Chapter 1: Introduction to Check Point Firewalls and Threat Prevention Products
In this chapter, we will learn about the past and the present of Check Point Software Technologies in the context of evolving cybersecurity challenges. We will become familiar with the three main product lines, their components, and their relevance to the threat prevention capabilities of Check Point firewalls. We will examine the flexibility and advantages of security management architecture, address the learning process, and go through the user and account creation process in preparation for the following chapters.
In this chapter, we are going to cover the following main topics:
- Learning about Check Point's history and the current state of the technology
- Understanding the Check Point product lineup and coverage
- Introducing the Unified Management concepts and the advantages of security product consolidation
- Familiarization with the Security Management Architecture (SMART)
- Determining how we learn
- Navigating the Check Point User Center
Technical requirements
For this chapter, we will need a web browser for access to the Check Point User Center and a smartphone running either iOS or Android, with an authentication manager application of your choice and a time-based, one-time password functionality, such as Google or Microsoft Authenticator, to enable second-factor authentication for access to the User Center.
Learning about Check Point's history and the current state of the technology
To get a sense of the product and the company behind it, it is good to have perspective. When were they founded? How long have they been in business? How consistent is their performance over time? What areas of cybersecurity is the company working in and how well are they rated? To find the answers to these questions, let's look at the past and the present of Check Point Software Technologies.
"In the beginning, there was FireWall-1"
In 1994, FireWall-1, released by Check Point Software Technologies, effectively launched the commercial firewall market and, according to Gartner, Check Point has been named a leader in the Network Firewalls category 21 times since.
The company received the following mention at the Cybersecurity Excellence Awards for 2016: "All of the US Fortune 100, and over 90% of the Fortune 500, rely on Check Point solutions to protect their networks and data." 1
Shortly after launching FireWall-1, Check Point released VPN-1 for remote access and secure connectivity with peers and, over the years, continued to introduce additional components, enhancements, and new products. Since then, the cybersecurity arena has become saturated with many entrants bringing new products to the market. Throughout all of this time, Check Point's expanding product line, and especially their evolving management interface, has been recognized as the gold standard against which all competitors are measured.
Check Point firewalls were originally created to run on multiple operating systems and hardware, hence the name of the company, Check Point Software Technologies.
This is an important distinction when compared with the offerings provided by other vendors that were creating their solutions based on specialized ASICs (Application-Specific Integrated Circuits). When cloud computing ushered in a new era in information technology, Check Point was able to immediately offer the same degree of protection to cloud-based environments as was previously available to traditional infrastructures. Since Check Point enterprise firewalls were running on x86/x64 platforms, they did not require porting or emulation to do that.
Check Point today
Check Point's products are now deployed in 88 countries and more than 100,000 businesses. It has offices in 75 countries, over 3,500 security experts, and a world-acclaimed research and intelligence organization2. Its firewall and threat prevention product line has offerings that cover an entire spectrum of clients; from small offices to enterprises, carrier networks, government agencies, and industrial control systems. They are available in the largest number of cloud services, including Amazon AWS, Microsoft Azure, Oracle Cloud, Google Cloud services, Alibaba Cloud, and IBM Cloud.
Check Point Software Technologies was recognized as a Microsoft Security 20/20 Partner Award Winner for Most Prolific Integration Partner in 2020, and for Most Transformative Integration Partner in 20213.
By protecting networks, hosts, data, workloads on hypervisors, containers, and microservices from advanced threats while using unified management architecture, Check Point remains at the forefront of cybersecurity. It has grown organically and, through judicious acquisitions and integration of complementary products over the years, and is now the largest publicly traded cybersecurity company in Israel, a nation known worldwide for its remarkably strong information security and intelligence capabilities.
With an unparalleled commitment to product evolution and quality, its ever-growing list of partners, dedicated support for automation, and orchestration for organizations adopting DevSecOps practices, it is the best choice for anyone looking to embark on their journey of becoming a member of the cyber defense elite.
Now that we've learned a little about the company's history, let's take a look at Check Point's product line.
Understanding the Check Point product lineup and coverage
The scope of Check Point offerings could be better understood when looking at the following chart depicting the three main branches of products:

Figure 1.1 – Check Point unified security architecture components
The Quantum branch is primarily concerned with hardware appliances, but it does include Check Point's own cloud-hosted scalable management solution (Quantum Smart-1 Cloud).
The small business appliances in the Quantum branch are running an embedded version of Check Point's firewall. They are different from the rest of the lineup in that category, but they, too, could be managed from the same centralized management solutions as the rest.
The CloudGuard branch, while primarily concerned with cloud-based solutions, includes those for the on-premises virtualization environments, such as VMware vSphere, Microsoft Hyper-V, and Nutanix. Additionally, the management servers deployed in the cloud as VMs are also considered to be part of the CloudGuard product line.
The Harmony branch contains solutions necessary to safeguard endpoints inside, as well as outside, of your organization (including BYOD and mobile devices) and to provide your users with multiple choices for secure remote connectivity.
Now that we have learned about the scope of Check Point products, let's take a look at the benefits of having a single vendor solution protecting your infrastructure and data.
Introducing the Unified Management concepts and the advantages of security product consolidation
Historically, security-conscious enterprises were practicing defense-in-depth by layering and combining multiple solutions in the hope of preventing systems and network compromise. While this approach was viable 10 years ago, it is getting progressively more difficult to maintain it.
Let's look at the evolution of the threats over time to get a better idea of why this is so by using the following diagram:

Figure 1.2 – Attack generations and types, escalation, and the response over time
In addition to the complexity and advances of the attacks, the numbers of bad actors, as well as the number of different attacks, are increasing exponentially. The field of offensive cybersecurity is attracting an ever-increasing number of people, not all of them ethical hackers. This contributes to the snowballing effect and the number of compromised systems, networks, and companies. The latest batch of attacks focusing on the supply chain is yet another manifestation of this trend.
The sheer number of cybersecurity vendors and point solutions, each trying to address different problem areas, makes it a virtual impossibility for smaller teams to manage them effectively. It takes years to gain proficiency with a single product, let alone multiple ones. Add to this the rapid development cycles of each vendor trying to keep up with evolving capabilities of cybercriminals and offerings by competition, and you will have to spend most of your time learning about new features and changes in all of these products, while at the same time fighting compatibility issues.
For a while, the combination of Security Information and Event Management (SIEM) solutions as hubs for the consolidation of logs, their correlation, and Security Orchestration Automation and Response (SOAR) actions based on pre-defined conditions looked like a possible solution to this problem. However, these options failed to address the multi-vendor cost of human capital, further complicating the operations of smaller security teams. They are now primarily relegated to larger enterprises, carrier networks, and Managed Security Services Providers (MSSPs) that can afford to keep staffed Security Operations Centers (SOCs) and dedicated data science and analytics specialists. For most other companies, SIEMs are either becoming log graveyards or are mostly used for after-the-fact investigations and audits, but not for proactive threat prevention.
Important Note
For the organizations that do utilize SIEMs, Check Point has out-of-the-box integration with ArcSight, LogRhythm, QRadar, RSA, McAfee, Splunk, and Sumologic, and its log exporter can be configured to work with any syslog-, CEF-, LEEF-, and JSON-compliant product. There is also a dedicated Check Point app for Splunk (https://sc1.checkpoint.com/documents/App_for_Splunk/html_frameset.htm) for seamless integration.
Serious advances in active prevention or response have also been made by several dedicated Endpoint Detection and Response (EDR) vendors. Unfortunately, the EDRs are relying on the installation of their agents on managed endpoints. Components of the infrastructure that do not have the agents remain unprotected.
All the networking gear, printers, copiers, conference room equipment, CCTV, building access and environmental controls, and other innumerable Internet of Things (IoT) devices are the shadow army that could be exploited and used for attacks or snooping on your infrastructure. The same applies to all devices on which the OS or firmware is controlled by the vendor or those that are supplied by service providers or business peers.
To compensate, EDR vendors are now actively expanding their integration with partners and going through the rapid acquisitions of complementary businesses to improve the coverage of their products.
Recognizing that the effective prevention of complex modern attacks requires more than just loosely coupled integration between various security tools, in 2017, Check Point developed and introduced its Infinity architecture. Tightly integrated products covering all aspects of security infrastructure with common management and enforcement policies dramatically improve detection and prevention rates.
Check Point was perfectly positioned to address these challenges since its ThreatCloud is one of the most established and largest commercial worldwide threat detection networks. The likelihood of Check Point encountering new attacks or variants of exploits closer to home is pretty good because of its huge global presence. The quality of the data is great since the product coverage extends from networks to endpoints, mobile, cloud, IoT, and industrial systems. Its analytics are supercharged by the ML and AI to identify malware DNA, a set of unique code segments and behavior characteristics that associates each newly encountered malware with a previously known malware family whenever such similarities can be identified. This helps to predict and prevent other, non-immediately apparent attack capabilities and vectors of emerging zero-day threats.
Having all these abilities provided by products from the same security vendor, as well as using common terminology, configuration, logging, analysis, management interfaces, and forensics capabilities, eliminates the complexity and the overhead of multiple point solutions. It also significantly improves your chances of deterrence and the containment of cyber attacks.
In January 2018, the MITRE Corporation released Adversarial Tactics, Techniques, and Common Knowledge version 1 (ATT&CK v1), a framework that validated Check Point's vision for unified security. And in the same month, Check Point announced Infinity Total Protection, a simple, all-inclusive, per-user, per-year subscription covering all of its products, including hardware, software, 24x7 premium support, and network security, as well as endpoint, mobile, cloud, and data security with real-time threat prevention.
Competitors realizing the advantages of this approach adopted similar strategies and a new term, Extended Detection and Response (XDR), was coined.
Important Note
Although it is unlikely that your organization is relying on a single vendor's solutions for all or even most of its cybersecurity needs, strategic consolidation resulting in massive benefits should be considered.
Most likely, Check Point firewalls in your environment are a part of the heterogeneous security infrastructure consisting of multiple point products. In this case, it is imperative to understand their roles, capabilities, and limitations in order to extract maximum value from the product while keeping track of what it is not designed or configured to do, and where complementary security solutions should be applied.
Network segmentation, network access control, threat prevention for individual network segments, categories, and hosts continue to remain some of the key elements of overall sound security posture. Having the benefit of threat intelligence generated by sensors present in all categories of information technology covered by the Infinity architecture makes Check Point firewalls some of the most effective threat prevention and detection tools in your cybersecurity arsenal.
Important Note
Check Point's mantra is prevention first, so it is often the case that engineers must, on purpose, disable prevention in the demo environments to showcase the product's detection capabilities at multiple points in the attack's kill chain.
Now that we know that vendor consolidation may yield better overall results by offering unified visibility of attacks, let's look at what the Security Management architecture can do for the administration of the Check Point infrastructure.
Familiarization with the Security Management Architecture (SMART)
Check Point's Security Management architecture is the foundational principle behind the centralized administration of multiple products and devices using common management interface(s).
Smart in the name of Check Point products dates back to when it was used as the acronym for Security Management Architecture. It is now present in the name of management servers and services, as well as Smart-1 products and their components: SmartLog and SmartEvent, Check Point's GUI, and the SmartConsole. There is also a migration tool for transition from competing solutions called SmartMove. In a nutshell, SMART could be described as a collection of the administrative stations, management, log, monitoring, and analytics servers that manage a variety of the gateways, endpoints, cloud-based inspection, and threat prevention products designed to seamlessly work together. It is practically infinitely scalable.
The following is a simple diagram depicting a basic implementation of the Check Point gateway and management infrastructure and their components:

Figure 1.3 – Basic components of Check Point's management architecture
Important Note
Although we commonly refer to it as a firewall, a correct definition would be gateway, where a firewall is just one of the components.
SmartConsole is the Windows-based management client application that is connected to all of your management servers, regardless of the components they are running. It will be your primary interface for managing the Check Point infrastructure.
In the context of network architecture, a basic implementation could look as simple as the following:

Figure 1.4 – All-in-one implementation. Management and gateway on a single device
In Figure 1.4, a single all-in-one device is acting as both a management server and a gateway. This is appropriate for the smallest environments that are aspiring to have world-class protection, but either lack the budget or justification to implement a distributed Check Point environment. It is also appropriate for small-scale labs where you may explore new release features and functionality.
In a slightly more demanding environment, which I would recommend as a good starting point, the management server running all of its constituent components resides on a separate appliance or a virtual machine. In this case, the gateway is running on a dedicated appliance as follows:

Figure 1.5 – Basic implementation with a dedicated management server
The advantage of this approach is the ability to manage many gateways from a common management server using a common object database.
Important Note
The functionality of the gateway is not dependent on the availability of the management server: even if it is down for maintenance or is being upgraded, the gateways continue to function and are logging locally. Once the management server comes back online, the logs are being automatically ingested by the management server.
Scaled further, SmartEvent is split from the management and log server to provide dedicated log correlation and reporting, as follows:

Figure 1.6 – SmartEvent log correlation and reporting on a dedicated server
This is a typical precursor for the expansion to either a multi-site or a hybrid environment, where a common SmartEvent server is used for log correlation, reporting, and analytics with multiple management and log servers. Since SmartEvent cannot be part of high-availability management, it should reside on a separate appliance or virtual machine. This is also one of the ways to offload your existing management server appliance if its utilization is consistently high.
And in a more typical data center environment, high-availability management and site-specific log servers are implemented to manage a larger number of gateways and clusters, as illustrated in the following diagram:

Figure 1.7 – Management high availability with dedicated log servers for multi-site environments
When your gateways and clusters under management generate a massive number of logs, it may be necessary to provide adequately sized log servers for each logically grouped location (typically based on geography or a specific data center).
The environment shown in Figure 1.7 allows you to ensure that the management servers used to create, manage, and install security policies in your environment will perform consistently, irrespective of the load on log servers.
Scaled even further, it may look like this:
Multiple SmartConsoles and API clients multi-domain management servers/security management servers multiple enterprise environments comprised of gateways, clusters, scalable platforms, hyperscale solutions, and/or endpoints logging to dedicated log servers with monitoring and analytics provided by SmartEvent servers and forwarding logs to an SIEM of your choice
The more complex and expansive your infrastructure, the more granular implementation of Check Point management you may require to assure the necessary performance and redundancy.
Another option that should be specifically mentioned here is Quantum Smart-1 Cloud, a cloud-based management environment that is redundant and scalable on demand to accommodate your enterprise. Check Point takes care of the maintenance updates, upgrades, and high availability in the background, while you are simply administering your infrastructure from it. We will revisit management options in a later chapter to compare the advantages of different choices for specific circumstances.
As you go through this book, you will acquire valuable foundational knowledge equally applicable to all of the implementations described previously.
We now understand that the Security Management architecture allows you to grow your company and maintain the same level of protection, regardless of its scale or model. Before we go all technical, let's look at learning approaches, available options, and the reasoning behind this book's format.
Determining how we learn
There is a widely adopted learning and retention concept representation known as either the learning pyramid or the cone of experience. This is depicted in the following diagram:

Figure 1.8 – Learning and retention4
Not everyone agrees with the exact quantification of the results, but there is no denying that the more of these activities and mediums of learning you are exposed to, the better the outcome.
The comprehension of concepts from reading the material varies depending on how well it is written. If the book or guide is well illustrated, it makes it easier to tie the concepts to real-world applications. Watching someone doing it in a video affirms the validity of the printed or static material. When you are working on a subject in your own lab environment, your confidence in being able to reproduce the results and your level of comfort with expanding your knowledge of the subject grow even further.
Follow the instructions in the book and its complementary online materials to get the most out of it. Choose your own names, emails, and fictional or real company names for registration on portals and access to the products we will be using in the lab.
Some of you may not have the necessary computing capabilities at your disposal to replicate the lab. For them, and those who may be reading this book during your commute, the included screenshots should provide a close approximation of the experience.
We now understand the learning methodologies that impact our comprehension and retention. In the next section, we will familiarize ourselves with the Check Point User Center and configure credentials required for access to resources used in the labs.
Navigating the Check Point User Center
The Check Point User Center is the portal for access to a variety of resources, and the place where you will create or manage your Check Point accounts, users, and products. It is also a place where you generate and download licenses and support contracts.
It is accessible at https://usercenter.checkpoint.com.
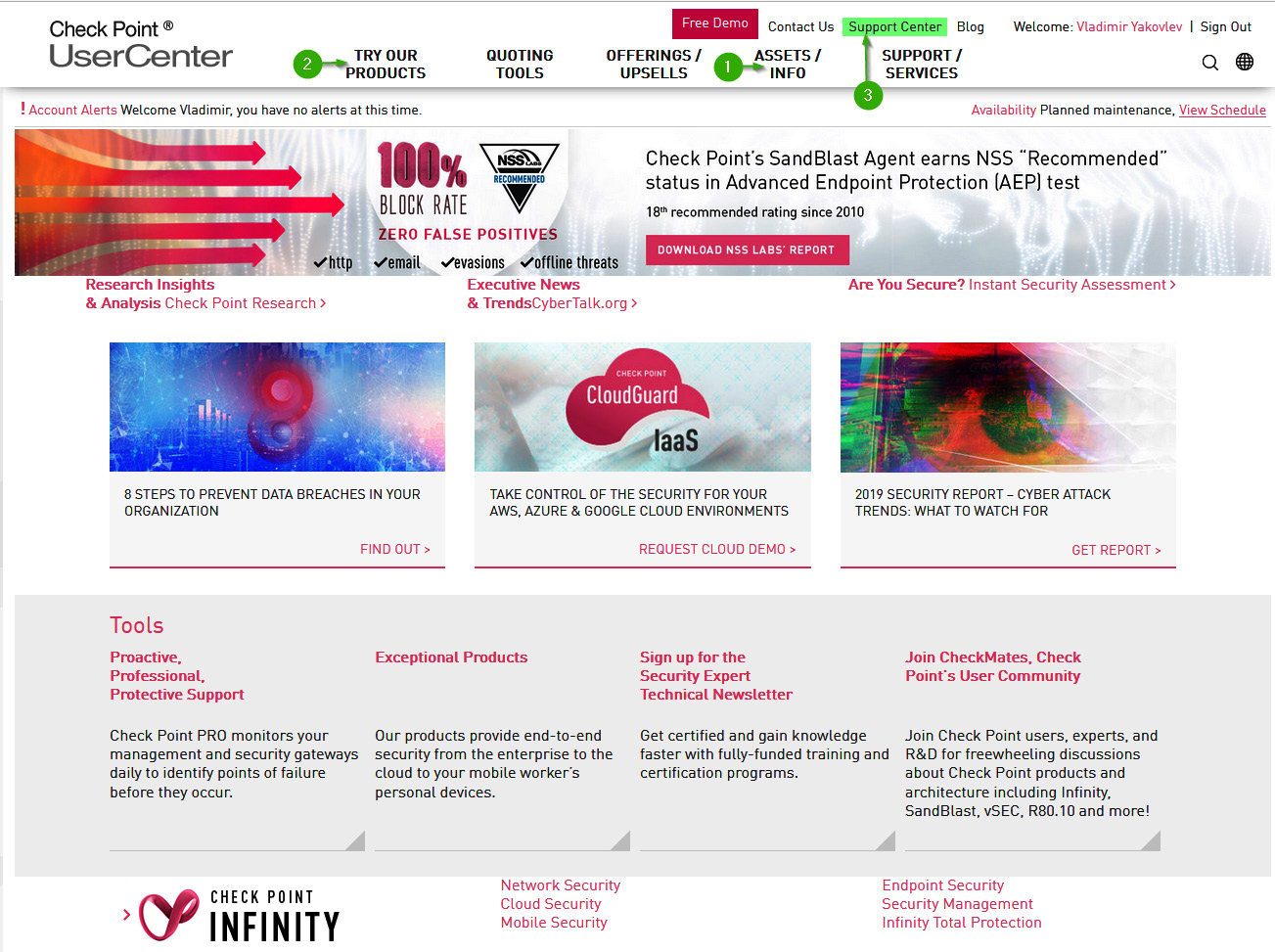
Figure 1.9 – User Center
We will be using the ASSETS/INFO and TRY OUR PRODUCTS sections to obtain and maintain our lab licenses as we go through the book.
From the User Center, you can get to Support Center, a place where you can open and manage Service Requests (SRs), report security issues, subscribe to or access the PRO Support portal (a proactive monitoring and reporting service), and gain access to the technical documentation, alerts, subscriptions, product downloads, and search capabilities across SecureKnowledge articles, downloads, documentation, and CheckMates community posts and discussion threads.
The following screenshot shows Support Center:
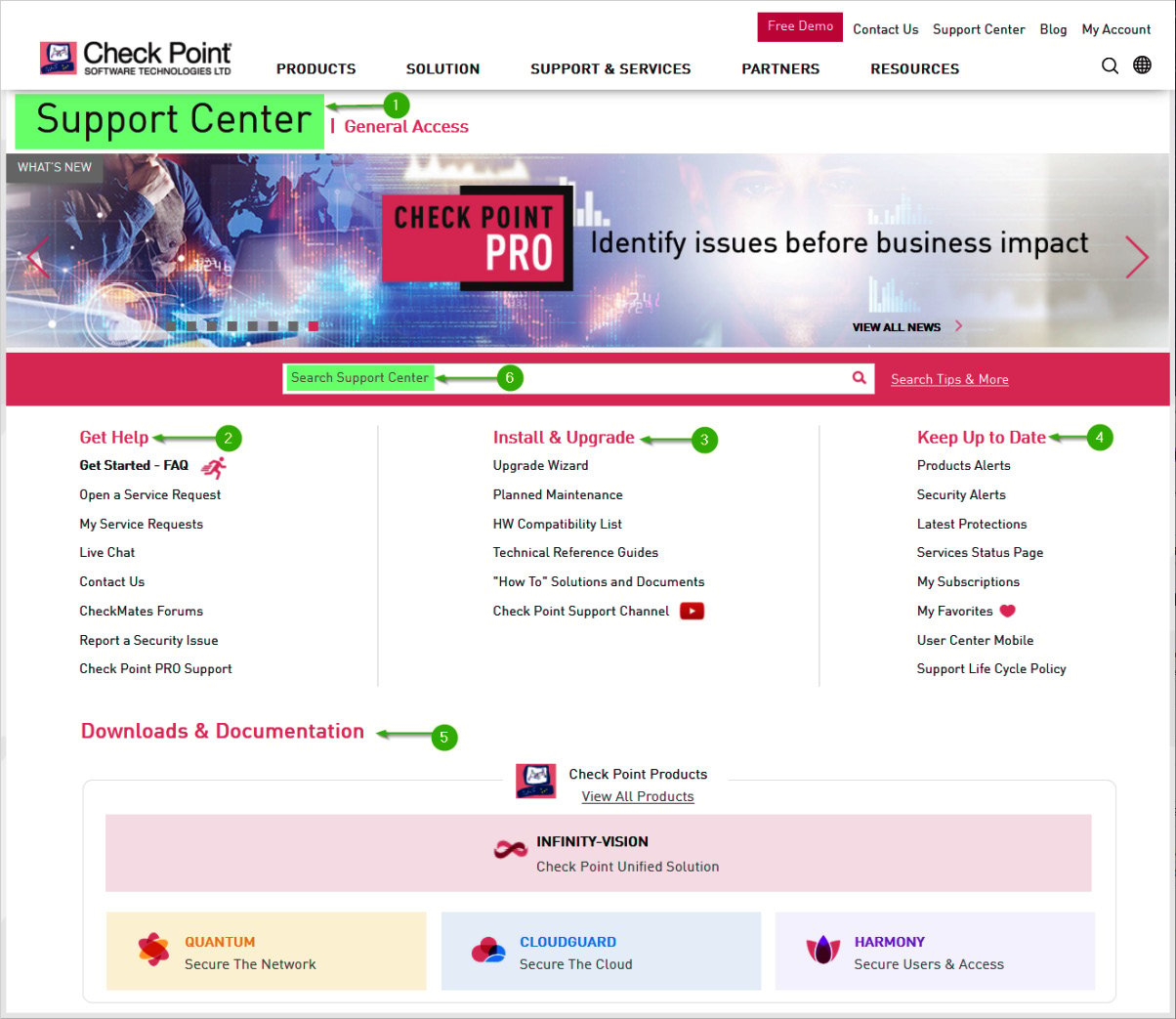
Figure 1.10 – Support portal
Both portals are interlinked, but if you know what you need, it is simpler to get to the right place through a corresponding link.
The Support Center may be accessed at https://supportcenter.checkpoint.com.
Important Note
While it is not necessary to register with Check Point in order to download and try their firewall product, this trial will be limited to 15 days. To extend it beyond the initial 15 days, you will have to go through the registration process to request a trial or lab license(s).
Since we must learn how to register and manage users and accounts and how to license the product, we will now start with the registration process.
Follow these steps to register as a portal user and create an account:
- In your browser, go to https://usercenter.checkpoint.com.
- When prompted with the Sign In screen, click on Sign Up Now.
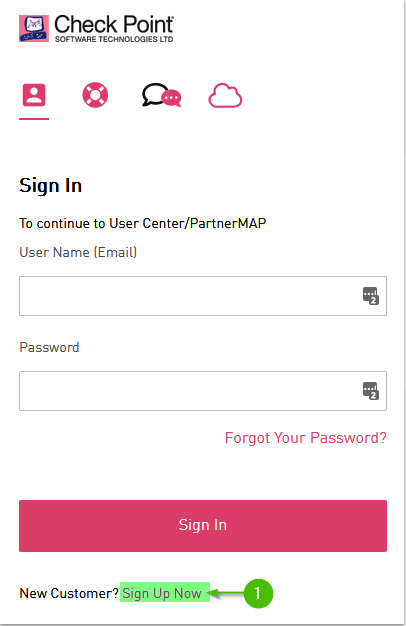
Figure 1.11 – Sign Up Now
Populate the fields with your information and then click Submit.
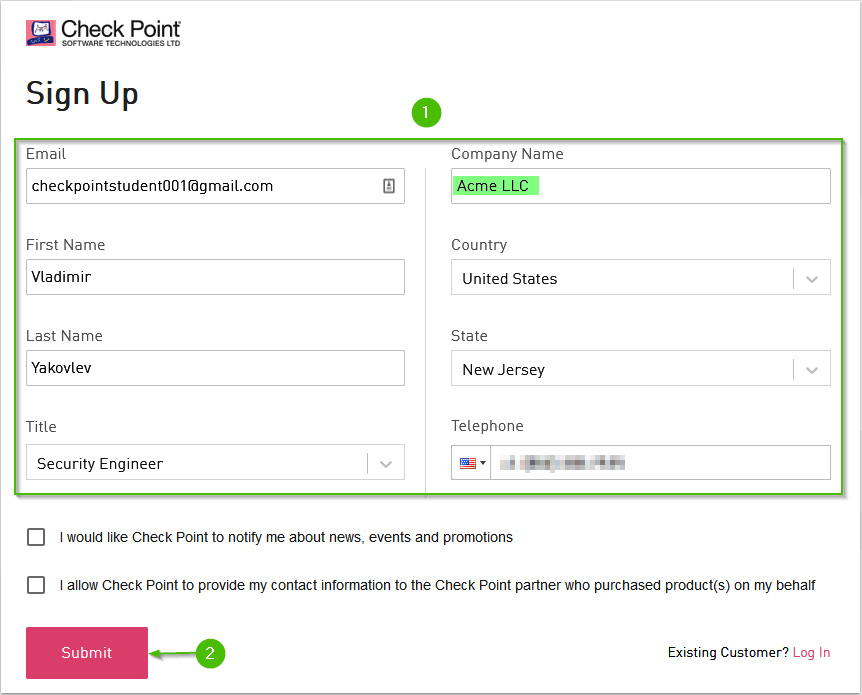
Figure 1.12 – Sign Up; user information
- The Success! popup will appear; check your mailbox to continue.
- Click on Confirm Email in the body of the message.
- Create and confirm a suitably strong password using a combination of uppercase and lowercase letters, numbers, and symbols and then click Submit.
- Click Sign In.
- Enter your username (the same as the email in step 2 and the password from step 5) and then click Sign In.
- Once you are logged in for the first time, click on your username in the top-right portion of the screen and then click on the Security shield icon on the left to configure the Multifactor Authentication (MFA).
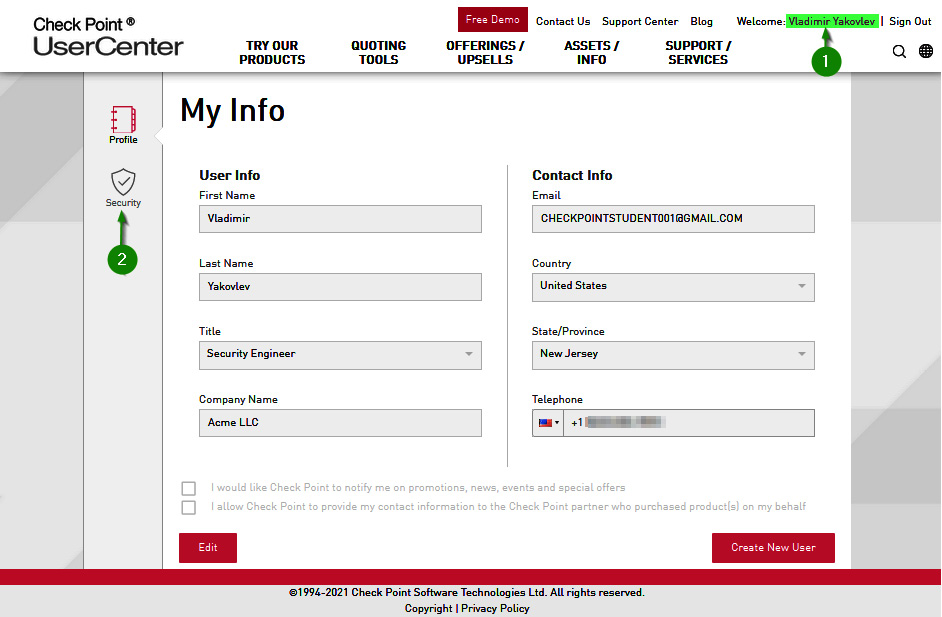
Figure 1.13 – Securing User Center access
- Toggle the 2-Step Verification switch to the On position:
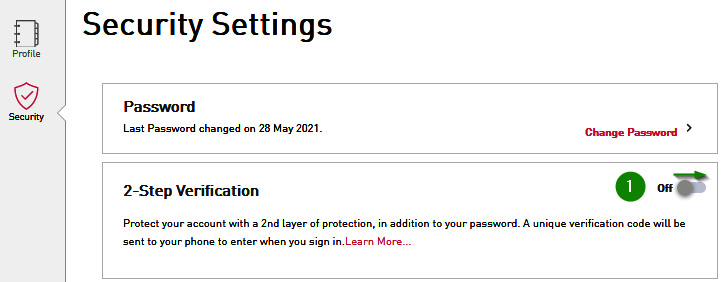
Figure 1.14 – Turning on 2-Step Verification
- Enter your mobile phone number, verify that the Text Message option is selected, and then click Verify Phone.
- Enter the code received via text message and then click Activate.
- Your phone number is now shown as Verified. Click on the Display Backup codes arrow.
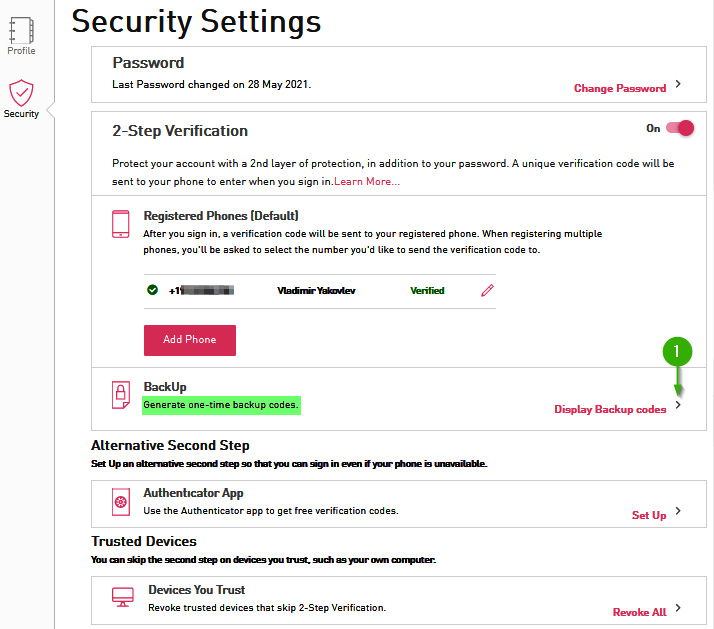
Figure 1.15 – Backup codes for 2FA
- Click on Generate New Backup codes. When backup codes are displayed, click Print. If you do not have a printer connected, print codes to PDF. Click Close.
- In the Authenticator App section, click the arrow to the right of Set Up.
- Choose your mobile phone platform and then click Next.
- If you do not have an authentication application on your phone, install either Microsoft Authenticator or Google Authenticator or your preferred MFA application. When installed, or if already available, add the new account to it by scanning the QR code and then click Next.
- If the scan fails (observed on very high-resolution monitors with particular brightness and contrast), click on CAN'T SCAN IT?, manually enter the key into the authentication manager, and then click Next.
- Enter the dynamically generated one-time code and click Next. Note the time remaining for the action on your phone while doing it.
- The authentication app now becomes the default method for the second factor. Let's look at the following screenshot:
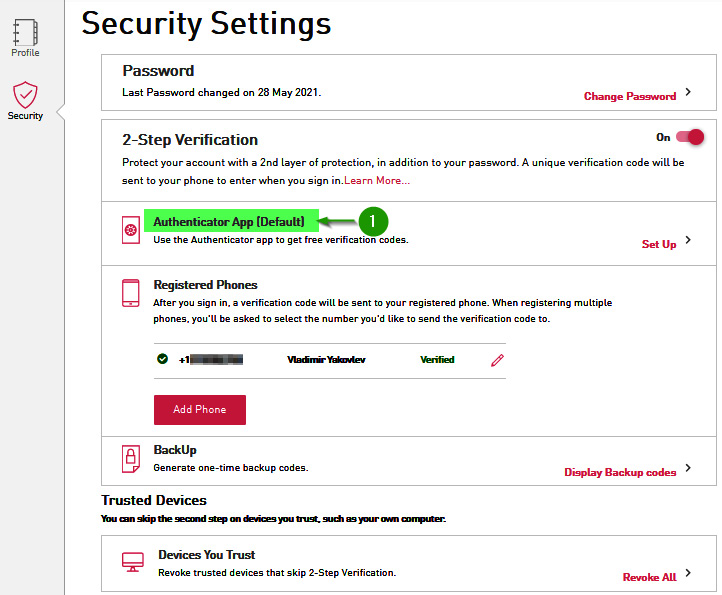
Figure 1.16 – Authentication app as the default 2FA
We can now securely log on to the User Center and access its resources.
Summary
In this chapter, we learned about the history and the present-day state of the technology and services offered by Check Point. We saw the flexibility and scalability of the Secure Management architecture and learned about the advantages of consolidated security solutions, and why they are emerging as the preferred choice for addressing today's complex threat environments. We have also created and secured our User Center account.
Now that we understand the modular nature of Check Point management architecture, we are ready to look at firewall locations within common network topologies and talk about the significance of their placement.
In the following chapter, we will address where and when certain features are better employed for different outcomes. We will learn how to determine the utilization of your currently deployed firewalls and calculate the capacity for new ones.
Further reading
- https://cybersecurity-excellence-awards.com/candidates/check-point-software-technologies/
- https://www.checkpoint.com/about-us/company-overview/
- https://www.microsoft.com/security/blog/2021/03/11/finalists-announced-in-second-annual-microsoft-security-20-20-awards/
- https://en.wikipedia.org/wiki/Edgar_Dale



















 Download code from GitHub
Download code from GitHub
