Chapter 1: Introduction to the Security Landscape
This chapter provides an overview of our connected world. Specifically, it looks at how cybercriminals in the cyber landscape are becoming more sophisticated and dangerous. It looks at how they abuse the worldwide connectivity between people and technology. In recent years, the damage from cyberattacks has become increasingly destructive and the majority of the population actually thinks that antivirus software will protect them from all kinds of cyber threats. Of course, this is not true and there are always security aspects that need to be dealt with in order to improve antivirus software's overall security and detections.
Many people and organizations believe that if they have antivirus software installed on their endpoints, they are totally protected. However, in this book, we will demonstrate – based on our original research of several antivirus products – why this is not completely true. In this book, we will describe the types of antivirus engines on the market, explore how antivirus software deals with threats, demonstrate the ways in which antivirus software can be bypassed, and much more.
In this chapter, we will explore the following topics:
- Defining malware and its types
- Exploring protection systems
- Antivirus – the basics
- Antivirus bypass in a nutshell
Understanding the security landscape
In recent years, the internet has become our main way to transfer ideas and data. In fact, almost every home in the developed world has a computer and an internet connection.
The current reality is that most of our lives are digital. For example, we use the web for the following:
- Shopping online
- Paying taxes online
- Using smart, internet-connected televisions
- Having internet-connected CCTV cameras surrounding our homes and businesses.
- Social media networks and website that we are using in a daily basis to share information with each other.
This means that anyone can find the most sensitive information, on any regular person, on their personal computer and smartphone.
This digital transformation, from the physical world to the virtual one, has also unfolded in the world of crime. Criminal acts in cyberspace are growing exponentially every year, whether through cyberattacks, malware attacks, or both.
Cybercriminals have several goals, such as the following:
- Theft of credit card data
- Theft of PayPal and banking data
- Information gathering on a target with the goal of later selling the data
- Business information gathering
Of course, when the main goal is money, there's a powerful motivation to steal and collect sellable information.
To deal with such threats and protect users, information security vendors around the world have developed a range of security solutions for homes and enterprises: Network Access Control (NAC), Intrusion Detection Systems (IDS)/Intrusion Prevention Systems (IPS), firewalls, Data Leak Prevention (DLP), Endpoint Detection and Response (EDR), antiviruses, and more.
But despite the wide variety of products available, the simplest solution for PCs and other endpoints is antivirus software. This explains why it has become by far the most popular product in the field. Most PC vendors, for example, offer antivirus licenses bundled with a computer purchase, in the hope that the product will succeed in protecting users from cyberattacks and malware.
The research presented in this book is based on several types of malicious software that we wrote ourselves in order to demonstrate the variety of bypass techniques. Later in this book, we will explore details of the malware we created, along with other known and publicly available resources, to simplify the processes of the bypass techniques we used.
Now that we have understood why organizations and individuals use antivirus software, let's delve into the malware types, malicious actors, and more.
Defining malware
Malware is a portmanteau of malicious software. It refers to code, a payload, or a file whose purpose is to infiltrate and cause damage to the endpoint in a few different ways, such as the following:
- Receive complete access to the endpoint
- Steal sensitive information such as passwords and the like
- Encrypt files and demand a ransom
- Ruin the user experience
- Perform user tracking and sell the information
- Show ads to the user
- Attack third-party endpoints in a botnet attack
Over the years, many companies have developed antivirus software that aims to combat all types of malware threats, which have multiplied over the years, with the potential for harm also growing every single day.
Types of malware
To understand how to bypass antivirus software, it's best to map out the different kinds of malware out there. This helps us get into the heads of the people writing antivirus signatures and other engines. It will help us recognize what they're looking for, and when they find a malicious file, to understand how they classify the malware file:
- Virus: A malware type that replicates itself in the system.
- Worm: A type of malware whose purpose is to spread throughout a network and infect endpoints connected to that network in order to carry out some future malicious action. A worm can be integrated as a component of various types of malware.
- Rootkit: A type of malware that is found in lower levels of the operating system that tend to be highly privileged. Many times, its purpose is to hide other malicious files.
- Downloader: A type of malware whose function is to download and run from the internet some other malicious file whose purpose is to harm the user.
- Ransomware: A type of malware whose purpose is to encrypt the endpoint and demand financial ransom from the user before they can access their files.
- Botnet: Botnet malware causes the user to be a small part of a large network of infected computers. Botnet victims receive the same commands simultaneously from the attacker's server and may even be part of some future attack.
- Backdoor: A type of malware whose purpose is – as the name suggests – to leave open a "back door", providing the attacker with ongoing access to the user's endpoint.
- PUP: An acronym that stands for potentially unwanted program, a name that includes malware whose purpose is to present undesirable content to the user, for instance, ads.
- Dropper: A type of malware whose purpose is to "drop" a component of itself into the hard drive.
- Scareware: A type of malware that presents false data about the endpoint it is installed on, so as to frighten the user into performing actions that could be malicious, such as installing fake antivirus software or even paying money for it.
- Trojan: A type of malware that performs as if it were a legitimate, innocent application within the operating system (for example, antivirus, free games, or Windows/Office activation) and contains malicious functionality.
- Spyware: A type of malware whose purpose is to spy on the user and steal their information to sell it for financial gain.
Important Note
Malware variants and families are classified based not only on the main purpose or goal of the malware but also on its capabilities. For example, the WannaCry ransomware is classified as such because its main goal is to encrypt the victim's files and demand ransom, but WannaCry is also considered and classified as Trojan malware, as it impersonates a legitimate disk partition utility, and is also classified and detected as a worm because of its ability to laterally move and infect other computers in the network by exploiting the notorious EternalBlue SMB vulnerability.
Now that we have understood malware and its varieties, we should take a look at the systems created to guard against these intrusions.
Exploring protection systems
Antivirus software is the most basic type of protection system used to defend endpoints against malware. But besides antivirus software (which we will explore in the Antivirus – the basics section), there are many other types of products to protect a home and business user from these threats, both at the endpoint and network levels, including the following:
- EDR: The purpose of EDR systems is to protect the business user from malware attacks through real-time response to any type of event defined as malicious.
For example, a security engineer from a particular company can define within the company's EDR that if a file attempts to perform a change to the
SQLServer.exeprocess, it will send an alert to the EDR's dashboard. - Firewall: A system for monitoring, blocking, and identification of network-based threats, based on a pre-defined policy.
- IDS/IPS: IDS and IPS provide network-level security, based on generic signatures, which inspects network packets and searches for malicious patterns or malicious flow.
- DLP: DLP's sole purpose is to stop and report on sensitive data exfiltrated from the organization, whether on portable media (thumb drive/disk on key), email, uploading to a file server, or more.
Now that we have understood which security solutions exist and their purpose in securing organizations and individuals, we will understand the fundamentals of antivirus software and the benefits of antivirus research bypass.
Antivirus – the basics
Antivirus software is intended to detect and prevent the spread of malicious files and processes within the operating system, thus protecting the endpoint from running them.
Over time, antivirus engines have improved and become smarter and more sophisticated; however, the foundation is identical in most products.
The majority of antivirus products today are based on just a few engines, with each engine having a different goal, as follows:
- Static engine
- Dynamic engine (includes the sandbox engine)
- Heuristic engine
- Unpacking engine
Of course, most of these engines have their own drawbacks. For example, the drawback of a static engine is that it is extremely basic, as its name implies. Its goal is to identify threats using static signatures, for instance, the YARA signature (YARA, Welcome to YARA's documentation, https://yara.readthedocs.io/en/stable/). These signatures are written from time to time and updated by antivirus security analysts on an almost daily basis.
During a scan, the static engine of the antivirus software conducts comparisons of existing files within the operating system to a database of signatures, and in this way can identify malware. However, in practice, it is impossible to identify all malware that exists using static signatures because any change to a particular malware file may bypass a particular static signature, and perhaps even completely bypass the static engine.
The following diagram demonstrates the static engine scanning flow:
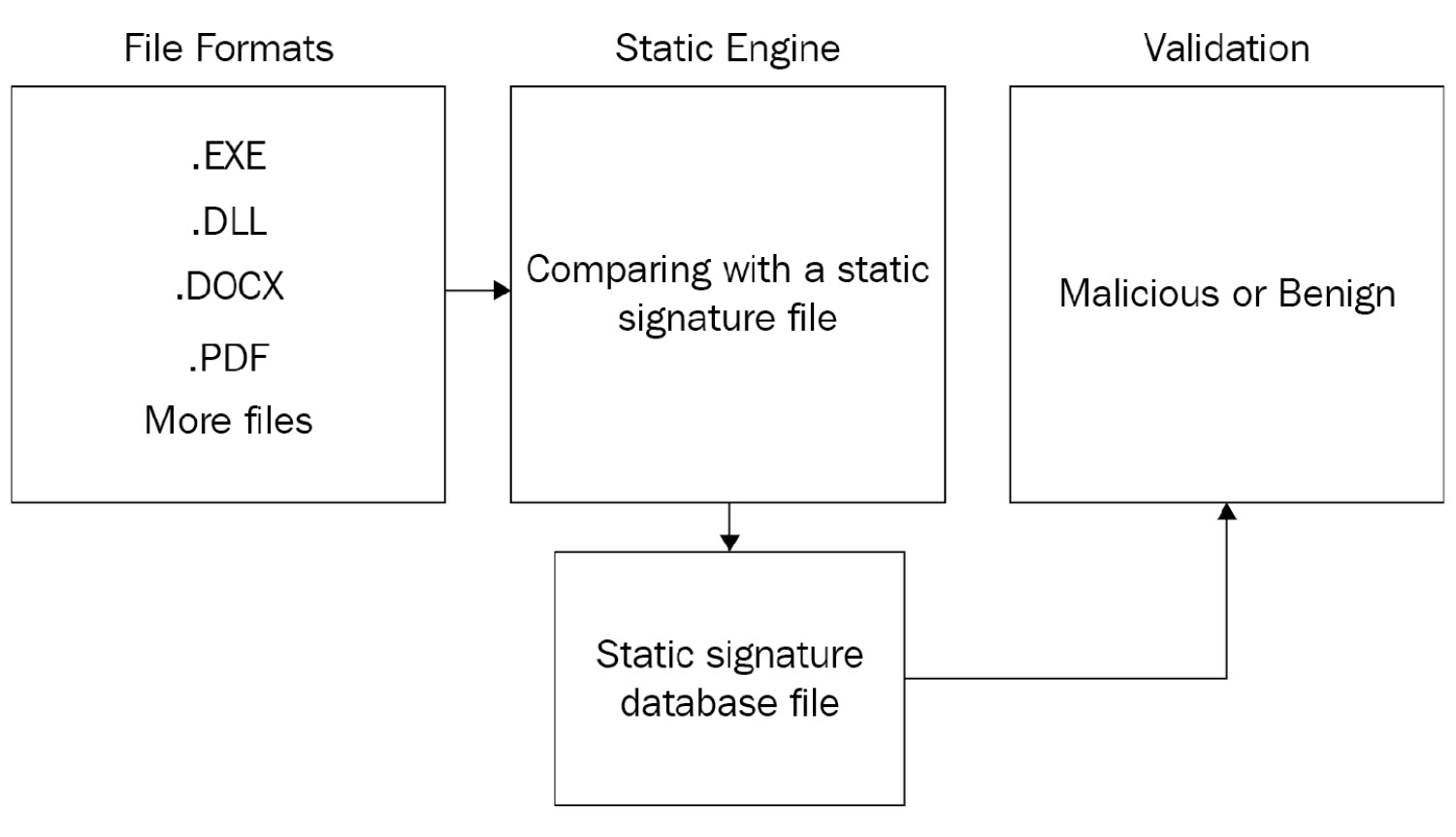
Figure 1.1 – Antivirus static engine illustration
Using a dynamic engine, antivirus software becomes a little more advanced. This type of engine can detect malware dynamically (when the malware is executed in the system).
The dynamic engine is a little more advanced than the static engine, and its role is to check the file at runtime, through several methods.
The first method is API monitoring – the goal of API monitoring is to intercept API calls in the operating system and to detect the malicious ones. The API monitoring is done by system hooks.
The second method is sandboxing. A sandbox is a virtual environment that is separated from the memory of the physical host computer. This allows the detection and analysis of malicious software by executing it within a virtual environment, and not directly on the memory of the physical computer itself.
Running malware inside a sandboxed environment will be effective against it especially when not signed and detected by the static engine of the antivirus software.
One of the big drawbacks of such a sandbox engine is that malware is executed only for a limited time. Security researchers and threat actors can learn what period of time the malware is executing in a sandbox for, suspend the malicious activity for this limited period of time, and only then run its designated malicious functionality.
The following diagram demonstrates the dynamic engine scanning flow:
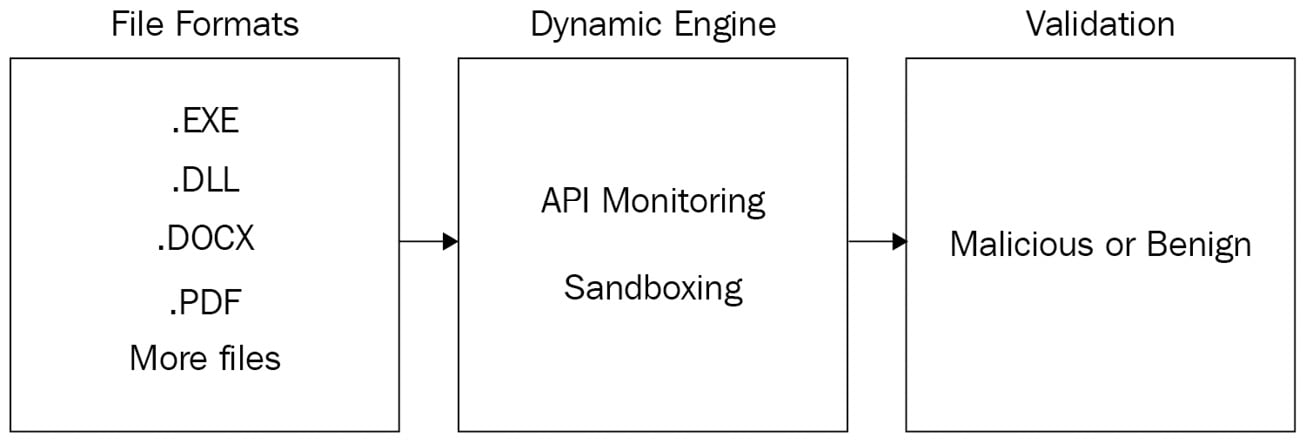
Figure 1.2 – Antivirus dynamic engine illustration
Using a heuristic engine, antivirus software becomes even more advanced. This type of engine determines a score for each file by conducting a statistical analysis that combines the static and dynamic engine methodologies.
Heuristic-based detection is a method, that based on pre-defined behavioral rules, can detect potentially malicious behavior of running processes. Examples of such rules can be the following:
- If a process tries to interact with the
LSASS.exeprocess that contains users' NTLM hashes, Kerberos tickets, and more - If a process that is not signed by a reputable vendor tries to write itself into a persistent location
- If a process opens a listening port and waits to receive commands from a Command and Control (C2) server
The main drawback of the heuristic engine is that it can lead to a large number of false positive detections, and through several simple tests using trial and error, it is also possible to learn how the engine works and bypass it.
The following diagram demonstrates the heuristic engine scanning flow:
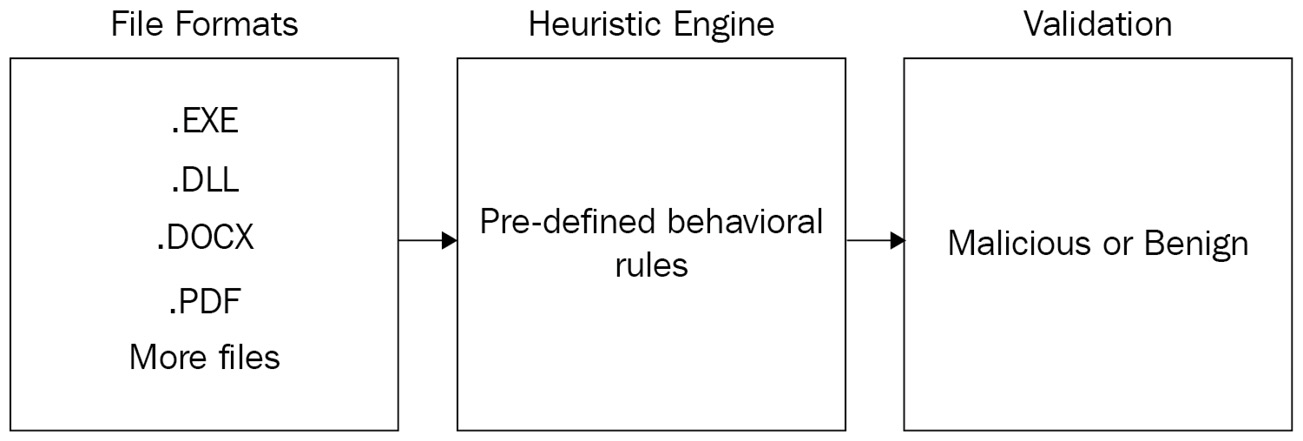
Figure 1.3 – Antivirus heuristic engine illustration
Another type of engine that is widely used by antivirus software is called the unpacker engine. In Chapter 5, Bypassing the Static Engine, we will discuss what a packer is, how the unpacking process works, and how to bypass antivirus software using packing.
One of the major drawbacks of today's advanced antivirus software centers on their use of unpackers, tools used by antivirus engines to reveal malicious software payloads that have undergone "packing," or compression, to hide a malicious pattern and thus thwart signature-based detection.
The problem is that there are lots of packers today that antivirus software does not have unpackers for. In order to create automated unpacker software, security researchers from the antivirus software vendor must first perform manual unpacking – and only then can they create an automated process to unpack it and add it to one of their antivirus engines.
Now that we understand the basic engines that exist in almost every antivirus software, we can move on to recognize practical ways to bypass them to ultimately reach the point where we are running malware that lets us remotely control the endpoint even while the antivirus software is up and running.
Antivirus bypass in a nutshell
In order to prove the central claim of this book, that antivirus software cannot protect the user completely, we decided to conduct research. Our research is practically tested based on our written and compiled EXE files containing code that actually performs the techniques we will explain later on, along with payloads that perform the bypass. The goal of this research wasn't just to obtain a shell on the endpoint, but rather to actually control it, transmit remote commands, download files from the internet, steal information, initiate processes, and many more actions – all without any alert from the antivirus software.
It is important to realize that just because we were able to bypass a particular antivirus software, that does not mean that it is not good software or that we are recommending against it. The environment in which the antivirus software was tested is a LAN environment and it is entirely possible that in a WAN environment, the result might have been different.
The communication between the malware and the C2 server was done using the TCP protocol in two ways:
- Reverse shell
- Bind shell
The difference between these two methods lies in how communication is transmitted from the malware to the attacker's C2 server. Using the method of the bind shell, the malware acts as a server on the victim endpoint, listening on a fixed port or even several ports. The attacker can interact with the endpoint using these listening port(s) at any time the malware is running.
Using the reverse shell method, the listening fixed port will be open on the attacker's C2 server and the malware acts as a client, which in turn will connect to the attacker's C2 server using a random source port that is opened on the victim endpoint.
The following diagram demonstrates the differences between reverse and bind shell:
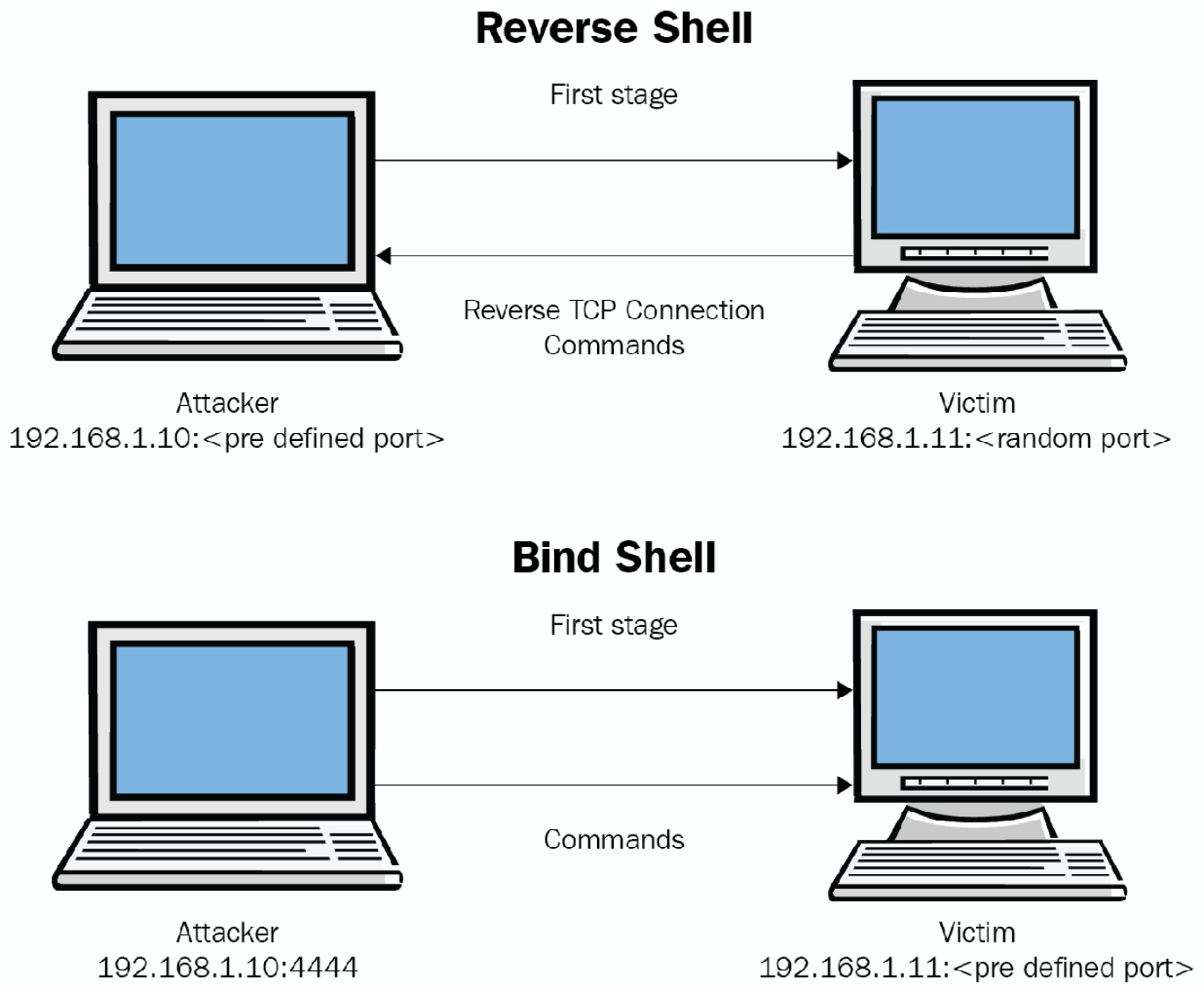
Figure 1.4 – Reverse shell and bind shell
Most of the time, threat actors will prefer to base their malicious payload to interact with their C2 servers on the reverse shell technique. This is because it is relatively easy to implement; it will work behind Network Address Translation (NAT) and it will probably have the chance to fool antivirus software and firewall solutions.
Summary
In today's world, antivirus software is an integral part of security for endpoints including computers and servers, ranging from ordinary users to the largest organizations.
Most companies depend on antivirus software as a first or even last line of defense against cyber threats. Because of this, we decided to research antivirus software, find vulnerabilities in their engines, and most importantly, discover ways to bypass them to prove that they simply do not provide a completely bulletproof solution.
To conduct antivirus bypass research, it is crucial to understand the cybersecurity landscape. Every day, new risks and threats for home and business users emerge. It is important to get familiar with security solutions that provide better cybersecurity. Additionally, it's important, of course, to understand the basic solution, the antivirus, and to understand its inner workings and fundamentals to conduct better antivirus research. This helps both users and organizations evaluate whether their antivirus software provides the expected level of security.
In the next chapter, you will learn about the fundamentals and the usage of various tools that will help in conducting antivirus research lead gathering that will eventually influence the next levels of antivirus bypass research.