Chapter 1: New Career in Cyber… "Who Dis?"
Cybersecurity is the hot new career field. It might even be hotter than the Kardashians. Why, you ask? To put it simply, technology is spearheading global growth. With new technology such as artificial intelligence and machine learning comes more cybersecurity demand. It's the whole supply and demand concept you learned in high school.
While more jobs are becoming remote, virtual, or replaced by robots, how do you think they are protected and secured? Cybersecurity is more than an IT helpdesk or the hackers you see on TV. It's a broad spectrum within all aspects of technology that has made cybersecurity an upward slope for careers, which will not change anytime soon.
What we know today will drastically change from what we know 1 year from now. We know that cybersecurity professionals make great money and get to wear hoodies and flip-flops to work. With all the positives do come some negatives you will learn about within this chapter.
During this chapter you will have me, Jaclyn (Jax) Scott, leading you. You are encouraged to have a notebook close while reading this chapter and following chapters to help with your data retention.
In this chapter, we will explore cybersecurity by breaking it down into the following sections:
- Learning about the current state of the industry
- Exploring the foundations of cybersecurity
- Understanding the pro and cons of cyber careers
Learning about the current state of the industry
Cybersecurity is rapidly growing because of emerging technology that is producing an ever-changing threat-scape. There is a reason for the rapid growth of technology, and it's outside of the next cool Clubhouse or Tinder app or that new self-driving car that picks up self-drinking slushies. It lies within history.
As you may have heard in history class, history educates us about our future. This is true even within cybersecurity. The world leaders are driven by one thing, what is that? Power! How has power historically been obtained? Typically, and sometimes the most prevalent example is war. As cyber has emerged, so has a new type of warfare called cyberwar, which is ongoing.
The battlespace and the soldiers have changed. As technology emerges and grows, so have the world powers seated at the executive table. China in 2019 was the first country to send an unmanned rover to the far side of the moon. We have self-driving cars and the prediction is that in 5 years, we could take trips to Mars. Technology is growing and maturing in unimaginable ways.
Understanding why cybersecurity is advancing in all sectors to include phone apps and smart TVs will help you grasp the projected technological growth and prepare you for a cyber career. It's crucial you understand the maturing threat-scape and vulnerabilities that exist everywhere.
Here are some things to consider related to the cybersecurity industry:
- Hackers are becoming more advanced.
- Tools for amateur hackers continue to get simpler.
- Cybercrime is exploding (and it's expensive for organizations).
- Automation is the future.
- Vulnerabilities are endless.
In 2020, many careers were impacted due to the global health crisis and pandemic called COVID-19, while cybersecurity jobs remained in demand. A primary reason is because everyone went from working in a controlled office space with secured networks and on-premises monitoring to working on grandma's 100/100 Wi-Fi with a default password that was 4 years old.
This new workforce left a lot of employees and companies extremely vulnerable to a cyberattack. There was a considerable increase in ransomware attacks during 2019-2020 because attackers exploited these vulnerabilities. This meant more job opportunities for penetration testers and cybersecurity professionals to protect the new remote workforce.
Cybersecurity is not going away because cybercriminals will always find more creative ways to lure their victims to "click", which keeps you in a cyber job long after your first marriage.
Cyber laws and regulations
Before we jump into the next section, we will cover some of the cyber laws that influence the overall cyber growth and impact this field.
As we are writing this book, cybersecurity laws and legislation are a sticky topic. Congressional leaders are uncertain on how to address them because they don't know how to manage the cyber growth and the World Wide Web. The threat-scape is changing quickly, making it very challenging to determine what to address. Many of the cyber laws we have today are reactionary laws, meaning something happened, then a law was developed and enacted trying to prevent it from happening again.
An example of a reactionary law is when the first significant data breach happened to Yahoo in 2016, when hackers stole approximately 500 million accounts dating back to 2014. This breach then sparked the need for data protection and next came the Consumer Privacy Protection Act of 2017.
The challenge is knowing what laws you need before something happens. How can you create a law to predict something that has happened yet?
To understand the purpose of cybersecurity regulations, we will give you a law overview to help you better understand the current state of cyber legislation.
Quick cyber law class
The United States legislative system falls within three broad categories: criminal, civil, and administrative law. Cybersecurity regulation comprises directives from the Executive Branch while legislation comes from Congress designed to safeguard information technology and computer systems. The purpose of cybersecurity regulations is to force organizations to protect consumer data from being stolen and used for malicious means.
It wasn't till the Computer Fraud and Abuse Act (CFAA) of 1984 that the US saw any significant legislation specific to cyber law. This law covered general crimes such as malicious damage to federal computer systems of more than $1,000, trafficking of computer passwords, and modification of medical records. CFAA received its first amendment in 1994 when Congress recognized the face of computer security had drastically changed since 1984; this amendment was called the Computer Abuse Amendment Act.
The Computer Abuse Amendment Act considered more sophisticated actors that could target organizations through malicious code. It would allow for offenders' imprisonment, regardless of whether they intended to cause damage or not. There were more amendments in 1989, 1994, 1996, 2002, and the final one in 2008. Nevertheless, the laws was still very vague. This law also led to Aaron Schwartz's well-known case of 2009 and eventually his arrest a couple of years later in 2011. Mr. Schwartz was prosecuted for downloading many academic research papers from the MIT database.
Here is a brief list of current cyber legislation you will likely hear more about as you move through your cyber career:
- Health Insurance Portability and Accountability Act (HIPPA) of 1996: Designed to protect individual health records.
- Consumer Privacy Protection Act of 2017: This law was developed shortly after the large Yahoo breach in 2016 and was designed to protect customer information to avoid identity theft.
- General Data Protection Regulation (GDPR) of 2018: This is the European Union's most stringent privacy and security law globally, and it impacts US activities.
- California Consumer Privacy Act (CCPA) of 2018: This was the first US-specific bill passed to protect the consumer's rights by giving them more control of personal information shared.
In recent years, the US government also used specific bills and laws to strengthen its effort with communication and data sharing.
This includes the following bills and organization:
- Cybersecurity Information Sharing Act (CISA) of 2014: CISA provides a platform for information sharing through an open source platform while spreading cyber activity awareness.
- Cybersecurity Enhancement Act of 2014: Voluntary collaboration platform for public-private partners to improve cybersecurity through research, education, and public awareness.
- Federal Exchange Data Breach Notification Act of 2015: Requires health insurance to notify any individual whose personal data was subject to unauthorized access, such as a data breach.
- National Cybersecurity Protection Advancement Act of 2015: This was an amendment to the Homeland Security Act of 2002 to allow other entities such as tribal, private, and non-federal representatives within the Department of Homeland Security (DHS) National Cybersecurity and Communications Integration Center (NCCIC).
The following is a message from the United States Department of Justice on who to report cybercrimes to, dated April 1, 2021:
Now that you understand why cybersecurity is the trending career field and the laws that govern it, we will move into the foundations of cybersecurity.
Exploring the foundations of cybersecurity
What is cybersecurity? Cybersecurity defines processes, technology, and design frameworks developed to protect organizations' devices, programs, data, and other valuable assets from unauthorized access from a cyber threat.
This section will provide you with a basic understanding of cybersecurity, key terms such as risk versus vulnerability, and different cybersecurity frameworks, which include the CIA Triad, NIST, ISO, and SOC2.
Threats, assets, vulnerabilities, and risks will be covered in the following section. We will explain the fundamentals of how cybersecurity professionals protect data, devices, networks, and systems from attacks from viruses, malware, hackers, and data breaches.
Asset, vulnerability, risk, and threat
Some terms you will hear often within cybersecurity are asset, vulnerability, risk, and threat. These are key terms you should learn and know. We will cover these briefly in this section
Here are their breakdowns:
- Asset: This is anything in the environment that needs to be protected, such as data, people, proprietary tools, and processes essential for business operations.
- Vulnerability: A weakness within your organization that can be exploited, such as flaws in software code and out-of-date software.
- Risk: The likelihood or possibility a threat was successful in breaching your network, the risk would be the asset's total loss. The following is an example of the risk formula to identify your organization's risk:
Risk = Threat x Vulnerability
- Threat: Anything that is trying to degrade, disrupt, or steal your asset is a threat. This would include cybercriminals or insider threats.
The preceding is not an inclusive list, it is the basics to help you get started. We encourage you to dig further into each of these to understand their roles within cybersecurity. Next, we will discuss the CIA Triad.
What is the CIA Triad?
The CIA Triad is not the Central Intelligence Agency composed of US government employees who provide national security intelligence to congressional leaders in America. The CIA Triad in cyber means Confidentiality, Integrity, and Availability. These are the core pillars of information security (InfoSec) a subset of cybersecurity. Throughout this chapter, we will focus on the CIA Triad three pillars as they are foundational elements of InfoSec.
The CIA Triad will be referenced throughout your career because it's the foundation in developing information security policies.
"So, what is the CIA Triad?" We are happy you asked. We will explain the CIA Triad by using the following diagram:
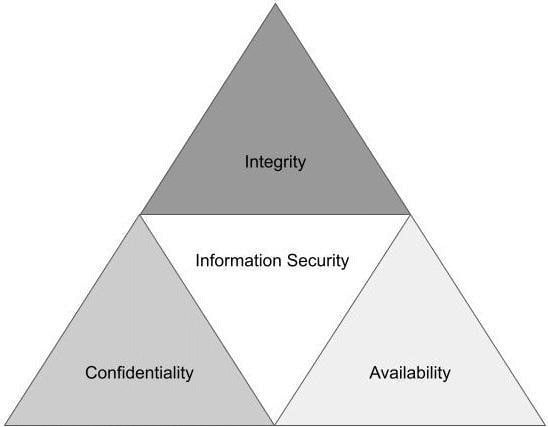
Figure 1.1 – CIA Triad
The easiest way of thinking about the CIA Triad is as a security model to help unpack various information technology (IT) security components. This model helps develop security policies to identify problem areas on a network while providing appropriate solutions. In the next section, we dissect each pillar in more detail.
Confidentiality
The best way to think about confidentiality is ensuring that only select users can access specific data. This could include encryption techniques, but there are far more ways to achieve confidentiality on a network.
Generally, all organizations have some form of sensitive information. This may include client data, company proprietary data, and customer or employee personal identification information (PII). Most companies' information systems store information that has some degree of sensitivity.
Data is the new gold and criminals target organization data in the hope of either encrypting or stealing data. Then the organization are forced to pay large ransoms to get it back. A common attack technique is a ransomware attack, where a criminal either encrypts or steals your data then holds it hostage until you pay the ransom using cryptocurrency.
Note
Cybercriminals will often target organizations with significantly more sensitive data because they know the payout will be larger.
An attack vector used for a ransomware attack is a phishing email. Once the threat actor has successfully breached the network, the second phase of an attack could include password stealing, credential harvesting, and data encryption.
Not all data breaches are criminal in action, meaning someone in the organization could share classified information with someone who does not have the appropriate classification to read the data. An example could include forwarding an email to the wrong Susan Smith. Instead of sending it to Susan Smith in Countermeasure, they instead sent it to Susan Smith in Human Resources. Another example is leaving a computer unattended and the email inbox open with PII data exposed for another employee to see.
An intentional or unintentional data breach will lead to the same result: sharing confidential data with those who do not have access.
Countermeasures to help reduce the likelihood of a data breach and increase confidentially would include the following:
- Access control list
- File and volume encryption
- Authentication through software to control access
- Administrative policies
- Continuing employee training and awareness
- Physical hardenings such as cameras and access control
The preceding countermeasures should be part of a layered security approach. It is best to have multiple security countermeasures in place to protect the confidentiality of data.
Integrity
This pillar ensures that your data stays intact and is not changed or altered. This provides data assurance, completeness, and accuracy. Data integrity is essential for both data at rest (stored data) and at flow (emails). Integrity maintenance starts with access control and ensuring that only authorized users have access to modify data.
Data integrity protection extends beyond malicious attacks. Unintentional alterations can occur if access controls are not maintained and the employee obtains access to a file and deletes or alters files, causing data loss or, network complications.
Try searching Largest data breach of today, or Largest data breach of 2021, and more than one article about different breaches will come up. Why? Because data breaches are becoming more and more prevalent and, unfortunately, will never go away.
Hackers are becoming more creative and finding novel ways to lure their victims into their clickbait. The cyberwar between cybercriminals and cybersecurity experts is a cat and mouse game. The number one thing you can do to protect integrity of data is ensure your organization's countermeasures are maintained regularly. Authentications should be robust, with access control updated regularly to help prevent unauthorized access to networks and files.
Another great example of how integrity of data is being questioned are through deep fakes. Deep fakes are videos or photos that look and sound like the real thing. As technology becomes better, identifying deep fakes becomes more challenging. The integrity of the document or photo is then in question and can create a myriad of other problems.
Availability
Availability ensures that the users have timely and uninterrupted access to information, systems and networks. How many times have you been working and suddenly your cloud storage stops working or the document you were working on is gone or corrupt? Availability ensures access to data at any time without any obstacles such as network outages or data breach.
A malicious attack includes cyber-espionage, where the attacker's intent is to impact the network by encrypting all the data. By denying access to the data, organizations are forced to pay the ransom or start over from scratch, which can also cost a lot of money and time. There are unintentional and non-malicious activities that impact availability that include natural disasters, bandwidth, or unscheduled software updates.
Important note
Certain individual states in the United States are proposing new laws to ban ransom payments to cybercriminal.
An example attack method that adversaries use to disrupt companies' data availability is known as Denial of Service or DoS attacks. This is an unsophisticated attack in which an attacker will flood a server with requests to overwhelm and disrupt the web service or degrade services for clients and employees.
Countermeasures to strengthen availability are as follows:
- Large organizations should consider hardware redundancies such as backup servers and data storage availability.
- Automatic cloud-scaling capabilities.
- Monitoring software such as endpoint protection to monitor the network for performance will help prevent unwanted traffic.
- Standard firewalls and routers should be updated regularly to ensure compliance.
At this point, you should have a solid foundational understanding of the CIA Triad, its purpose, and how to apply it within your organization. Next, we will cover three different cybersecurity frameworks. This is dense information, so I completely understand if you are reaching for something a little stiffer than water.
Different cybersecurity frameworks
The first cybersecurity framework we will discuss is NIST. NIST stands for National Institute of Standards and Technology. NIST is a framework that helps a company develop organizational controls and risk management for their information security program.
Important note
There are other internationally recognized security frameworks not covered in this book; these include IASME, COBIT, and CIS.
The NIST framework is broken into three parts:
- Framework Core
- Implementation Tiers
- Framework Profiles
Framework Core
The Framework Core is made up of five functions. The easiest way to remember them is to think of Identify and Protect as the organization's actions to prepare itself against a cyberattack. Detect, Response, and Recover are all the things you will do after a breach or incident occurs.
The five core functions are as follows:
- Identify: Manages risks by correctly understanding assets, data, and other resources.
- Protect: Protocols and countermeasures in place to protect critical infrastructure.
- Detect: Defines what makes an event versus regular network activity.
- Respond: Response to events through predefined actions.
- Recover: Recovery processes for repair services and network.
If you want to learn more about NIST and download the framework's Core Function and Category spreadsheet, you can visit https://www.nist.gov/ and search for NIST Framework.
Implementation Tiers
The Implementation Tiers are a total of four tiers, which range from partial to adaptive. Figure 1.2 provides you with a graphic depiction of the NIST Tiers and the degree to which information is shared, and how well cybersecurity risk and decisions are integrated into the organization's broad spectrum:
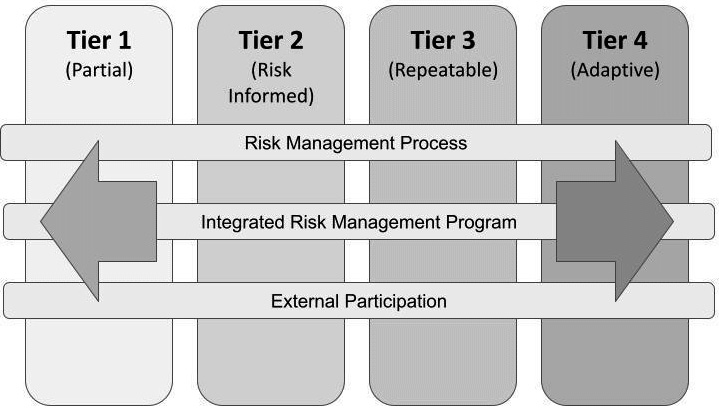
Figure 1.2 – NIST Implementation Tiers
These Tiers are defined by the organization requirements' objective. The organization must decide its level of risk, resources, and tools to defend against a breach.
Framework Profiles
The last portion of the NIST Framework is optional but highly encouraged because it helps an organization define its unique security posture objectives. Protection of data is essential, and companies must clearly define their risks and resources. The Framework Profiles are used to identify opportunities for refining or improving overall cyber hygiene. Organizations can have a current and future profile for their end state. A business may also have different profiles based on their business needs and capabilities. This process takes time and should be looked at as an ongoing and never-ending process.
Organizations should always be working on their current cyber profile to identify opportunities to increase cyber awareness and harden overall cybersecurity posture to improve security.
ISO Cybersecurity Framework
ISO 2700/27001 was created by the International Organization for Standardization. Their certifications are recognized internationally as the international standard for validation for cybersecurity programs. This standard is more risk-based focused versus technical focus.
Important note
Cybersecurity risk is an organization's probability of exposure or loss resulting from a data breach or cyberattack. When an organization takes a risk-based approach, it typically means the organization uses a methodology based on the analysis of the risk and the risk of the management framework.
This framework has over a dozen different standards for organizations to use for their security management of assets.
SOC2 Cybersecurity Framework
SOC2 stands for Service Organization Control Type 2 and is a cybersecurity framework and auditing standard developed by the American Institute of Certified Public Accountants (AICPA) to ensure organizations are securely managing client and vendor data. NIST and SOC2 may appear to be opposite sides of the same coin; both are designed to review an organization's internal controls.
Note
NIST offers a framework for InfoSec and privacy controls while SOC2 enables organizations to obtain certifications of compliance.
We encourage you to take additional time and look into these frameworks, and the others, when you have more time. Next, we will discuss the different types of cyber attacks.
Types of cyber attacks
There are a lot of terms you will learn and need to understand to speak cyber. Terms used to explain certain cyber attacks are essential to know so you can understand the threat to then implement the proper countermeasure to mitigate the threat. For example, if an organization was concerned about a Distributed Denial of Service (DDoS) versus a phishing attack, the infosec team would have different countermeasures to investigate and mitigate the risk.
This section describes the top 10 most seen cyberattacks. This is basic information designed to provide a high-level context of different threats.
Distributed Denial of Service (DDoS)
A DDoS attack is achieved when an adversary targets your network and floods it with a high number of packets. This type of attack is measured by the amount of bandwidth involved. An example is in 2019 when a DDoS attack impacted GitHub. GitHub reported a peak of 1.35 terabits per second. At the time, this was the largest DDoS attack to date.
What happens during at attack like this is the threat actor will overwhelm the server and make it impossible to conduct business as usual (BAU). Unlike most attacks, where the attacker is trying to gain access, a DDoS is designed to degrade the company network and denial of service.
If you see a DDoS attack, it's likely an unsophisticated attack. However, recently, experts are beginning to see cybercriminals using DDoS as a secondary attack vector layered onto a primary attack. An example is when a threat actor targets a victim using a phishing lure. Once successful, they will encrypt all the victim's data. If the client refuses to pay the ransom, the threat group will conduct a DDoS on their network to disrupt it enough, making it impossible to conduct BAU. Eventually, the victim will pay or wipe everything and migrate to an entirely new server, which can be very costly with a lot of downtime.
Here are some types of DDoS attacks you may see:
- TCP SYN Flood attack: This happens during the Transmission Control Protocol (TCP) session when initializing a handshake. They exploit the buffer space and overload the system with connection requests.
- Smurf attack: The attack will spoof a known IP address and the Internet Control Message Protocol (ICMP) to overwhelm the target network. This is an echo request targeted at a select range of IPs with a response reaching back to the spoofed IP.
- Teardrop attack: The attacker will overlap the length and fragment fields within sequential IP, causing the system to try and fail at reconstructing the packets making the system stop working.
- Ping of Death attack: This attack uses IP packets to ping a target network and a large IP size. When the IP packet is not allowed, the threat actor will fragment the IP. Once the system accepts the packet, it will then experience buffer overflows and crashes.
Man-in-the-Middle
Man-in-the-Middle is when an adversary places themselves between a client and server's communication. This is when the following could occur:
- Session hijacking: This is when the attacker can control the client and then disconnect the client from the server. Once disconnected, the attack will replace the host machine IP address with the attacked IP address then spoof the client sequence number. The computer would look like BAU while under the control of the attacker.
- IP spoofing: This is when the attacker uses what appears to be a legitimate IP address to communicate with the host computer. The host machine could accept the packet from the spoofed IP and act upon it.
- Replay: The attack will replay an old message to obtain access to a system. This is accomplished when the attackers intercept a message to save for later use.
Mitigation techniques include using secured session tokens, time-stamping messages, and secure DNS. Multi-Factor Authentication, or MFA, and digital certificates also help to mitigate these attacks and aid in keeping confidentiality and integrity intact during communication.
Note
MFA is a multi-step authentication process to grant users access to specific applications. Examples of MFA include something you know, something you have, and something you are. Examples would be a password, an authenticator code, and a fingerprint.
Phishing, spearphishing and business email compromise attacks
Phishing is the most used vector for cyberattacks. Phishing attacks can be divided into three different attacks listed below.
- Spearphishing: Targeted attack that focus on a small group of people or organization.
- Business Email Compromise (BEC): Targets higher leadership or someone who can make purchases. Typically, the lure in this attack will be about a gift card purchase coming from a trust source
- Phishing: Untargeted attacks sometimes referred to as a "spray and pray" attack. Spray and pray are the most common phishing attacks and they are designed to hit a larger number of emails without a specific target in mind.
Typically, the emails will come from a trusted source to lure its victims to click. They will also use emotional queues to get their victims to click, such as urgency or money tied to the message.
Most organizations have certain protocols to ensure their employees are trained to identify a phishing email versus a legitimate email.
Drive-by attack
Have you ever seen an advertisement online to win an iPad? Surprise, you never win an iPad, but you might win new malware on your computer. These attacks are called drive-by compromises because they lure their victims by setting clickbait on either legitimate websites or within a search engine.
Protection from these attacks could include spam-blocking software and maintaining an updated and patched browser. Try to avoid having too many unnecessary programs, browser extensions, or apps on your computer. These are third-party vendors that could be hacked and could impact you and your security.
Password attack
Attackers know if they obtain your password, they will likely have access to others areas of your system.
Tip
Do not use the same password for everything. Consider the strength of the password to the data you are attempting to protect. The password for your bank account should be stronger than the password you use for your video streaming platform. Both have personal data, but one has more critical data than the other.
Some of the techniques used for password hacking includes brute-force and dictionary attacks:
- Brute-force attack is when the attacker will rely on guessing, often through automation, and attempting as many times as possible. Typically the guesses are attributed back to the user's likes and hobbies. If your password is complex enough, it will take a long time to crack it.
- Dictionary attack is when the attacker attempts to use the most common passwords.
If either of these attacks are successful, the attacker will gain access to your machine and can collect or encrypt your data.
MFA helps mitigate this risk, as do timeouts.
Note
Timeout sessions are examples of when a user is logged off after idle time or after a certain period of time such as 12 hours. Then the user must re-authenticate to begin the session again.
Cross-site scripting attack
A cross-site scripting attack happens when a user goes to a legitimate website that was injected with malicious code. When the victim visits this website, the website will transmit the page with the attack payload in an HTML text. Then the malicious script will execute on the host machine. The outcome could be seen by stealing cookies, capturing screenshots, and logging keystrokes by prompting the user to log in again.
SQL injection attack
This type of attack is seen within a database-driven website. The attacker will input a SQL command into a database input to run the predefined SQL command. If successful, the SQL injection can modify or exploit data on the database, and even give a command to the operating system. To reduce the likelihood of this type of attack, ensure your access to the database is updated regularly, sanitize your variables/inputs, and configure baselines for the database management systems.
Malware attack
Malware is a fancy way of saying malicious software. There are many different types of malware, which can be Trojans, stealth viruses, logic bombs, worms, droppers, and ransomware. We encourage you to conduct your own research to learn more about malware.
Malware is the standard type of infection you will likely see on a system. It's essential to have a basic understanding of each type of malware and how it can infect a system. The best approach to limit possible infection of malware is by keeping operating systems patched, VPN enabled, and using an updated browser. Most successful attacks can be avoided with proper system patching and software updates.
Eavesdropping attack
An eavesdropping attack is also known as a snooping or sniffing attack. Unlike the Man-in-the-Middle attack, an eavesdropping attacker listens either passively or actively to the user's network. They listen to the network traffic to find data such as credit card info or passwords. The best prevention against this type of attack is MFA and overall system encryption.
Rogue software attack
Attackers have been using rogue software attacks since 2008. The attacker will lure its victims by making them think they have a virus on their machine. Once they have struck panic in the victim, they will convince them to pay for a removal tool that is masquerading as legitimate software.
The vector for this type of attack can be when a user goes to a website and suddenly sees a popup saying, "Your system has been infected with malware, act now, click here to conduct a virus scan." Once the victim clicks, depending on the victims antivirus, the download begins. Another name for the malware used in this type of an attack is called scareware because the purpose is to scare the victim into reacting quickly.
The following diagram will assist you with remembering the attack names:
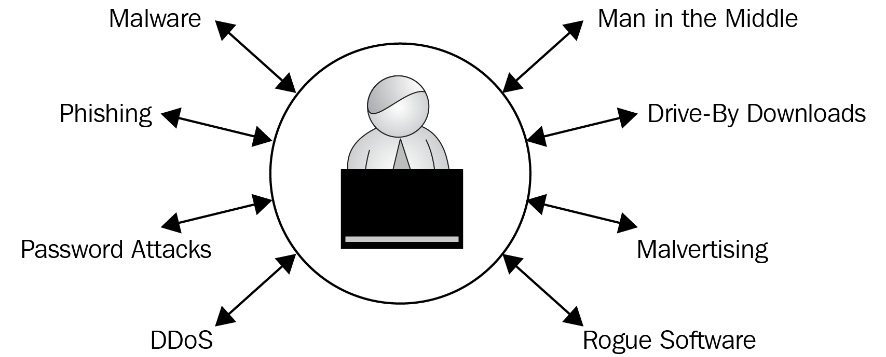
Figure 1.3 – Types of cyber attacks
As we conclude this section, we encourage you to take the time to research and learn more about cyberattacks.
In the next section, we will discuss cyber careers. I will provide you some pros and cons to prepare you for entering this field.
Understanding the pros and cons of cyber careers
Earlier in this chapter, we discussed how cybersecurity is the hot new career field and that it's not going away anytime soon. Before stepping into any new industry, it's important to know the pros and cons of that industry. This section will explain some of the advantages and disadvantages of the cyber field.
The following are subjective to the business and our professional thoughts. It is best you research and network with others in the industry to obtain a clearer understanding of this career field.
Some advantages of working in cybersecurity are as follows:
- Flexible hours.
- Sizeable salaries.
- Remote work.
- Culture varies in each workplace.
- A large diversity of positions and specialties.
- Recruiters look for you.
- You can train yourself.
Let's go into detail of each of these in the next sections.
Flexible hours
The cyber industry runs on a 24/7 clock. It never ends, which is wonderful news for those needing to work flexible hours. It also makes entry into the sector a little easier. As you may imagine, typically, the graveyard shifts are less-sought-after hours, meaning, if you have the ability, working a swing shift at night could be your ticket into the industry. Also, depending on the company, they may allow you to work off-hours to accommodate school or other activities as long as you still clock 40 hours. This will always depend on the organization, so make sure you talk with the recruiter on the hours and flexibility.
Great salaries
This career field pays well because of the skills and education required. Depending on your geographic location and company, many entry-level jobs will start between $70-$80. There are a lot of other factors that tie into this salary. A good rule of thumb is coming in with supporting education (either certificates or college) and hands-on experience. Then you can negotiate to a higher position. Education and the hands-on experience will be discussed in Section 3, Now You're in; Time to Level Up!, of this book.
Remote work life
More cybersecurity jobs are moving to remote work environments. This is because the companies see the benefits of saving overhead costs while allowing their employees to control their daily work life. This is not a hard and fast rule. You should verify with the employer whether they are fully remote or whether they provide a hybrid work life.
If you seek to work in an environment that requires a security clearance, you will likely be required to work on-premises 90% of the time. Again, this is something you should discuss with the recruiter to confirm the dynamics of that organization.
Cultures vary
When you have worked in one cybersecurity environment, you have worked in one cybersecurity environment. Many times, merely changing departments, not the company, is all you need. This is a pro because you may land your first job and a few months in realize you don't enjoy the culture. Fear not, you can talk with your current leadership and see about moving into another section.
From my personal experience of moving from one section to another, it was a positive shift for my professional growth. Never feel like you are stuck. If the culture does not fit your personal beliefs and values, know that it's not the same everywhere.
If you can, reach out to others in the organization to get their thoughts on the culture before accepting a job. Ask a lot of questions and if the company doesn't align with your beliefs, move to something else.
Large diversity of positions and specialties
Diversity of careers in cybersecurity is endless. This is very exciting because you can never get bored in this career field. Additionally, you can progress quickly through further education and training. With the appropriate certifications and degrees, you can learn your way out of your old job and into a new position.
Recruiters look for you
Once you have some hands-on experience in this field, pivoting becomes much easier. One reason is because there are more cyber jobs available than qualified candidates. This means the recruiters sometimes contact you for jobs. The best way to put yourself out there is through a proper brand and network. Branding and networking will be discussed later in Section 3, Now You're in; Time to Level Up!, of the book.
You can train yourself
In this career field, you don't need a formal education. The great news is you can train yourself through free online resources and certification. There are a ton of free online resources to help you learn and develop the skills you need to succeed. Take advantage of the free resources before you begin paying 3000-7000$ for a certification.
Now that we have gotten you super excited about all the positive aspects of this career, let's pivot a bit and explain the downsides or cons of this field.
Some disadvantages of working in cybersecurity are as follows:
- Entry-level has prerequisites.
- Businesses don't understand cyber yet.
- Change is rapid and learning never stops.
- Cybercriminals don't take vacations.
- This career field requires serious passion.
- Mental burnout due to high cerebral work.
- Jack of all trades and master of none.
Let's explain each one.
Entry level has prerequisites
Unlike other positions, where you can start at an entry level with a basic degree and learn everything OJT (On the Job Training), that is not the case within cybersecurity. Even the entry-level SOC (Security Operations Center) analyst positions require a baseline understanding to triage data, research logs, and document reporting. Also, keep in mind this industry isn't the easiest to break into. You may have a college degree in computer science. Still, without hands-on experience, you could get passed up for someone who has no college but a couple certifications and 5-7 years of field experience.
Businesses don't understand cyber yet
Many organizations still think cyber is IT, there to fix their printer. Sometimes the older generation who don't understand the difference between cyber and IT. No thanks to the fantastic hacker TV shows making everyone think if you work in cyber you must be a hackers. Be patient because the change is slow. You must educate others on the difference between cyber and IT.
Change is rapid, and learning never stops
What can drain people in this field is the constant need to be reading and learning because cybercrime never stops. This can be challenging for someone who is initially entering the field in their mid to late 40s. Not only is it medically proven that learning at an older age can be more challenging, but you are learning a new skill while staying ahead of the rapidly changing threat-scape. The best advice here is to eat the cake one bite at a time. Anything is possible, but you must know this field isn't easy at first, but it does get easier.
Cybercriminals don't take vacation
Cybersecurity is rapidly changing. This is because cybercriminals are continuously evolving by updating malware variants and refining their Tactics, Techniques, and Procedures (TTPs), to circumvent security protocols and breach the network. Therefore, cybersecurity professionals are trying to stay one step ahead of the adversary. This is why SOC's run 24/7 and you may find yourself working long hours. We will discuss burnout shortly, but know, in this industry, there will always be work because the cybercriminals will always be attacking you.
This career field requires serious passion
This is a con and not a pro because you will dislike this industry if you do not have passion for your job. The passion drives your desire to learn and it's because of this passion and learning that you will thrive in this industry. If you find yourself in a job with no passion, I encourage you to identify whether this is due to your external environment or possibly the position. Sometimes the passion is lacking because we are not in the right role. We will discuss the different roles available in cybersecurity in Section 2, YOUR Path Into the Industry, of this book. Just know, passion is key to success in field. Without passion, you will be drained and not enjoy your work.
Mental burnout due to high cerebral work
Burnout in this industry is a real thing. Before entering this field, I didn't fully understood burnout. It took me about 4 months of working 80-90 hours a week with no break when I hit a wall and couldn't get out of bed for nearly 2 weeks. The reason, which I now know, was because I was mentally exhausted. I was putting so much strain on my cerebral cortex that my body finally broke down.
Depending on your specialty, you will hear about alert fatigue, which is when you review alerting or other data daily. When you feel like you are done and cannot look at any more data this is when you reach alert fatigue. This is when you stop and move into something else to give your mind a break. This is the same with education, too much education at one time can drain you.
Tip
Make sure to take regular breaks and give back to yourself. Micro breaks during the day are just as important as longer breaks like the weekend.
Jack of all trades and master of none
Within this field, it is easy to do a certification here and there and jump around from one position to another. This is great for learning about new jobs and seeing what fits your personality and character the best. However, it is recommended that eventually you should stay put long enough to become an SME (Subject Matter Expert) in your job. Make sure to take the time to develop 1-2 excellent skills. This could be a coding language, threat hunting, or pen testing. Then you can tie that skill into other aspects of your work. Most skills in this industry will overlap with one another. Don't think because you focus on one thing that if you move to another, you will never use it again.
Ultimately, this is your career and life. Make sure to do your own research and know the organizations before taking a job. Don't be afraid to move around and make changes if you're not happy. There are a lot of companies you can work for and a plethora of career directions you may take.
Summary
By the end of this chapter, you should have a basic understanding of what cybersecurity is and where it's going in the next few years. You should also have a good knowledge of cybersecurity law and why it's a challenging topic for congressional leaders to address.
We also covered foundational data of cybersecurity, which included primers such as the CIA Triad, NIST, ISO, and SOC frameworks. We provided you with a basic understanding of the most seen cyberattacks. The final section covered the advantages and disadvantages of this industry, with recommendations before entry into this industry.
Next up, Kim Nguyen will guide you through the next chapter, where you will learn about the different types of cyber careers. She dives into the cybersecurity roadmap, top prominent cybersecurity domains, and how to choose a career. Grab something to drink and settle in because things are warming up.
Questions
- What does the CIA in the CIA Triad mean?
- Name three cyber threats we discussed.
- What happened in 2016 that caused congress to enact the Consumer Privacy Protection Act of 2017?