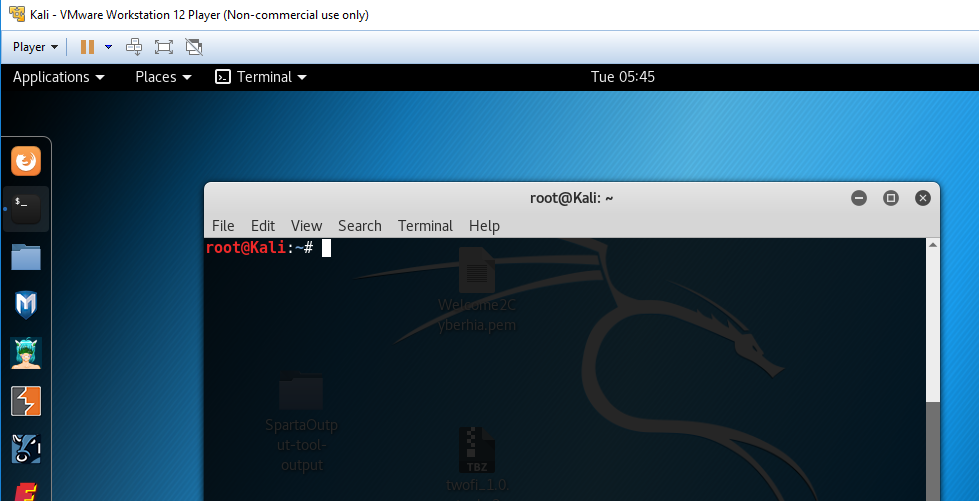
You can choose to install Kali to the host operating system or run it as a live image. Once all the steps of installation are complete, you are ready to launch Kali from VMware without any problem, as shown in the following screenshot:
VirtualBox
VirtualBox is similar to VMware Workstation Player, and is a hypervisor that's an open source and completely free desktop application from which you can run any virtual machine, once it's installed on the host operating system. VirtualBox can be downloaded from this URL:
https://www.virtualbox.org/wiki/Downloads
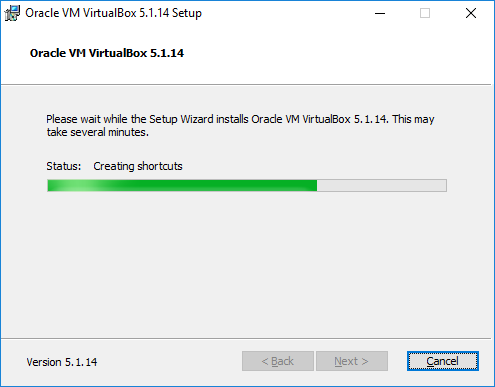
We will now go ahead and install Kali on VirtualBox. Similar to VMware, we will just execute the downloaded executable, which should lead us to the following screen:
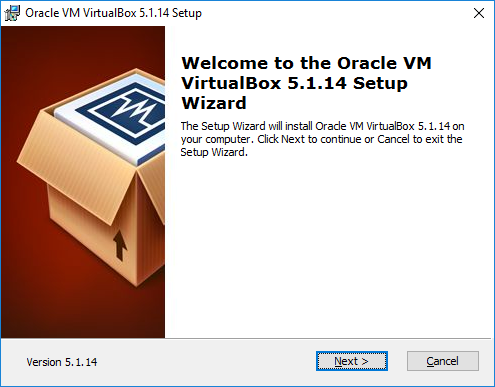
Once we click on Next, the VirtualBox should provide options to customize the different ways to store, but by default, we would be selecting VirtualBox Application:
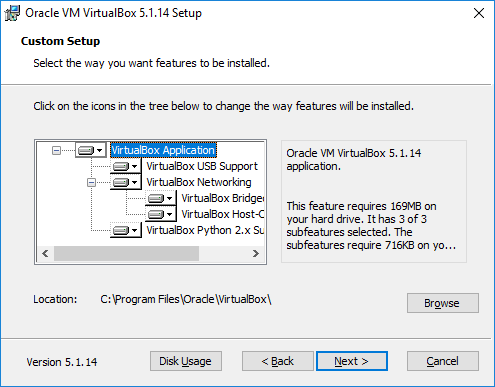
Click on Next; you will be able to see the progress, as shown in the following screenshot:
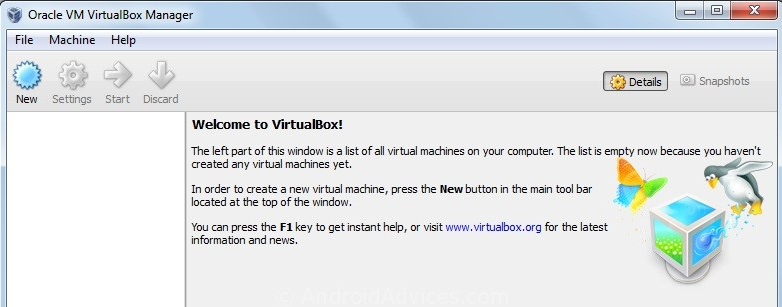
The following screenshot shows the confirmation message you get on the successful installation of Oracle VirtualBox:
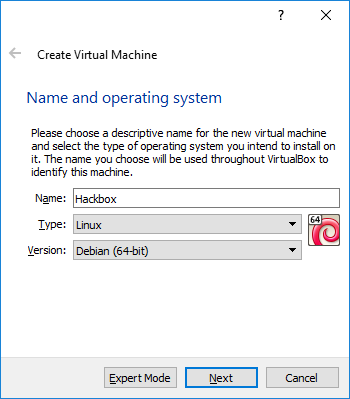
So, the next step is to install Kali onto VirtualBox. Click on New from the menu, which should take us to the following screen, where we can type the name of our choice and select the right version of the platform: for example, 64-bit Debian or 32-bit Debian, as per the ISO image that we downloaded:
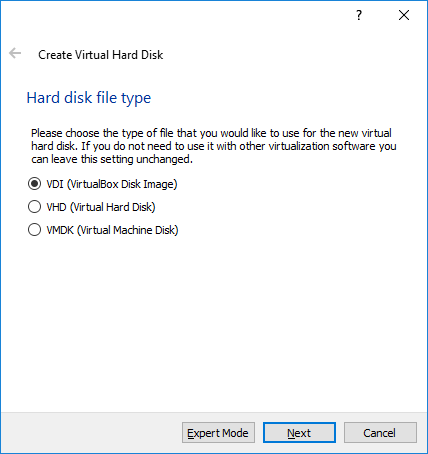
Click on Next and provide the amount of RAM required for Kali. We recommend at least 1 GB. By clicking on Next, we will be creating a virtual hard drive for Kali on the host operating system. Click on Next to choose the hard disk file type: mostly, we select VDI (Virtualbox Disk Image), as shown in the following screenshot:
By clicking on Next, we will be creating the size of the HDD, as shown in the following screenshot:

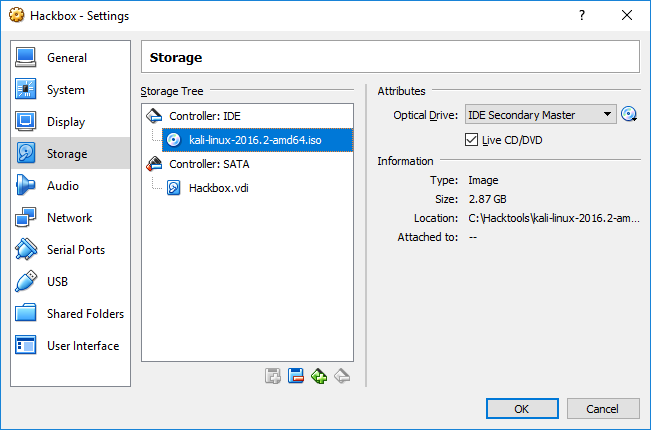
Finally, we have to go to Hackbox | Settings to load the ISO image as an external drive, as shown in the following screenshot:
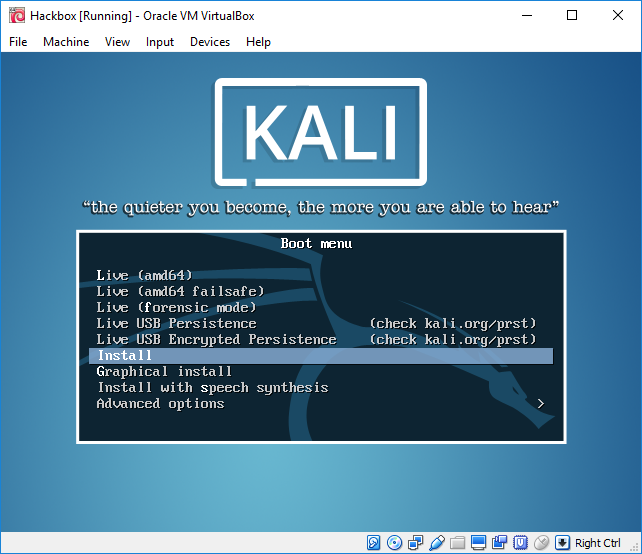
That's it; we should now be able to see the following screen and install Kali to VirtualBox without any issues:
Installing to a Docker appliance
Docker is an open source project that is designed to automate the deployment of software containers and applications instantly. Docker also provides the additional abstraction and automation layers of operating system-level virtualization on Linux.
Docker is available for Windows, macOS, Linux, Amazon Web Services (AWS), and Azure. For Windows, Docker can be downloaded from this URL:
https://download.docker.com/win/stable/InstallDocker.msi
The following steps show how to install Docker on a Windows 10 machine:
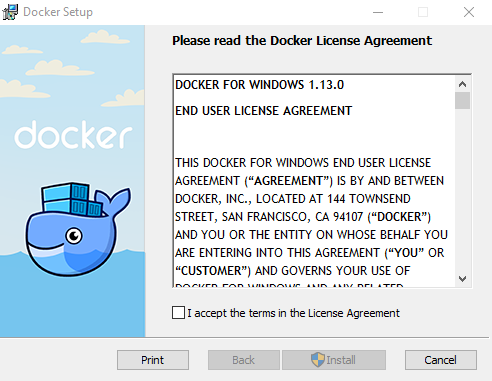
Docker for Windows utilizes the Hyper-V feature on Microsoft Windows. If Hyper-V is not enabled, it is very likely that we will be looking at the following screenshot:
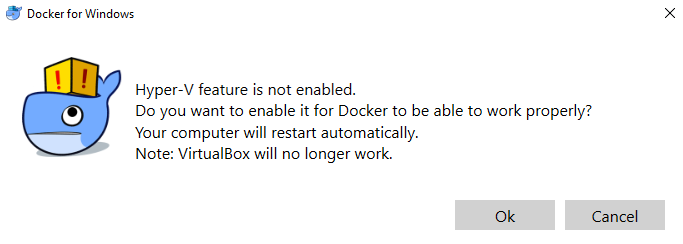
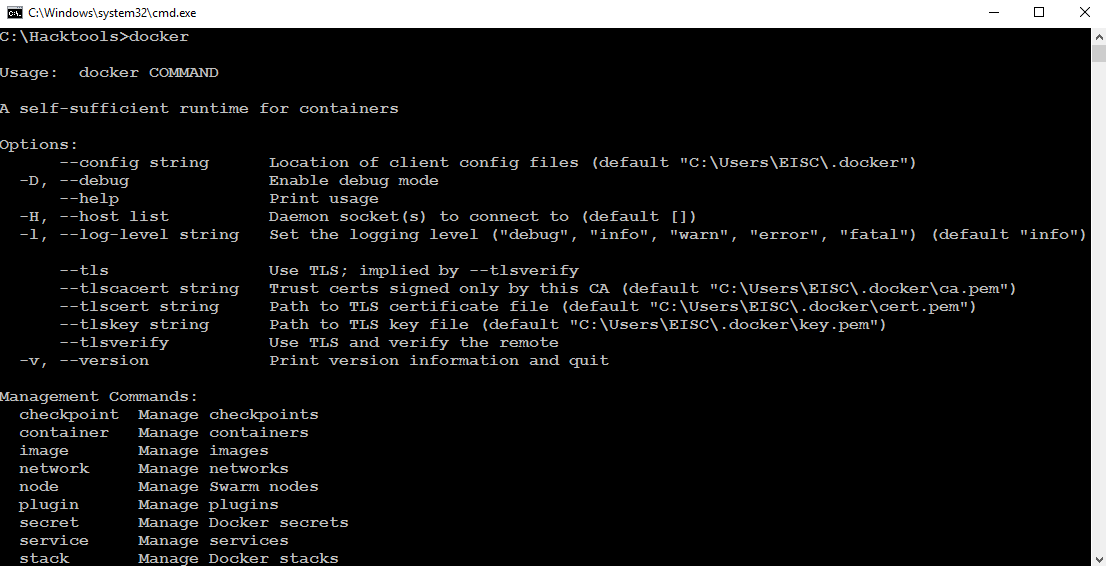
Once you click on Ok, Hyper-V will be enabled by the Docker application; we can check that through our Command Prompt by simply typing docker as a command, as shown in the following screenshot:
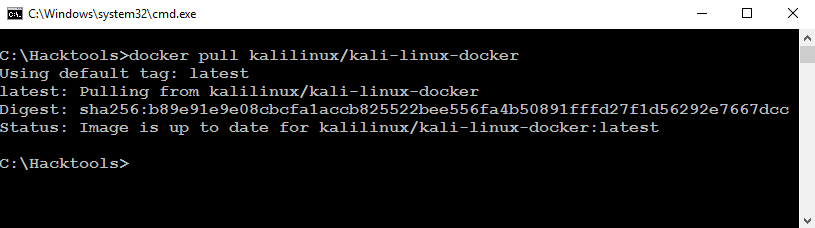
Now, we have installed the Docker appliance to the Windows host operating system. We will now install Kali using the fairly simple docker pull kalilinux/kali-linux-docker commands, as shown in the following screenshot:
Once Kali is downloaded to our Docker application, we should now be able to run Bash from the downloaded Kali Docker appliance instantly, without any hassle, by running run -t -i kalilinux/kal-linux-docker /bin/bash, as shown in the following screenshot:
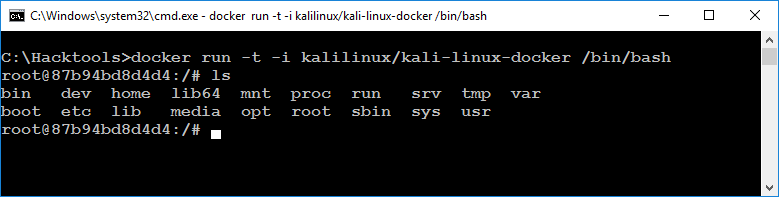
We should be able to run Kali directly from Docker. Also, note that Docker utilizes the VirtualBox environment in the background. So, it is a virtual machine running on VirtualBox through the Docker appliance.
Installing Kali to the cloud – creating an AWS instance
AWS is a cloud-based platform from Amazon, primarily built to offer customers the power of compute, storage, and content delivery anywhere and anytime. As a penetration tester or hacker can utilize AWS to conduct pentesting, in this section, we will go through the easiest ways of installing Kali Linux into AWS, which will be handy in case of external command and control.
First, you will need to have a valid AWS account. You can sign up by visiting the following URL:
https://console.aws.amazon.com/console/home
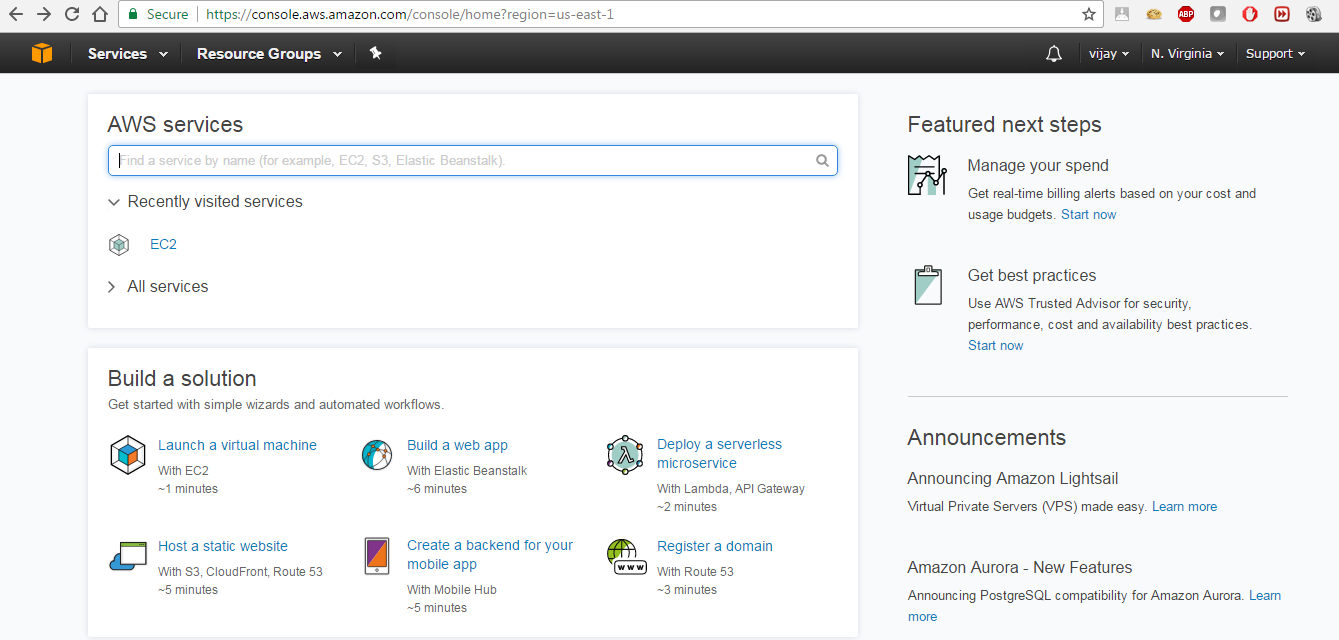
When we log in to the AWS account, we will be able to see all the AWS services, as shown in the following screenshot:
The second step is to launch Kali on AWS as an instance. We will customize Kali by installing a Debian operating system. The open source community has made it very simple to directly launch with preconfigured Kali 2016.2 in the Amazon Marketplace. The following URL will enable us to directly launch Kali within a few minutes:
https://aws.amazon.com/marketplace/pp/B01M26MMTT
When you visit the link, you will be able to see something similar to the following:

Click on the Accept Software Terms & Launch with 1-Click button and go to your AWS console by visiting https://console.aws.amazon.com/ec2/v2/home?region=us-east-1. You should now be able to launch the instance by clicking on Launch Instance by selecting the Instance ID or the row, as shown in the following screenshot:

We will need to create a key-value pair in order to make sure only you can access Kali . You will now be able to log in to your AWS cloud using the private key that you generated during the key-value pair creation. Then, you should be able to log in by entering the following command from your command shell:
ssh -i privatekey.pem ec2-user@amazon-dns-ip
The following screenshot depicts the successful installation of Kali on AWS:

All the terms and conditions must be met in order to utilize AWS to perform pentesting. Legal terms and conditions must be met before launching any attacks from the cloud host.
Organizing Kali
Installation is just the beginning of the setup; organizing Kali is very important. In this section, we will deep dive into the different ways of organizing HackBox through customization.
Configuring and customizing Kali
Kali is a framework that is used to complete a penetration test. However, the tester should never feel tied to the tools that have been installed by default or by the look and feel of the Kali desktop. By customizing Kali, a tester can increase the security of client data that is being collected, and make it easier to do a penetration test.
Common customizations made to Kali include the following:
- Resetting the root password
- Adding a non-root user
- Speeding up Kali operations
- Sharing folders with Microsoft Windows
- Creating encrypted folders
Resetting the root password
To change a user password, use the following command:
passwd root
You will then be prompted to enter a new password, as shown in the following screenshot:

Adding a non-root user
Many of the applications provided in Kali must run with root-level privileges in order to function. Root-level privileges do possess a certain amount of risk; for example, miskeying a command or using the wrong command can cause applications to fail or even damage the system being tested. In some cases, it is preferable to test with user-level privileges. In fact, some applications force the use of lower-privilege accounts.
To create a non-root user, you can simply use the adduser command from the Terminal and follow the instructions that appear, as shown in the following screenshot:

Speeding up Kali operations
Several tools can be used to optimize and speed up Kali operations:
- When using a virtual machine, install the VM's software drive package: Guest Additions (VirtualBox) or VMware Tools (VMware). We need to ensure that we run apt-get update before the installation.
- When creating a virtual machine, select a fixed disk size instead of the one that is dynamically allocated. It is faster to add files to a fixed disk, and there is less file fragmentation.
- The preload application (apt-get install preload) identifies a user's most commonly used programs and preloads binaries and dependencies into memory to provide faster access. It works automatically after the first restart following installation.
- BleachBit (apt-get install bleachbit) frees disk space and improves privacy by freeing the cache, deleting cookies, clearing internet history, shredding temporary files, deleting logs, and discarding other unnecessary files. The advanced features include shredding files to prevent recovery and wiping free disk space to hide traces of files that have not been fully deleted.
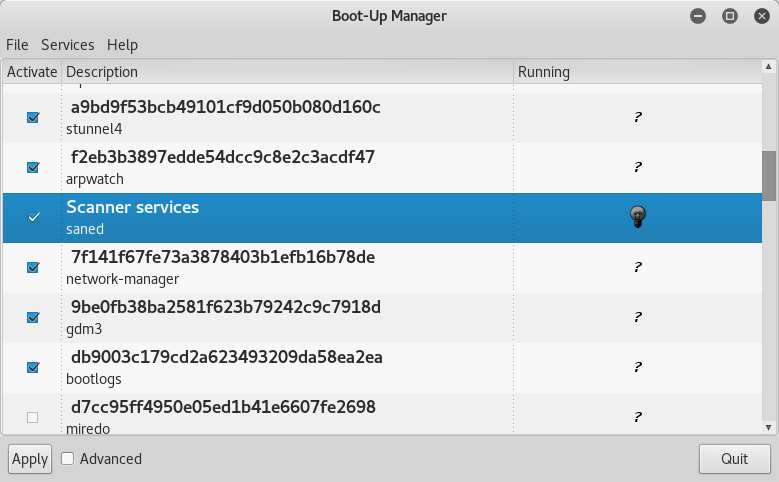
- By default, Kali does not show all applications that are present in the start-up menu. Each application that is installed during the boot-up process slows the system data and may impact memory use and system performance. Install Boot Up Manager (BUM) to disable unnecessary services and applications that are enabled during the boot-up process (apt-get install bum), as shown in the following screenshot:
- Add gnome-do (apt-get install gnome-do) to launch applications directly from the keyboard. To configure gnome-do, select it from Applications | Accessories. Once launched, select the Preferences menu, activate the Quiet Launch function, and select a launch command (for example, Ctrl + Shift). Clear any existing commands and then enter the command line to be executed when the launch keys are selected.
- Rather than launching directly from the keyboard, it is possible to write specific scripts that launch complex operations.
Sharing folders with the host operating system
The Kali toolset has the flexibility to share results with applications residing on different operating systems, especially Microsoft Windows. The most effective way to share data is to create a folder that is accessible from the host operating system as well as the Kali VM guest.
When data is placed in a shared folder from either the host or the VM, it is immediately available via the shared folder to all systems that access that shared folder.
To create a shared folder, perform the following steps:
- Create a folder on the host operating system. In this example, it will be called Kali_Share.
- Right-click on the folder and select the Sharing tab. From this menu, select Share.
- Ensure that the file is shared with Everyone and that the Permission Level for this share is set to Read / Write.
- If you have not already done so, install the appropriate tools onto BackTrack. For example, when using VMWare, install the VMWare tools (refer to Appendix, Installing Kali Linux).
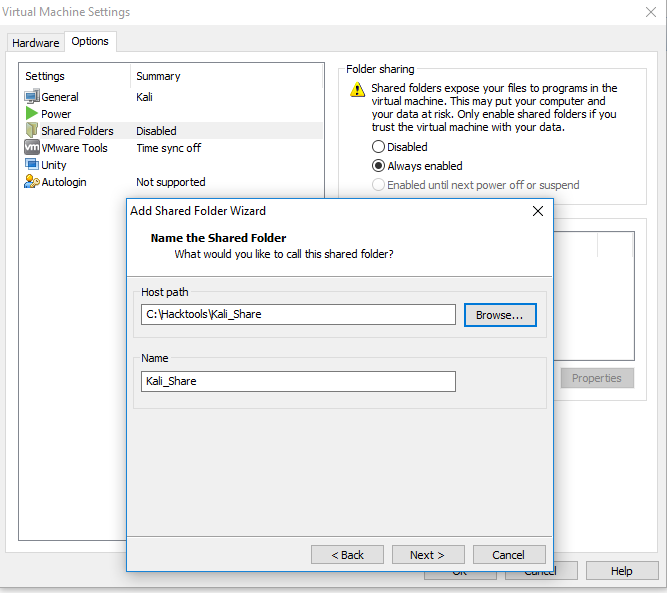
- When the installation is complete, go to the VMWare Player menu, select Manage, click on Virtual Machine Settings, locate the menu that enables Shared Folders, and select Always Enabled. Create a path to the shared folder that is present on the host operating system, as shown in the following screenshot:
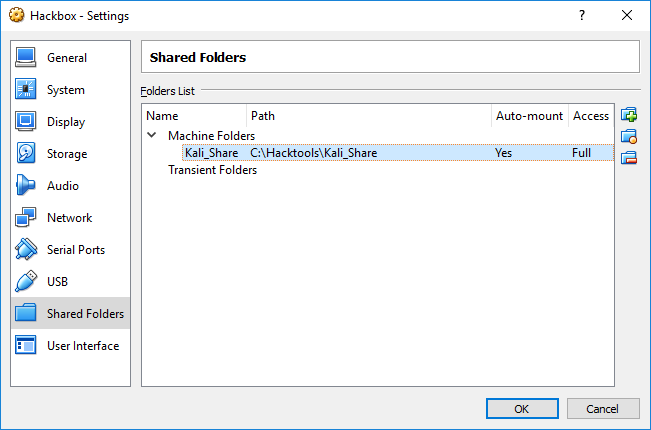
- In the case of Oracle VirtualBox, select the VM and go to Settings and select Shared Folders, as shown in the following screenshot:
- Open the file browser on the Kali desktop. The shared folder will be visible in the mnt folder (it might be placed in a subfolder, hgfs).
- Drag the folder onto the Kali desktop to create a link to the real folder.
- Everything placed in the folder will be accessible in the folder of the same name on the host operating system, and vice versa.
The shared folder, which will contain sensitive data from a penetration test, must be encrypted to protect the client's network and reduce the tester's liability, should the data ever be lost or stolen.
Using Bash scripts to customize Kali
In order to maintain system and software development, command-line interfaces developed multiple shells in Linux; namely, sh, bash, csh, tcsh, and ksh.
We can utilize the following Bash scripts to customize Kali depending upon the goal of our pentesting:
Building a verification lab
As a penetration tester, it is recommended that you set up your own verification lab to test any kind of vulnerabilities and have the right proof of concept before emulating anything in a live environment.
Setting up a virtual network with Active Directory
As we progress in building our own verification lab, it's worth keeping in mind that the majority of corporate companies utilize Microsoft Active Directory for user administrative management and resource sharing activities, such as printer use, file sharing, and identity management. Attackers are no longer interested in just running the command on the server or shutting it down; they are now more focused on owning a full domain controller, which can potentially be the DNA of a company. We will perform some advanced attacks on Active Directory and the DNS server. In this section, we will install Active Directory on a Windows 2008 R2 server.
We will perform the same steps that we performed to install Kali to install Windows 2008 R2 to the same network.
Now we will see step-by-step instructions to install Active Directory Domain Services. Assuming we have already installed the Microsoft Windows 2008 R2 server, click on Server manager, go to Roles, and then click on Add Roles. This should take us to Before you Begin, and clicking on Next will bring up the following dialog box:
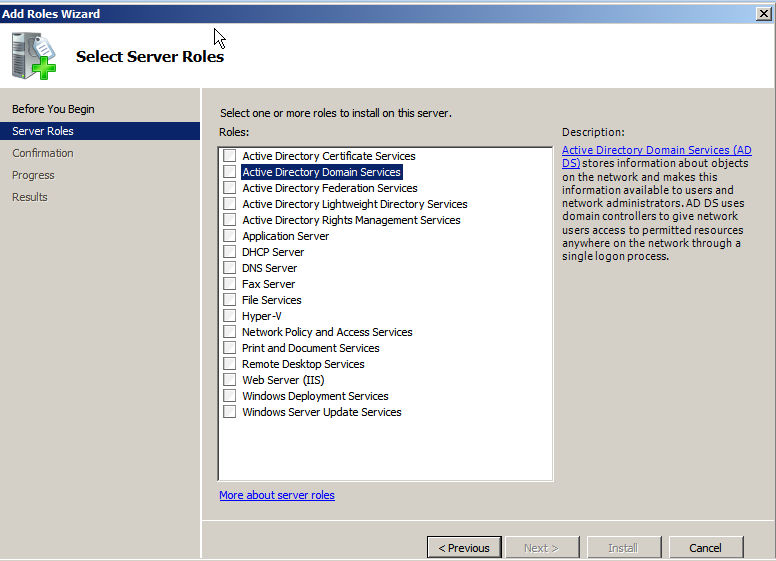
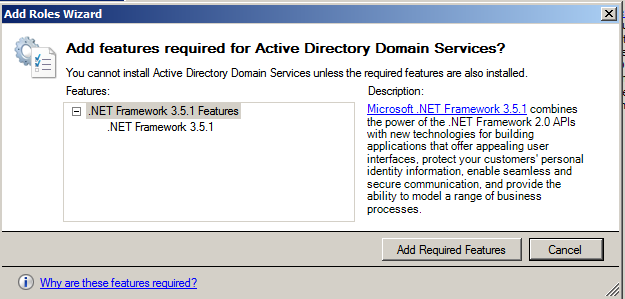
Select Active Directory Domain Services. When we select this, we are likely to get the following alert to install .NET Framework 3.5.1 Features, which is necessary for ensuring that all the API features are enabled. Click on Add Required Features, as shown in the following screenshot:
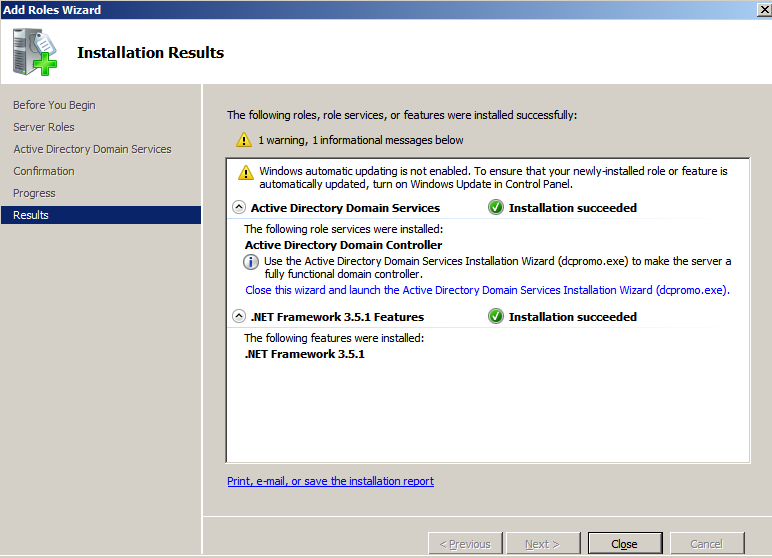
Let's move ahead and click on Install to continue. Both the items will be installed and we will see the successful completion of the installation of Active Directory Domain Services, as shown in the following screenshot:
Once the service is installed, we need to ensure that we run the service by clicking on the Active Directory Domain Services installation wizard and creating a new forest by following the instructions. In our case, we will be creating a new forest with FQDN as Secure.kali.com. Then with the domain NetBIOS name as Secure, set the forest functional level to Windows 2003 or Windows 2008 R2. This will invoke the Domain Name Server (DNS). As a fresh install, we will need to install DNS and follow the wizard. Finally, we must have a new domain as secure.kali.com, as shown in the following screenshot:

Installing defined targets
Practice makes perfect. In order to practice the art of exploitation, it is always recommended that you make use of software that is generally known to be vulnerable. In this section, we will install Metasploitable3, which is a Windows platform, and Multilladae, which is a PHP framework web application.
Metasploitable3
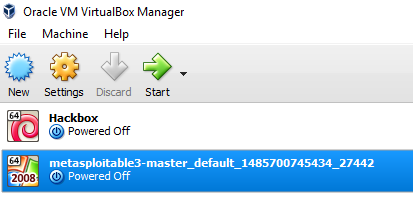
Metasploitable3 is an indubitably vulnerable virtual machine that is intended to be tested for multiple exploits using Metasploit. It is under a BSD-style license. This virtual machine can be downloaded from https://github.com/rapid7/metasploitable3. You can download the ZIP file and unzip it to your favorite Windows location (typically, we segregate this in the c:\HackTools\ folder) or you can use the git clone link with the Bash command.
Install all the relevant supporting software, such as Packer, Vagrant, VirtualBox, and the Vagrant reload plugin.
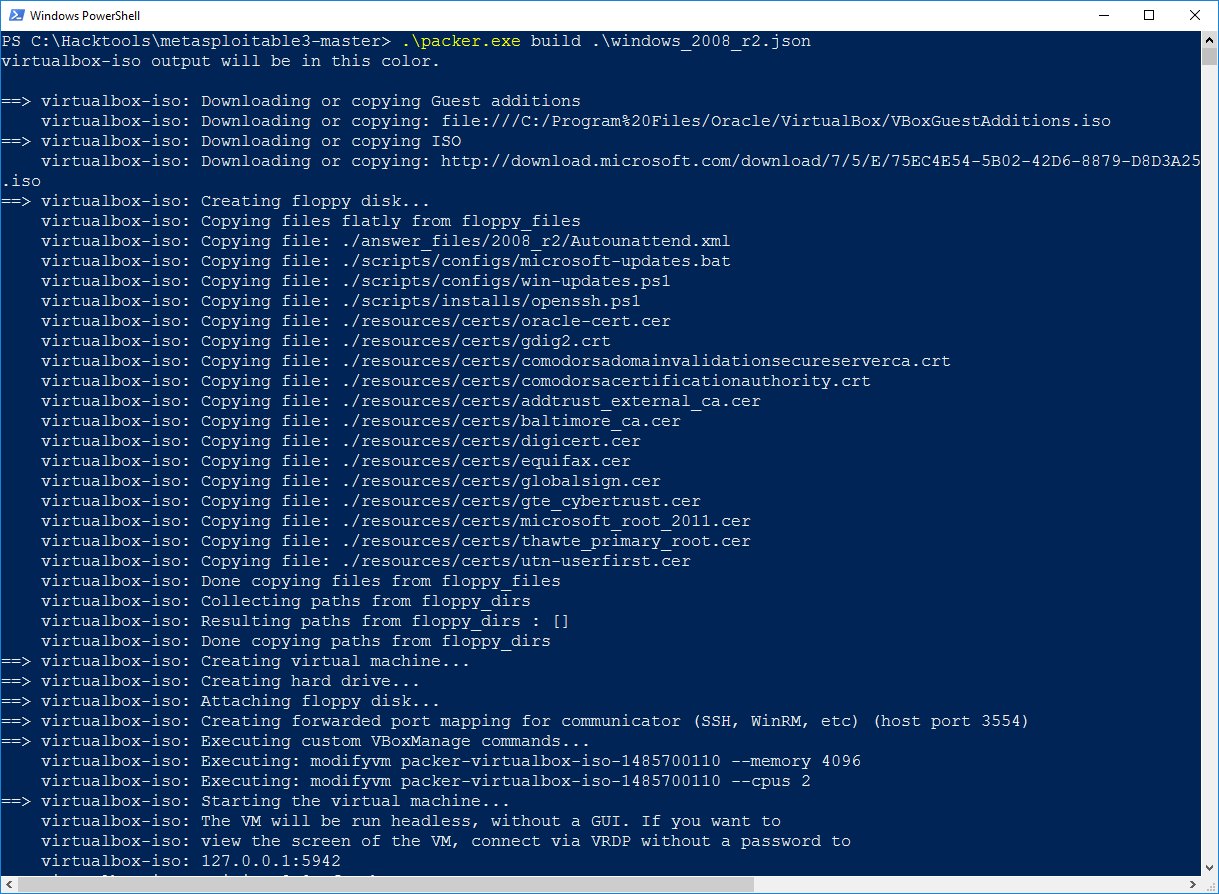
The following is a screenshot of the manual installation of Metasploitable3 on the Windows 10 host operating system:
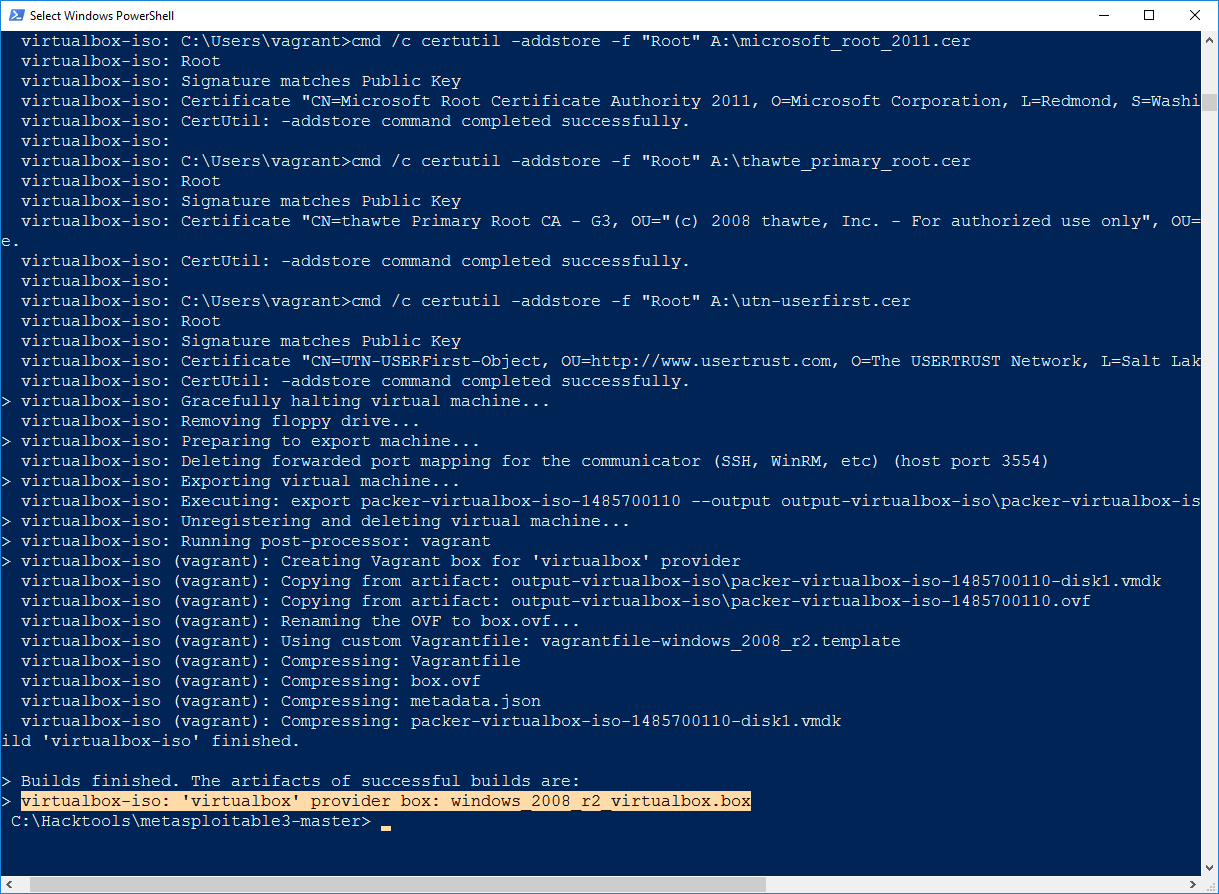
Once the packer build has downloaded the ISO vbox image, you will receive a message as shown in the following screenshot:
After the VirtualBox file is downloaded, you will just have to run vagrant up in the same PowerShell. This should bring up your new VM in your virtual box without any problem, as shown in the following screenshot:
Mutillidae
Mutillidae is an open source insecure web application that is designed for penetration testers to practice web app-specific vulnerability exploitation.
XAMPP is another free and open source cross-platform web server solution stack package, developed by Apache Friends. XAMPP can be downloaded from this URL:
https://www.apachefriends.org/download.html
We will now be installing XAMPP to our newly installed Microsoft Windows 2008 R2 server to host it. Once XAMPP is downloaded, let's go ahead and install the executable by following the wizard. Once the installation is complete, launch XAMPP and you should be able to see the following screen:

Mutillidae can be downloaded from https://sourceforge.net/projects/mutillidae/files/latest/download.
Unzip the file and copy the folder to c:\yourxampplocation\htdocs\<mutillidae>.
We should be able to see the web application installed successfully, as shown in the following screenshot, and it can be accessed by visiting http://localhost/mutillidae/:

Managing collaborative penetration testing using Faraday
One of the most difficult aspects of penetration testing is remembering to test all of the relevant parts of the network or system target, or trying to remember whether the target was actually tested. In some cases, a single client may have multiple penetration testers performing scanning activities from multiple locations and management would like to have a single view. Faraday can provide a single view, assuming all the penetration testers are able to ping each other on the same network, or on the internet for external assessment.
Faraday is a multiuser penetration test Integrated Development Environment (IDE). It is designed for testers to distribute, index, and analyze all the data that is generated during the process of a penetration testing or technical security audit to provide different views such as management, executive summary, and an overall issues list.
This IDE platform is developed in Python by InfoByte. Download the application from https://github.com/infobyte/faraday/wiki or directly git clone the link, as shown in the following screenshot:
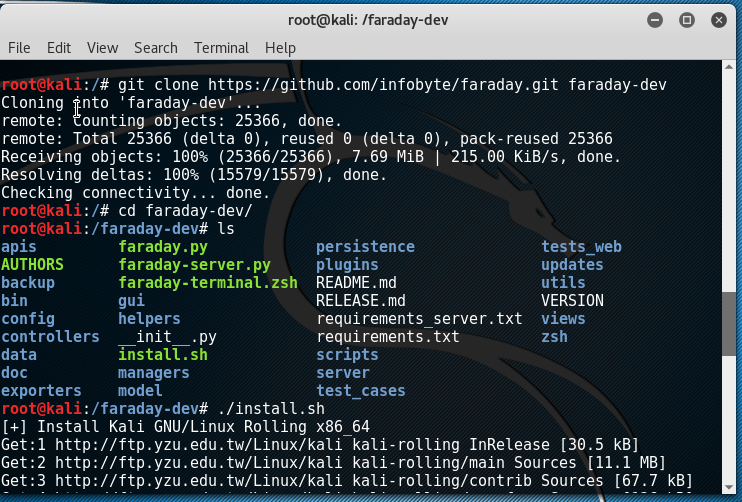
Once the folder is cloned to your Kali, run ./install.sh to install any dependencies. Do not forget to start the CouchDB service, as Faraday utilizes CouchDB as its database for storage. Finally, we run faraday-server.py to launch the Faraday server for an integrated platform, and then as the client, we should be able to launch Faraday by running faraday.py, as shown in the following screenshot:
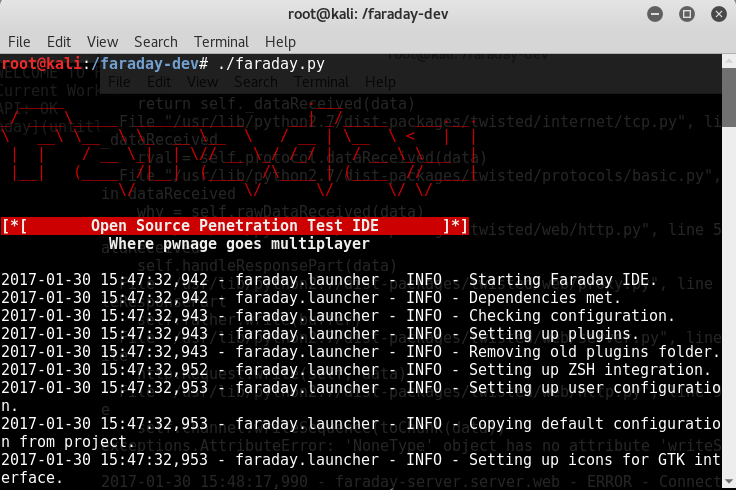
Launching Faraday should open up the Faraday shell console to us, as shown in the following screenshot:
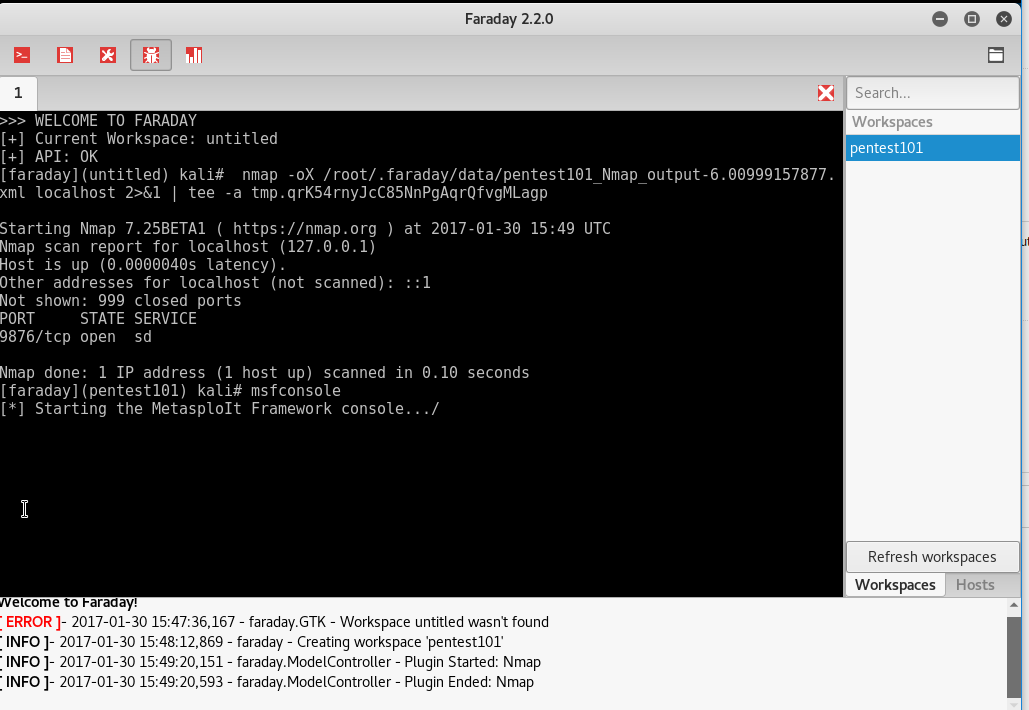
One positive aspect of the application is that you will be able to visualize the information from any scanning that you do, or that any other penetration tester does, by clicking on Faraday web, as shown in the following screenshot:
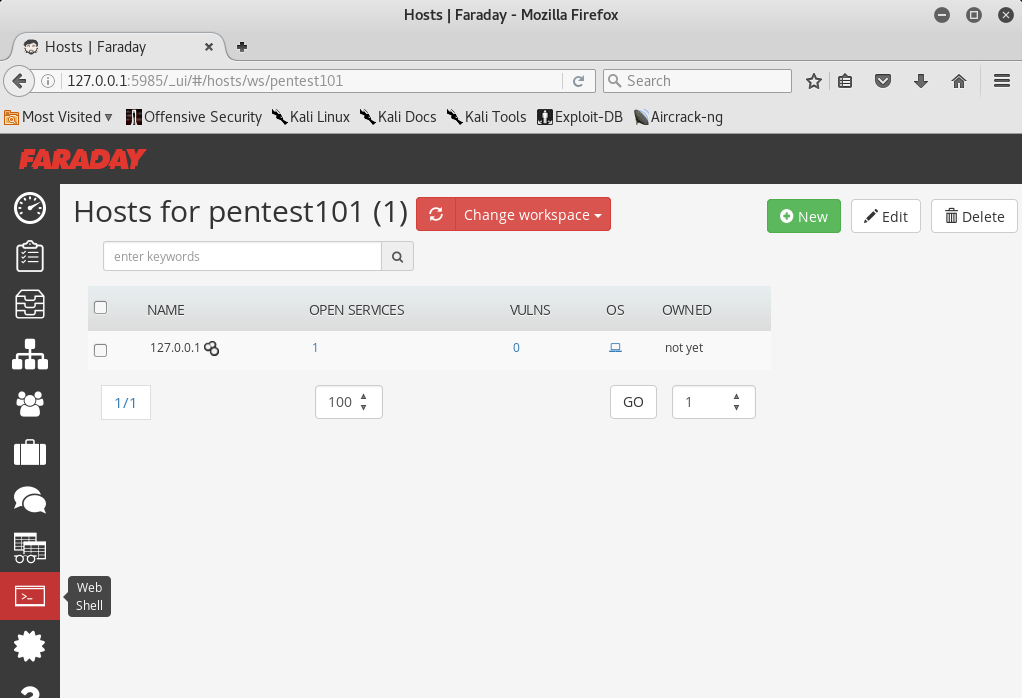
There is a limitation on the free version of Faraday for the community, which can be utilized to visualize all the lists of issues in a single place.
Summary
In this chapter, we had a journey into different goal-based penetration testing methodologies that help organizations to test themselves against real-time attacks. We saw how penetration testers can use Kali in multiple different platforms to assess the security of data systems and networks. We have taken a dive into installing Kali on different virtualized platforms and have looked at how quickly we can run a Linux operating system on the Windows platform using Docker.
We built our own verification lab, set up Active Directory Domain Services, and also set up two different virtual machines on the same network. Most importantly, you learned how to customize Kali to increase the security of our tools and the data that they collect. We are working to achieve the goal of making tools support our process, instead of the other way around!
In the next chapter, you will learn how to effectively master Open Source Intelligence (OSINT) to identify the vulnerable attack surfaces of our target and create customized username-password lists to facilitate more focused attacks and other exploits.



















 Download code from GitHub
Download code from GitHub


