Introduction to Advanced Infrastructure Penetration Testing
Security is a critical concern for enterprises and organizations of all sizes, in all industries. Information security is a set of processes, tools, policies, and systems implemented to protect against internal and external threats that can damage or disrupt information assets. This book is hands-on and designed to take you through real-world techniques so that you can gain the required and highly demanded skills that will enable you to step into a new level of penetration testing career. Every chapter is designed, not only for you to learn the methodologies, tools, and techniques to simulate hacking attacks, but also so that you will also come away with a new mindset. In this chapter, you will be introduced to the latest penetration testing strategies and techniques. It will take you through every required step in detail to carry out efficient penetration testing and furthermore, to be able to evaluate a pentesting report, based on industry-accepted metrics. Once you have completed the chapter, you will have the skills to deliver a high-standard and well-documented penetration testing report, after practicing the techniques to gather information on any target, even in the deep web, and move beyond automated tools.
Information security overview
Before diving into penetration testing, let's start by discovering some important terminology in information security. The core principles of information security are confidentiality, availability, and integrity. These principles institute what we call the CIA triad.
Confidentiality
Confidentiality asserts that all the information and data are accessible only by persons who are authorized to have access. It is important to make sure that the information won't be disclosed by unauthorized parties. The theft of Personal Identifiable Information (PII) is an example of a confidentiality attack.
Integrity
The aim of integrity is to protect information against unauthorized modification; in other words, the trustworthiness of data. This means that data has to be consistent, accurate, and trustworthy during every single information process. Some protection methods must be in place and available to detect any changes in data.
Availability
Availability seeks to ensure that the information is available by authorized users when it is needed. Denial of Service (DoS) is an example of an availability attack. High-availability clusters and backup copies are some of the mitigation systems used against availability attacks.
Least privilege and need to know
Least privilege and need to know describes the fact that authorized users should be granted the minimum amount of access and authorization during their jobs. Need to know means that the user must have a legitimate reason to access information.
Defense in depth
Defense in depth, or layered security, is a security approach using multilayer security lines, and controls an example of a defense in depth approach using multiple firewalls from different vendors to improve the security of the systems.
Risk analysis
The main role of an information security professional is to evaluate risks against enterprise assets (resources that need protection) and implement security controls to defend against those risks. Analyzing risks is a very important skill because good judgment will make us select the best security controls and protection mechanisms, including the amount of financial resources needed for the deployment of these safeguards. In other words, a bad decision will cost the enterprise a huge amount of money and even worse, the loss of customers' data. We can't calculate the risk in a quantitative way without knowing the threats and vulnerabilities. A threat is a potential danger to our assets that could harm the systems. A vulnerability is a weakness that allows the threat to take negative actions. These two terms and the connection between them is described by the formula Risk = Threat*Vulnerability.
To evaluate the threat and the vulnerability, you need to assign a number in a range of one to five, for example. Using another range is possible. Sometimes, we can add another factor named impact, which describes the impact of the damage caused. In other cases, it is expressed as an amount of money to describe the cost of that impact, so the formula could be expressed as Risk = Threat*Vulnerability*Impact.
The information security professional needs to classify risks based on two metrics: the frequency of occurrence and the severity of accident. The results of this classification will dictate the next action plan. Thus, if the risks are high, they must notify senior management. The next step is to create a roadmap to downgrade every risk to low, as much as possible, as shown here:

Information Assurance
Information Assurance (IA) refers to the assurance of the confidentiality, the integrity, and the availability of information and making sure that all the systems are protected during different phases of information processing. Policies, guidelines, identifying resource requirements, identifying vulnerabilities, and training are forms of information assurance.
Information security management program
The main aim of the information security management program is to make sure that the business operates in a reduced risk environment. This means coworking happens between organizational and operational parties during the whole process. The Information Security Management Framework (ISMF) is an example of a business-driven framework (policies, procedures, standards, and guidelines) that helps an information security professional establish a good level of security.
Hacking concepts and phases
Hacking refers to the gaining of unauthorized access to a system to disclose data, exploiting vulnerabilities within information system. In this section, we will discuss types of hackers and hacking phases.
Types of hackers
We can classify hackers into categories based on their intentions. If the aim of the hacker is to damage or to steal information, then they are classed as a black hat hacker. If it is a security professional with the goal of securing a systems, then they are classed as a white hat hacker. The description is as follows:
- Black hat hackers: These are individuals or groups that use their computer skills to gain access to information using malicious techniques, for various reasons, for example, financial gain.
- White hat Hackers: These are information security professionals. Their main role is to protect information systems against black hat hackers.
- Gray hat hackers: These work both offensively and defensively.
- Script kiddies: Usually, these are unskilled individuals who use tools and scripts, without knowing how they work.
- Hacktivists: These are hackers with a political agenda or defenders of a cause.
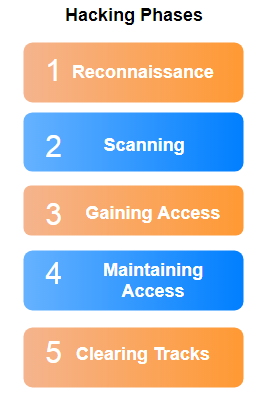
Hacking phases
For a hacking attack to succeed, the operation must follow a set of phases.
Reconnaissance
In this first phase, before taking any action, the attacker must be prepared by carrying out an information-gathering exercise on the target. The attacker collects, from many sources, every piece of publicly available sensitive information, such as target clients, employees, and network information. At the end of this phase, the hacker will have a clear view of the network (domain name, IP ranges, TCP/UDP services, and authentication mechanisms), the system (user/group names, system banners, and system architecture), and organizational information (employee details, press released, and location). There are two types of reconnaissance or footprinting.
Passive reconnaissance
Passive reconnaissance involves acquiring information about the target without directly interacting with it, for example, searching public information.
Active reconnaissance
Active reconnaissance involves interaction with the target, for example, calling technical support to gain some sensitive information.
Reconnaissance is not only technical. It is also an important weapon of competitive intelligence. Knowing some financial aspects of the target could mean that the attack succeeds.
Scanning
After gathering a good amount of information on the target, the attacker has to scan it to reveal useful information about the system and use this information for the next phase (the gaining access phase). During this process, the attacker will look for different types of information, and for that, he will use different types of scanning.
Port scanning
Port scanning is the process of sending packets to a target with the aim of learning more about it in association with well-known port numbers. There are two categories of port scanning: TCP scanning and UDP scanning. To attempt port scanning, it is recommended you to use Nmap, which is an open source port scanner and network exploration tool.
Network scanning
Network scanning describes the process of locating all the live hosts on a network. Scanning a range of IPs is a type of network scan. The basic technique to discover live hosts is a ping sweep. It simply sends ICMP echo requests to multiple hosts from a range of IP addresses. Hping2 is an easy command-line network scanner for TCP/IP protocol.
Vulnerability scanning
During this subphase, the attacker tries to identify weaknesses in the target. The main aim of this type scanning is to find a potential way of exploiting the system. There are a variety of tools for vulnerability scanning, such as Nessus, Nexpose, and many other scanners.
Gaining access
At this stage, the attacker already has what they need to launch their attack, including IP range, identified systems, services, user lists, security vulnerabilities, and flows. Now they only need to bypass security controls to gain access to the system, using several techniques such as password cracking, social engineering or privilege escalation, and gaining other user permissions.
Maintaining access
Mostly, the aim of a hacking attack is not only to get information using unauthorized access, but to also maintain that access. Every day, attackers are coming up with new ways to maintain access. The most well-known technique is hiding files from the system owner and users to avoid being caught.
Clearing tracks
The final phase of every successful hacking attack is clearing the tracks. It is very important, after gaining access and misusing the network, that the attacker cover the tracks to avoid being traced and caught. To do this, the attacker clears all kinds of logs and malicious malware related to the attack. During this phase, the attacker will disable auditing and clear and manipulate logs. The order of the hacking phases is shown here:
Penetration testing overview
By definition, penetration testing is simulating external and internal attacks. The main goal of penetration testing is to enhance the security position of an organization.
Penetration testing types
There are three categories of penetration testing:
- White box pentesting
- Black box pentesting
- Gray box pentesting
White box pentesting
During white box pentesting, or what's sometimes named complete-knowledge testing, the organization gives the pentesters all required information. This type of pentesting is used when the organization wants to perform a full audit of its security and maximize the testing time. It can be done at any point to check its security position. The information provided before performing the pentesting could be, and it is not limited to the following things:
- Network information: Network typology and diagrams, IP addresses, intrusion detection systems, firewalls, and access information
- Infrastructure: Both hardware and software information is made available to the pentesters
- Policies: This is really important because every pentester has to make sure that the pentesting methodology is aligned with the organization's policies
- Current security state including previous pentesting reports
Black box pentesting
In a black box pentesting session, the pentester simulates a real-world attack to gain access to a system or IT infrastructure. Thus, he opts for a pentesting approach with no information about the organization and no prior knowledge of the infrastructure. This type of pentesting is very effective because the pentester wears a black hat and uses a black hat hacker's techniques to bypass the organization's security guards. It is carried out from a black hat hacker's point of view. So, they use fingerprinting techniques to discover everything about the organization.
Gray box pentesting
Gray box pentesting involves simulating an attack by an insider. The pentester is given partial and limited information, like any normal user. This sort of testing lies between black box and white box pentesting.
The penetration testing teams
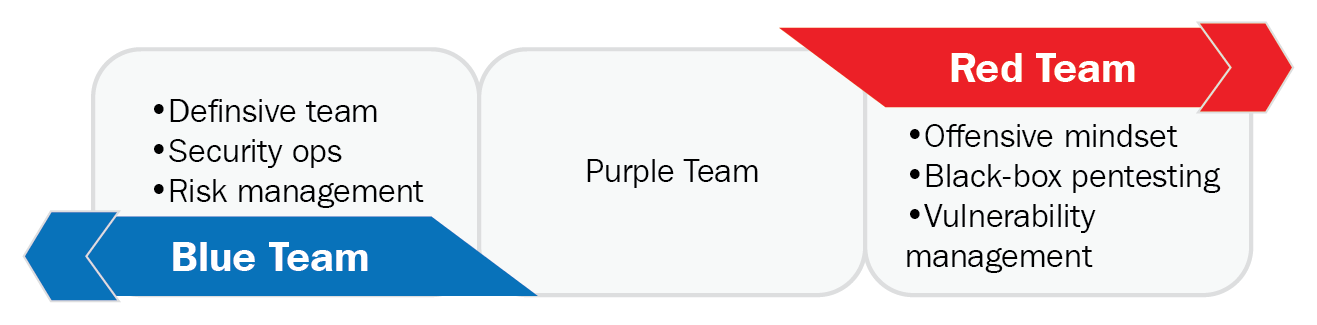
Red teaming and blue teaming are two concepts inspired by strategies used in the military.
Red teaming
The role of a red team is clear. They generally have a specific mission, which is testing the current state of physical and digital security of an organization. The members of a red team have an offensive mindset. They try to attack a specific area.
Blue teaming
Blue teams are the defensive layer. Their mission is to defend against the red team. In general, they are the internal security team.
Purple teaming
To ensure effective penetration testing, a new team is created named the purple team. This team has an effective approach to make the communication between red teams and blue teams clearer, as shown in the following figure:
Pentesting standards and guidance
Before diving deep into pentesting standards and guidelines, we need to define some important terminology to avoid any confusion or misconceptions about four different terms: policies, standards, procedures, and guidance. All these terms play important roles in information security management, but a clear understanding of the difference between them is essential to avoid using them in the wrong way.
Policies
Policies are written documents by high-management level members that specify the responsibilities and required behavior of every individual in an organization. In general, policies are short and don't specify technical aspects, such as operating systems and vendors. If the organization is large, policies could be divided into subpolicies. One of the well-known information security policies is the COBIT 5 Information Security Policy set, as shown here:

Standards
Standards are a low-level description of how the organization will enforce the policy. In other words, they are used to maintain a minimum level of effective cybersecurity. They are also mandatory.
Procedures
Procedures are detailed documents that describe every step required in specific tasks, such as creating a new user or password reset. Every step is mandatory. These procedures must align with the organization's policies.
Guidance
Guidance or guidelines are a set of recommended tips and useful pieces of advice from hands-on experienced people and institutions. There are many standards and guidelines followed by penetration testers. The following are some of the well-known ones, with the required steps for every standard or guideline.
Open Source Security Testing Methodology Manual
The Open Source Security Testing Methodology Manual (OSSTMM) is a comprehensive document released by Pete Herzog and distributed by the Institute for Security and Open Methodologies (ISECOM). According to OSSTMM, every penetration testing should include security testing of information, processes, internet technology (port scanning, firewalls, and so on), communications, wireless, and physical environment.
Information Systems Security Assessment Framework
The Information Systems Security Assessment Framework (ISSAF) is a methodology where the penetration tester imitates the hacking steps with some additional phases. It goes through the following phases:
- Information gathering
- Network mapping
- Vulnerability identification
- Penetration
- Gaining access and privilege escalation
- Enumerating further
- Compromising remote users/sites
- Maintaining access
- Covering the tracks
Penetration Testing Execution Standard
The Penetration Testing Execution Standard (PTES) is a set of technical sections. It helps the penetration tester to deliver an effective pentesting report by walking through the following seven sections:
- Pre-engagement interactions
- Intelligence gathering
- Threat modeling
- Vulnerability analysis
- Exploitation
- Post-exploitation
- Reporting
Payment Card Industry Data Security Standard
The Payment Card Industry Data Security Standard (PCI DSS) is an important reference for organizations that are planning to work with major brand credit cards'. It was released in 2014. It is used to assure the security of credit card holders' data and avoid frauds. The compliance is performed once per year by a qualified security assessor, who is provided by the PCI Security Standards Council or internally for small data amount cases. PCI DSS goes through the following four phases:
- Pre-engagement
- Engagement: penetration testing
- Post-engagement
- Reporting and documentation
Penetration testing steps
Penetration testing essentially goes through multiple steps, based on the chosen methodology. In our case, we will study every phase according to the PTES.
Pre-engagement
Before conducting penetration testing, pre-engagement interactions between the pentester and the client should be established. This is a very important phase because you can view pentesting as an information technology project. Like any IT project, it needs great planning capabilities. Pentesting is not a set of technical steps but requires many management and organizational skills. An effective pentesting would start with a meeting with the client to have a crystal understanding of all their needs and vision. As a result of the meeting, a test plan will be developed. It will describe in detail how the pentest will be conducted. Many important items need to be taken care of during the pre-engagement phase.
The objectives and scope
It specifies the target of the pentesting, including the scope (IP addresses and hosts), in a very detailed way. In general, it also contains what assets are to be tested and what is out of bounds. The pre-engagement must also include the time period of the penetration testing mission.
A get out of jail free card
Hacking is an illegal act, so you need to assure that all your work will be done in a legal way. A get out of jail card usually signed by a high-level manager will be enough to get you out of trouble. Here the word "card" is a contract between the two parties that should solve the legal problem if any.
Emergency contact information
To avoid any panic situations when you find something serious, a predefined contact information list is a good idea to ensure a fast and efficient communication channel when it's needed. For example, If you are having an overwhelming network traffic issue because of an intensive automation tool, you need to contact the network engineer.
Payment information
Payment information indicates the payment terms of the penetration testing. When discussing the schedule of the testing, the pentester should also discuss payment arrangements. During the negotiation, you can discuss the payment structure, for example, getting paid after delivering the final report, half amount up-front before conducting the pentesting, or according to a payment schedule. Also, non-payment penalties could be added to the agreement.
Non-disclosure agreement
The aim of a signed non-disclosure agreement (NDA) is to make the pentester commit to keeping all the confidential information and the findings safe. During penetration testing, you will be exposed to a certain amount of data with different classification ranks. That is why, it is a wise decision to sign a document to reassure the upper management that all the collected information is protected.
Intelligence gathering
The intelligence gathering stage is when the pentester searches for all available information about the organization from public sources. At the end of this phase, he will have a clear view of the network (domain name, IP ranges, TCP/UDP services, and authentication mechanisms), the systems (user/group names, system banners, and system architecture), and organizational information (employee details, press releases, and location). It depends on the type of pentesting (black, white, or gray). Implementing a good intelligence gathering methodology will facilitate the work in later steps.
The fuel of intelligence gathering is to get publicly available information from different sources. Intelligence gathering is not important in information security and penetration testing, but it is vital for national security, and as many concepts are inspired by the military strategies, in the cyber security field intelligence gathering is also inspired by the battlefields. But in a penetration testing context, all the techniques in this phase should be legal because good intentions do not mean breaking the law, that is why, we said publicly available information. If it is not, the case will be considered as industrial espionage. According to International Trade Commission estimates, current annual losses to US industries due to corporate espionage to be over $70 billion.
Intelligence gathering not only helps improve the security position of the organization, but it gives managers an eagle eye on the competition, and it results in better business decisions. Basically every intelligence gathering operation basically is done following a structured methodology.
Public intelligence
Public intelligence is the process of gathering all possible information about the target, using publicly available sources, and not only searching for it but also archiving it. The term is generally used by government agencies for national security operations. A penetration tester should also adopt such a state of mind and acquire the required skills to gather and classify information. In the era of huge amounts of data, the ability to extract useful information from it is a must.
Social engineering attacks
Social engineering attacks are when employees or others are psychologically deceived into providing sensitive information. Social engineering is the art of manipulating people to gain information about the users in order to ascertain sensitive information, such as login credentials or classified information. Using a human quality like trust in a deceptive way always shows that the human is the weakest layer in information security. One of the social engineering techniques is phishing, which is a technical method of social engineering. As we all know, Phishing is sending an email or text message that appears to come from a legitimate institution and tricking the user to type his login credentials. Spear-phishing is the same technique, but in a more specific range, such as sending phishing emails to short lists of high profile contacts
Physical analysis
Physical security is really critical in the information security landscape. Identifying physical equipment plays a huge role in intelligence gathering.
Information system and network analysis
This technique searches out information about the target including network services, devices, domains, and the information system information.
There are many intelligence gathering categories: human intelligence, signal intelligence, open source intelligence, imagery intelligence, and geospatial intelligence.
Human intelligence
Human intelligence (HUMINT) is the process of collecting information about human targets, with or without interaction with them, using many techniques such as taking photographs and video recording. There are three models of human intelligence:
- Directed Gathering: This is a specific targeting operation. Usually, all the resources are meant to gather information about a unique target
- Active Intelligence Gathering: This process is more specific and requires less investment, and it targets a specific environment.
- Passive Intelligence Gathering: This is the foundation of human intelligence. The information is collected in opportunistic ways such as through walk-ins or referrals. So there is no specific target, except collecting information and trying to find something.

Signal intelligence
Signal intelligence (SIGINT) is the operation of gathering information by intercepting electronic signals and communications. It can be divided into two subcategories: communications intelligence (COMINT) and electronic intelligence (ELINT).
Open source intelligence
Open source intelligence (OSINT), as its name suggests, involves finding information about a defined target using available sources online. It can be done using many techniques:
- Conducting search queries in many search engines
- Gaining information from social media networks
- Searching in deep web directories and the hidden wiki
- Using forum and discussion boards
For example, if you want to search for a specific employee, you can use a theHarvester tool, and it will help find all public information about that person.
You can get theHarvester from its GitHub repository using this command from your console:
git clone https://github.com/laramies/theHarvester
Then, type ./theHarvester to run the script.
For example, if you want to collect information about a targetwebsite using Google search, simply run the following command:
theharvester -d targetwebsite.org -l 100 -b google
Here, the -l option is the limited number of results and -b indicates the search engine. In our case, we used the Google search engine:

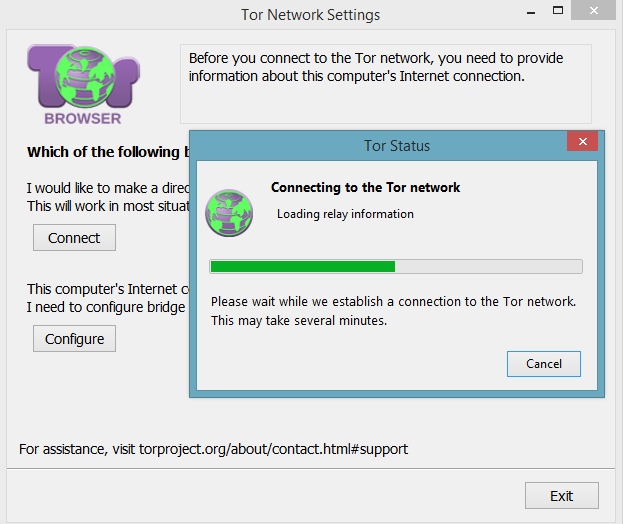
It is an advantage to gather information from the hidden web, not only for reconnaissance purposes but for competitive intelligence. To access the deep web, you simply have to download the Tor Browser via its official website https://www.torproject.org/ and install it. Open the browser and hit Connect to access the network:
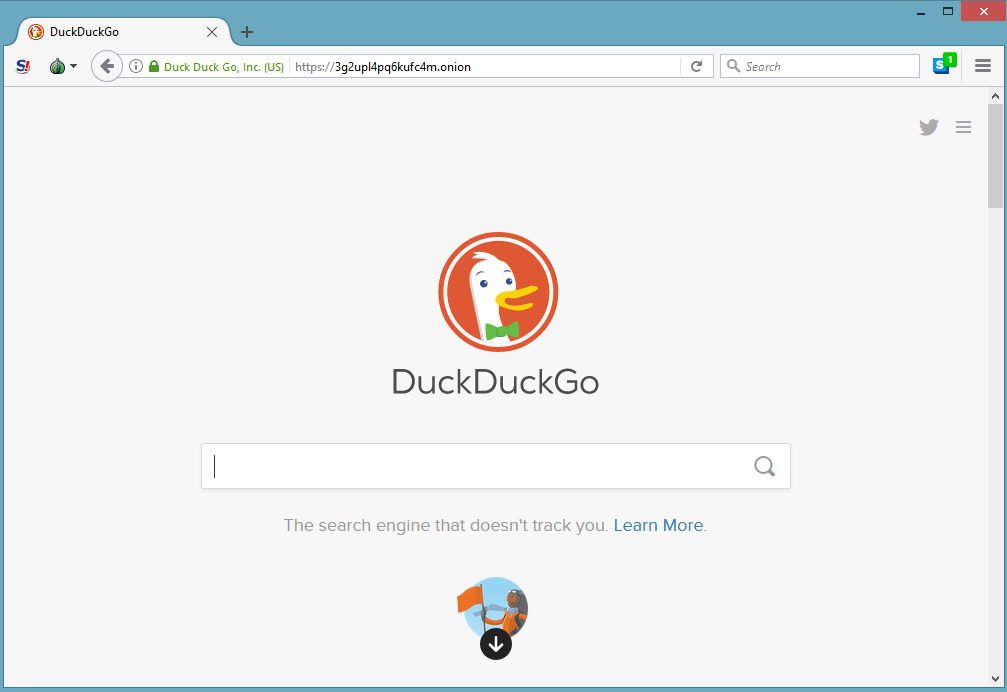
Now, you are surfing the hidden web. You can use the hidden wiki for Tor websites from this link, http://wiki5kauuihowqi5.onion (they are represented as DomainName.onion), or simply use the DuckDuckGo search engine:
Not only you can search for personal identifiable information, but you can also search for online devices and even industrial control systems. For example, you can check www.shodan.io. This search engine will help you find devices online. The following screenshot is publicly available information about wind turbines searched by Shodan.io:

To discover the great potential of the Shodan search engine, let's take a glimpse into the power of this giant. First, go to www.shodan.io and create a new account:
Use the search bar to enter a search query, or you can simply hit a predefined category: Netcams, default password, dreambox, industrial control systems, and so on. This is a snippet of the most popular search tags:
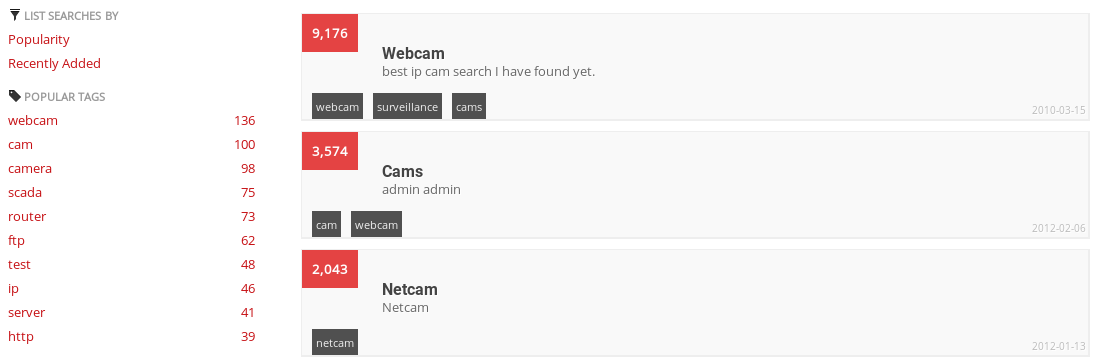
Let's hit Netcams as a demonstration. According to the screenshot listed as follows, the search engine found at least 8,632 publicly available sources of Netcam information, including their IP addresses with detailed descriptions about them:

Also, you can use a real-time map to search online devices such as routers:

Imagery intelligence
In the battlefield, imagery intelligence (IMINT) is the process of analyzing images and videos from different sources and devices such as electronic display images and infrared cameras. In penetration testing, image intelligence also works in the same way, where it is the operation of identifying information about the target using different photos and videos from different public resources as follows:
- Social media (Facebook, LinkedIn, and so on) videos
- Reverse searched photos for other editions
- Live streams
There are many image analysis tools that you can use to extract data from an image. One of them is ExifTool. It is a small tool used to extract juicy information about a defined image. Like the following graph, just download ExifTool from this link, https://www.sno.phy.queensu.ca/~phil/exiftool/, and type ./exiftool image.png:

Geospatial intelligence
Geospatial intelligence (GEOINT) is the exploitation and analysis of imagery and geospatial information to describe, assess and visualize a defined area. The term GEOINT has become associated with information security and penetration testing. Identifying and collecting information about an organization will give penetration testers the ability to anticipate the physical intrusion of the organization. Thus, the role of a penetration tester is to make sure that data and sensitive information is safe from external threats.
There are many available sources to check for geospatial information. Google Maps is a free geospatial service provided by Google. The following is the result of a search, using a Google Map query:

Threat modeling
Threat modeling is a security approach to identify threats against the infrastructure of an organization. Modeling and quantifying are always wise decisions in information security, and especially in penetration testing. Measuring threats in a realistic way will help penetration testers make good decisions later. The aim of this structured approach is the identification and ranking of threats and assets, using a method that aligns with the business needs of the organization, and then mapping them.
In order to perform effective threat modeling, the penetration tester goes through five analysis steps.
Business asset analysis
During the business asset analysis, the pentester focuses on the assets by gathering any related documents about the assets, and in other situations, conducting interviews within the organization. It could include information about the following:
- Infrastructure design
- System configuration
- User account credentials
- Privileged user account credentials
Information about the technical assets is not sufficient to obtain efficient modeling. Penetration testers should gather information about all the policies and the procedures of the organization, and sometimes, the organization plan, if needed.
Business process analysis
Business is the central point in information security. A wise information security analysis will certainly assure that the organization works in a proper way and generates revenues. All the assets that are in a relationship with business processes are required to be mapped and analyzed, starting with the most critical ones. The following are the assets:
- Information assets
- Human assets
- Third-party assets
Threat agents analysis
During this type of analysis, all the threats based on the location metric are mapped. We can divide threats into two categories—internal and external threats. Employees of the organizations, including the upper management, are also part of this classification because humans are the weakest layer when it comes to information security.
Threat capability analysis
After having a clear understanding about threat agents, now it is time to check for any available tools, exploits, and payloads currently out there that could be used against the organization infrastructure, in addition to analyzing the possible communication mechanisms.
Motivation modeling
A penetration tester could model the motivations behind an attack. In competitive environments and volatile businesses, motivation modeling should be added to the pentester checklist.
Vulnerability analysis
Threats are a serious problem for people and organizations. A clear understanding of vulnerability analysis is important to ensure that wise managerial decisions are taken and that a secure environment is built as a result of correctly identifying and mitigating such potential threats. Unfortunately, this is still a challenging area for information professionals because threats are becoming more sophisticated and hard to detect every day. Vulnerability assessment is the process of identifying, measuring, and classifying vulnerabilities in an information system. Vulnerability analysis is a critical skill for every pentester.
There is a big misunderstanding when it comes to vulnerability assessment. Many penetration testers confuse vulnerability analysis with penetration testing. In fact, penetration testing is simulating an attack, whereas vulnerability assessment is intended to identify vulnerabilities in a specific area. You can view it as a scanning operation.
A vulnerability management life cycle goes through the following six main phases:
- Identification and discovery: During this phase, the pentester tries to identify all the assets within the discussed scope, including open services and operating systems and tries to detect common potential vulnerabilities in an information system, usually using automation tools and vulnerability scanners.
- Prioritizing and classification: The penetration tester prioritizes the assets based on sensitivity criteria or based on categories. You can also prioritize vulnerabilities using a ranking system, for example, using the Common Vulnerability Scoring System (CVSS) for the Common Vulnerabilities and Exposures (CVE) vulnerabilities.
- Assessment: This involves documenting analyzed risks. The pentester must make a decision about the risk acceptance after an evaluation process. When conducting a vulnerability assessment, you need to validate every found vulnerability. Using vulnerability scanners is important to detect potential vulnerabilities, but penetration testers need to verify every one of them to avoid false positive and incorrect flags.
- Report: During this phase, the pentester shows the results of the conducted vulnerability assessment including the number of issues and trends, accompanied by graphical representations of the obtained artifacts.
- Remediate: This is a detailed roadmap that includes recommendations and the steps required to remediate and fix vulnerabilities, not only technically, but it could include budgets, time slots, raking, and so on.
- Verification: The final step involves verifying the fixed vulnerabilities after a follow-up check:

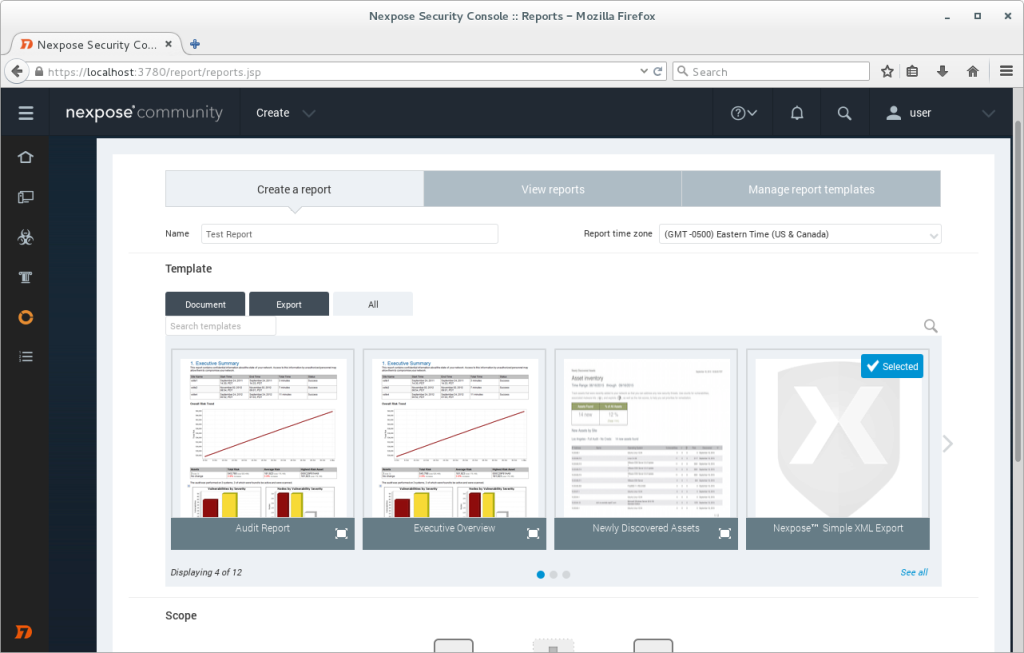
Vulnerability assessment with Nexpose
There are many vulnerability management tools currently available that can help the penetration tester during a vulnerability assessment mission, such us Beyond Security, Qualys, Core Security, and many other tools. One of the most well-known vulnerability management tools is the Rapid7's Nexpose. Nexpose assesses vulnerability in a defined infrastructure.
Installing Nexpose
You can install Nexpose by following the below steps:
- Downloading the community edition from the official website, https://www.rapid7.com/products/nexpose/.
- For the demonstration, we installed Nexpose for Windows 64 edition. You can use the Linux edition as well:
- Fill in the required information and move to the next steps:

Starting Nexpose
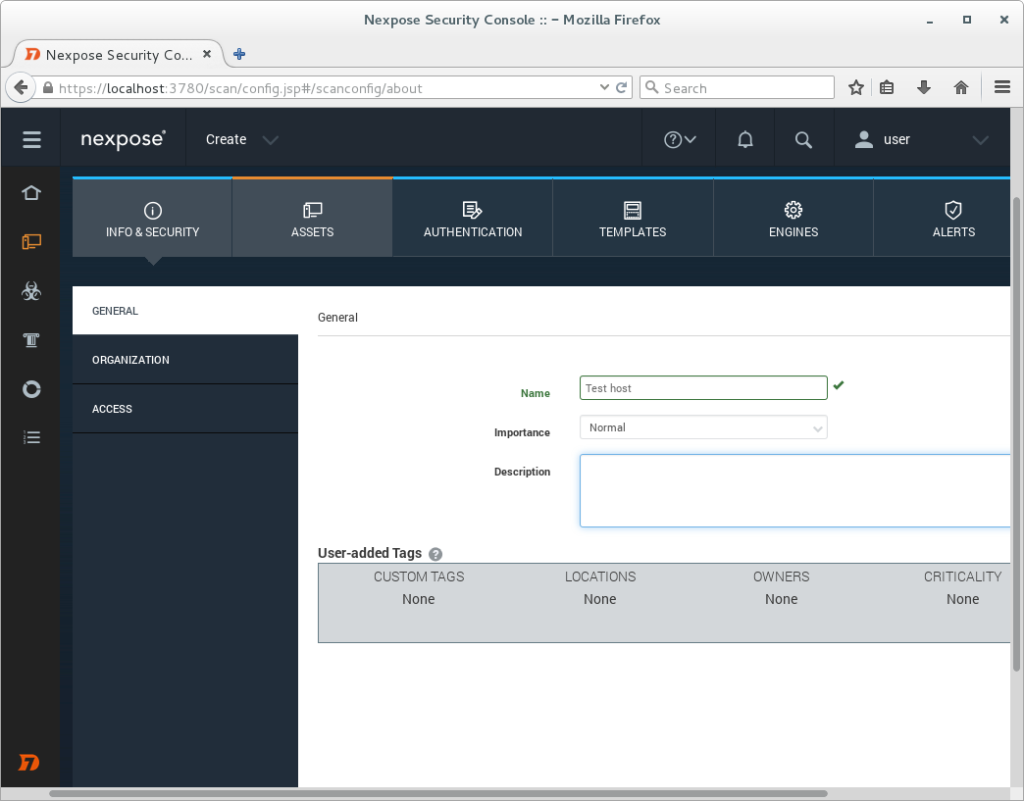
To use Nexpose, you just need to navigate to http://localhost:3780 and enter your credentials.
Start a scan
To start a Nexpose scan, open a project, click on Create and select Site, for example. Then, enter a target IP or an IP range to start a scan:
After the scan is finished, you can generate a scanning report:
Exploitation
By this stage, the penetration tester already has what he needs to launch his attack. Now he only needs to bypass security controls to gain access to the infrastructure system. During this phase, the penetration tester wears a black hat and tries to gain access to the infrastructure from a malicious hacker's perspective. After a good threat analysis, now it is time to exploit every vulnerability. In order to exploit these vulnerabilities, you can use a variety of automation tools and manual testing. The most famous exploitation tool is Metasploit, which is a must in every penetration tester's arsenal.
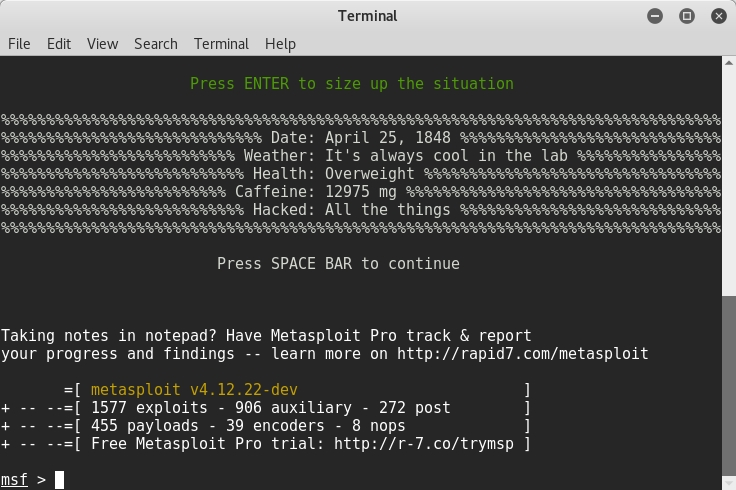
To explore the exploits, a user can use the show exploits command.
Post-exploitation
Getting root privileges is not the end of the road. As discussed before, maintaining access is an essential phase in hacking methodologies, thus post-exploitation is required to not only maintain access but to spread into the infrastructure, to further compromise the system. This phase is critical; the penetration tester simulates an advanced attack; that is why, rules of engagement should be agreed before conducting post-exploitation. This shows and supports the importance of the first pentesting phase (pre-engagement) to protect your client and of course, protect yourself.
Based on the penetration testing execution standard, a post-exploitation phase should go through six sections.
Infrastructure analysis
Networks are the backbone of every modern organization and institution. So an infrastructure analysis will start by identifying the following:
- Every network interface in the scope
- Routing information
- DNS servers and cashed DNS queries
- Proxy servers
- ARP entries
Not only network information but also identifying networking services is critical. They include the following:
- Listening services
- VPN connections
- Mapping the neighbor devices using protocols such as Cisco Discovery Protocol and Link Layer Discovery Protocol
Pillaging
By definition, pillaging is gathering all possible information from the systems. Knowing where the data is located, for example, could help predict the pivoting techniques. To perform an effective penetration testing, you need to gather all, and not limited to, the following information, installed software and services:
- Printers shares and security services
- Database servers
- Directory servers
- Certificate authority services
- Code management servers
- Virtualization services
High-profile targets
High profiles are extremely desirable from a hacker's perspective. Your job as a penetration tester is to make them top of your target list because compromising a high profile could result in compromising a business unit. Don't forget that curiosity and challenging spirit are motives for black hat hackers. That is why, C-level profiles are highly targeted.
Data exfiltration
During data exfiltration, the pentester maps all the exfiltration paths. The aim of this step is to make sure that there is no data leaving the organization in a sneaky way. Analyzing the data flow is of high priority, whereas data is the center of attention for hackers.
Persistence
Backdoors and meterpreters are very common techniques to assure the persistence, even after rebooting the system. Also, creating new accounts with complex passwords will gain you some presence time.
Further penetration into infrastructure
Curiosity is a double-edged weapon. It is part of who we are as humans. Persistent attacks are not enough for a hungry hacker. So, a penetration tester will look for further techniques to compromise more systems and networks in the infrastructure, to gain more access. Some of these techniques are:
- Ping sweep
- Internal DNS enumeration
- Install uploaders
- Services enumeration
- Port forwarding
- VPN to internal networks pivoting
Cleanup
Finally, the penetration tester must clean up the compromised systems of any used scripts, binaries, new accounts, and configurations during the previous post-exploitation steps.
Reporting
The final phase of pentesting is reporting. This is a deliverable document that includes all the findings and the processes conducted during the pentest mission. This step is very important for many reasons. The pentester needs to write a legible report so that every detail could be retested another time. Also, it should be comprehensible by the management board. Every report must be very clear and meaningful for both the technical and non-technical sides. To achieve a good pentesting report for different types of people, it should contain the following sections.
Executive summary
This section gives a high-level glimpse of the findings and specifies the main aims of the penetration testing. The target audience of this section is the upper management because they care about the security of the organization, more than the technical details. That is why, in an executive summary, it is not recommended you mention the technical specifications of the findings. The executive summary includes the following:
- A background explains the purpose of the penetration testing and an explanation of some technical terms for the executive, if needed. The upper management, after reading the background, will have a clear idea about the goal and the expected results of the penetration testing.
- An overall position relating to the effectiveness of the test by highlighting some security issues, such as according to the PTES standard, the business is lacking an effective patch management process.
- Risk score is a general overview of risk ranking based on a predefined scoring system in the pre-engagement phase. Usually, we use the high/low scoring metrics or a numerical scale.
- Recommendation summary specifies the required steps and methods to remediate the security issues discussed in the previous point.
- Strategic roadmap indicates a detailed short- to long-term roadmap to enhance the security of an organization, based on ordered objectives.
Technical report
This section is made for technical managers and information technology staff. It includes detailed information about all the conducted steps and operations. It is structured the following way:
- An introduction
- Information gathering
- Vulnerability assessment
- Vulnerability confirmation
- Post-exploitation
- Risk/exposure
- Conclusion to give a final overview of the test
Penetration testing limitations and challenges
Penetration testing is facing many challenges in the information security landscape. The limited scope of penetration testing with temporal-space boundaries makes it a hard mission, especially when you are working in a production environment. Lack of communication with the client could make it even harder. There are some common issues and challenges, which could occur when conducting a pentesting:
- Timing while pentesting is limited by a time period
- During a pentesting, you can't cover all the vulnerabilities and threats
- Presence of restricted areas
- Sudden and unexpected technical incidents due to heavy scanning and automated tools
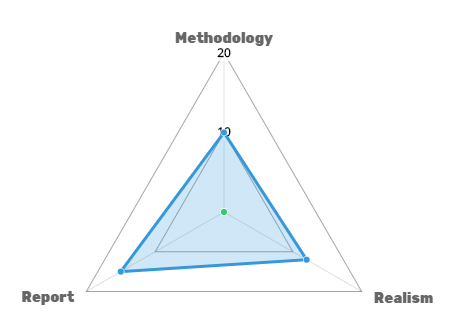
Pentesting maturity and scoring model
Penetration testing like any systemic methodology needs to be evaluated to provide useful insights about the reliability of the used methodology. A well-designed pentesting approach and a good evaluation strategy should be based on quantified approved criteria, to quickly determine the depth and the quality of testing. Industry leaders are aware of all well-known penetration testing methodologies, but due to some understanding difficulties, many of these companies are using their own methodologies. An effective penetration testing program assures that the objectives of your penetration testing program were met without creating misunderstandings, misconceptions, or false expectations. A maturity model is needed to assure that the pentesting methodology meets the organization needs; you can build the most suitable maturity model for your organization needs. You can get inspired by a penetration testing model made by voodoo security. It is built to give an idea about such models.
The penetration testing maturity model is based on three main criteria. Each criteria has five questions to answer by yes or no. If yes, the overall score will be added by one point, else, it will add nothing. Based on your responses to all the questions, the overall score will define the evaluation of your penetration test.
Realism
This metric is used to evaluate whether the penetration testing is realistic, and it is built to simulate real-world attacks. Answer the following questions in terms of yes or no:
- Did you use the black box approach?
- Did you avoid detection?
- Did you use social engineering?
- Did you use exfiltrated data?
- Did you emulate a malware?
Methodology
This metric is based on the methodology itself, and the tools are used in every step when conducting the penetration testing. Answer the following questions in terms of yes or no:
- Does the used methodology already exist or is it customized?
- Are all the steps done in a connected way?
- Did you use both manual and automated tools?
- Did you actually exploit the target?
- Is pivoting allowed?
Reporting
This metric evaluates the resulting report as it is an important step in penetration testing, whereas it is written for multiple audiences. Answer the following questions in terms of yes or no:
- Did you remove false positives?
- Are your steps repeatable?
- Are the vulnerabilities assessed used in contextual risks?
- Do the results align with the business needs?
- Is the remediation plan suitable for the organization?
Based on the obtained score, you can evaluate your penetration testing and rank it using the following scale:
- 0-5: Low maturity level
- 6-10: Medium maturity level
- 11-15: High maturity level
For better presentation, you can use graphical charts:
Summary
In this chapter, we covered the different penetration testing methodologies and the required steps to conduct a full-scale, high-value, and repeatable pentesting, in addition to gaining the in-demand skills to evaluate one. Furthermore, in the next chapter, the journey will continue. You will expose weaknesses in a Linux infrastructure, and you will not only learn how to secure Linux machines but also detect vulnerabilities and exploit them at the kernel level.



















 Download code from GitHub
Download code from GitHub



