Incident Response – Evolution and Current Challenges
As we learned in the previous chapter, Incident Response (IR) is the approach used to manage security incidents in order to reduce the damage to an organization and improve the recovery of affected services or functionalities. IR activities follow a plan, which is the set of directions that outline the response procedures and the roles of different team members. IR has become a necessity for organizations facing rising threat levels, and this chapter discusses its importance.
With the focus of this chapter being the evolution and then the challenges of IR, we'll begin by looking at how IR has evolved with threats and advancements in technology. We'll then look at the challenges that IR teams face today, especially with the tasks of assessing current levels of security in the organization, anticipating and protecting systems from future threats, being involved in legal processes relating to cyber-attacks, uniting the organization during crises, and integrating all security initiatives. We'll cover the following main topics:
- The evolution of incident response
- Challenges facing incident response
- Why do we need incident response?
We'll begin by exploring some recent history, and how IR has evolved over time.
The evolution of incident response
The general notion regarding the origin of hacking is that it started in the 1960s, around the time of the invention of modern computers and operating systems. To disprove this notion, let's next briefly explore the history of data breaches, to develop an idea of the context behind the modern attack environment.
The history of data breaches
Data interception associated with hacking activities goes as far back as 1836, when two persons were caught intercepting data transmissions in a criminal manner.
During the last decade of the 1700s, France implemented a national data network, which was one of a kind at the time, to transfer data between Paris and Bordeaux. It was built on top of a mechanical telegraph system, which was a network of physical towers. Each tower was equipped with a unique system of movable arms. The tower operators would use different combinations of these arms to form numbers and characters that could be read from a similar distant tower using a telescope. This combination of numbers and characters was relayed from tower to tower until it reached the other city. As a result, the government achieved a much more efficient, speedier mechanism of transferring data.
Interestingly, all this happened in the open. Even though the combinations were encrypted, and would've required an experienced telegraph operator to decode the message at the far end to bring up the original message, the risks were just around the corner. This operation was observed by two bankers, Francois and Joseph Blanc. They used to trade government bonds at the exchange in Bordeaux, and it was they who figured out a method to poison the data transfer and obtain an indicator of current market status, by bribing the telegraph operators. Usually, it took several days before the information related to bond performance reached Bordeaux by mail. Now, they had an advantage to get that same information well before the exchange in Bordeaux received it.
In a normal transmission, the operator included a backspace symbol to indicate to the other operator that they needed to avoid the previous character and consider it a mistake. The bankers paid one of the operators to include a deliberate mistake with a predefined character, to indicate the previous day's exchange performance, so that they could assume the market movement and plan to buy or sell bonds. This additional character did not affect the original message sent by the government, because it was indicated to be ignored by the receiving telegraph operator. But this extra character would be observed by another former telegraph operator who was paid by the bankers to decode it by observing through a telescope.
Using this unique information related to market movement, the Blanc brothers had an advantage over the market for two years, until they were caught in 1836. The modern equivalent of this attack would perhaps be data poisoning, a man-in-the middle attack, misuse of a network, or social engineering. However, the striking similarity is that these attacks often go unnoticed for days or years before they get caught. Unfortunately, the Blanc brothers could not be convicted as there were no laws under which they could be prosecuted at that time. Maybe the Blanc brothers' hack was not so innovative compared to today's cyber-attacks, but it does indicate that data has always been at risk. And, with the digitization of data in all shapes and forms, operations, and transport mechanisms (networks), the attack surface is huge now. It is now the responsibility of the organization and individuals to keep the data, network, and computer infrastructure safe.
Let's fast-forward another 150 years, to 1988. This is when the world witnessed the first-ever computer virus—the Morris worm. Even though the creator of the worm, Robert Tappan Morris, denied the allegation that it was intended to cause harm to computers, it did, indeed, affect millions of them. With the intention of measuring the vastness of the cyber world, Morris wrote an experimental program that was self-replicating and hopped from one computer to another on its own.
It was injected into the internet by Morris, but, to his surprise, this so-called worm spread at a much faster rate than he would have imagined. Within the next 24 hours, at least 10% of internet-connected machines were affected. This was then targeted to the Advanced Research Projects Agency Network (ARPANET), and some reports suggested that the number of connected computers at the time was around 60,000. The worm exploited a flaw in the Unix email program Sendmail, and a bug in the finger daemon (fingerd). Morris' worm infected many sites, including universities, military organizations, and other research facilities. It took a team of programmers from various US universities working non-stop for hours to reach a solution. It took a few more days still to get back to a normal state. A few years later, in 1990, Morris was convicted by the court for violating the Computer Fraud and Abuse Act; unlike at the time of the Blanc brothers, when there was no law to prosecute, Morris was criminally liable.
Moving forward another two decades to 2010, when the world saw what it never imagined could happen in Stuxnet: an extremely coordinated effort to create a specifically crafted piece of software, which was purpose-built to target the Iranian nuclear facility. It targeted Industrial Control Systems (ICSes). This was designed only to target a specific brand and make of Siemens ICS, which manages the speed of centrifuges in a nuclear facility. It is presumed that it was designed to deliver onsite because the Iranian facility that it was targeting was air-gapped.
This was one-of-a-kind industrial cyber sabotage. The malware was purpose-built so that it would never leave the facility of the nuclear plant. However, somehow (there is still speculation as to how), it still made its way out to the internet. It took researchers many months after its discovery to figure out the working principle of the malware. It's speculated that it took at least a few years to develop it to a fully functional working model. Since Stuxnet, we have witnessed many similar attack patterns in the form of Duqu and Flame, and it's believed by some experts in this field that malware similar to these are still active.
Currently, we are seeing new variants of attack with new modus operandi. Their intent is to earn money by using ransomware or to steal data in order to sell or destroy it. Ransomware attackers use computer viruses to infect a computer, encrypting and locking information in the computer. They then ask for a ransom from the owners to regain access to their computers. Alternatively, attackers might use victims' infrastructure to run crypto miner malware to mine cryptocurrencies.
Today, security has taken center stage, not only because the attack surface has increased for each entity, or the number of successful high-profile and mass attacks is more normalized, but because of the fact that each one of us knows that the need to secure data is paramount, irrespective of whether you are a target or not.
Modern cybersecurity evolution
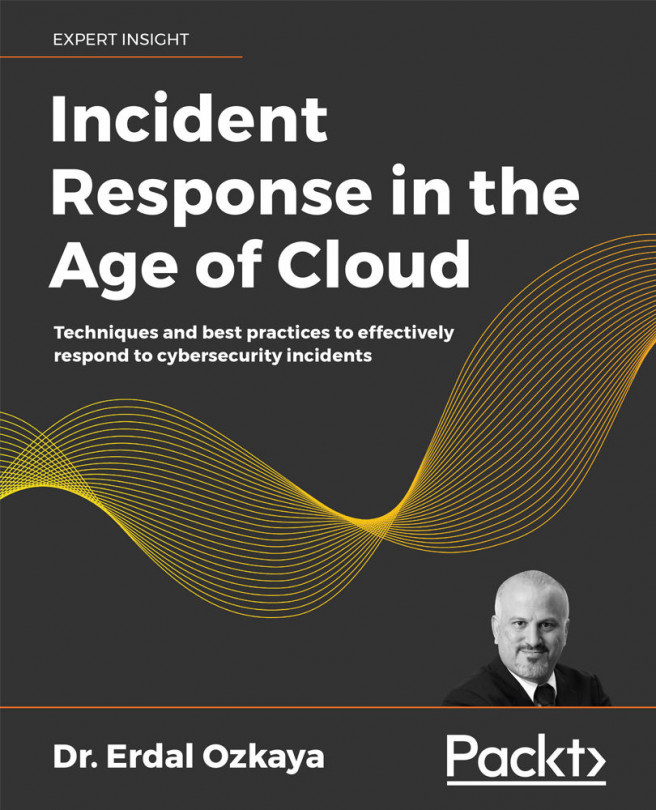
Compared just with the last decade or so, the cybersecurity landscape has evolved as threats have become more sophisticated. Not only organizations but more and more individual devices are connected to the internet. While beneficial technological progress has been happening, attacks have also evolved, as illustrated in the following diagram:
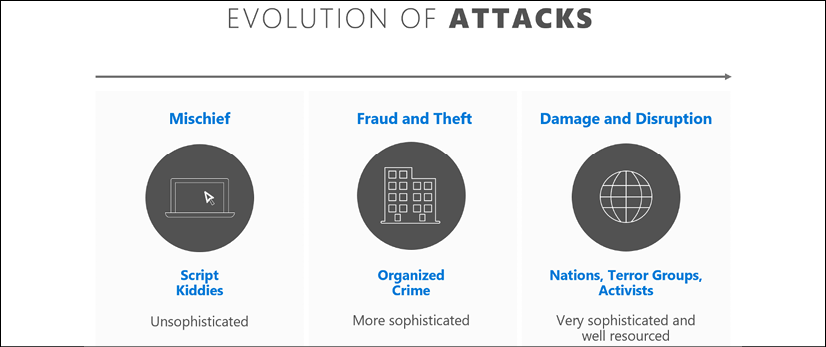
Figure 2.1: Evolution of attacks
Considering the past couple of decades since 2000, Script Kiddies were initially the main culprits, and their main motivation was "mischief." Script kiddies are unskilled persons who use attack scripts developed by other people in attacks. They were a significant threat in the early and mid-2000s due to the increased access to personal computing, low levels of security capabilities in early computers, and access to scripts written by expert hackers.
In comparison, today we see that Organized Crime is getting more and more sophisticated and their Fraud and Theft capabilities are increasing. A good example of the damage more organized attacks can inflict is the 2017 WannaCry ransomware attack, which exploited a zero-day vulnerability in Microsoft Windows and affected 150 countries, extorting victims for decryption keys. While in the 2000s a single script could've been used by multiple script kiddies until it became widely known or obsolete due to patches, currently attackers can use zero-day vulnerabilities and use them to attack systems while there are no known defenses.
The activities of Nations and Terror Groups can cause serious financial damage, as well as a negative brand reputation for affected organizations. Nation-state attackers are usually sponsored by governments and they target other government agencies or critical infrastructure as well as any key industries known to contain sensitive data or intellectual property. Nation-state attackers are well known to strike via sophisticated techniques, one of the most well-known attacks being the Stuxnet attack on an Iranian nuclear plant.
It's really important to understand the attackers and think like them to be able to create a proper IR plan. As the famous general Sun Tzu said in his book The Art of War: to win a war, we need to know the enemy, ourselves, and the attack ground. To learn more about possible attackers, it is highly recommended to read intelligence reports from security vendors such as Microsoft or Comodo, or from providers like Verizon, which can give a more detailed perspective on the current security landscape. Verizon Data Breach Report 2019 is based on a detailed analysis of 41,686 security incidents, including 2,013 confirmed data breaches. Some statistics of who was behind the recorded cyber-attacks are as follows:
- 69% involved outside actors
- 34% involved internal actors
- 2% involved partners
- 5% featured multiple parties
- 39% of breaches involved organized criminal groups
- 23% involved nation-state or state-affiliated actors
When we look at the threat actors' actions, we see the following trends:
- 52% of breaches involved hacking
- 33% included social attacks
- 28% involved malware
- 21% of breaches involved human error
- 15% involved misuse by authorized users
- 4% of breaches involved physical actions
The report also highlights that the victims were:
- 16% public sector entities
- 15% healthcare organizations
- 10% financial organizations
- 43% small businesses
As you can see from the preceding figures, the increase in technology has resulted in an increase in attacks exploiting this progress. To be able to deal with these complex attacks, which can affect organizations of any size, it's important to develop capable IR teams, which we will cover in Chapter 3, How to Organize an Incident Response Team.
Furthermore, to combat this evolution of attacks, enforced structured change in IR has been, and continues to be, necessary in conjunction with the evolution of the threat landscape. It's important to highlight that the threat landscape will continue to evolve, but the basics of IR will develop around the same framework: identify, contain, eradicate, and recover. IR processes have evolved in some ways, though. In the past, cybersecurity professionals were often seen as security guards at the gate, responsible for protecting corporate data and preventing cyber-criminals from gaining access to enterprise systems. This largely involved maintaining a "perimeter defense" and dealing with attacks as they came.
However, enterprises in recent years have started to use cloud services and bring-your-own-mobile-device policies, which operate outside the corporate network. This has shattered the perimeter defense concept and forced the security team to spend most of its time searching for threats that have already penetrated the organizational walls. Thus, today, when confronted with a breach, as well as taking a more proactive approach (more on this in Chapter 3, How to Organize an Incident Response Team), more and more enterprises are aware of the importance of Digital Forensics Incident Response (DFIR) strategies. These specialist investigation techniques are used to more effectively hunt for more sophisticated malicious entities hiding in the infrastructure, as well as providing the right tools to detect and remediate compromises as soon as possible.
Despite some progress in this area, the following statistics from IBM show us why we need to continue to invest in and evolve our IR processes; the cost of a breach, on average, is astronomical, as shown by IBM's analysis in Figure 2.2. Please keep in mind that 2020 was a more extraordinary year, where organizations needed to deal with the COVID-19 pandemic alongside normal security protocols:
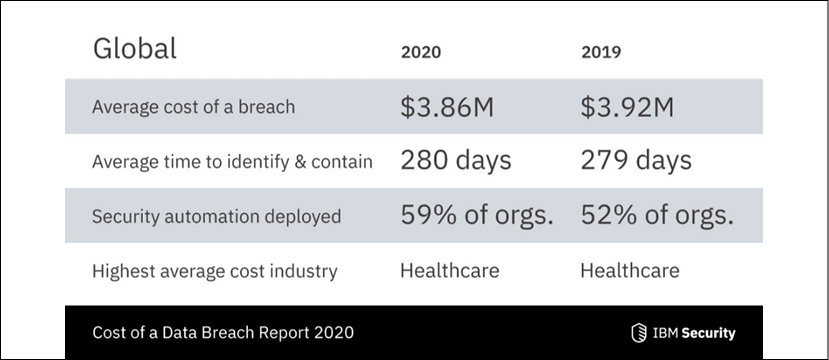
Figure 2.2: IBM cost of data breach statistics
Now, you can review the IBM statistics in the following figure, and compare them to the costs detailed in the breach report in Figure 2.2:
Figure 2.3: IBM security statistics highlighting IR value
Clearly, by investing in this book and learning IR, you are on the right path for yourself and your organization.
As you have learned by now, due to the continued evolution of attackers' techniques and methods, it is no longer a question of whether you will experience an incident, but rather when. Moving forward, readers are encouraged to communicate this to senior management since IR requires approval and input from every business unit. In the next section, we'll take a look at how IR imposes some challenges on the teams tasked with the process.
Challenges facing incident response
IR is a fairly challenging process, and IR teams meet a fair share of challenges when carrying it out. Every organization is susceptible to attacks, yet it is upon IR teams to ensure the protection of the organization, its healthy reputation, and customer trust, and moreover ensure that a similar threat will not reoccur in the future.
When a security incident occurs, confusion might hit organizations, especially if they have never handled similar security events before. An informed IR plan guides organizations, regardless of prior experiences, on how to handle each aspect of an incident. IR also mitigates the effects of a security event, to ensure minimal damage and fast recovery of key business processes. Therefore, depending on the stage of an attack or intrusion, the IR plan will detail the steps that must be taken to ensure the best outcomes for the organization. Without this guiding tool, the organization would find it hard to systematically contain any security event.
However, there are still many issues that arise in the wake of an attack that an IR team will need to effectively counter. The following section will detail some of the main challenges facing IR teams. We'll start by considering the importance of protecting the company brand.
Protecting the company brand
One major challenge facing IR teams is protecting their organization's brand, as IT security is closely tied to the reputation and valuation of an organization. As observed in recent breaches, poorly handled security incidents hurt the brands of the affected companies. For instance, Yahoo's valuation dropped by 350 million US dollars after a hack in 2017 that was reported to have affected one billion users. Similarly, a report by Kacy Zurkus indicated that the common aftermath of security breaches in organizations is a decrease in stock price.
Zurkus' article can be accessed here: https://www.infosecurity-magazine.com/news/companies-stock-value-dropped-1/.
Zurkus estimated the average drop of stock value to be 7.5%. However, security incidents, if correctly handled, might not have such a dramatic effect on the brand of the company. Due to effective incident management, Sergei Klebnikov reports that big-name companies that have been victims of security breaches mostly recover and outperform the market in as little as six months after the breach.
Klebnikov's article can be accessed here: https://www.forbes.com/sites/sergeiklebnikov/2019/11/06/companies-with-security-fails-dont-see-their-stocks-drop-as-much-according-to-report/#29da9aed62e0.
Examples of post-incident activities in such companies might include more optimized customer relationship management, to ensure that the existing clientele is retained and new customers are strategically acquired. Thus, IR faces a crucial challenge in providing ways that the organization can prevent negative publicity as a result of cyber-attacks, and thereby maintain or increase its market share.
As you can see in Figure 2.4, many well-known corporations have experienced cyber incidents or been hacked:

Figure 2.4: Organizations that have fallen victim to cybercrime
"There are two types of organizations: the ones that know they've been hacked and the ones that don't."
Preventing future breaches
As discussed in Chapter 1, Getting Started with Incident Response, the last phase of an incident management plan is reporting, and avoidance of future security incidents. Therefore, a major challenge facing IR teams is to identify the exploited vulnerability and implement permanent fixes to prevent the incident from reoccurring, leading to a better-secured organization. Some of these fixes include setting up schedules for patching, security evaluations, and backups to ensure that the organization will be best placed to deal with any future security incident. Therefore, IR acts as a preventative measure for future potential attacks.
Preparing for attacks
With the increased number of attacks, organizations are challenged to adopt and increase their cyber resilience, to survive security breaches. One of the ways to ensure resilience is by having IR teams and plans that are ready at all times. IR teams and IR plans are two tools that are part of the larger defense mechanism that an organization develops to ensure the security or recovery of its core assets during and after a security incident. IR entails building a competent team and structuring highly effective response plans that can be activated when required. Therefore, this challenge involves planning how to ensure the defense or survival of the organization before the actual attacks begin. We'll continue to consider this challenge with a discussion on the concept of cyber resilience in the next section.
Developing cyber resilience
Cyber resilience is a new approach to security that recognizes the threat of persistent, changing attacks. Having a resilient cybersecurity strategy that enables organizations to respond to inevitable breaches is key, rather than hoping that the data will never be compromised. As such, cyber resilience is a crucial counterpart to cybersecurity. As mentioned earlier, there are no shortcuts in cybersecurity, so it's important to adopt a long-term strategy, as illustrated in the following figure:
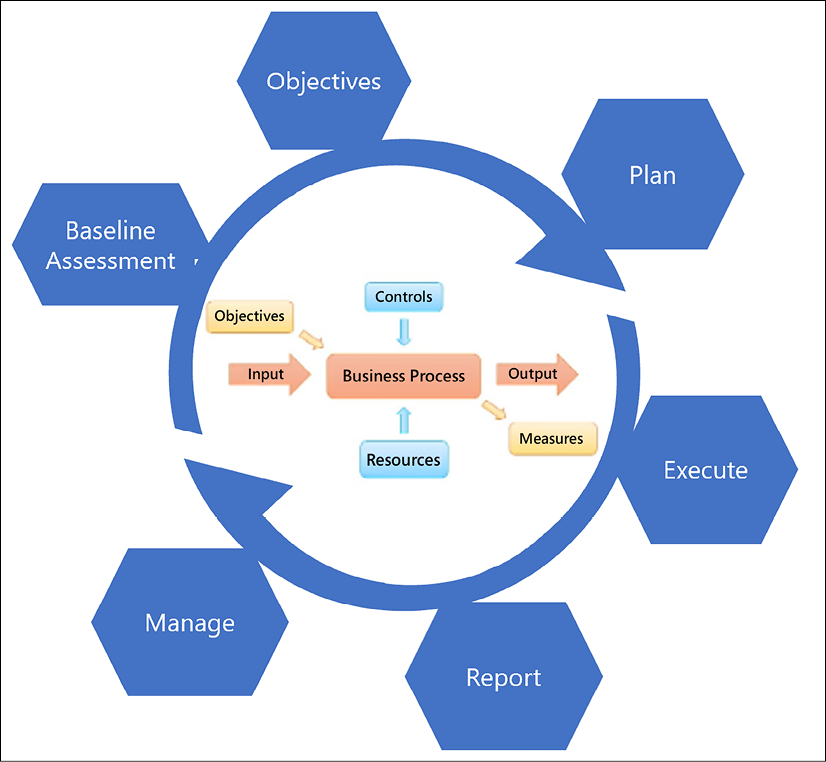
Figure 2.5: Cyber resilience strategy steps
The steps on how you can develop a long-term cyber resilience strategy are as follows:
- Baseline Assessment: This is the step in which you will need to align your organization's business requirements to your operational capabilities, and determine how you can build a successful strategy.
- Objectives: In this step, you will need to identify your resources and controls to ensure that your operational objectives are fully aligned with the strategy.
- Plan: Agree on an initial plan of action, which includes working with third-party partners.
- Execute: This step is when the plan will be carried out.
- Report: Have an outcome of the strategy in the short term (30 days), mid-term (60 days), and the long term (180 days). You can change the number of outcome days based on your needs. This is based on the Objectives and Inputs, which will need to be fed into the Business Process (see the flowchart at the center of Figure 2.5), based on your organization's Controls and Resources. These steps will help us to generate the Output (report) and Measures to take.
- Manage: Your IR plan needs to be continually updated and managed accordingly.
Now, let's consider another challenge that faces IR teams: security safeguard assessment.
Assessing security safeguards
IR is modeled around the organization's existing defense mechanisms. Thus, during the development of an IR plan, a challenge the organization faces is to assess all other defenses to work out a way they will work with the IR team. Commonly, network security tools, enterprise and host-based antivirus systems, endpoint detection and response systems, intrusion detection systems, cloud connections, and user awareness training are considered and evaluated when setting up an IR plan, as illustrated in Figure 2.6:
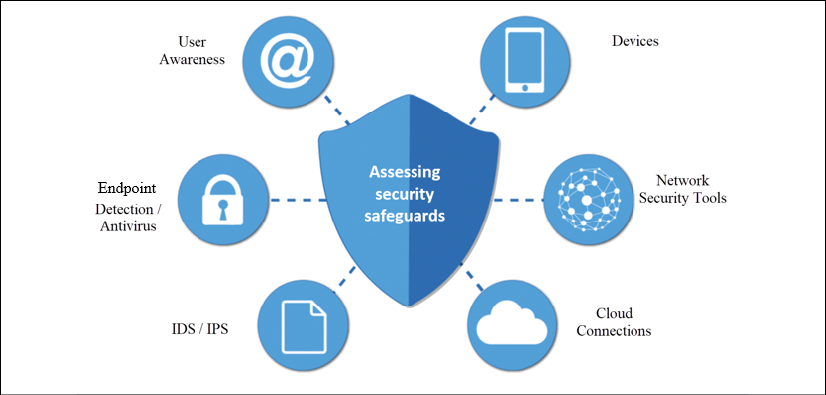
Figure 2.6: Assessing your security safeguards
The assessment of these tools provides room for the organization to find weaknesses in the safeguards and make changes to ensure better security.
Aiding investigations and legal prosecutions
In the IR process, the third phase is the investigation stage, where the IR team collects and examines evidence relating to the security incident. The evidence is retrieved from an assortment of sources such as logs, users, and security tools and may help identify the attacker or reveal the trails to other complacent parties. Eventually, the evidence can be used in the prosecution of suspects in court. Therefore, from a legal perspective, IR is important as it may help the organization win legal battles against suspected attackers, malicious employees, or unscrupulous third parties.
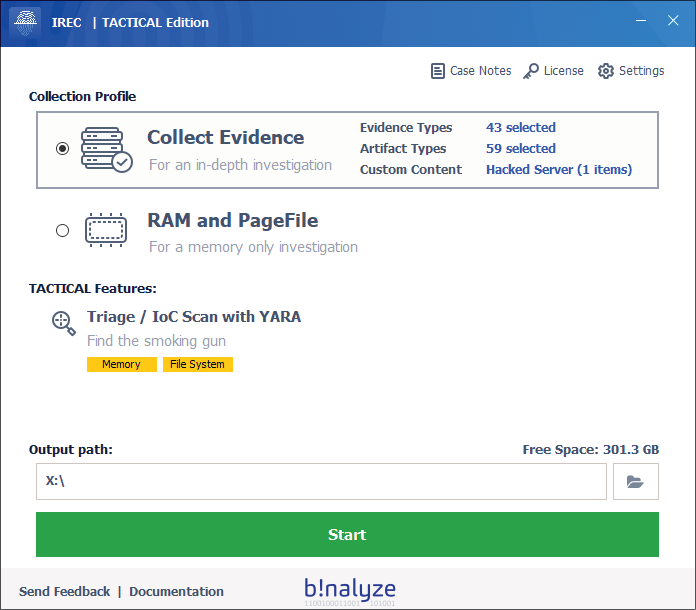
Figure 2.7: For collection evidence, tools like IREC can be used
Figure 2.7 illustrates how the IREC tool from Binalyze can help us to collect evidence, which we will demonstrate later, in Chapter 14, Incident Case Studies.
Bringing the organization together during crises
In most organizations, employees are grouped into functional units, hence they only concentrate on tasks pertinent to their departments. IR teams are composed of personnel from different departments who work toward preventing extensive damage and ensuring the recovery of the organization during security incidents. During security events such as attacks, each team member brings competencies from their respective departments. For instance, communication personnel will disseminate information as appropriate to all stakeholders during an attack, while an IT support specialist will be involved in stopping the execution of the attack. The collaboration of many departments in the IR process improves cohesion and cooperation in the organization even after the security incident has been dealt with.
Ensuring the integration of security initiatives
Organizations might have several security initiatives that work independently. For instance, many organizations have IT security policies, employee training programs, security awareness programs, IT auditing, change management plans, and penetration testing as part of their security framework. However, most of these initiatives are not integrated.
For instance, penetration testing exercises might not be connected to employee training programs. IR has a unifying effect on the existing security measures to bolster the defense capability of the organization. Therefore, during IR planning, all these tools will be identified and refined to work together to secure the organization. For example, during the planning process, related initiatives such as employee training and security awareness programs can be combined. Similarly, IT auditing and penetration testing could be made to complement each other in a situation where penetration testers identify weaknesses first, and IT auditors focus more on the problematic areas when examining the organization's IT assets.
Improving the overall security stature of the organization
Conventionally, organizations relied on cybersecurity tools to ensure the security of their organizations. Hence, only the IT department was tasked with cybersecurity-related functions. However, as the frequency, complexity, and intensity of attacks have grown, organizations have had to adopt more effective security measures to prevent, combat, and manage attacks. IR is one of the relatively new ways to improve the security stature of the organization. When all else fails and an attack permeates to the organization, the IR team can be tasked with eliminating the source and recovering the organization. Thus, security is no longer hedged just on security software but also on a highly effective team that will resolve security threats when they occur.
The following are six best practices you can use to improve your organization's security posture:
- Conduct a cybersecurity risk assessment
- Prioritize risk
- Track security metrics
- Implement automated cybersecurity solutions
- Educate your employees
- Create an IR plan
These categories will be explored throughout different chapters in this book.
The headings in this section have covered some of the main challenges faced by IR teams when carrying out IR. Mainly, these teams have to look at how they can secure the company's brand, prevent future attacks, improve security stature, integrate all security initiatives, assist with evidence collection to aid in investigations, and still be a strong unit that brings the organization together during crises.
Why do we need incident response?
Incidents are on the increase and it has become apparent that if they are not contained properly, they can easily escalate into issues that can damage an organization. A reliable solution is to prepare adequately on how to address security incidents when they happen. IR enables organizations to take essential steps to address the ever-present threat of cyber threats.
Therefore, IR is a necessity in organizations today. Poor handling of incidents can lead to the escalation of manageable security events into catastrophes. As recent reports from security incidents have shown, IR helps organizations to mitigate attacks, minimize losses, and even prevent future security incidents.
To achieve the best outcomes from IR processes, the organization should ensure that it acts with speed immediately after a security event is detected. However, before executing the mitigative actions, the nature and extent of the security incident have to be determined. In the short term, the organization ought to focus on deploying resources to combat the active threat and return the organization to normalcy. This should be done in parallel with seeking assistance from law enforcement and third parties to assist with tracking down the cause. In the long term, IR activities can be focused on identifying the cause of the threat to find permanent fixes, improving the security tools used to ensure better detection and prevention, prosecuting the culpable parties, and addressing reputational damage.
Despite the reliance on conventional cybersecurity approaches that are heavily reliant on security tools, new threats can be best mitigated by people and processes. Hence, IR, which combines the efforts of security tools with people and processes, will often lead to more effective solutions. Organizations must, however, continually evaluate their IR plans and teams to ensure that their effectiveness improves over time. Nonetheless, the importance of IR in modern IT environments cannot be underestimated.
Tips
- As discussed in Chapter 1, Getting Started with Incident Response, always be ready.
- Build proper detection and reporting capabilities.
- Education/awareness should be one of your core priorities.
- Always keep an eye on data breach reports from Verizon, Microsoft, and Kaspersky, as well other vendors. If you don't want to go through all those individual websites, you can check my blog, where all the aforementioned reports are kept under one blog post every year: https://www.ErdalOzkaya.com.

Figure 2.8: Threat reports under one link, updated regularly
Summary
This chapter has gone through the evolution and current challenges of IR. It has explained the need for IR to respond to changes in the threat landscape and technology advancements. It has also highlighted that teams also face various challenges with IR. As explained, IR must help the organization handle incidents effectively by providing a guide to contain and mitigate the effects of security events. An IR team also has a responsibility to protect the company brand by handling any eventualities that might ruin the reputation of the company. Methods to prevent future breaches are necessary by ensuring the implementation of permanent fixes to common security incident sources and preparing for attacks by boosting cyber resilience. Furthermore, IR contributes to the improvement of the security stature of the organization and ensures the integration of an organization's security initiatives. Lastly, IR teams face the challenge of assisting legal investigations and court prosecutions by collecting evidence that can be used to build a case against suspects of attacks.
In the next chapter, we will look at the composition of the IR team, to learn more about the various professionals required to make the team function optimally.
Further reading
The following are resources that can be used to gain more knowledge on this chapter:
- Comodo, breach detection resources: https://www.comodo.com/business-security/email-security/breach-detection.php
- Forbes, Companies With Security Fails Don't See Their Stocks Drop As Much: https://www.forbes.com/sites/sergeiklebnikov/2019/11/06/companies-with-security-fails-dont-see-their-stocks-drop-as-much-according-to-report/#29da9aed62e0
- Infosecurity, Companies' Stock Value Dropped 7.5% after Data Breaches: https://www.infosecurity-magazine.com/news/companies-stock-value-dropped-1/
- DARKReading, Why Every Organization Needs an Incident Response Plan: https://www.darkreading.com/edge/theedge/why-every-organization-needs-an-incident-response-plan/b/d-id/1335395
- Infosecurity, The Importance of a Cyber Incident Response Plan and the Steps Needed to Avoid Distaster: https://www.infosecurity-magazine.com/opinions/the-importance-of-a-cyber-incident/